OLLI Course: Be Safer on the Internet
OLLI Course: Be Safer on the Internet
Course Desc. | Instructor | Course Topics
Course Description
- upcoming: ?
- previous: Zoom: Spring 2020; Ashland: Winter 2019, Fall 2017, Fall 2016, Spring 2015, Fall 2015; Medford: Winter 2016
- Course URL:
https://communicrossings.com/olli-course-be-safer-internet
this site will continue to be available and updated - Course Handout: web pages as .pdf (offline copy), with active links; updated occasionally;
- Zoom: Use, Setup, Safety
- Be Safer on the Internet (version 2) is a shorter [3-session] remote version of my original [5-6 session] course.
- Are you glued to your devices more these days, and concerned about the privacy and security of your personal information?
- Learn preventive strategies, trade-offs and practical steps to reduce your risks (even from the NSA!) for computers, tablets, and smartphones.
- "Offline" topics: software updates, local & cloud backups, WiFi and router setup.
- "Online" topics: encryption, browsing, email, messaging/chat, search, malware, ad blocking, VPNs, social media.
- Specific settings will be demonstrated only for latest macOS and iOS (iPad/iPhone) systems, Safari browser and selected apps.
However, users of Android, Windows, and other/older devices/apps are welcome to find and then apply analogous changes to their own system and browser settings. - This shorter course will not discuss passwords and password managers -- see separate course P@s$w0rdz;
nor the topics: firewalls, file sharing, mobile/travel, "Internet of Things", and children's safety. - Table comparing topics covered in Be Safer on the Internet -- original (version 1) & new (version 2) -- and P@s$w0rdz (Passwords)
Original (version 1) course description
- Would you like to improve the privacy and security of your personal information -- offline and online?
- This lecture course covers preventive strategies, discusses trade-offs and prioritizes practical steps to reduce your risks (even from the NSA!) for computers, tablets, and smartphones.
- Topics include strong passwords, password managers, software updates, local & cloud backups, WiFi and router setup,
browsing, email, messaging, encryption, malware, ad blocking, 2-factor authentication, VPNs, social media, travel, and the "Internet of Things". - Specific settings will be demonstrated only for latest macOS and iOS (iPad/iPhone) systems, Safari browser and selected apps.
- However, users of Android, Windows, and other/older devices/apps, who are familiar with the location of their system and browser settings, are welcome to attend and use provided references to adjust similar settings.
- Former students wanting a refresher are welcome, too -- there's too much information in the course to absorb and implement at one time; risks and best practices continue to evolve; these pages are updated periodically -- be sure to check back for advice, esp. about issues highlighted in the news -- In particular, the Course Updates page highlights major issues, e.g., Meltdown/Spectre CPU vulnerabilities, latest software updates, Equifax hack, etc.
- Optional e-book: Take Control of Your Online Privacy (if it's updated in near future, discounted version may be available).
- More about the course: Introduction: Approach, Audience, Devices, E-books
 About the Instructor
About the Instructor
Internet Privacy & Security Courses: Topics: Overview & Sessions
- "Getting information off the Internet is like taking a drink from a fire hydrant." ~Mitchell Kapor
- The same might be said about this course -- many topics to cover; too little time; it can seem overwhelming.
- I'll highlight and introduce the most important issues.
- We may touch on other topics briefly during Q&A, and/or you can study materials and References on your own.
- You can even take the course again, if there's something you missed or didn't understand, or to hear the latest advice.
- A 1-page 'cheat sheet' summarizes some of the advice from this course,
which mirrors / includes much of the content of the ebook: Take Control of Your Online Privacy (TCYOP) - See this course's original Topics page for even more "Top 10" check lists & best practices.
| Be Safer on the Internet (version 1) | ... (version 2) | P@s$w0rdz |
|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
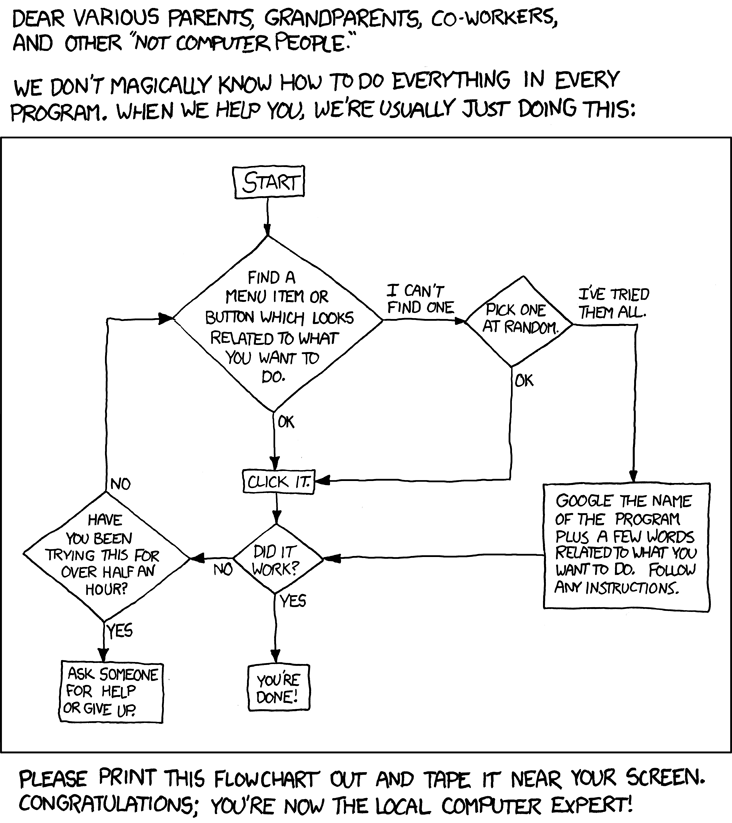
Non-expert Online Practices 1. Use Antivirus Software 2. Use Strong Passwords 3. Change Passwords Frequently 4. Only Visit Websites They Know 5. Don't Share Personal Info |
Expert Online Practices 1. Install Software Updates 2. Use Unique Passwords 3. Use 2-Factor Authentication 4. Use Strong Passwords 5. Use a Password Manager |
|
 |
|
|
||
Safer Internet: Introduction
Safer Internet: Introduction
Quotes | The Problem | References
Quotes
The "Problem"
- The Internet's initial design did not foresee today's privacy and security problems.
- Instead, the Internet has evolved like patchwork over the past 50 years.
- Human nature has not evolved much over the millenia.
- Users can be gullible; governments, spies and criminals are attracted to ever more sensitive data and weak safeguards.
- More people & devices are connected to the Internet, for many more uses, from more locations.
- With inexpensive online storage, data tends to accumulate.
- Total online privacy is basically impossible, but also probably not what you want.
- Ordinary people with ordinary needs can still avoid the biggest privacy and security threats.
- Additional sections -- from
All Courses: Introduction[menu] - Resources: where to find materials, i.e., here
- Navigation: using this web site
- Handouts: how to create your own printed version
References
- What's New; Intro; Online Privacy Quick Start {TCYOP-3: 4-10; TCYOP-2: 5-9; TCYOP-1: 8-11}
- What Happens On The Internet Stays On The Internet (Duh) 5/14/2009
Safer Internet: Introduction: Approach
Safer Internet: Introduction: Approach
 The Plan
The Plan
- Awareness: help you understand the kinds of information you might want to protect, and from whom, as well as techniques to improve privacy and security.
- Promote a sense of urgency -- without undue panic, hopefully.
- Vary the depth of coverage, depending on student background and questions.
- Follow Joe Kissell's e-book: Take Control of Your Online Privacy {TCYOP}
though it's not necessary to have a copy since it's getting out of date - Offer even more advice, and links to many articles: reviews, news, issues
 Start from the inside-out: you, your computer, network connection, the internet
Start from the inside-out: you, your computer, network connection, the internet- Explain just enough of the underlying jargon, infrastructure and technology to enhance understanding
- Emphasize preventive, proactive, personal measures -- rather than deal with post-loss emergencies -- though increasingly there will be some actions you need to take to deal with the aftermath of corporate and government breaches
- Plan & Prioritize (by difficulty/experience labels: [1, 2, 3]): manageable steps you can take to reduce your privacy and security risks -- though not completely from the NSA.
- Present trade-offs: convenience/effort for you vs. sensitivity/value of your info; one size does not fit all
- Update advice over time, based on new threats and tools -- check Course Updates section
- Guarantee that...
Safer Internet: Introduction: Audience
Safer Internet: Introduction: Audience
Who
- You -- "ordinary" users with willingness to:
- Explore settings on your computers/devices and read articles
-- or if you're not DIY, at least understand the risks/issues, while enlisting your 'techie' friend/relative - Take action: make some immediate changes, and create a plan for later actions
- Avoid procrastination, panic, guilt or information overload
- Ask questions, especially about jargon (or see PC Glossary definitions of Computer and Internet Terms)
Advice Levels / Tags
- [#] prefix on advice/references suggests* experience, importance and/or effort:
- [1] Beginners: some familiarity with system/browser settings; high impact; mostly easy
- [2] Intermediate: more experienced; moderate, some complexity, less common
- [3] Advanced: savvy users, developers, administrators; more complex; special situations; research or future-oriented
- -- or Extreme: dissidents, journalists, whistleblowers, celebrities, lawmakers, lawbreakers, corporations, crytocurrency speculators, paranoids
- *categories are not rigid -- arguably, some items could shift +/-1
- This Chart Shows How Computer Literate Most People Are
Distribution of Computer Skills (none, terrible, poor, medium, strong) Among People Aged 16-65, by country; 12/7/2016
Safer Internet: Introduction: Settings
Safer Internet: Introduction: Settings
Devices & OS | System Settings | Apps
Devices & Operating Systems
- Modern-day desktop computers, laptops, tablets, and phones provide similar connection capabilities,
and most web browsers and email applications provide similar privacy and security features
-- though often with different names and options. - It would be difficult here to provide or discuss up-to-date recommendations and configuration advice
specific to every site, device model, operating system version, application, and tool
-- in every country & situation. - As mentioned in the course description, Steve will list or demonstrate specific examples
of settings for only most recent macOS & iOS (iPad, iPhone) -- not: watchOS, tvOS;
location of settings may change in newer software updates. - He will also demo (and sometimes recommend) specific applications in different categories,
e.g., browser: Safari; email: Mail; local (disk) backup: Time Machine, Carbon Copy Cloner;
remote (cloud) backup: Backblaze; password manager: 1Password;
VPN (Virtual Private Network): Witopia; ad blocker: Wipr, Adblock Plus; etc.
-- there may be other viable alternatives for you (platform, features, costs) - If you're using Windows, Android, Chromebook, Linux, or an older version of macOS or iOS,
or some other wearable or home device/camera/streaming box/system (e.g., "Internet of Things"), don't panic
-- you should be able to locate corresponding settings by exploring your device or reading articles (I provide many). - Each topic has links to articles in a References section, subdivided by platform and subtopics.
- Also, see section: Finding More Help: other e-books, classes, consultants.
System Settings
via Menu
- general setting format: OS:
preference / application > menu/tab > etc., e.g.,  Android:
Android: Apps > Settings > etc.- iOS:
Settings > General > etc. - macOS:
Apple menu / Launchpad > System Preferences >
Security & Privacy > etc. - Windows:
Control Panel > etc.
via Search
- And: How to use Android Pie's search bar to control your phone's settings Verge; 3/4/2019
 macOS:
macOS: Launchpad > Search- iOS:
Settings > Search - iOS: iOS (Spotlight search): from the Lock screen or first page of the Home screen,
swipe right to enter the Widgets screen, which features a Spotlight search box
Before Change
- Save current system or account settings to make possible later undo much easier,
e.g., via screenshot or movie; is there aReset / Defaultsbutton? - macOS: shift-cmd-4; drag across area; screen image appears on Desktop; open in Preview
Finder > Help: "Take pictures of the screen"- How to Replace Your Mac's Screenshot Tool With Something Better LH; 1/18/2022
- How to Take Full Web Page Screen Capture on Mac with Firefox
OSXD; 12/9/2021 - How to Change Your Mac's Default Save Location for Screenshots (and Why You Should) LH; 8/27/2021
- The Hidden Trick for Capturing Document-Modal Dialogs in Mac Screenshots TB; 7/23/2021
- How to Take Screenshots on Your Smart TV LH; 10/27/2020
- How to Change Where Screenshots Are Saved on Your Mac cmd-sh-5: Options; MR; 6/5/2020
- How to take a screenshot on a Mac -- the comprehensive guide ApIn; 8/19/2019
- How to Take a Screenshot on Any Phone or Laptop Wired; 9/11/2021
- How to Take Scrollable, Full-Page Screenshots of Websites on iOS LH; 2/11/2021
- iOS: press Home button, then power button immediately; screen image appears in Photos
- How to Take Full Page Screenshots in Safari on iPhone & iPad iOS 13, Safari; OSXD; 2/6/2020
- How to Take iPad Screenshots Using Keyboard Shortcuts OSXD; 5/14/2019
- How to take a screenshot on a Chromebook PC; 8/13/2021
- This Is the Best Screenshot Tool for Windows LH; 3/23/2022
- All the Ways to Take Screenshots in Windows 11 LH; 9/17/2021
After Change
- Save any new login name, password, recovery key, security answer, etc. in a secure place,
e.g., password manager -- see Passwords section
Apps
- Check Internet-related Preferences, Settings or Tools for your device's apps, e.g.,
- web browsers: Firefox, Google Chrome, Internet Explorer, Opera -- in addition to Safari
- mail clients: Outlook, Thunderbird -- in addition to Mail
- communication, social networking, maps, etc.
Access
- macOS:
"dock" / Launchpad; also "Other" folder, e.g., Disk Utility; Keychain Access Finder > Applications; also Utilities folder, e.g., Disk Utility; Keychain Access- menubar (top right), e.g., WiFi; Time Machine; DNSCrypt; Bluetooth; 1Password; Dropbox
- iOS:
Home button; double-click for open apps
Search
- macOS:
Launchpad > Search - iOS:
swipe down on home screen > Search
Update / Buy
- macOS:
Apple menu > App Store - iOS:
App Store
Safer Internet: Introduction: Topics
Safer Internet: Introduction: Topics
Summary | Not Covered | References, Check Lists
 Summary
Summary
- Our topics parallel the sequence in Take Control of Your Online Privacy {TCYOP} discussed under Introduction: E-books -- plus pre-requisite offline practices for protecting local systems and info.
- We'll cover these topics over six 2-hour sessions, which should allow enough time for you to understand background, context, tradeoffs, see demonstrations of settings/apps, and ask questions.
- Typical privacy & security recommendations could be summarized in 15 minutes or so, e.g., free 1-page 'cheat sheet': Quick Start section {TCYOP-4: 11-12; TCYOP-3: 9-10} Fix the Easy Things; Choosing Better Passwords; About Two-Factor Authentication; Create Privacy Rules for Yourself; Purge Your Info from Data Brokers; Cope with Special Cases
 Or, you could read one of the ~50 overlapping 'fix this' articles available (Refs below) to improve some important practices, e.g., 'top-ten' check lists, best-practices, end-of-year reminders, New-Year's resolutions, after-the-fact-attack advice.
Or, you could read one of the ~50 overlapping 'fix this' articles available (Refs below) to improve some important practices, e.g., 'top-ten' check lists, best-practices, end-of-year reminders, New-Year's resolutions, after-the-fact-attack advice.- However, the goal of this course is for you to understand which of these many recommendations are the most important, why, and how to implement.
Yes, I've perused and prioritized all of them -- so that you don't have to! - Introduction: The "Problem"
- Approach: TCYOP; Info & Advice; Level of Detail; Tradeoffs
- Audience: Who; Advice Levels / Tags
- Settings: Devices & OS, Apps
- Topics (this page): Table of Contents (TOC); below: # of Sessions; What We Won't Cover {TCYOP-4: 2-4; TCYOP-3: 2-4}
- Finding More Help: Online; Groups, People
- Discounts: E-books, 1Password, Witopia, etc.
- E-books: TCYOP; Formats(.pdf, .epub, Kindle); Editions; Other e-books
- Resources: this web site; article references
- Navigation: Text / Image Size; Links; Search within a page; Top/Bottom of page controls; Slideshows
- Handouts: print/pdf your own; e.g., print web page, with presentation points/discussion at top, possibly omitting References
- Privacy, Security and Anonymity: Definitions & Analogies {TCYOP-4: 17; TCYOP-3: 15}
- What Do You Have to Hide?: attacks, financial, health, identity theft, vehicles {TCYOP-4: 13-17; TCYOP-3: 11-15}
- Who Wants Your Private Data?: companies, governments, hackers {TCYOP-4: 18-28; TCYOP-3: 16-28}
- Develop a Privacy Strategy: Policy / Law; Behavior; Planning; Technology {TCYOP-4: 29-50; TCYOP-3: 29-38}
- Offline Systems & Data {TCYOP: mentions importance of these in passing}
- Passwords -- Introduction: Strength; Generate; Test; Store
- Accounts: computers, phones
- Backups: Incremental vs. Complete (Clone); Local vs. Remote (Cloud); also Death, Photos
- Software Updates: Minor & Major System; App Stores; Replacing a Device
- Encryption: archive or partition with files, notes; whole disk
- Erasing Your Device: Secure Erase; Cleanup; Redaction; Recycling
- Keep Your Internet Connection Private: connection encryption overview {TCYOP-4: 51-77; TCYOP-3: 39-63}
- Encrypt Wi-Fi: Wi-Fi & Router Passwords; WPA2 Encryption; DNS (Domain Name System)
- Use a VPN: Virtual Private Network, e.g., Witopia
- Avoid Malware: User; App Stores; Anti-Virus; Browser Extensions; Flash; Java; cyberattacks / cyberwar
- Turn Off Unnecessary Services: Lock Screen; Find My Mac/iPhone/iPad; Location; Camera; Microphone; Bluetooth
- Use a Firewall: hardware, software
- Browse the Web Privately: browsers {TCYOP-4: 78-109; TCYOP-3: 64-90}
- Go to the Correct Site: Links; Bookmarks; Fraudulent Sites; Search
- Use HTTPS: URLs; Updates; VPN; also, Certificates, OpenSSL
- Manage Storage of Private Data: Private Browsing; Cookies; Autofill; Tracking; Browsing; Search; Download History; Caches
- Block Ads: Popups, Tracking; Content Blockers, e.g., AdBlock Plus
- Protect Passwords: Introduction: Strength, Generate, Test; Identity; Strength; Password Managers, e.g., 1Password; 2-Factor Authentication/2-Step Verification; Biometrics
- Search Privately: Search Suggestions, Providers, e.g., DuckDuckGo
- Anonymity: [3] Censorship, Wikileaks; Dark Web / Deep Net; NSA, CIA; Tor
- Shopping: credit cards; ShopSafe; PayPal; Bitcoin
- Improve Email Privacy: webmail (browser) vs. email client (app) encryption; phishing; spam; remote content {TCYOP-4: 110-131; TCYOP-3: 91-108}
- Email: Anonymity: [3] additional encryption
- Talk and Chat Privately: messaging, audio, video {TCYOP-4: 132-136; TCYOP-3: 109-114}
- Keep Social Media Sort of Private-ish: Privacy Settings & Policies; Facebook; Twitter {TCYOP-4: 137-146; TCYOP-3: 115-120}
- Share Files Privately: Apps, Music, Photos; Networks; also, BitTorrent, Copyright, Piracy {TCYOP-4: 147-155; TCYOP-3: 121-129}
- Manage Your Mobile Privacy: Accounts; Backup; Encryption; Network; Location; Public Devices {TCYOP-4: 156-165; TCYOP-3: 130-139}
- Keep the Internet of Things Private: Smart TVs, Wearables {TCYOP-4: 166-170; TCYOP-3: 140-144}
- Maintain Privacy for Your Kids {TCYOP-4: 171-173; TCYOP-3: 145-147}
- Course Updates: summary of significant changes
What We Won't Cover
- Some intermediate [2] and most advanced [3] issues, unless there's time and student interest
- Problems with your specific device & configuration (esp. non-Internet related); however, I may include tips about usage and cost, and interesting how-tos; also see More Help section for learning, troubleshooting recommendations
- Other non-digital privacy / security issues: paper, home, surveillance, death, etc. -- some in Offline Reference sections
- Internet history, technology questions and social issues ask me to re-offer OLLI course: Internet History and Issues
References: To Do (Not Do) / Check Lists
- Apple: macOS: Security
Software Updates; Gatekeeper; FileVault 2;
Privacy Controls; Password Generator;
iCloud Keychain; Sandboxing; Runtime protections;
Antiphishing; Find My Mac - Apple: Manage Your Privacy
Secure your Devices: passcode; Touch ID, Find My;
Secure your Apple ID: password, security questions, 2-step verification;
Stay secure: phishing, passwords, notifications;
Sharing: iCloud settings, location data, apps, ads, private browsing, children's privacy, diagnostic data - Apple: iOS Security
System Security: Secure boot chain; System Software Authorization; Secure Enclave; Touch ID; Face ID
Encryption and Data Protection: Hardware security features; File Data Protection; Passcodes; Data Protection classes; Keychain Data Protection; Access to Safari saved passwords; Keybags; Security Certifications and programs
App Security: App code signing; Runtime process security; Extensions; App Groups; Data Protection in apps; Accessories; HomeKit; SiriKit; HealthKit; ReplayKit; Secure Notes; Shared Notes; Apple Watch
Network Security: TLS; VPN; Wi-Fi; Bluetooth; Single Sign-on; AirDrop security; Wi-Fi password sharing
Apple Pay: Secure Element; NFC controller; Credit, debit, and prepaid card provisioning; Payment authorization; Transaction-specific dynamic security code; Contactless payments with Apple Pay; Paying with Apple Pay within apps, or on the web or with Handoff Rewards cards; Apple Pay Cash; Suica Cards; Suspending, removing, and erasing cards
Internet Services: Apple ID; iMessage; FaceTime; iCloud; iCloud Keychain; Siri; Continuity; Safari Suggestions; Siri Suggestions;
Device Controls: Passcode protection; iOS pairing model; Configuration enforcement; Mobile device management (MDM); Shared iPad; Apple School Manager; Device Enrollment; Apple Configurator 2; Supervision Restrictions; Remote Wipe; Lost Mode; Activation Lock
Privacy Controls: Location Services; Access to personal data; Privacy policy
Apple Security Bounty; iOS11 white paper; 1/2018 - AARP: Online Safety AARP Technology Education and Knowledge (TEK) Center, e.g.,
How Secure is Your Home Network?
How to Practice Safe Browsing
Keeping Your Computer Up to Date
Seasons Cheatings: Protecting Yourself from Holiday Frauds & Scams
Are Your Passwords Strong Enough - Back Up and Secure Your Digital Life
product reviews: Hard drive;
Online backup service; Cloud sync; Local backup software;
Password manager: free, paid; Two-factor authentication;
Virtual private network service; Secure browser extensions;
Things to skip: Hard drive data-recovery plans;
Traditional or free antivirus suites;
Identity-theft protection; NYT; 11/14/2023 - 9 Tips for Staying Safe Online with Your iPhone, Mac, or iPad
1: Regularly Install Software Updates;
2: Use Strong & Unique Passwords;
3: Use a Password Manager;
4: Use Two-Factor Authentication (2FA);
5: Be Cautious with Sketchy Links & Websites;
6: Be Cautious with Email Attachments;
7: Ignore Scary Pop-ups and Alerts from the Web;
8: Be Wary of Public Wi-Fi Networks;
9: Backup Your Devices; OSXD; 8/14/2023 - Let's bust these four myths of digital privacy and security
1: Stop spammers by writing out “at” and “dot” in your email address;
2: Digital criminals are dumb;
3: You need a VPN to stay safe online;
4: Your email address and phone number are secrets; WaPo; 2/17/2023 - Lock down your Mac with these 10 security tips
Choose a strong login password;
Change your Lock Screen settings;
Use Apple's password manager (or other PM);
Turn on Find My Mac; Set up multiple users;
Lock down your Mail; Limit your app downloads;
Keep your software up to date; Use a VPN;
Augment Apple’s XProtect antivirus; MW; 1/5/2023 - Steps to Simple Online Security (ToC); articles:
1: Always use strong passwords
2: Set Up Two-Factor Authentication
3: Enable Automatic Updates Everywhere
4: Encrypt Your Computer's Storage
5: Track or wipe a lost device
6: Backups
7: Secure Your Smartphone
8: Free Antivirus Software Is Good
9: Secure Your Web Browser
10: Secure Your Wi-Fi
Send messages and files safely
Lock down social media accounts
Extra security for financial and health data
What to do if you think you've been hacked
Secure small gadgets and smart-home devices
Maintain privacy at international borders and protests
Securely sell or donate old electronics
Digital security for online dating and sexting; NYT; 4/1-4/22/2022 - How to lock down your data and enhance privacy on iPhone and iPad
Set a strong passcode & use biometrics;
Edit your Lock screen; USB connections;
Make sure Find My is enabled;
Turn on App Tracking Transparency;
Manage your permissions;
Delete unused (or untrustworthy apps);
Enable privacy in Mail (tracking pixels);
Review Apple's privacy access;
Wipe your EXIF data (location);
Use strong passwords; ApIn; 3/29/2022 - A Practical Guide to Securing Your Windows PC
Click cautiously and install less;
Don't put off automatic updates;
Enable BitLocker;
Back up your files;
Set up Microsoft Defender properly;
Secure your Windows login with a password (and consider logging in with Windows Hello);
Remove software you don’t need (and any "bloatware");
Do a permissions audit;
Check your privacy settings;
NYT; 3/4/2022 - A Practical Guide to Securing Your Mac
Be careful what you click and install;
Don't turn off automatic updates;
Enable FileVault;
Enable the built-in firewall;
Back up your files;
Use a login password (and enable Touch ID if you can);
Consider a guest account;
Delete software you don’t need;
Audit your privacy permissions;
NYT; 3/4/2022 - Privacy myths busted: Protecting your mobile privacy is even harder than you think
settings alone aren't enough to secure your privacy,
but they're a lot more powerful with the right apps;
Use a PIN code to lock your phone
-- not fingerprints or facial recognition;
Disable location tracking;
Turn off your mobile ad ID;
Check your apps and accounts;
Sign out of all other devices;
Lock down your social media;
Enable 2FA; Check for leaky apps;
Fail-safe: Nuke your phone remotely;
The real key to privacy: Add these five apps
1. Signal Private Messenger App; 2. Surfshark VPN;
3&4. Brave Browser and DuckDuckGo;
5. BitWarden password manager; CNet; 1/9/2022 - Securing your digital life:
the key to protecting your digital life is to make it as expensive and impractical as possible
for someone bent on mischief to steal the things most important to your safety, financial security, and privacy;
Part one: The basics
What in my digital life can give away critical information tied to my finances, privacy, and safety?
What can I do to minimize those risks?
How much risk reduction effort is proportional to the risks I face?
How much effort can I actually afford?
Reducing your personal attack surface: mobile, computers, browsers;
threat modeling; Ars; 10/25/2021 - Part two: The bigger picture—and special circumstances
reduce the risks posed by data breaches and identity fraud
Everything counts in multiple accounts
When 2FA is not enough; Social exposure; Special cases; 10/27/2021 - Part three: How smartphones make us vulnerable
Targeted SMS phishing;
Fleece apps and fake apps;
Pigs to the slaughter: fake app stores;
Ars; 11/14/2021 - 6 Things You Need to Do to Prevent Getting Hacked
Use Multi-Factor Authentication;
Get a Password Manager;
Learn How to Spot a Phishing Attack;
Update Everything;
Encrypt Everything;
Wipe Your Digital Footprint;
Wired; 8/29/2021 - Five Tech Commandments to a Safer Digital Life
Thou Shalt Not Use Weak Passwords
Use Multifactor Authentication
Thou Shalt Not Overshare
Thou Shalt Not Share Data About Friends
Remember to Stay Skeptical; NYT; 3/24/2021 - How to Spring Clean Your Online Accounts Now That You're Stuck at Home
Delete your unused accounts;
Back up your stuff;
Organize your photos;
Declutter your devices;
Catch up on your emails;
Reset website permissions;
Update your software;
Analyze your fitness stats;
Cancel some subscriptions;
Turn on two-factor authentication; Giz; 3/26/2020 - The Complete Guide to Avoiding Online Scams
Never, ever click a link to your bank or financial institution from an email;
Don’t give out your passwords;
Use strong passwords (and secret questions);
Don’t buy anything from a random email you receive;
Watch out for job postings that look too good to be true;
Do not give out your personal info or Social Security number;
Take advantage of your browser’s security features;
Ignore website popups that say you have a virus; LH; 1/13/2020 - 8 Ways to Better Navigate the Internet in 2020
Take back (some of) your privacy;
Clean up after yourself;
Mind your manners;
Learn to fight fair;
Write better emails;
Think twice before you send that DM;
Do a data ‘cleanse;
Guard your health data; NYT; 12/26/2019 - Staying safe online
Use unique user name and password combinations on different websites;
Sign up for 2-step verification on sites that offer it;
Set up alerts for account changes;
Contact details up to date (email, phone number, address, etc.)?
Review your account at least monthly;
Request and review your credit reports from the 3 major credit bureaus;
On social media, don't share too much personal information, and check privacy settings; Vanguard; 10/29/2019 - 10 Tips to Avoid Leaving Tracks Around the Internet
Duck Google for email, search
Jam Google (e.g., different gender)
Avoid unnecessary web tracking
Careful on public Wi-Fi
Use Apple
Don't "Sign in with Facebook"
Identity theft, from a pro
Don't use Facebook; NYT; 10/6/2019 - 7 Cybersecurity Threats That Can Sneak Up on You
Rogue USB Sticks
Zombie (unused) Accounts
Untrusted Browser Extensions
Bogus Online Quizzes
Leaky Photo Uploads
Smart Home Snooping
Malicious Charging Cables; Wired; 10/6/2019 - 5 Cheap(ish) Things to Beef Up Your Digital Security
1. A password manager, e.g., 1Password
2. A virtual private network service (VPN)
3. A two-factor authentication app, e.g., Authy (built-in to 1Password)
4. A webcam cover
5. A paper shredder; NYT; 9/25/2019 - NYT: Secure Your Digital Life in 7 (Easy) Days:
1. Set Up a Password Manager;
2. Check Your Smartphone's Privacy Settings;
3.Protect Your Browsing;
4. Protect (Encrypt/Locate) Your Laptop;
5. Vaccinate Your Computer;
6. Get All the Software Updates;
7. Lock Down Your Most Important Accounts (2FA) - 101 Data Security Tips: Quotes From Experts On Breaches, Policy, News 9/25/2019
- 9 Seemingly Harmless Things You Should Never Do Online
1. Don't Take Personality Quizzes From Unknown Sources in Social Media.
2. Don't Post Your Full Birth Date and Hometown Online.
3. Don't Use Public Wi-Fi Without Verifying that it's a Legitimate Network.
4. Don't Follow Up a Gaming Session with Some Online Banking.
5. Don't Click on Links or Attachments in Emails Without Verifying the Source.
6. Don't Use The Same Password For Multiple Accounts.
7. Don't Click Links To "Promotions" Sent Through SMS; MF; 7/2/2019 - [2] 6 things you should do to protect yourself from hackers (but probably won't)
#1: Know which public Wi-Fi to trust
#2: Run tests for weaknesses
#3: Disable and manage third-party permissions
#4: Encrypt your data yourself
#5: Overwrite any deleted files
#6: Practice the ‘Principle of Least Privilege'; TNW; 4/14/2019 - 15 strategies everyone should know to protect their online information
1. Use a password manager
2. Be fully aware of what you're sharing
3. Avoid clicking on links
4. Be diligent, aware, and cautious
5. Enable double-confirmation on all accounts
6. Use credit locks and cloud security
7. Remove personal data from your social media
8. Do your research
9. Check your settings
10. Protect your online browsing
11. Stop using the same password for everything
12. Stick with reputable sites
13. Close old accounts you’re no longer using
14. Start over with a new credit card and new accounts
15. Remove yourself from people search sites; TNW; 2/15/2019 - How to Do a Data 'Cleanse'
1. Have you backed up your data?
2. Are your phone's photos safe?
3. Have you cleaned out your machine?
4. Is your software up-to-date?
NYT; 2/1/2019 - How to Protect Yourself on Data Privacy Day
1. Own Your Online Presence
2. Keep a Clean Machine
3. Protect Your Personal Information
4. Connect with Care
5. Be Web Wise; National Cyber Security Alliance (NCSA); OR DOJ; 1/29/2019 - Keep your digital life secure with these 6 simple tricks
1. Set boundaries. Decide -- on your own, and in advance -- what data you're willing to share with apps and online services, and stick to those limits
2. Burst your filter bubble. People who get their news primarily -- or exclusively -- from social media are subjecting themselves to the whims of the algorithms that decide what to display to each user
3. Manage your passwords
4. Turn on multi-factor authentication
5. Delete apps you don't use
6. Keep the apps you do use up-to-date; TNW; 1/12/2019 - Cybersecurity 101
Why you need to use a password manager;
Two-factor authentication can save you from hackers;
How to protect your cell phone number and why you should care;
How to browse the web securely and privately;
How to choose and use an encrypted messaging app; TC; 12/25/2018 - Online security tools: The holiday gift that shows you really care
Give a password management app or subscription;
Add a second factor to complement a password;
Sign them up for account breach notifications;
Install free or paid anti-malware software;
Set up online backups;
Turn on FileVault on their Macs;
Set up a VPN account;
Credit freeze; MW; 12/5/2018 - Bad (Better) Consumer Security Advice
unsecured Wi-Fi & VPN;
proactively create accounts: Social Security Admin., IRS, USPS;
two-factor authentication;
strong passwords, unique for each account (but don't change frequently);
credit freezes;
airport outlets? Schneier; 12/4/2018 - After Marriott Breach, How to Protect Your Information Online NYT; 11/30/2018
- Guide to Not Getting Hacked
Review Your Threat Model
Keep OS and apps up to date
Use a Password Manager
Use two-factor authentication
Don't use Flash
Do use antivirus
Do use an ad blocker
Do use a VPN
Disable macros
Backup files
Don't overexpose yourself for no reason
Don't open attachments without precautions
Do opt out of data broker websites
Do sext if you want, but do it safely
Mobile Threat Model
If you can, get an iPhone
If you love Android, get Pixel
Lock up that Telephone Number
Threat Model (privacy and surveillance)
Signal
Social Media
Device Cameras, Microphones, and the Internet of Things
Chatting
Tor Browser
Virtual Private Networks
PGP
Private Email Servers (don't do it)
Encrypt your Hard Drive
Credit Cards
Data Retention for Lawyers, Journalists, and Anyone Else
Log Off
version 3: MB; 11/12/2018 - How to Make Your Mac as Secure as Possible
Software Update
Identified Developers
File Vault
Location
Spotlight Suggestions
DNS; LH; 10/5/2018 - How to Be Invisible Online (Without Going off the Grid) infographic;
1. How to Anonymize Everything You Do Online: Go Incognito; Block 3rd Party Cookies; Tailor Permissions for Websites You Access; Use HTTPS Everywhere
2a. On Facebook: Limits Access to Future Posts; Change Public to Friends-only; Stop People Using Your Personal Info for Finding You; Prevent Your Name Being Linked with Ads; Block Facebook Ads from Accessing Your Data
2b. On Twitter: Prevent Twitter from Tracking You; Stop Including Location Data in Tweets; Stop Twitter from Using Your Contacts
2c. On Instagram: Make Your Posts Private; Prevent Instagram from Sharing Info with other Social Network Sites
2d. On Snapchat: Make Sure Only Your Friends Can Contact You; Select Who You Want to See Your Stories; Remove Yourself from the 'Quick Add' Section; Move Private Snaps Saved in your Memories to 'My Eyes Only'; Pay Attention to Screenshot Notifications
3a. On iOS: Remove Website Tracking Data in Safari; Enable Fraudulent Website Warning; Block Ad Tracking
3b. On Android: Opt Out of Ads Personalization; Disable Google Backup; 8/28/2018 - Gizmodo: 6 Ways You're Risking the Security of Your Gadgets Without Thinking
1. Watching TV and movies illegally
2. Sharing your accounts with other people
3. Using short PIN codes and pattern unlock
4. Practising poor USB security
5. Leaving your webcam and mic uncovered
6. Not updating your software; Giz; 7/4/2018 - Motherboard: Security Tuneup
1. You Should Take Five Minutes to Update Your OS and Apps;
2. It's Time to Actually Use Your Password Manager;
3. You Should Be Using Two-Factor Authentication on Everything;
4. Ad Blockers Are Good for Security, Too;
5. Seriously, Stop Using Flash;
[3] 6. Put an Extra Passcode On Your Cellphone Account (SIM hijacking)
7. If You Use Word, You Need to Turn Off This One Feature: disable macros; MB; 5/23/2018 - Gizmodo: All the Annoying Tech Chores You Need to Do When You Have Time
Update your software;
Free up some space;
Scan for problems;
Get your photos organized;
Update your router;
Move to the cloud;
Untangle your wires;
Clean your gadgets; Giz; 1/2/2018 - 5 New Year's Resolutions to Protect Your Technology
1. Update Your Software;
2. Read Privacy Policies;
3. Delete Unnecessary Apps;
4. Use a VPN;
5. Protect Your Hardware; NYT; 12/27/2017 - Guide to Digital Security choose your profile:
[1-2] Civilian: You're a regular user, but hackers and malware are lurking;
7 Password Tips; Basic Smartphone Security; Resist Phishing Attacks; Keep Your Kids Safe; Protect Yourself from Doxing;
[3] Public Figure: Activist? Journalist? Politician? Consider yourself a target;
How to Encrypt All Your Data; Google Advanced Protection: a Step-by-Step Look; Use Tor for more than just Browsing; Physical Steps to Amp up your Digital Security;
[3+] Spy: Professionals are after you. Time to get serious;
How to Remove the Mic from your Devices; Sniff Out Bugs Planted in your Room; Extra Paranoid Measures for Superspies; Wired; 12/9/2017 - [3] Physical Measures to Amp Up Your Digital Security
Tape Over Your Webcam;
Slap on a Privacy Shield;
Use a Physical Authentication Key; Wired; 12/9/2017 - [3+] Extreme Security Measures for the Extra Paranoid
The Air Gap Up There;
Faraday Cage aux Folles;
Frickin' Laser Microphones;
Literally Put a Blanket Over Your Head; Wired; 12/9/2017 - Take These 7 Steps Now to Reach Password Perfection
1. Use a password manager
2. Go long
3. Keep 'em (special chars) separated
4. Don't change a thing
5. Single-serve only
6. Don't trust your browser
7. Add two-factor too; Wired; 12/9/2017 - How to Secure Your Mac
Part 1 secure setup, non-admin account, parental controls, privacy settings; MW; 11/9/2017;
Part 2 [3] firmware passwords, iCloud two-factor authentication, Safari Browser, Time Machine; MW; 11/15/2017 - Gizmodo: 5 Incredibly Stupid Security Mistakes You Make Everyday
1. Using the same login details everywhere/forever;
2. Not protecting your phone’s lock screen;
3. Not using two-step authentication;
4. Sharing too much information;
5. Using Wi-Fi without thinking; Giz; 10/4/2017 - How to Create a Strong Password
make your passwords very long
don't use a common phrase
test your password
don't reuse your password
use a password manager
don't store passwords in your browser
follow the rules every time
use two-factor authentication
don't ruin all this by using security questions
remember, everything is broken; LH; 8/14/2017 - A Hacker's Guide to Protecting Your Privacy While Dating
1. Don't share your passwords or devices;
2. Set up a Google Voice number to use for first dates;
3. Use a VPN on shared Wi-Fi networks, including your home network;
4. If you're going to make a sex tape, do it consensually and privately; Giz; 7/30/2017 - 10 ways to protect your privacy now
1. Don't overshare on social media;
2. Take control of your children's devices;
3. Secure your Wi-Fi;
4. Become a password master;
5. Keep software up to date;
6. Be browser-savvy;
7. Be a ghost (Ghostery);
8. Be app-aware;
9. Arm your computer (firewall, AV);
10. Shred your documents; MT; 7/9/2017 - Protecting Your Digital Life in 9 Easy Steps
1. Download Signal, or Start Using WhatsApp to send text messages;
2. Be wary of clicking on unfamiliar links or documents and apply software updates;
3. Protect your computer’s hard drive with FileVault or BitLocker — and back up your data to an online backup service, external hard drive, or both;
4. The way you handle your passwords is probably wrong and bad (use strong unique passwords, stored in a password manager);
5. Protect your email and other accounts with two-factor authentication;
6. Use a browser plug-in called HTTPS Everywhere;
7. Invest in a Virtual Private Network, or VPN;
8. Remember that incognito mode isn’t always private;
9. Do sensitive searches in DuckDuckGo;
Bonus: cover your webcam with tape; NYT; 5/16/2017 - How Not to Protect Your Privacy Online
1. Deleting your browsing history doesn’t work;
2. Using an incognito window doesn’t work;
3. Installing an ad blocker doesn’t work; Giz; 3/31/2017 - How to Snoop-Proof Any Phone or Tablet
passcode;
lockscreen;
apps (Signal, Whatsapp, browsers);
VPN;
minimize stored data; Giz; 3/3/2017 - Consumer Reports: 66 Ways to Protect Your Privacy Right Now
1. Check Your Data Breach Status
2. Stop WiFi Imposters
3. Use 10-Minute (Temporary) Mail
4. See Who Shared Your Private Data
5. Lock Your Screens: Long PIN;
6. Try to Be Unique;
7. But Not Too Personal;
8. Do Better Finger Art
9. Snail Mail Privacy: Shred These 5 Document Types;
10. Shut Off the Flow of Credit Card Offers;
11. Receive Less Mail
12. Return to Sender
13. Turn On Automatic Updates
14. Make Sure There's Info-Security Staff
15. Make Unbreakable Passwords: Stop Making Sense
16. Use a Password Manager
17. Got a Great One? Okay, Write It Down.
18. Be Password Loyal (password entropy)
19. Stop ID Theft After a Death
20. Two-Factor Authentication
21. Activate a PIN
22. Watch Your Bills
23. Let Google Scan Your Files
24. Check on the Kids
25. Lock Down Your Baby Monitor
26. Outwit Your Smart TV
27. Shut Down Webcam Creeps
28. Deploy Your Firewall
29. Restrict File Sharing
30. Cloak Your Computer
31. Do All of This Automatically
32. Use a VPN
33. You Know What? Just Fake It.
34. Use Everyday Encryption: Do Your Phone First
35. Encrypt Your Computer or just Sensitive Files
36. Encrypt Your USB Drive
37. Stop Oversharing on Facebook: Keep GPS Data Private
38. Turn on Log-In Approvals (two-factor authentication)
39. Become Elusive
40. Leave a Group
41. Reduce Ad Overload
42. Hide ID-Theft Clues
43. Use Separate Browsers for low- and high-stakes websites
44. Tuneup Home WiFi Privacy: Find an Ethernet Cable
45. Get the Router's IP Number
46. Update the Router Username and Password
47. Change the SSID
48. Then Hide It
49. Embrace Encryption
50. Update Firmware
51. Make Sure Remote Management Is Off
52. Shut It Down
53. And, Uh—Maybe Get a New Router
54. Check Links Before You Click
55. Add HTTPS Everywhere
56. Block Snoops
57. Avoid Ransomware: Back Up Your Data
58. Keep Software Updated
59. Try Haggling (Ransom discount)
60. But Not Right Away (if you're going to pay)
61. Use Ubuntu OS
62. Scoff at Fake Email Notices
63. Call Customer Service
64. Tighten Google Privacy: Tweak the Settings
65. Make Google Forget You
66. Keep Your Fitness Data to Yourself; CR; 2/21/2017 - Your 5 Totally Achievable Security Resolutions for the New Year
1. Set Up a Password Manager;
2. Enable Two-Factor Authentication;
3. Make Backups;
4. Know How to Use a VPN;
[2] 5. Use End-to-End Encrypted Chat Apps; Wired; 12/29/2016 - Five Resolutions to Simplify Your Tech Life
1. Clean Up Your Password Hygiene;
2. Maintain Your Devices;
3. Mind Your Infrastructure;
4. Be Less Wasteful (recycling);
5. Be a Smarter Shopper; NYT; 12/27/2016 - Let Your Whole Family Watch This Internet Security Basics Course
How to choose a good password;
How to know when to trust a website;
Why we need all those software updates;
How to protect your phone from hackers;
How to protect your home from the Internet of Things;
5 ways to protect yourself online; videos; LH; 12/15/2016 - EFF (Electronic Frontier Foundation): Surveillance Self-Defense e.g., How-To Tutorials:
Avoid Phishing Attacks;
[3] Circumvent Online Censorship;
Delete your Data Securely on Linux, Mac OS X, Windows;
Enable Two-factor Authentication;
Encrypt Your iPhone, Your Windows Device;
[3] Install and Use ChatSecure;
Use KeePassX password manager;
[3] Use OTR (Off-the-Record) for Mac, Windows, Linux;
[3] Use PGP (Pretty Good Privacy) for Linux, Mac OS X, Windows;
[2] Use Signal for Android, iOS;
[3] Use Tor (The Onion Router) for Windows, Mac OS X;
[2] Use WhatsApp on Android, iOS; EFF; 12/1/2016 - A beginner's guide to beefing up your privacy and security online
Install updates, especially for your operating system and your browser;
Use strong passwords and passcodes;
Encrypt your phones and computers;
Two-factor authentication;
Using a password manager (and good password practices);
[2] Using Signal for SMS and voice calls;
Using VPNs, especially on public Wi-Fi;
E-mail security (is hard to do);
Deleting old e-mails; Ars; 12/1/2016 - 3 Ways to Boost Your Family's Online Security This Holiday
1. Download Firmware, Operating System, and App Updates;
2. Securely Configure Wi-Fi Networks;
3. Strengthen Email Password; Wired; 11/24/2016 - 11 security basics that keep you safe from holiday tech dangers slideshow
1. Card skimming;
2. Support scams;
3. Phishing;
4. Public Wi-Fi;
5. Internet of Things;
6. System and software patching;
7. Ad blocking;
8. Two-factor authentication;
9. Check statements;
10. RFID protection;
11. EMV cards (Europay-Mastercard-Visa chip); MW; 11/22/2016 - 10-Minute Digital Privacy Tuneup
Turn on Automatic Updates;
Use Screen Locks on Every Device;
Check Your Data-Breach Status;
Use Temporary Email Addresses;
Cover Your Laptop Webcam;
Use the HTTPS Everywhere Browser Extension;
Turn Off Location Tracking in Apps; CR; 9/20/2016 - 12 Security Tricks to Stay Safe Online
1. Keep your software up to date;
2. Trim down your browser;
3. Turn on two-step verification;
4. Check activity on your accounts;
5. Protect your phone's lock screen;
6. Protect your laptop account;
7. Embrace end-to-end encryption;
8. Be careful on public wi-fi;
9. Don't share more than you need to;
10. Check your key accounts;
11. Get help with online security;
12. Use a few real-world hacks, e.g., tape over webcam, wired connection, no passwords on post-its; Giz; 8/5/2016 - Mac News Network: security best practices:
part 1 passwords, Wi-Fi, encryption, phishing; 6/6/2016;
part 2 password managers, downloads, account security; 6/8/2016;
part 3 unregistering devices, private browsing mode, VPNs; 6/10/2016 - Top 10 Tech Security Basics Every Person Should Follow
1. Watch Out for Social Engineering Attacks;
2. Make Your Phone's Lock Code More Secure;
3. Back Up Your Computer Automatically;
4. Install the Best Antivirus and Anti-Malware Software;
5. Lock Down Your Wireless Router;
6. Never Send Sensitive Information Over Email Unless It's Encrypted;
7. Don't Use Public Wi-Fi Without a VPN;
8. Use a Password Manager;
9. Use Two-Factor Authentication;
10. Regularly Review Your App Permissions and Security Settings; LH; 3/26/2016 - 9 Facts About Computer Security That Experts Wish You Knew
1. Having a strong password actually can prevent most attacks;
2. Just because a device is new does not mean it's safe;
3. Even the very best software has security vulnerabilities;
4. Every website and app should use HTTPS;
5. The cloud is not safe -- it just creates new security problems;
6. Software updates are crucial for your protection;
7. Hackers are not criminals;
[2] 8. Cyberattacks and cyberterrorism are exceedingly rare;
[3] 9. Darknet and Deepweb are not the same thing; Giz; 8/9/2015 - Google: Comparing Expert and Non-Expert Security Practices
Use antivirus;
Install latest OS updates;
Turn on automatic updates;
Update applications;
Clear cookies;
Use unique, strong passwords; Don't write down passwords;
Save passwords or use a password manager;
Check if HTTPS; Look at the URL bar;
Be skeptical of everything;
Be suspicious of links -- don't click links from unknown people;
Don't enter passwords on links in email; Don't open email attachments;
Visit only known websites;
Use two-factor authentication; 7/23/2015 - Oregon State Public Interest Research Group (PIRG): Resource Guide to Online Privacy
1. Social Media Privacy;
2. Secure Passwords;
3. Stop Cookies;
4. How to avoid viruses;
5. Keeping your Social Security Number secure;
6. Secure Websites;
7. Scam Email; 11/7/2013 - Electronic Frontier Foundation: Ten Steps You Can Take Right Now Against Internet Surveillance
1. Use end-to-end encryption;
2. Encrypt as much communications as you can;
3. Encrypt your hard drive;
4. Strong passwords, kept safe;
[3] 5. Use Tor;
6. Turn on two-factor (or two-step) authentication;
7. Don't click on attachments;
8. Keep software updated, and use anti-virus software;
9. Keep extra secret information extra secure;
10. Be an ally to EFF; 10/25/2013
Safer Internet: Introduction: Finding More Help
Safer Internet: Introduction: Finding More Help
Local Groups, Classes | Online | People, Consultants, Companies
Creative Commons Attribution-NonCommercial 2.5 License
Local Groups, Classes
- OLLI Tech courses
- Ashland Mac Users Group (AshMUG); resource list
- Rogue Valley Senior Aces
- Ashland Senior Center
- Ashland Parks & Rec
- Choose Privacy Week May 1-7; American Library Assoc.
- Rogue Community College (RCC)
- So You Bought Someone a Gadget. Here’s How
Not to Become Their Tech Support. NYT; 3/19/2020 - How to Fix Your Family's Tech Problems Without Going Crazy
Make sure the device is running the most updated version of its software;
Try restarting fussy devices; Try a different cable;
Ask them to let you fiddle with their device directly;
Instead of a frantic phone call, try a FaceTime;
Ask them to factory-reset their device and set it up again;
Take photos before you become the tech support; LH; 12/30/2019
Online
Help / ?in your OS and applications -- as you look for and change settings.- This course's References sections for each topic, especially for your OS
- Support sections on hardware / software vendor web sites: manuals, tutorials, FAQs, software updates, forums
- Take Control e-books
- How to Chat with Apple Support OSXD; 8/26/2020
- Tech blogs / magazines, e.g., LifeHacker.com [LH]; ArsTechnica [Ars]; macOS/iOS: Tidbits.com [TB]
- Online security tools: The holiday gift that shows you really care MW; Give a password management app or subscription; Add a second factor to complement a password; Sign them up for account breach notifications; Install free or paid anti-malware software; Set up nline backups; Turn on FileVault on their Macs; Set up a VPN account; Credit freeze; 12/5/2018
People, Consultants, Companies
- Your techie family and friends
- Knowledgable class members -- for extra credit, email Steve tips, specific settings for other platforms, links to articles to add to course
- AshMUG links to Rogue Valley consultants/developers as well as Mac tech and education sites
- Local individuals / consultants / companies, that students have used/recommended, in no particular order --
inquire about rates, platforms, services, areas served, experience with your problem: - Nick Viani (Mac); nickviani @ gmail.com
- Derek Enterprises (Mac, iOS); machelp @ toddderek.com
- Grey Jensen (Mac, iOS)
- Mike Davis (Mac, iOS); help4macintosh @ gmail.com
- Ashland Personal Computing Technologies Pierre Petetit; pierre @ ashlandpctech.com
- Audio and Video Solutions Josh Sommers ianmedia3 @ gmail.com
- Conrad Gardner (Win); conrad @ nethuns-digital.us
- Connecting Point (Mac, Win, iOS)
- Dr. Networking (Win, Mac)
- Geek Squad?
- EFF FOIA Suit Findings: FBI Relationship With Best Buy's Geek Squad Dates Back 10+ Years staff would tip FBI on unlawful customer data, in some cases be paid; 3/6/2018
- Any that you recommend -- or that I should remove?
Safer Internet: Introduction: Discounts
Safer Internet: Introduction: Discounts
Save $
- Time-sensitive discounts/promotions are sometimes available for software, services, and e-books,
e.g., especially around "Black Friday" and "Cyber Monday" (after Thanksgiving)
or special dates, e.g., World Backup Day (Mar 31 for backup products). - Some member/referral discounts for password manager, e-books, backups, VPN and cell service are listed below:
- Tidbits.com members can receive discounts
- 1Password (password manager): 6 months free subscription
- Take Control e-books (Macintosh System, Apps; iPad/iPhone/iPod;
Internet/Networking; Digital Photography; Windows): 30% - and over 80 Mac and other products, e.g., Retrospect backup software: 20% to 40%
- Backblaze: if subscribing to Backblaze backup cloud service, use this referral link -- or code:
00gxf7--
to receive a free month; and Steve receives a free month credit. - Witopia (VPN): if subscribing to PersonalVPN (aka Witopia) service, use this referral link -- or code:
Q8Hg3YRM--
to receive a 15% discount; and Steve receives a similar credit. - For unlimited cellular voice and text (and limited 4G dataplan) in US, you can save money
by having a monthly, pay-for-what-you-need cellular phone plan.
I suggest checking your bills over past year to see your average monthly usage.
I pay < 1/2 with Consumer Cellular for our calling, texting and data compared to AT&T.
If you decide to switch to Consumer Cellular, mention that Steve Weyer referred you, and we'll both get a credit;
if you're an AARP member, you'll save an additional 5% per month - Consumer Cellular Offers Cheap, No-Nonsense Access to AT&T's Cellular Network TB; 7/12/2021
Safer Internet: Introduction: E-books
Safer Internet: Introduction: E-books
TCYOP
As mentioned earlier, this course is based on Joe Kissell's e-book:
Take Control of Your Online Privacy {TCYOP}, from the excellent Take Control series of technical e-books.
TCYOP is suggested but not required for this course;
this course generally uses the same chapter/section headings and sequence.- 4.0; 4/11/2019; 178 pp.; reg: $15*
- 'cheat sheet'; free; 1 pp. .pdf
- sample; free; 43 pp.; .pdf
- older versions: 3.0; 4/2017; 152pp.; 2.0; 5/2015; 135pp.1.1; 3/2014; 123pp.
- "{TCYOP-4: #}" in course material refers to Chapter and Figure pages in the current .pdf edition
- "{TCYOP-4: #; TCYOP-3:#}" (in smaller font) refers to pages in older editions (for students from previous terms).
- *If there's enough interest before the class is offered, I can obtain discounted copies of TCYOP (@$3) for students.
Or, you can save $ if you order multiple TakeControl e-books (many about related topics: Passwords; 1Password (password manager);
Apple Mail; Backing up your Mac; Dropbox; FileVault; iCloud; iOS; macOS; Mac Security), or join Tidbits.com (30%)
Safer Internet: Privacy, Security, Anonymity
Safer Internet: Privacy, Security, Anonymity
Quotes | Definitions | Analogy | References
Quotes
- "You have zero...
- Pres. Obama: "We don't have a domestic...
- "Right' to privacy?...
- "The only truly secure system is one that is...
- "Privacy is not...
- "We live in a society exquisitely dependent on science and technology,...
Definitions
- Privacy: freedom from observation or attention
- Security: freedom from danger or harm
- Anonymity: freedom from identification or recognition {TCYOP-4: 17}
- Advice, settings and tools may affect more than one of these, and be repeated for different topics
Analogy: paper postal mail
- Privacy: postcard vs. envelope
- Security: stolen check or ID; white powder; locked mailbox
- Anonymity: no return address; PO box
 "Before" network diagram: {Figure 1. TCYOP-3: 44; TCYOP-2: 39; TCYOP-1: 39}
"Before" network diagram: {Figure 1. TCYOP-3: 44; TCYOP-2: 39; TCYOP-1: 39}
References
- {TCYOP-3: 15; TCYOP-2: 14; TCYOP-1: 17}
- sections: Refs:Analogies
- What is the Internet? OLLI course: Internet History and Issues
- topics: definitions, myths, quizzes
- The Privacy Project: introduction, article series NYT; 4/10/2019
- Note to Self podcast episodes
- The Privacy Divide Stories
- Wikipedia: Internet Privacy; Internet Security; Anonymity
- Wikipedia: Electronic Frontier Foundation (EFF); eff.org
- HowStuffWorks: Computer & Internet Security
- HowStuffWorks: Top 5 Internet Myths
Al Gore Invented the Internet; Your ISP is Tracking Your Every Move;
The Internet is Filled With Sexual Predators; The Internet Will Make You Rich;
Everything You Read on the Internet is True - HowStuffWorks. Quizzes: Internet Fact or Fiction (10); Internet Myths (20);
Internet Advanced (10); Internet World Records (10); Computer History (20) - Internet - How does it work? video: 1:47
- The New Terminology for Privacy the language of digital privacy is changing; NYT; 4/10/2019
- A Bibliography on Privacy A running list of some of the best writing
on the intersection of technology and privacy; NYT; 4/10/2019
Analogies
- Wikipedia: Internet metaphors; public-key cryptography: symmetric vs. asymmetric encryption
- Analogy between the postal network and TCP/IP layers: application, transport, internet, data link, physical
Safer Internet: What Do You Have to Hide?
Safer Internet: What Do You Have to Hide?
Quotes | Summary | Who's at Risk | Types of Info | Identify Theft, Credit Freeze | Farfetched Example? |
References: General | Attacks,Leaks | Equifax, Credit Bureaus & Freezes |
Face | Financial | Health | Home | Identity Theft | Location | Vehicles | Voting
Quotes
- "What happens in Vegas...
- "There are only two types of companies...
- "If you give me six lines written by the hand of the most honest of men,..
- "If you think it, don't say it. If you say it,...
- "Data is the new...
- "We live in what's called an open society, which of course means...
- "Even if you're not doing anything wrong,...
- "Surveillance is the...
- "Reality #1: Bad guys already have access to...
- Your data -- the abstract portrait of who you are, and, more importantly,
of who you are compared to other people -- is... - "I give the fight up: let there be an end, a privacy,...
- "Arguing that you don't care about the right to privacy
because you have nothing to hide... - "It's impossible to move, to live, to operate at any level...
- "The internet is just...
- "Some might say 'I don't care if they violate my privacy; I've got nothing to hide.'...
- "My name is Avery Ryan. I was a victim of cyber crime...
Summary
- Who's at Risk? have SSN? use credit card? post on social media? read privacy policies? high-profile?
- Types of Info contacts, financial, location, medical, passwords, ...
- Identify Theft, Credit Freezes
- Example -- farfetched, or is it?
- References
Who's at Risk?
- Everyone's information, even a fragment, can valuable to someone for
profiling, money (e.g., advertisers, hackers) and/or control (e.g., governments, abusers). - [1] Anyone who has ever had a loan or credit card -- very likely affected by 9/2017 Equifax breach
- [1] Anyone whose SSN, email or other sensitive details have been
or will be leaked by a careless company or incompetent government agency - [1] Anyone who's posted to Facebook or other social media
- [1] Anyone unaware of current recommended privacy and security practices.
- [2] Anyone who's read privacy policies and changed some settings -- there's always more to review / do
- [3] Any high-profile target: celebrity, politician, business, political dissident,
investigative journalist, whistleblower
Types of Info
- Contact information: home address, phone, email -- yours and family
- Vital Statistics: your birthday, birthplace, family members
- Financial information: SSN, credit cards, purchases, tax returns, bank statements
- Your current and past locations -- via smartphone or car
- Photos
- Medical information: health records, DNA
- Biometrics: fingerprints, face scans, movement (motion sensors)
- Password(s): if a password is stolen, login to that site and change it, before a hacker does
-- hopefully, you have devious security question answers
and/or 2-factor authentication for any sensitive accounts. - However, if you re-used that password for other sites -- a big no-no -- you'll have to scramble...
- Email, chat, and other communication history
- Browsing behavior -- current and historical {List. TCYOP-4: 87-98; TCYOP-3: 73-74}; browser 'footprint'
- Personally-identifiable vs. anonymously-aggregated information; content vs. metadata
- Data across different sites via cookies or IP address (or 'browser fingerprint')
can be mined/aggregated to reveal patterns, and lead to individuals - How anonymous/unique are you: zip code + birthdate + gender?
- Other devices: voting systems, (smart)TV, set-top/streaming box, game console,
smart watch, health/fitness trackers, home automation, car; section: "Internet of Things" (IoT) - Others' devices: cameras, wearable technology
- NYT quiz: How Many Times Has Your Personal Information Been Exposed to Hackers?
- NIST Quiz: Are you Safe Online?
- Pew: Cybersecurity Knowledge Quiz
- haveibeenpwned.com check if you have an account that has been compromised in a data breach;
pwned (gaming term) = totally dominated, conclusively defeated - HPI Identity Leak Checker check whether your email address, along with other personal data
(e.g. telephone number, date of birth or address), has been made public on the Internet
where it can be misused for malicious purposes
Identity Theft
- A good place to start: FTC: identitytheft.gov
- 2023 cyber-attacks targeted a vulnerability in the MOVEit filesharing technology used by
many federal & state agencies and corporations around the world. This exposed personal information
of millions of people, including social security numbers in many cases. - e.g., MOVEit hack spawned over 600 breaches but is not done yet -- cyber analysts Reut; 8/8/2023
- Your bank or financial institution may offer a free credit monitoring service; set up credit freezes (below).
- If you have ever had a loan, mortgage or credit card,
you are very likely affected by the Equifax breach (9/2017)
-- with at least your birthdate, name, address, SSN available to hackers worldwide - Equifax grand leak total (5/2018): 146.6 million names, 146.6 million dates of birth,
145.5 million social security numbers, 99 million addresses
and 209,000 payment cards (number and expiry date) exposed;
also 38,000 American drivers' licenses and 3,200 passport details - You may be vulnerable due to other past or future leaks
from other companies or government agencies with sloppy security. - However, there are still some things you can do to minimize the damage
-- many of them free (with some redundancy) - Closely monitor credit card activity for unrecognized charges
with your credit card companies -- at least monthly, but preferably more often. - Set up SMS and/or email notifications and fraud alerts with your credit card company
for charges over certain amounts or from certain sources, esp. online, international. - Check your credit report & score, e.g., annualcreditreport.com free; creditkarma.com
- If your credit card is missing or stolen, in addition to checking your report,
you can set up notifications/alerts with some credit agencies. - optoutprescreen.com: to reduce mailed credit and insurance offers
which might be stoken from your mailbox; opt-out for 5 years (electronically), for life (via mail) - File your income taxes as early as possible -- and setup an online account with IRS
to review past tax returns -- so that a hacker doesn't file early (with your SSN) and claim a refund,
or steal your info/identity: Get Transcript; View Your Tax Account
Check/Freeze Credit Reports
- Freeze credit reports with all 3 major credit reporting agencies
-- to prevent future applications for mortgages, auto loans, credit cards with your SSN - Federal law now requires credit bureaus to offer security freezes free of charge,
and they're much simpler to set up than in the past;
some states used to charge $10; unfreezes should also be free? - A freeze accomplishes the same thing as a lock, but with a freeze, your rights are defined by law.
- With credit locks, the credit bureaus set the rules;
the lock option is more prominent on their websites -- but I've provided direct links for setting up freezes below - If you set up only a lock earlier with EquiFax (or the other agencies),
re-enroll with a freeze; note: any pre-existing lock will be removed, e.g., TrustedID Premier - Save the generated PIN, e.g., in your password manager, in order to unfreeze
when applying later for a new loan or credit card. - Equifax: Freeze
- TransUnion: Freeze
- Experian: Freeze
- Innovis: Freeze; lesser known than the 'big 3' credit agencies, but since it's free, why not?
- National Consumer Telecom and Utilities Exchange for telecommunication, pay TV and utility accounts
- Some credit/identity monitoring services may be free (with ads):
e.g., CreditKarma.com; or included in membership, e.g., ProtectID (AAA) - Credit agencies and others may offer some free credit/identity monitoring services,
but beware of paid upgrades for these and other services -- they're often unnecessary,
duplicative, overpriced, e.g., Equifax: Complete Premier, Family Plan, ID Patrol
do you really want to trust and reward the company (Equifax) that leaked your info in 2017?;
or Lifelock which paid FTC fines for deceptive advertising?
Farfetched Example?
CALLER: Is this Gordon's Pizza? GOOGLE: No sir, it's Google Pizza. CALLER: I must have dialed a wrong number. Sorry. GOOGLE: No sir, Google bought Gordon’s Pizza last month. CALLER: OK. I would like to order a pizza. GOOGLE: Do you want your usual, sir? CALLER: My usual? You know me? GOOGLE: According to our caller ID data sheet, the last 12 times you called you ordered an extra-large pizza with three cheeses, sausage, pepperoni, mushrooms and meatballs on a thick crust. CALLER: OK! That’s what I want. GOOGLE: May I suggest that this time you order a pizza with ricotta, arugula, sun-dried tomatoes and olives on whole wheat gluten free thin crust? CALLER: What? I detest vegetables. GOOGLE: Your cholesterol is not good, sir. CALLER: How the hell do you know? GOOGLE: Well, we cross-referenced your home phone number with your medical records. We have your blood test results for the last 7 years. CALLER: But I do not want your rotten vegetable pizza! I already take medication for my cholesterol. GOOGLE: Excuse me sir, but you have not taken your medication regularly. According to our database, you purchased a box of 30 cholesterol tablets only once, at Drug RX Network, 4 months ago. CALLER: I bought more from another drugstore. GOOGLE: That doesn’t show on your credit card statement. CALLER: I paid in cash. GOOGLE: But you did not withdraw enough cash according to your bank statement. CALLER: I have other sources of cash. GOOGLE: That doesn’t show on your last tax return unless you bought them using an undeclared income source, which is against the law. CALLER: WHAT THE HELL? GOOGLE: I'm sorry, sir, we use such information only with the sole intention of helping you. CALLER: Enough already! I'm sick to death of Google, Facebook, Twitter, WhatsApp and all the others. I'm going to an island without internet, cable TV, where there is no cell phone service and no one to watch me or spy on me. GOOGLE: I understand sir, but you need to renew your passport first. It expired 6 weeks ago.
References
- {TCYOP-3: 13-17; TCYOP-3: 11-15}
- sections: Refs: Attacks,Leaks; Equifax, Credit Bureaus & Freezes; Face; Financial;
Health; Home; Identity Theft; Location; Vehicles; Voting - topics: credit freeze, data imports, dating, DNA, elections, FOIA, haveibeenpwned.com,
hospitals, pacemakers, revenge porn, surveillance - companies/organizations: Anthem, Apple, Ashley Madison, Blue Cross, Comcast, Deloitte,
Delta, Dow Jones, Equifax, Facebook, FDA, Google, Hyatt, IRS, &J, Kickstarter, Lifelock, Medicare,
Orbitz, Panera, Scottrade, Sears, Strava, SWIFT, T-Mobile, Tinder, Uber, Under Armour, Whole Foods - see course sections: Malware: cyberwar, ransomware; Shopping: Payment / Credit Cards
- Wikipedia: Information Privacy; Privacy Law; operations security (opsec)
- Wikipedia: revenge porn sexually explicit media that is distributed without the consent of the individual(s) involved
- Predict My Profile predicts psychological traits from digital footprints of human behaviour, e.g., Facebook or blog posts
- Keep Your Data Secure With a Personalized Plan interactive; choose devices; needs; situations; Consumer Reports
- Security News This Week
each weekend, WIRED rounds up the security vulnerabilities and privacy updates that deserve your attention - How to Remove Your Personal Info From Google by Using Its 'Results About You' Tool set up alerts for whenever your home address, phone number, and email address appears in Search; Wired; 9/3/2023
- Americans Flunked This Test on Online Privacy NYT; 2/7/2023
- How to rescue your hacked account: Facebook, Instagram, Snapchat, and more
Apple, Facebook, Google, Instagram, Snapchat, Spotify, TikTok, Twitter; Verge; 10/17/2022 - The Default Tech Settings You Should Turn Off Right Away
Apple, Google, Meta, Amazon, Microsoft; NYT; 7/27/2022 - Steps to Simple Online Security: Extra security for financial and health data;
What to do if you think you've been hacked NYT; 4/22/2022 - Your Digital Footprint: It's Bigger Than You Realize CNet; 4/4/2022
- 6 Ways to Delete Yourself From the Internet Wired; 1/3/2022
- How a Burner Identity Protects Your Inbox, Phone, and Credit Cards
Private email forwarding: SimpleLogin;
Throwaway email: Maildrop;
Virtual credit card: Privacy;
Second phone number: Google Voice;
All-in-one burner identity: MySudo;
NYT; 6/28/2021 - What Would Happen If All Personal Data Leaked at Once? Giz; 9/7/2020
- 9 Apps to Boost Your Phone's Security and Privacy Wired; 8/16/2020
- Privacy Threats in Intimate Relationships
those closest to us know the answers to our secret questions, have access to our devices,
and can exercise coercive power over us; 6/5/2020 - Giving People Property Rights In Data Will Not Solve Privacy, But... TD; 6/1/2020
- BlackBaud affected SOU Foundation donors; 5/2020
- Work-from-Home Security Advice 3/19/2020
- Here's How to Protect Yourself When Your Data Inevitably Leaks
2FA; different userids/passwords; Giz; 3/4/2020 - Infosec Buzzword Bingo: 2020 Edition MB; 2/11/2020
- Researchers Find 'Anonymized' Data Is Even Less Anonymous Than We Thought MB; 2/3/2020
- Phone Hacks Can Happen to Anyone. Here's How to Protect Yourself.
vacation clues, hotel Wi-Fi and inadequate verification procedures; NYT; 1/31/2020 - Want Your Personal Data? Hand Over More Please NYT; 1/15/2020
- Novelists, poets and artists imagine life in the age of surveillance NYT; 1/3/2020
- The Decade We Learned There’s No Such Thing as Privacy Online
And a corrupt U.S. government seems incapable and unwilling to do anything about it; MB; 12/31/2019 - Why an internet that never forgets is especially bad for young people
Obsessive documentation of one's life online has made it hard for young people to shed their past identities
and might have bad effects for society at large; MIT; 12/27/2019 - What’s the Worst That Could Happen With My Phone Data?
Our Journalists Answer Your Questions NYT; 12/26/2019 - The Worst Hacks of the Decade Stuxnet; Shamoon; Sony Hack; Office of Personnel Management Breach;
Ukrainian Blackouts; Shadow Brokers; 2016 US Presidential Hack; NotPetya; Equifax; Aadhaar; Wired; 12/23/2019 - Freaked Out? 3 Steps to Protect Your Phone directions avail. for And, iOS;
1. Stop sharing your location with apps;
2. Disable your mobile ad ID;
3. Prevent Google from storing your location; NYT; 12/19/2019 - How to Opt Out of the Most Popular People Search Sites
Family Tree Now, Whitepages, Spokeo, Instant Checkmate, Pipl, Intelius; LH; 12/12/2019 - Company Leaves 752,000 Birth Certificate Copy Applications
Publicly Exposed on Amazon Cloud Account Giz; 12/10/2019 - How to Protect Yourself After T-Mobile's Big Data Breach LH; 11/25/2019
- You’re Tracked Everywhere You Go Online. Use This Guide to Fight Back.
Don’t hand over data unless you have to; opt out of advertiser tracking: simpleoptout.com;
check how social media sites are using your data; NYT; 11/24/2019 - Amnesty International says Facebook and Google's omnipresent surveillance
is inherently incompatible with the right to privacy and is a danger to human rights AI; 11/21/2019 - [2] A Paranoid Guide to Fighting the ‘Bugging Epidemic’
With surveillance gear cheaper and easier to use, security experts say checking your environment
for cameras and microphones is not a crazy idea; NYT; 11/15/2019 - This Website Has Solved Cybersecurity ;-) new parody website generates random excuses
to explain why companies got hacked and apologize to their users; MB; 11/6/2019 - Americans and Digital Knowledge Survey of 4,272 US adults shows patchy knowledge on tech issues:
many answered correctly on cookies and phishing, few knew about 2FA, https, or private browsing; Pew; 10/9/2019 - [2] A technical look at Phone Extraction PI; 10/14/2019
- Personal information of most of Ecuador's population, including 6.7M children,
left exposed online with home addresses, phone numbers, work information, more ZD; 9/16/2019 - I Shared My Phone Number. I Learned I Shouldn't Have. NYT; 8/15/2019
- How Many Times Has Your Personal Information Been Exposed to Hackers? NYT; quiz; 7/30/2019
- You're very easy to track down, even when your data has been anonymized
A new study shows you can be easily re-identified from almost any database, even when
your personal details have been stripped out; check your anonymity (w/ zip, birthdate, gender); MIT; 7/23/2019 - Amazon offers $10 to Prime Day shoppers who hand over their data
let Amazon track the websites you visit; Reut; 7/16/2019 - The One Company I Gave My Address To Won't Delete It MB; 7/16/2019
- Selling Your Private Information Is a Terrible Idea rights; NYT; 7/5/2019
- 6 Unexpected Places Hackers Can Find Your Information
1. Social Media
2. E-Commerce Websites
3. Quizzes
4. Search Engines
5. Fitness Trackers
6. Digital Trash Bins; MF; 7/2/2019 - You Care More About Your Privacy Than You Think plus, how to sext securely; NYT; 6/11/2019
- Poor People's Privacy Can't Be an Afterthought NYT; 4/25/2019
- Think You're Discreet Online? Think Again "data inference" technology; NYT; 4/21/2019
- Why You Can No Longer Get Lost in the Crowd NYT; 4/17/2019
- Do You Know What You've Given Up? Introducing The Times Privacy Project; NYT; 4/10/2019
- It's Time to Panic About Privacy We claim to want it, companies claim to provide it,
but we all just accept that, well, you have no privacy online; NYT; 4/10/2019 - Where Would You Draw the Line? The boundaries of privacy are evolving quickly.
Show us where you would set them; survey; NYT; 4/10/2019 - My Phone Knows All, and That's Great Sure, electronic eyes are spying.
But look at all this pocket computer can do! NYT; 4/10/2019 - What the Bible Says About Secrets Scripture offers at least two views of privacy:
It's necessary for a healthy spiritual life, but it also provides a place where sin can be committed; NYT; 4/10/2019 - Education and Science Giant Elsevier Left Users’ Passwords Exposed Online MB; 3/18/2019
- [3] How a Bitcoin Evangelist Made Himself Vanish, in 15 (Not So Easy) Steps
Step No. 10: Buy a decoy house to fool the DMV; NYT; 3/12/2019 - Is Your Seatmate Googling You? We underestimate the risks to privacy in our everyday,
offline lives; experiment to determine difference between the privacy we think we have when we’re in public
and the privacy we actually have; NYT; 3/8/2019 - People Are Concerned About Their Privacy in Theory, Not Practice, Says New Study
81% of consumers say they’ve become more concerned about how companies use their data,
while 87% think companies should be more heavily regulated on personal data management;
apparently it’s not enough for them to take actions in response. 71% said that they were willing
to give up privacy to get access to what technology can offer. Only 45% have updated their privacy
settings on products in response and 16% walked away from a company because of data misuse; Fortune; 2/26/2019 - Your phone and TV are tracking you, and political campaigns are listening in
'digital fence' pushed ads onto the iPhones and Androids of all those attending the meeting.
Not only that, but because the technology pulled the unique identification numbers off the phones,
a data broker could also use the digital signatures to follow the devices home. Once there,
the campaign could use so-called cross-device tracking technology to find associated laptops,
desktops and other devices to push even more ads; possible solutions? VPN, ad blocking,
app settings (or safer apps), TV settings; LAT; 2/20/2019 - Feds share terror watchlist with 1,400 private groups 2/20/2019
- NATO Group Catfished Soldiers to Prove a Point About Privacy
What can we find out about a military exercise just from open source data?
What can we find out about the participants from open source data, e.g., social media?
Can we use all this data to influence the participants' behaviors against their given orders? Wired; 2/18/2019 - The Wired Guide to Your Personal Data (and Who Is Using It)
What Constitutes "Personal Data"? Who Buys, Sells, and Barters My Personal Data?
The History of Personal Data Collection; The Future of Personal Data Collection; Wired; 2/13/2019 - Stolen Internet Account Data AshMUG; .pdf; 2/9/2019
- Why data, not privacy, is the real danger
Personal data harvested at scale and exploited via microtargeting threatens people's autonomy;
they can predict what you’re talking about without actually listening; NBC; 2/4/2019 - Run a Comprehensive Background Check on Yourself
Credit Agencies; Employment Screening; Tenant/Housing Screening;
Bank and Check Screening; Medical Insurance; LH; 1/31/2019 - He Reported on Facebook. Now He Approaches It With Caution.
privacy practices on his devices; NYT; 1/23/2019 - Cyberstalkers are crowdsourcing danger to victims’ doorsteps with dating apps CNet; 1/22/2019
Attacks, Leaks
- haveibeenpwned.com check if you have an account that has been compromised in a data breach;
pwned (gaming term) = totally dominated, conclusively defeated; now available via 1Password - Take These Steps to Protect Your Data After a Cyberattack
if you're a Dish, SlingTV, or Boost Mobile customer, you need to protect yourself now; LH; 4/7/2023 - A look at 2022's worst breaches, leaks, ransomware attacks,
state-sponsored hacking campaigns, and digital takeovers, including at least two Twilio breaches Wired; 12/31/2022 - What to Do if Your Password Is Exposed in a Data Breach Giz; 7/27/2022
- The Worst Hacks and Breaches of 2022 So Far Wired; 7/4/2022
- The Biggest Hacks of 2021 (So Far) Giz; 10/7/2021
- Reset Your Twitch Password Right Now LH; 10/6/2021
- Company That Routes Billions of Text Messages Quietly Says It Was Hacked
hackers had unauthorized access to Syniverse's system for years; Vice; 10/4/2021 - Fallout begins for far-right trolls who trusted Epik to keep their identities secret
colossal hack of Epik, an Internet-services company popular with the far right, has been called the
“mother of all data lodes” for extremism researchers; WaPo; 9/25/2021 - T-Mobile has been hacked yet again -- but still doesn't know what was taken
Data reportedly includes SSNs, driver license numbers,
and more for 100 million people; Ars; 8/16/2021 - Update Your Snapchat Password Immediately
Snapchat users are receiving repeated 2FA login alerts, and no one knows why; LH; 6/24/2021 - Mystery malware steals 26M passwords from 3M PCs Ars; 6/9/2021
- Ten Years Of Breaches In One Image
Nearly 8 billion usernames have leaked since June 2011; Verge; 6/8/2021 - In epic hack, Signal developer turns the tables on forensics firm Cellebrite
to infect investigators' computers; Ars; 4/21/2021 - No password required: Mobile carrier exposes data for millions of accounts
Q Link Wireless made data available to anyone who knows a customer's phone number; Ars; 4/9/2021 - How to Check if Your Phone Number Is in the Huge Facebook Data Leak checker; Giz; 4/5/2021
- Reset Your Ubiquiti Passwords Right Now LH; 4/1/2021
- There's a vexing mystery surrounding the 0-day attacks on Exchange servers
a half-dozen groups exploiting the same 0-days is unusual, if not unprecedented; Ars; 3/11/2021 - Microsoft's 'Crazy Huge Hack,' Explained Exchange Server; Giz; 3/8/2021
- Hackers Just Looted Passenger Data From Some of the World's Biggest Airlines
SITA / Star Alliance; Giz; 3/5/2021 - How A Cybersecurity Firm Uncovered The Massive Computer Hack NPR; 12/21/2020
- More Hacking Attacks Found as Officials Warn of 'Grave Risk' to U.S. Government SolarWinds; NYT; 12/17/2020
- Spotify resets passwords after a security bug exposed users’ private account information
over past 7 months, data exposed may have included email address, preferred display name,
password, gender, and date of birth -- only to certain business partners of Spotify; TC; 12/10/2020 - A hacker is selling access to the email accounts of hundreds of C-level executives
Office 365 and Microsoft accounts of CxO, President, Director, ...; ZD; 11/27/2020 - What to Do About the Data Leak That Hit 8 Major Hotel Booking Sites
Agoda; Amadeus; Booking.com; Expedia; Hotels.com; Hotelbeds; Omnibees; Sabre; LH; 11/9/2020 - How to Know If You’ve Been Hacked, and What to Do About It Wired; 7/19/2020
- A Brazen Online Attack Targets V.I.P. Twitter Users in a Bitcoin Scam
employees who had access to internal systems had their accounts compromised in a
'coordinated social engineering attack'; NYT; 7/15/2020 - Should You Worry About MGM's Latest Data Breach?
142 million MGM Resorts guests; LH; 7/14/2020 - Police Are Buying Access to Hacked Website Data MB; 7/8/2020
- The Worst Hacks and Breaches of 2020 So Far Wired; 7/3/2020
- How Have I Been Pwned became the keeper of the internet’s biggest data breaches
10 billion+ breached accounts; TC; 7/3/2020 - Hacks Are Always Worse Than Reported: Nintendo's Breached Accounts Magically Double TD; 6/10/2020
- What to Do if Your Old LiveJournal Password Was Leaked LH; 5/28/2020
- EasyJet admits data of nine million hacked BBC; 5/19/2020
- GoDaddy Was Apparently Hacked Last Year, So Check Your Hosting Account Credentials Giz; 5/5/2020
- Nintendo account hack FAQ: What happened, who's at risk, and how you can secure your ID PC; 4/24/2020
- 10 Billion Wrecked Accounts Show Why You Need 'Have I Been Pwned' LH; 4/9/2020
- Marriott says 5.2 million guest records stolen in another data breach TC; 3/31/2020
- Dear Ashley Madison user. I know everything about you. Pay up or else.
Emails threaten to publish intimate details unless members pay a hefty ransom; Ars; 2/1/2020 - Iranian hackers have been 'password spraying' the US grid
State-sponsored group "Magnallium" has been probing US utilities for the past year; Ars; 1/12/2020 - Not so IDLE hands: FBI program offers companies data protection via deception
FBI's IDLE program teases thieves with 'decoy data'; Ars; 12/20/2019 - It's Time to Secure Your Zynga Account LH; 12/19/2019
- T-Mobile says it suffered a data breach that affected over one million customers,
exposing their names, billing addresses, phone numbers TC; 11/22/2019 - Hackers breached Macy’s website and hijacked customers’ payment info TNW; 11/19/2019
- 7.5 Million Adobe Accounts Exposed by Security Blunder Adobe Creative Cloud; Giz; 10/25/2019
- Whirlpool Left Appliance Data, User Emails Exposed Online TD; 10/25/2019
- Data Breach Warning For 200 Million Android And iOS Gamers Zynga: Words With Friends; 9/30/2019
- Hackers Stole Data on Nearly 5M DoorDash Users, Including Order History
email address, phone numbers, driver's licenses, and more; TNS; 9/26/2019 - Capital One Data Breach Affects 100 Million; Woman Charged as Hacker NYT; 7/29/2019
- Slack is resetting passwords due to 2015 hack CNet; 7/18/2019
- Sprint says hackers had access to customers' names, billing,
device details, and more via Samsung's website ZD; 7/16/2019 - Gen. Nakasone on US CyberCommand Defending Forward; .pdf; Joint Force Quarterly, #92; Q1/2019
- You have around 20 minutes to contain a Russian APT attack
from initial foothold to full-on breach of your cyber-security defenses; North Korea and China a little longer; ZD; 2/19/2019 - Hacker Lexicon: What Is Credential Stuffing?
attackers take a massive trove of usernames and passwords (often from a corporate megabreach) and try to "stuff"
those credentials into the login page of other digital services. Because people often reuse the
same username and password across multiple sites, attackers can often use one piece of credential info
to unlock multiple accounts; Wired; 2/17/2019 - Marriott now lets you check if you’re a victim of the Starwood hack use checker at own risk; TC; 2/15/2019
- Hacker claims to have posted ~617M online account details stolen from
16 hacked companies for sale on the dark web
MyHeritage and 500px confirm stolen data; Reg; 2/11/2019 - A second, massive Collections leak of 2.2 billion email addresses probably has your information
"Collections #2-#5" leak; PC; 1/31/2019 - [2] Criminals Are Tapping into the Phone Network Backbone to Empty Bank Accounts 'SS7' attacks; MB; 1/31/2019
- Monster 773 million-record breach list contains plaintext passwords to be added to haveibeenpwned.com;
widely circulated "Collection #1" was used in automated credential stuffing attacks; Ars; 1/17/2019 - [2] Some of the biggest web hosting sites were vulnerable to simple account takeover hacks
Bluehost, DreamHost, Hostgator, OVH, iPage; via phishing links; TC; 1/14/2019 - Marriott Concedes 5 Million Passport Numbers Lost to Hackers Were Not Encrypted
far easier for an intelligence service to track people who cross borders; NYT; 1/4/2019
Equifax, Credit Bureaus & Freezes
- TransUnion Failed to Quickly Place or Remove Freezes on Credit Reports
The Consumer Financial Protection Bureau accused the credit bureau, one of three major
credit reporting agencies, of "lying to consumers." NYT; 10/27/2023 - Identity Thieves Bypassed Experian Security to View Credit Reports 1/9/2023
- How to Handle a Suspicious Inquiry in Your Credit Report LH; 10/7/2020
- Your Equifax settlement $125 isn’t coming, but banks get their $5.5M Ars; 5/19/2020
- Equifax Doesn't Want You to Get Your $125. Here's What You Can Do. NYT; 9/16/2019
- Equifax Claims Administrator says victims must provide more info to claim cash
credit monitoring service you already have; Ars; 9/9/2019 - Credit Karma glitch exposed users to other people's accounts TC; 8/14/2019
- Equifax Cash Settlement Backtracking Leaves a Bad Taste TB; 8/5/2019
- The Nitty-Gritty of the Equifax Settlement It may take you a while to get your $125 (or less); Slate; 7/29/2019
- Equifax Claims May Not Get You $125 NYT; 7/29/2019
- You're Entitled to $125 or More in the Equifax Breach Settlement TB; 7/26/2019
- Equifax Data-Breach Settlement: Get Up to $20,000 If You Can Prove Harm NYT; 7/22/2019
- Equifax Is Finally Getting Kicked in the Money Bags Due to Its Disastrous 2017 Hack Giz; 5/23/2019
- Now wanted by big credit bureaus like Equifax: Your alternative data
e.g., phone and electric bills, rent, and payments to many types of credit providers such as payday lenders,
rent-to-own stores, and online personal lenders; 4/6/2019 - MyEquifax.com is yet another security disaster
need to provide SSN and DOB, but they were leaked earlier; TC; 3/8/2019 - The great Equifax mystery: 17 months later, the stolen data has never been found
not on dark web; experts are starting to suspect a spy recruitment scheme; CNBC; 2/13/2019 - Year of Free Credit Report Monitoring Is Ending. Here's What to Do Now.
switch to free credit freeze instead of lock; NYT; 1/11/2019
Face
- A Face Search Engine Anyone Can Use Is Alarmingly Accurate
PimEyes, $30/mo.; NYT; 6/26/2022 - Are ‘10-Year Challenge’ Photos a Boon to Facebook’s Facial Recognition Technology? NYT; 1/19/2019
Financial
- IRS to adopt Login.gov as user authentication tool 2/22/2022
- IRS says taxpayers wanting to access their accounts online will not be subjected to facial recognition if they choose to ID themselves in "a virtual interview" NYT; 2/21/2022
- To Get the Most From Social Security, Log On
a variety of online tools can guide retirees looking to make the most of this benefit; NYT; 1/28/2021 - Hacker Tricked Robinhood Support Into Revealing Data Of 5 Million Users TD; 11/15/2021
- Robinhood Hack Compromises Millions of Customer Email Addresses and Names Giz; 11/8/2021
- Use This IRS Security Tool to Protect Yourself From Refund Fraud
Identity Protection PIN Opt-In Program; info; Giz; 12/4/2020 - Some Robinhood users say someone sold their investments and withdrew funds;
Robinhood says users' personal email accounts were compromised, not its systems BB; 10/9/2020 - How Not to Become a Victim of Social Security Fraud Calls NYT; 3/6/2020
- Intuit Is Buying Credit Karma. Should You Cancel Your Account?
effect on Equifax settlement? other options; NYT; 2/28/2020 - Why the IRS Wants You to Do Your Taxes Early protect your identity and prevent tax refund fraud; LH; 2/4/2020
- Database exposes names of risky potential bank customers
Convicted criminals and people susceptible to extortion are named in a LexisNexis database; CNet; 12/13/2019 - Google will offer checking accounts, says it won’t sell the data Ars; 11/13/2019
- For Big Banks, It's an Endless Fight With Hackers Capital One, and others; NYT; 7/30/2019
- Credit Scores Could Soon Get Even Creepier and More Biased
based on AI and non-traditional data such as your social media profile; MB; 6/13/2019 - 885 Million Records Reportedly Leaked Online: Bank Transactions, Social Security Numbers,
and More First American Financial (title insurance); Giz; 5/24/2019 - Why Rewards for Loyal Spenders Are ‘a Honey Pot for Hackers'
collect vast amounts of personal data, are easy to join and often have flimsy passwords; impersonate customers,
breach loyalty profiles and then tap into separate accounts; deplete balances or sell points on dark web marketplaces; NYT; 5/11/2019 - Stolen Credit Card Numbers Are Now Worth About $15 Each Online
chip cards were supposed to cut down on fraud. They may have just shifted it online; Slate; 5/8/2019 - Mystery data breach reportedly exposes 80 million names, addresses, and income info in U.S.
from an insurance, healthcare, or mortgage company? PC; 4/29/2019 - Checking on Social Security Estimates Is a Good Idea, but Many People Don't Do It
shift from paper; NYT; 4/12/2019 - A.I. Is Changing Insurance Some technologies are better left in the laboratory; NYT; 4/10/2019
- Personal Data of 2.3 Million Disaster Victims Was Released by FEMA, Report Says NYT; 3/22/2019
- How to Outsmart the Most Common Money Scams hang up the phone; prevent credit card fraud; LH; 3/1/2019
Health
- HowStuffWorks: Will your electronic medical record be safe?
- I'm Worried About My Dad's Heart. So We Got Him an Apple Watch CNet; 12/23/2022
- How to protect your privacy when using mental health care apps NPR; 7/18/2022
- In a Post-Roe World, the Future of Digital Privacy Looks Even Grimmer NYT; 7/13/2022
- 11 Online Privacy Tips for Getting an Abortion Giz; 5/6/2022
- How to Protect Your Digital Privacy if Roe v. Wade Falls Wired; 5/5/2022
- How to Carry Your Covid Health Data on a Smartphone
add SMART Health Cards to Apple and Google wallet apps;
save a photo; NYT; 12/1/2021 - The Garmin Ransomware Hack Is Horrifying
fitness tracking companies are vulnerable troves of sensitive data and aren't taking your privacy seriously; MB; 7/28/2020 - Despite qualms from some experts, Google and Apple's exposure notification API
enables the most privacy-respecting approach to contact tracing in history TD; 5/20/2020 - Emergency Surveillance During COVID-19 Crisis 3/20/2020
- Why is the healthcare industry still so bad at cybersecurity? Ars; 2/9/2020
- Inside Google's Quest for Millions of Medical Records WSJ; 1/11/2020
- A tweet gave a journalist a seizure. His case brings new meaning to the idea of 'online assault.'
GIF that strobed violently across his computer screen, flashing a red, yellow and blue geometric pattern behind the words
"YOU DESERVE A SEIZURE FOR YOUR POSTS"; WaPo; 12/16/2019 - What to Consider Before Trading Your Health Data for Cash NYT; 11/27/2019
- How to Lock Down Your Health and Fitness Data Wired; 11/17/2019
- Google: You can trust us with the medical data you didn’t know we already had
Google has 50M people's medical records but won't merge them with other Google data; Ars; 11/13/2019 - Popular health websites in UK are sharing sensitive user data with dozens of companies
including Google and Facebook along with data-brokers and adtech firms FT; 11/12/2019 - Anyone Can Look at Millions of Americans' Medical Images and Data, Report Finds
187 servers in the U.S. that lacked passwords or basic security precautions; data from more than 16 million medical scans
worldwide are available online; some scans include sensitive information such as names, birthdates, and in some cases,
Social Security numbers; ProPublica; 9/17/2019 - When Apps Get Your Medical Data, Your Privacy May Go With It NYT; 9/3/2019
- These Hackers Made an App That Kills to Prove a Point Medtronic insulin pumps; Wired; 7/16/2019
- How to Protect Your DNA Data Before and After Taking an at-Home Test
privacy policies; larger (more accountable) companies; NYT; 6/12/2019 - Researchers: 33 of 36 apps for depression or smoking cessation shared data
with third-parties and 2 apps shared very sensitive info, like health diary entries
Do I trust the person who made the app, and do I understand where this data is going? Verge; 4/20/2019 - Making Babies in the Year 2045 Huge pools of health data collected over the past generation
allow you to pick many of your child's genetic traits. Are you comfortable with that? NYT; 4/10/2019 - Homeland Security warns of critical flaws in Medtronic defibrillators TC; 3/22/2019
- Health Apps Can Share Your Data Everywhere, New Study Shows MB; 3/21/2019
- Storing Health Records On Your Phone: Can Apple Live Up To Its Privacy Values? NPR; 2/27/2019
Home
- How Your Landlord Could Be Tracking You
Key fobs and other smart-access technologies make it easier for us to get in and out of our homes
-- but they're also a privacy hazard; NYT; 12/17/2019
Identity Theft
- Wikipedia: Identity Theft; credit freeze aka credit report freeze, a credit report lock down,
a credit lock down, a credit lock or a security freeze; 'In the credit origination process, access to a credit report
is critical for a lender to make a risk assessment. Because a credit freeze effectively stops any access to the credit report,
it places a block in the process of issuing credit. Individuals who freeze their credit reports must therefore unfreeze
their reports before they wish to apply for credit themselves' - HowStuffWorks: How can I find out what information exists about me online?;
How Identity Theft Works; Is there such a thing as a free credit report? - HowStuffWorks: How can I erase my identity and start over?
- About: How To Remove Your Information from Public Websites
- OR: credit freeze, fraud alert; search data breaches
- Privacy Rights Clearinghouse: Consumer Guides
- Protect Yourself From Identity Theft AAA Via, pp 26-27 Nov/Dec 2020
- Should You Use a 'Dark Web Scan' to Protect Your Identity? LH; 10/23/2020
- Never Email Your Social Security Number, I Am Begging You LH; 7/1/2020
- 'Pure Hell for Victims' as Stimulus Programs Draw a Flood of Scammers
criminals have used people’s Social Security numbers, home addresses and other personal information
-- much of which was available online from past data breaches — to assume their identities and bilk them
out of their stimulus checks and unemployment benefits; portal allows people to enter a new bank account
address for the government to send them their money, but it requires only a few pieces of data for verification:
a Social Security number, an address, a phone number and a date of birth; NYT; 4/23/2020 - Scam Awareness Soc. Sec. Admin.: Office of the Inspector General; 1/2020
- Scammers Look for Vulnerability, and Find It in Older People NYT; 9/22/2019
- What is a “Dark Web Scan” and Should You Use One? 3/26/2019
- How Do Scammers Know So Much About Me?
they're good sleuths, but too often we give our data away; AARP; 1/9/2019
Location
- US Military Is Buying Location Data From Data Brokers,
Including Data Pulled From US App Users TD; 11/20/2020 - Six Reasons Why Google Maps Is the Creepiest App On Your Phone
1. Google Maps Wants Your Search History
2. Google Maps Limits Its Features If You Don't Share Your Search History
3. Google Maps Can Snitch On You
4. Google Maps Wants to Know Your Habits
5. Google Maps Doesn't Like It When You're Offline
6. Google Makes It Seem Like This Is All for Your Own Good;
Vice; 11/12/2020 - The Best Privacy-Friendly Alternatives to Google Maps
easiest to use and most up to date -- use privacy settings; OpenStreetMap; OsmAnd; Apple Maps; Here; Wired; 9/11/2020 - How Your Phone Is Used to Track You, and What You Can Do About It NYT; 8/19/2020
- IRS Used Cellphone Location Data to Try to Find Suspects
the unsuccessful effort shows how anonymized information sold by marketers is increasingly being used
by law enforcement to identify suspects; WSJ; 6/19/2020 - Leaked dataset from a location data company reveals a log of the movements of
12M+ Americans with 50B location pings across major cities between 2016 and 2017 NYT; 12/19/2019 - How to Set Your Google Data to Self-Destruct
option to set search and location data to automatically disappear after a certain time; NYT; 10/2/2019 - Why It's So Easy for a Bounty Hunter to Find You wireless carriers selling location data; NYT; 4/2/2019
- Stalkers and Debt Collectors Impersonate Cops to Trick Big Telecom
Into Giving Them Cell Phone Location Data MB; 3/12/2019 - Russia Votes to Ban Smartphone Use by Military, Trying to Hide Digital Traces
social media revealed actions the Kremlin wanted to keep secret, e.g., in Ukraine, Syria; NYT; 2/19/2019 - Police departments are using 'reverse location search warrants' to force Google
to hand over data on anyone near a crime scene Slate; 2/19/2019 - What A-GPS Data Is (and Why Wireless Carriers Most Definitely Shouldn’t Be Selling It)
'assisted GPS' data is intended for first responders answering 911 calls; MB; 2/7/2019 - Big Telecom Sold Highly Sensitive Customer GPS Data Typically Used for 911 Calls
~250 bounty hunters and related businesses had access to AT&T, T-Mobile, and Sprint customer location data; MB; 2/6/2019 - ‘Businesses Will Not Be Able to Hide’: Spy Satellites May Give Edge From Above NYT; 1/24/2019
Vehicles
- HowStuffWorks: How can you use in-car Internet?
- Mozilla Says Modern Cars Are Data Collection Nightmares on Wheels TB; 9/7/2023
- Carmakers Strive to Stay Ahead of Hackers NYT; 3/18/2021
- Insecure wheels: Police turn to car data to destroy suspects' alibis NBC; 12/29/2020
- This Company Built a Private Surveillance Network. We Tracked Someone With It
9 billion license plate scans accessible by private investigators; MB; 9/17/2019 - DMVs Are Selling Your Data to Private Investigators MB; 9/6/2019
- Your Car Knows When You Gain Weight NYT; 5/20/2019
- There Are Probably Cameras on Your Flight but Relax, They're Not On (Yet); NYT; 4/2/2019
- Locking More Than the Doors as Cars Become Computers on Wheels
Concern that cars could be seriously hacked -- by criminals, terrorists or even rogue governments --
has prompted a new round of security efforts on the part of the auto industry; NYT; 3/7/2019 - Singapore Airlines and American Airlines confirm that some seat screens have embedded cameras
but say they are disabled, after a photo of one goes viral; BF; 2/21/2019 - Where automotive cybersecurity is headed in 2019 TNW; 2/10/2019
Voting
- Internet Voting still insecure
- Voting Security Has Come A Long Way Since 2016 — But Vulnerabilities Remain NPR; 11/3/2020
- Election 2020: a primer on how hackers are targeting the election
and what officials are doing to protect it CNet; 10/27/2020 - 12 Cyber Threats That Could Wreak Havoc on the Election
Attacks on Data, Access, and Availability:
1. Ransomware
2. Advance Voter Data Manipulation
3. Day-of Vote Interruption
4. Actual Vote Manipulation
5. Messing With Reporting
6. Distributed Denial-of-Service Attacks
7. Infrastructure Attacks
Information Operations:
8. Hack-and-Dump
9. Misleading Voting Information
10. Voter-Targeted Disinformation
11. Social Media Threats
12. The Tweeter-in-Chief; Wired; 10/22/2020 - Ransomware Attacks Take On New Urgency Ahead of Vote NYT; 9/27/2020
- Don't Trust Facebook for Voting Information LH; 7/20/2020
- Amid Pandemic and Upheaval, New Cyber Risks to the Presidential Election NYT; 6/7/2020
- Q&A: Eugene Spafford on the Risks of Internet Voting 6/5/2020
- Putin Is Well on His Way to Stealing the Next Election Atl; 6/2020
- A Mobile Voting App That's Already in Use Is Filled With Critical Security Flaws Voatz; MB; 3/13/2020
- Despite Cybersecurity Risks And Last-Minute Changes, The 2020 Census Goes Online NPR; 3/2/2020
- 1 Simple Step Could Help Election Security. Governments Aren't Doing It using .gov domain; NPR; 1/29/2020
- 2020 Political Campaigns Are Trying To Avoid A 2016-Style Hack NPR; 1/28/2020
- New election systems use vulnerable software
vast majority of 10,000 election jurisdictions nationwide use Windows 7 or an older operating system to create ballots,
program voting machines, tally votes and report counts; lack of federal requirements or oversight; AP; 7/13/2019 - Hacking, Glitches, Disinformation: Why Experts Are Worried About the 2020 Census NYT; 7/3/2019
Safer Internet: Who Wants Your Private Data?
Safer Internet: Who Wants Your Private Data?
Quotes | Summary |
References: General | Companies | Government | Hackers, Trolls, Doxers
Quotes
- The best minds of my generation are thinking about...
- "Information on the Internet is subject to the same rules and regulations as...
- "The big thing I learned is that it's not possible to navigate the modern world...
- Common data breach responses:...
- "The debate about data security is not about choosing security or choosing privacy...
- "I got a call last night during dinner from Verizon asking me...
- "If the government has been monitoring my phone conversations,...
- "I signed up for a new calling plan today...
Summary
- Does a 'free' service require you to provide personal data or view ads?
- How do social media, advertisers, your ISP/cell provider, "Big Data" to support 'free' content or generate revenue?
- Employers, neighbors, stalkers, a vindictive ex
- Banks, lenders, and insurance companies
- Hackers
- "Big Brother": the government and law enforcement. NSA, GCHQ (UK), FBI, CIA, DOJ, TSA, ...
-- since 9/11, anything goes for 'war on terror' - Major copyright holders (RIAA, MPAA)
- [2] Request what companies are storing about you, then perhaps make changes to permissions and settings to minimize what's collected and shared. A few companies that provide such a 'data dump':
- Apple: Privacy (portal); privacy.apple.com > Get a Copy of your Data
- Facebook: My Account > Sign-in & security > Apps with account access; Settings > General > Download a copy of your Facebook data > Download Your Information > View : customize: dates, type/quality of info; Create File; (wait); expand .zip, open index.html in browser
- Google: Takeout: create an archive with your data from Google products
References
- {TCYOP-4: 18-28; TCYOP-3: 16-28}: Advertisers; Your ISP; The Google Problem; Data Brokers; Local Villains; Doxxers; Hackers; Big Media; Big Money; Big Data; Big Brother; Privacy Policies
- sections: Refs: Companies; Government; Hackers, Trolls, Doxers
- topics: banks, China, darkpatterns, doxing, EU, GDPR, police, Russia, Snowden, spyware, surveillance, Terms of Service, Wyden
- companies/organizations: Adobe, Apple, Ashley Madison, ATT, Carnival, CIA, Comcast, DEA, Disney, EFF, Evernote, Facebook, FBI, FCC, Google, Microsoft, NSA, Radio Shack, Target, TSA, Uber, Verizon
- Wikipedia: Internet privacy; Anonymity
- Wikipedia: International Data Privacy Day: Jan 28th
- Wikipedia: Electronic Frontier Foundation EFF; international non-profit digital rights group
- Wikipedia: doxing: researching and broadcasting personally identifiable information about an individual
- Privacy Rights Clearinghouse Privacy Topics
- [3] PrivacyTools.io Privacy? I don't have anything to hide; Global Mass Surveillance -- The Fourteen Eyes; VPN providers with extra layers of privacy; What is a warrant canary? Browser Fingerprint -- Is your browser configuration unique? WebRTC IP Leak Test -- Is your IP address leaking? Excellent Firefox Privacy Addons; Privacy-Conscious Email Providers; Email Clients / Alternatives; Privacy Respecting Search Engines; Encrypted Instant Messenger; Video & Voice Messenger; Encrypted Cloud Storage Services; Secure File Sync Software; Password Manager Software; File Encryption Software; Self-contained Networks; Decentralized Social Networks; Domain Name System (DNS); Productivity Tools; PC Operating Systems; Live CD Operating Systems; Mobile Operating Systems; Open Source Router Firmware
- The Man Who Trapped Us in Databases Hank Asher; NYT; 9/22/2023
- How Mobile Phones Became a Privacy Battleground—and How to Protect Yourself NYT; 9/29/2022
- AI's 6 Worst-Case Scenarios
1. When Fiction Defines Our Reality: deepfakes;
2. A Dangerous Race to the Bottom: speed over safety, testing, or human oversight;
3. The End of Privacy and Free Will: surveillance and tracking;
4. A Human Skinner Box: engagement-based algorithms;
5. The Tyranny of AI Design: biased perspectives and data;
6. Fear of AI Robs Humanity of Its Benefits: over regulation;
IEEE; 1/3/2022 - The State of Consumer Data Privacy Laws in the US (And Why It Matters)
US: no singular law that covers the privacy of all types of data.
Instead, it has a mix of laws that go by acronyms like HIPAA, FCRA, FERPA, GLBA, ECPA, COPPA, and VPPA;
state: only three states have comprehensive data privacy laws (CA, CO, VA);
NYT; 9/6/2021 - The Illusion of Privacy Is Getting Harder to Sell NYT; 8/19/2021
- The Assault on Our Privacy Is Being Conducted in Private NYT; 7/13/2021
- A Case Against the Peeping Tom Theory of Privacy Wired; 2/15/2021
- He Created the Web. Now He’s Out to Remake the Digital World. pods vs. silos; Tim Berners-Lee wants to put people in control of their personal data. He has technology and a start-up pursuing that goal; NYT; 1/10/2021
- Just Collect Less Data, Period. NYT; 7/15/2020
- Trolls, Hackers, Spies: The Cyber Decade MB; 12/26/2019
- 8 Historical Things That Prove Privacy Issues Aren't a Modern Problem MF; 11/11/2019
- How We Spy on Each Other Every Day Technology allows us to do it. Should we? NYT; 10/7/2019
- I Tried Hiding From Silicon Valley in a Pile of Privacy Gadgets Bloom; 8/8/2019
- The Age of Surveillance Capitalism: The Fight for a Human Future at the New Frontier of Power Google, Facebook; she likens the big tech platforms to elephant poachers, and our personal data to ivory tusks. "You are not the product, you are the abandoned carcass."; In exchange for surveillance we get convenience, efficiency and social connection. NYT book review; 1/15/2019
Companies
- Apple Security Research
security reports, real-time status updates, report issues, etc. - The Uber Hack Exposes More Than Failed Data Security NYT; 9/26/2022
- How Americans Woke Up to the Reality of Digital Life in 2022 NYT; 8/23/2022
- You Can Finally Get Your Personal Information Off Google LH; 4/29/2022
- Google Plans Privacy Changes, but Promises to Not Be Disruptive NYT; 2/16/2022
- New Apple Guide Offers Personal Safety Advice TB; 1/31/2022
- Big Data May Not Know Your Name. But It Knows Everything Else
"anonymity" is an abstraction; Wired; 12/19/2021 - Marketers are reacting to privacy laws and Big Tech policy changes with quizzes and other events to collect their own customer info and build detailed profiles WSJ; 12/2/2021
- You Are the Object of a Secret Extraction Operation
democracy; tragedy of the "un-commons"; NYT; 11/12/2021 - The Battle for Digital Privacy Is Reshaping the Internet NYT; 9/16/2021
- What the Privacy Battle Upending the Internet Means for You
more random ads online, higher prices and subscriptions galore; NYT; 9/16/2021 - Google's Privacy Backpedal Shows Why It's So Hard Not to Be Evil NYT; 6/14/2021
- How to see what Google knows about you, and delete it PC; 4/19/2021
- Apple’s C.E.O. Is Making Very Different Choices From Mark Zuckerberg Kara Swisher interview; NYT; 4/5/2021
- Apple is a leader in privacy, but there's still work to be done with the App Store, email, and more MW; 3/3/2021
- A new browser extension blocks any websites that use Google, Facebook, Microsoft, or Amazon it more or less renders the modern web unusable -- and that's the point; Verge; 2/24/2021
- What We Learned From Apple's New Privacy Labels requiring that app makers list the data they collect reveals a lot about what some apps do with our info but creates confusion about others; NYT; 1/27/2021
- Device and Data Access when Personal Safety is At Risk
Update your software
Restoring your device to factory settings
Protect your device
Protect your Apple ID
If you don't recognize a sign-in location
Check privacy settings
Using the Find My app
Sharing your location
Sharing with iCloud
Shared Albums in Photos
Shared Calendars
Sharing your Activity with Apple Watch
Delete unknown third-party apps
Delete unknown configuration profiles
If you use Family Sharing
Phishing and fraudulent requests to share info
Checklist: If you want to see if anyone else has access to your device or accounts
Checklist: If you want to stop sharing with someone whom you previously shared with
Checklist: If you want to make sure no one else can see your location
.pdf; Apple; 12/18/2020 - Google Is Tracking Everything You Do With Its 'Smart' Features -- Here's How to Make That Stop MF; 12/4/2020
- Barnes and Noble confirms it was hacked, says some users' personal information may have been stolen some customers were unable to download purchased e-books; Reg; 10/15/2020
- The Lesson We’re Learning From TikTok? It’s All About Our Data we should minimize how much we share with all of our favorite and not-so-favorite apps; NYT; 9/14/2020
- It Doesn't Matter Who Owns TikTok data flow among intermediaries; Giz; 8/6/2020
- Sen. Ron Wyden helped create the Big Tech industry. Now he wants to hold it accountable. the Senate’s biggest privacy hawk talks about Section 230 and sending Mark Zuckerberg to prison; Vox; 8/5/2020
- I Tried to Live Without the Tech Giants. It Was Impossible. Amazon, Facebook, Google, Apple, Microsoft; NYT; 7/31/2020
- One Of The World's Largest Web Tracking Companies Leaks Tons Of Personal Info From An Unsecured Server TD; 6/22/2020
- How Most Of The Anti-Internet Crew Misread The News That The NY Times Is Getting Rid Of 3rd Party Advertisers like Facebook and Google, it's collecting data on its users, and then using that data to sell access to advertisers -- segmented markets, not selling data exactly; TD; 5/20/2020
- How I fully quit Google (and you can, too) alternatives for: search; Chrome; Hangouts and Google Chat; Google Maps; Gmail; Calendar; Google Docs, Drive, Photos, and Contacts; Google Analytics; Android; TNW; 12/20/2019
- Behind the One-Way Mirror: A Deep Dive Into the Technology of Corporate Surveillance EFF; 12/2/2019
- What Not to Do on Your Work Computer
Don’t store personal files on your work-issued laptop or phone;
Don’t use Google Docs, Slack, or similar tools for anything you don’t want your employer to see;
Assume your internet traffic is monitored;
Be more careful with your computer when you’re in public;
How to see what’s running on your computer; NYT; 12/6/2019 - We Hate Data Collection. That Doesn’t Mean We Can Stop It. NYT; 11/15/2019
- Apple's Revised Privacy Page Provides More Per-App Detail TB; 11/8/2019
- Check Out Apple's Updated Privacy Site LH; 11/7/2019
- How to Automatically Delete Your Google Data, and Why You Should LH; 11/4/2019
- Data brokers like Sift and Kustomer, which share consumers' est. lifetime value with companies, now share it with customers on request due to new privacy laws data like food orders and Airbnb messages; you can request; NYT; 11/4/2019
- How to Tell Google What To Do With Your Data When You Die LH; 10/20/2019
- Apple iOS 13: Is Facebook And Google's Worst Nightmare Coming True? improved privacy settings; Forbes; 9/22/2019
- This Article Is Spying on You The same news organizations that do a great job of reporting on privacy problems -- have privacy problems; NYT; 9/19/2019
- Netflix's 'The Great Hack' Misses The Big Picture The real ‘hack' isn't Cambridge Analytica, Facebook, or the 2016 election. It's the system that made our data tragedies inevitable; MB; 7/26/2019
- Facebook And Google Trackers Are Showing Up on Porn Sites A new study scanned 22,484 pornography sites and found them riddled with trackers from major technology companies; NYT; 7/17/2019
- Why Does Google Know Everything You've Bought on Amazon for the Past Six Years? NYT; 6/4/2019
- A Brief History of How Your Privacy Was Stolen Google and Facebook took our data -- and made a ton of money from it. We must fight back; NYT 6/3/2019
- All the Ways Google Tracks You -- And How to Stop It On the Web; Devices, Audio, YouTube, and Gmail; Targeted Ads and Your Mobile Devices; Wired; 5/29/2019
- [2] A look at Apple's secret testing lab where Secure Enclave chips are subjected to extreme tests and Q&A with Craig Federighi about Apple's commitment to privacy; Ind; 5/28/2019
- Taming the Apex Predators of Tech monopolies; NYT; 5/21/2019
- You're Not Alone When You're on Google Why Do We Keep Telling It Everything? NYT; 5/17/2019
- How to Download Your Entire Amazon Purchase History LH; 4/27/2019
- How Tech Companies Say They Care Companies have said for decades that we should be in charge of our data. Why now, more than ever, does it seem like we aren't? NYT; 4/10/2019
- How Capitalism Betrayed Privacy The forces of wealth creation once fostered the right to be left alone. But that has changed; NYT; 4/10/2019
- Apple wants to be the only tech company you trust amid breaches and scandals, the company is positioning itself as a privacy provider; Verge; 3/26/2019
- Here are the data brokers quietly buying and selling your personal information 121 shadowy companies profiled; FC; 3/2/2019
- Stop saying, 'We take your privacy and security seriously' Common responses:
Lie: 'We take your privacy and security seriously' (if we did, our company wouldn't be profitable)
Deflect: 'All websites constantly experience account takeover attempts' (normal, since everybody has sloppy security)
Defend/Distract: 'There’s no story here; how about some other topic?' (we'd rather not have to explain our incompetence)
Deny: 'No further comment' (we have no clue about what to do next); TC; 2/17/2019 - Why We Can't Break Up With Big Tech Amazon, Facebook, Google, Microsoft and Apple; "The big thing I learned is that it's not possible to navigate the modern world without coming into contact with these companies." The exception? Apple. Hill says when she gave up her iPhone and stepped out of Apple's "walled garden," she had no trouble staying away from the company — and it wasn't collecting data on her; NPR; 2/10/2019
- Goodbye Big Five: Life without the Tech Giants Amazon, Facebook, Google, Microsoft, and Apple collectively make products that we love, products that we hate (but can't stop using), and products that dictate how we communicate and how we are seen. Their devices and services make our lives easier than they've ever been before, yet more complicated in unforeseen ways. Reporter Kashmir Hill spent six weeks blocking Amazon, Facebook, Google, Microsoft, and Apple from getting her money, data, and attention, using a custom-built VPN. Here's what happened; Giz; 1/22/2019
- Week 1: I Tried to Block Amazon From My Life. It Was Impossible. not just an online store -- its global empire also includes Amazon Web Services (AWS), the vast server network that provides the backbone for much of the internet; Giz; 1/22/2019
- Week 2: I Cut Facebook Out of My Life. Surprisingly, I Missed It Giz; 1/24/2019
- Week 3: I Cut Google Out Of My Life. It Screwed Up Everything Giz; 1/29/2019
- Week 4: I Cut Microsoft Out of My Life -- or So I Thought Giz; 1/31/2019
- Week 5: I Cut Apple Out of My Life. It Was Devastating Giz; 2/5/2019
- Week 6: I Cut the 'Big Five' Tech Giants From My Life. It Was Hell Giz; 2/7/2019
- Certificate Wars: A Quick Rundown of Apple's Dustup with Facebook and Google misuing 'Enterprise Certificates' to circumvent Apple’s App Store guidelines for a privacy-busting 'research; app; TB; 2/1/2019
- Apple blocks Google from running its internal iOS apps (now restored); abused "Enterprise Certification" to distribute internal apps to consumers, e.g., Screenwise Meter; other companies that distribute beta versions of their apps to non-employees: Amazon, DoorDash, Sonos; Verge; 1/31/2019
- Apple restores Facebook's ability to run internal iOS apps abused "Enterprise Certification" to distribute internal apps to consumers, e.g., Onavo VPN, then "Facebook Research"; Verge; 1/31/2019
- U.S. regulators have met to discuss imposing a record-setting fine against Facebook for privacy violations for potentially violating a 2011 FTC consent decree; WaPo; 1/18/2019
Government
- see Anonymity: Censorship
- Wikipedia: Search and seizure; 4th Amendment; Searches incident to a lawful arrest phone, computer
- Wikipedia: Third party doctrine US legal theory that holds that people who voluntarily give information to third parties -- such as banks, phone companies, internet service providers (ISPs), and e-mail servers -- have "no reasonable expectation of privacy." A lack of privacy protection allows the United States government to obtain information from third parties without a legal warrant and without otherwise complying with the Fourth Amendment prohibition against search and seizure without probable cause and a judicial search warrant.
- Wikipedia: Surveillance; 2013 mass surveillance disclosures; backdoors
- Timeline of NSA Domestic Spying EFF; 1791-2015
- Keeping Up with the Snoops: series latest surveillance news
- #1 12/10/2013; #2: The 4th Amendment Strikes Back 1/6/2014
- #3: A New Hope 1/30/2014; #4: When the Going Gets Weird 3/13/2014
- #5: A Roundup of Roundups 6/12/2014; #6: A Game of Chairs 8/6/2014
- #7: Too Many Snoops 11/21/2014; #8: Snoop Harder 2/26/2015
- #9: Junk in the PRISM Trunk 4/17/2015; #10 5/8/2015
- #11 backronyms: 'USA PATRIOT' Act = 'Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act;' 'USA FREEDOM' Act = 'Uniting and Strengthening America by Fulfilling Rights and Ending Eavesdropping, Dragnet-collection and Online Monitoring Act'; 6/4/2015
- A look at efforts by 50+ countries to control the data produced by their citizens, governments, and businesses
driven by privacy concerns, economics, and more; NYT; 5/23/2022 - The Top Ten Mistakes Senators Made During Today's EARN IT Markup TD; 2/10/2022
- China Is Winning the Big Data War NYT; 11/30/2021
- Apple will alert users exposed to state-sponsored spyware attacks ApIn; 11/25/2021
- Apple Sues Israeli Spyware Maker, Seeking to Block Its Access to iPhones NYT; 11/23/2021
- I Was Hacked. The Spyware Used Against Me Makes Us All Vulnerable. NYT; 10/24/2021
- How the United States Lost to Hackers NYT; 2/6/2021
- How your digital trails wind up in the hands of the police Phone calls. Web searches. Location tracks. Smart speaker requests; Ars; 12/29/2020
- CBP Refuses to Tell Congress How it is Tracking Americans Without a Warrant U.S. Customs and Border Protection is buying location data harvested from ordinary apps installed on peoples’ phones; MB; 10/23/2020
- What are geofence warrants? TNW; 9/5/2020
- CBP Now Has a Massive Searchable Database for Devices Seized at the Border the US border agency will be able to sift through data extracted from travelers' laptops and cellphones for up to 75 years; MB; 8/24/2020
- Masked arsonist might've gotten away with it if she hadn't left Etsy review woman who burned two police cars IDed by tattoo and Etsy review of her T-shirt; Ars; 6/18/2020
- Your Phone Is a Goldmine of Hidden Data for Cops. Here's How to Fight Back Giz; 6/2/2020
- The Best Apps for Safer Protesting Mobile Justice, Signal, Scanner Radio/Broadcastify, Private Video Recorder, Citizen, Nextdoor, The Photo Investigator/Photo Exif Editor, a good VPN, First Aid, Authy and 1Password; LH; 6/2/2020
- How to Protest Without Sacrificing Your Digital Privacy "clean" phone, or no phone; encrypted messaging apps; disable biometrics; scrub faces; disable location services; MB; 6/1/2020
- You Need This iPhone Shortcut if You're Protesting
Send a text message to one of your contacts, providing your street, latitude, and longitude, along with the message that you're being arrested;
Turn on your iPhone's rear camera and start taking a video;
Save the video to your iPhone when you're done with your recording;
Send said video to your aforementioned contact; LH; 6/1/2020 - The Secretive Company That Might End Privacy as We Know It Clearview AI (facial recognition); NYT; 1/18/2020
- NSA Security Awareness Posters; favorites: BBC, Motherboard
- Cloudflare Removes Warrant Canary: Thoughtful Post Says It Can No Longer Say It Hasn't Removed A Site Due To Political Pressure TD; 12/27/2019
- A Surveillance Net Blankets China’s Cities, Giving Police Vast Powers The authorities can scan your phones, track your face and find out when you leave your home. One of the world’s biggest spying networks is aimed at regular people, and nobody can stop it; NYT; 12/17/2019
- How NSO Group Helps Countries Hack Targets MB; 10/31/2019
- You're in a Police Lineup, Right Now Face-recognition technology is the new norm. You may think, "I've got nothing to hide,"" but we all should be concerned; NYT; 10/15/2019
- How ICE Picks Its Targets in the Surveillance Age big data; NYT; 10/2/2019
- How The U.S. Hacked ISIS NPR; 9/26/2019
- Private Surveillance Is a Lethal Weapon Anybody Can Buy Uzbekistan, United Arab Emirates; NYT; 7/19/2019
- Human Rights Watch reverse-engineered the app that the Chinese state uses to spy on people in Xinjiang 5/7/2019
- Will China Export its Illiberal Innovation? Products created for China's vast surveilled and censored domestic market are increasingly popular overseas; NYT; 5/2/2019
- Would You Let the Police Search Your Phone? We are much more likely to give consent than we think; NYT; 4/30/2019
- Losing Our Fourth Amendment Data Protection The courts have shielded information when we have a "reasonable expectation" it will stay private. What happens when we stop believing? NYT; 4/28/2019
- Made in China, Exported to the World: The Surveillance State NYT; 4/24/2019
- The Only Answer Is Less Internet Our emerging post-privacy order isn't quite totalitarian, but it's getting there; NYT; 4/13/2019
- Feeling Safe in the Surveillance State In China, where facial recognition cameras are celebrated as a national triumph, many citizens convince themselves that everywhere else is filled with danger; NYT; 4/10/2019
- A New Age of Warfare: How Internet Mercenaries Do Battle for Authoritarian Governments Sophisticated surveillance, once the domain of world powers, is increasingly available on the private market (NSO Group, DarkMatter, Black Cube, Global Risk Advisors, Cyberpoint). Smaller countries are seizing on the tools — sometimes for darker purposes; NYT; 3/21/2019
- Limiting Your Digital Footprints in a Surveillance State to protect himself and his sources from prying eyes in China, Paul Mozur, a technology reporter in Shanghai, leaves just an 'innocent trace' of digital exhaust; NYT; 2/27/2019
- How Russia Is Strong-Arming Apple Apple Russia is to adhere to a 2014 law that requires any company handling the digital data of Russian citizens to process and store it on servers physically located in Russia. Under Russian counterterrorism laws, Apple could be compelled to decrypt and hand over user data to security services on request; 1/31/2019
Hackers, Trolls, Doxers
- see also: Browsing: Dark Web/Deep Net
- Wikipedia: doxing practice of researching and broadcasting personally identifiable information about an individual
- Wikipedia: swatting act of tricking an emergency service (via such means as hoaxing an emergency services dispatcher) into dispatching an emergency response based on the false report of an ongoing critical incident
- Is cybersecurity an unsolvable problem? book: Fancy Bear Goes Phishing; Ars; 5/27/2023
- This Is Why I Teach My Law Students How to Hack NYT; 5/23/2023
- The Underground History of Russia's Most Ingenious FSB Hacker Group: Turla Wired; 5/20/2023
- 10 of the Best (and Worst) Hacker Movies Giz; 7/10/2022
- Hackers Gaining Power of Subpoena Via Fake "Emergency Data Requests"
via police email accounts; 3/29/2022 - Who is LAPSUS$, the Big, Bad Cybercrime Gang Hacking Tech's Biggest Companies? Giz; 3/26/2022
- The Slander Industry NYT; 4/24/2021
- The Incredible Rise of North Korea's Hacking Army
the country's cyber forces have raked in billions of dollars for the regime by pulling off schemes ranging from A.T.M. heists to cryptocurrency thefts; NYkr; 4/19/2021 - Credit Card Hacking Forum Gets Hacked, Exposing 300,000 Hackers' Accounts Carding Mafia; Vice; 3/26/2021
- Hackers Tell the Story of the Twitter Attack From the Inside NYT; 7/17/2020
- Iranian Spies Accidentally Leaked Videos of Themselves Hacking Wired; 7/16/2020
- Over 15 billion credentials in circulation on hacker forums BC; 7/9/2020
- Russian Criminal Group Finds New Target: Americans Working at Home EvilCorp; NYT; 6/26/2020
- A Guide to Pandemic Scams, and What Not to Fall For Fake Websites; Scam Calls; Email and Text Messages; Network Security; NYT; 5/13/2020
- Domestic Abusers Can Control Your Devices. Here's How to Fight Back. NYT; 4/6/2020
- How International Fraud Rings Operate and Target Older Americans AARP; 4/2/2020
- Someone Tried to Hack My Phone. Technology Researchers Accused Saudi Arabia. NYT; 1/30/2020
- WeLeakInfo gets pwned by FBI; Dutch, N. Irish police arrest alleged breach brokers site aggregated 12 billion usernames and passwords from over 10,000 breaches; Ars; 1/20/2020
- Hacker leaks passwords for more than 500,000 servers, routers, and IoT devices ZD; 1/19/2020
- Toolkit for digital abuse could help victims protect themselves TC; 8/15/2019
- Hackers breached SyTech, a contractor for Russia's FSB, and stole 7.5TB of data about its projects for the agency, including one for deanonymizing Tor traffic ZD; 7/20/2019
- 7 Myths about Hackers and What You Really Need to Look For
1. Myth: Hackers Only Attack Huge Companies.
2. Myth: Hackers Aren't Organized.
3. Myth: Hackers Rush To Get In and Out of Systems.
4. Myth: Hackers Can't See You When You're Browsing Incognito.
5. Myth: Hackers Can't Compromise Smart Phones.
6. Myth: Hackers Can Only Grab Data if Users Download a Malware File.
7. Myth: Hackers Can't Intercept Emails; MF; 7/2/2019 - Here's how digital forensics experts track down hackers TNW; 6/23/2019
- 5 Ways Hacking Will Evolve in the Future
1. Hackers Will Use Our Eyes to Deceive Us;
2. Hackers Might Be Able To Breach Your Data By Touch Alone;
3. Hackers Might Join Your Email Conversations;
4. Hackers Might Take Over Our Assistance Robots;
5. They'll Use Your Computer to Do Their Dirty Work For Them; MF; 5/30/2019 - 6 Unexpected Places Hackers Can Find Your Information social media; e-commerce; quizzes; search engines; fitness trackers; digital trash bins; MF; 5/30/2019
- How Physical Penetration Testers Break Into Supposedly 'Secure' Buildings job relies on people skills and social engineering; MB; 1/30/2019
- Breaking and Entering: The Extraordinary Story of a Hacker Called 'Alien' NYT book review; 1/15/2019
- Hackers dump private information of hundreds of German politicians including email addresses, mobile phone numbers, personal chat transcripts, and photos; Bloom; 1/4/2019
Safer Internet: Develop a Privacy Strategy
Safer Internet: Develop a Privacy Strategy
Summary | Policy/Law | Planning | Behavior | Technology |
References: General | Policy/Law | Plan | Behavior | Technology
Summary
- This course will provide both...
- Parts of a possible strategy:
- Policy & Law, e.g., read privacy policies, lobby government representatives
- Planning, e.g., important services/features vs. privacy & security? tradeoffs; cost? risks?
- Behavior, e.g., strong passwords; backup; update; think before you click or post (or signup)
- Technology, e.g., password manager, encryption
- (References)
Policy / Law
- "Relying on the government to protect your privacy is like...
- "Privacy policies" specify how your information will be used / shared -- no guarantee of protection or enforcement;
if you have some time, peruse -- rather than blindly accept - Privacy policies and settings may protect you against other users, but not against misuse or carelessness by the company itself or its advertising/business partners
- Most companies do not provide details about robustness of their security practices (because they're clueless, embarassed?)
- Terms & Conditions and Privacy Policies can change without notice, usually not for the benefit of users
- e.g., Linkedin: User Agreement (T&C), Privacy Policy; also: Ad Choices; Community Guidelines; Cookie Policy; Copyright Policy
- My Data Request summarizes/links to privacy policies at over 100 different companies
- Government regulations & laws usually lag the technology;
if they exist, they often favor corporate donors, lobbyists and surveillance agencies over consumers
Planning
- "Anything that can go wrong,...
- from EFF: Assessing Your Risks: Threat Modeling:
- "What do you want to protect?"
- "Who do you want to protect it from?"
- "How likely is it that you will need to protect it?"
- "How bad are the consequences if you fail?"
- "How much trouble are you willing to go through in order to try to prevent those?"
- Consider risks & needs by:
- location: home, school, work, vacation
- task: banking, searching, communicating, entertainment
- device: phone, tablet, computer, etc.
- type of information: required, optional, sensitive, personal
- convenience: all mail, calendar, search, payments, passwords with one trusted provider, or different places?
- What is the business product model of companies you use?
- e.g., Facebook, Google (advertising) vs. Apple (hardware)
- How "free" are their services? Do they track you, and sell/share your info?
- How does company respond to mistakes? Do you trust them?
- Will they admit and fix a problem, or deny and repeat?
- If their privacy settings don't protect your data, delete account and/or switch providers?
- Cost of your time & attention: would you rather be doing something else with your life vs. fake news/gossip, cute videos, tweaking settings, ...?
Behavior
- "The only people who like change...
- "Just because you can't do everything...
- "Hoaxes use weaknesses in human behavior...
- "We are all robots when...
- "Denial...
- Accept that some changes are necessary; to get the most out of this class, some homework is required.
- Invest attention and energy upfront to be proactive before problems occur.
- Since it would overwhelming to do everything that we'll discuss immediately, be selective and phase in gradually over months
-- maybe even take the class again next year! - Learn good habits, such as backing up regularly, updating software, choosing strong passwords, storing passwords securely,
logging out when not using your computer; connecting to known, encrypted WiFi networks, etc. - TV / movies often unrealistic when portraying security threats / practices
- Consider eliminating certain sites altogether, e.g., social media
- Before: minimize personal information that you provide / volunteer, e.g., Facebook
- After: inspect companies' data about you -- see What, e.g., Apple, Facebook, Google
- [2] After: purge info from data brokers
- Avoid installing malware inadvertently, e.g., clicking on links in suspicious emails, panicking & responding to scary popups
- "Social Engineering" can often defeat many otherwise secure systems -- especially if request comes from harried "boss",
desperate "friend", incarcerated "grandchild", irate "customer", e.g., phishing, fake sites - Quiz: What's Your Privacy Personality? Are You a Believer, Realist or Shrugger? (scroll to bottom)
-
PICNIC: "Problem In Chair, Not In Computer",
or
PEBKAC: "Problem Exists Between Keyboard And Chair"the "Pledge": don't do anything stupid! {TCYOP-4: 48-50; TCYOP-3: 36-38;}
- [3] Cyberinsurance? Hire Security Consultant? Pray?
| Non-expert Online Practices 1. Use Antivirus Software 2. Use Strong Passwords 3. Change Passwords Frequently 4. Only Visit Websites They Know 5. Don't Share Personal Info |
Expert Online Practices 1. Install Software Updates 2. Use Unique Passwords 3. Use Multi-Factor Authentication 4. Use Strong Passwords 5. Use a Password Manager |
Technology
- "If you think technology can solve your security problems,...
- "Technology is...
- "1) Everything that's already in the world when you're born is just normal;...
- "1) When a distinguished but elderly scientist states that something is possible,...
- A single technology fix may not be adequate: multiple technologies and/or behavior changes may be needed.
- Start by making one-time changes, such as more secure passwords, system & browser settings, privacy options on social networking sites, etc.
- Advice & tools change over time -- security is akin to game of "whack-a-mole"
- Ongoing: check vendor sites for updates; refer back here to course summaries & reference articles
 References
References
- {TCYOP-4: 29-50; TCYOP-3: 29-38}
- see also course section: Intro: Topics: To Do / Check Lists
- sections: Refs: Policy/Law; Plan; Behavior; Technology
- topics: data brokers, security prompts & fatigue, social engineering, threat modeling
- Vendor sites for privacy and security information, e.g.,
- Apple: How We Protect Your Privacy We protect your information on our products. We can create personalized experiences without using personal information. We give developers tools to meet our strict guidelines
- Apple: Security macOS; Software Updates; Gatekeeper; FileVault 2; Privacy Controls; Password Generator; iCloud Keychain; Sandboxing; Runtime protections; Antiphishing; Find My Mac
- Apple: Manage Your Privacy Secure your Devices: passcode; Touch ID, Find My;
Secure your Apple ID: password, security questions, 2-step verification;
Stay secure: phishing, passwords, notifications;
Sharing: iCloud settings, location data, apps, ads, private browsing, children's privacy, diagnostic data - Apple: iOS Security iOS10 white paper: System Security; Encryption and Data Protection; App Security; Network Security; Apple Pay; Internet Services; Device Controls; Privacy Controls; Apple Security Bounty; 3/2017
- Apple: Privacy Built-in; Government Information Requests; Privacy Policy
- TakeControl: Are Your Bits Flipped? trust; excerpt of e-book
- EFF: Surveillance Self-Defense TOC copied: 12/1/2016
- Playlists: Academic researcher? Activist or protester? Human rights defender? Journalism student? Journalist on the move? LGBTQ Youth? Mac user? Online security veteran? Want a security starter pack?
- Overviews: An Introduction to Threat Modeling; Choosing Your Tools; Creating Strong Passwords; Keeping Your Data Safe; Seven Steps To Digital Security; What Is Encryption? Why Metadata Matters
- Animated Overviews: How Strong Encryption Can Help Avoid Online Surveillance; How to Make a Super-Secure Password Using Dice; Protecting Your Device From Hackers; Using Password Managers to Stay Safe Online
- Tutorials: How to: Avoid Phishing Attacks; Circumvent Online Censorship; Delete your Data Securely on Linux, Mac OS X, Windows; Enable Two-factor Authentication; Encrypt Your iPhone, Your Windows Device; Install and Use ChatSecure; Use KeePassX; Use OTR for Mac, Windows, Linux; Use PGP for Linux, Mac OS X, Windows; Use Signal for Android, iOS; Use Tor for Windows, Mac OS X; Use WhatsApp on Android; Use WhatsApp on iOS
- Briefings: An Introduction to Public Key Cryptography and PGP; Attending Protests (Intl., USA); Choosing the VPN That's Right for You; Communicating with Others; How Do I Protect Myself Against Malware? Key Verification; Protecting Yourself on Social Networks; The Problem with Mobile Phones; Things to Consider When Crossing the US Border
- Passcode: Modern field guide to security and privacy CS Monitor; cybersecurity news and analysis
- How to Declutter Your Digital World NYT; 9/15/2020
- Total digital privacy is impossible, but obfuscation, the intentional shrouding of identity with useless information, can be a compromise MIT; 9/27/2019
- What We've Learned From Our Privacy Project (So Far) Surveillance Tools Are Readily Available; We Don't Know Enough About What Happens to Our Data; Privacy Violations Affect Us in Tangible Ways; Sacrificing Your Privacy Might Sometimes Be Worthwhile; 7/16/2019
Policy/Law
- Wikipedia: privacy policy
- A look at the bipartisan American Data Privacy and Protection Act, which privacy experts say might finally give the US a strong federal data protection law Wired; 7/21/2022
- The Messy Progress on Data Privacy NYT; 5/12/2022
- NSA report: This is how you should be securing your network ZD; 3/4/2022
- Companies Use 'Dark Patterns' to Mislead Users About Privacy Law, Study Shows MB; 1/13/2020
- Everything You Wanted to Know about Apple Security but Were Afraid to Ask Apple Platform Security; TB; 12/20/2019
- I Invented the World Wide Web. Here’s How We Can Fix It. Sir Tim Berners-Lee launches Contract for the Web, backed by 150+ organizations including Microsoft, Google, Facebook, and EFF to safeguard the web from abuse; NYT; 11/24/2019
- This AI reads privacy policies so you don't have to -- and it's actually pretty good TNW; 9/24/2019
- We Read 150 Privacy Policies. They Were an Incomprehensible Disaster. NYT; 6/12/2019
- The People Screaming for Blood Have No Idea How Tech Actually Works suddenly regulators' guns are blazing, but it looks thoughtless and is likely to prove pointless; NYT; 6/4/2019
- Your Privacy Is Our Business NYT; 4/27/2019
- How The Times Thinks About Privacy We're examining our policies and practices around data, too; NYT; 4/10/2019
- We're Not Going to Take It Anymore we've given up too much control over our digital lives. We need a law to take some of it back; NYT; 4/10/2019
- What Women Know About the Internet The digital world is not designed to keep women safe. New regulations should be; NYT; 4/10/2019
- Fix It Already: Nine Steps That Companies Should Take To Protect You
Android should let users deny and revoke apps' Internet permissions.
Apple should let users encrypt their iCloud backups.
Facebook should leave your phone number where you put it.
Slack should give free workspace administrators control over data retention.
Twitter should end-to-end encrypt direct messages.
Venmo should let users hide their friends lists.
Verizon should stop pre-installing spyware on its users’ phones.
WhatsApp should get your consent before you’re added to a group.
Windows 10 should let users keep their disk encryption keys to themselves; EFF; 2/28/2019 - Most Online 'Terms of Service' Are Incomprehensible to Adults, Study Finds reading the terms and conditions of online consumer contracts requires, on average, more than 14 years of education; MB; 2/12/2019
- How Silicon Valley Puts the 'Con' in Consent If no one reads the terms and conditions, how can they continue to be the legal backbone of the internet? NYT 2/2/2019
Plan
- EFF: How to Create Your Security Plan
- Security Planner improve your online safety with advice from experts; from Citizen Lab
- Big Companies Thought Insurance Covered a Cyberattack. They May Be Wrong. war exemption; NYT; 4/15/2019
Behavior
- A Paranoid Person's Guide to Preparing for Digital Danger NYT; 3/5/2022
- IT and security professionals think normal people are just the worst 'the well-meaning but negligent end user'; ZD; 4/2/2019
- Internet entrepreneur Arianna Huffington on the next big thing in tech: Disconnecting from it it is time to reevaluate our relationship with technology. If individuals want to thrive in a future dominated by AI and intelligent machines, they will need to create more time and space for human relationships that foster creativity. Less time on smartphones and apps, even disconnecting, will be key; CNBC; 2/9/2019
- Gavin de Becker, Bezos' Security Chief, Is a Guardian to the Stars peace of mind for celebrities, politicians; NYT; 2/7/2019
Technology
- EFF: Security Tips and Tutorials; Security Tool Guides
- Ethical.net: Alternatives & Resources: Browsers; Search engines; Email services; Analytics; Web hosting; Team collaboration; Messaging; Office; File sharing; Video hosting; Tools; Mobile apps; Blogging; Streaming services; Game stores; Social media; Browser extensions; Smartphones; Accommodation & Maps; Organisations; Conferences & Meetups; Magazines; Podcasts; Books; Films & Talks
- Website privacy options are often valid and relevant — but good luck finding them TNW; 11/6/2019
- Taking Steps to Maximize Privacy While Covering the Lack of It investigative reporter Jennifer Valentino-DeVries; NYT; 5/22/2019
- [2] The security threats of neural networks and deep learning algorithms
History shows that cybersecurity threats evolve along with new technological advances. Relational databases brought SQL injection attacks, web scripting programming languages spurred cross-site scripting attacks, IoT devices ushered in new ways to create botnets, and the internet in general opened a Pandora's box of digital security ills. Social media created new ways to manipulate people through micro-targeted content delivery and made it easier to gather information for phishing attacks. And bitcoin enabled the delivery of crypto-ransowmare attacks.
Deep learning and neural networks can be used to amplify or enhance some types of cyberattacks that already exist,e.g., replicate a target's writing style in phishing scams, automate the finding and exploitation of system vulnerabilities. They are overly reliant on data, which means they are as good (or bad) as the data they are trained with. They are opaque, which means we don't know how they function (or fail).
Adversarial examples, inputs that cause neural networks to make irrational mistakes, accentuate the differences between the functions of AI algorithms and the human mind, e.g., computer vision, voice recognition. Data poisoning creates problematic behavior in deep learning algorithms by exploiting their over-reliance on data. Deep learning algorithms have no notion of moral, commonsense and the discrimination that the human mind has. TNW; 1/19/2019
Safer Internet: Offline Data
Safer Internet: Offline Data
Introduction
- There are only 2 kinds of users:...
- What happens to your information if:
- your devices and/or backups are lost, stolen, destroyed or corrupted -- at home or while travelling?
- you neglect to install security updates -- and your system is compromised?
- you lose/forget your passwords?
- you donate or sell your computer?
- you become forgetful, incapacitated, or deceased?
Summary
- [1] Create Strong Unique Passwords -- stored in a Password Manager
- [1] Set strong account passwords / passcodes on computer, tablet, phone
- [1] Backup devices frequently to local and cloud storage; [2] preferably encrypted.
- [1] Update software regularly for system, application and browser (plus extensions)
- [2] Securely erase devices before donating, selling or recycling.
Safer Internet: Offline: Passwords Intro
Safer Internet: Offline: Passwords Intro
| Non-expert Online Practices 1. Use Antivirus Software 2. Use Strong Passwords 3. Change Passwords Frequently 4. Only Visit Websites They Know 5. Don't Share Personal Info |
Expert Online Practices 1. Install Software Updates 2. Use Unique Passwords 3. Use 2-Factor Authentication 4. Use Strong Passwords 5. Use a Password Manager |
Summary
- Passwords are now covered in a separate 3-session OLLI course: P@s$w0rdz
- As an introduction, each section below includes highlights copied from P@s$w0rdz --
each Heading links to the corresponding detailed P@s$w0rdz section for the latest information. - A later section Browse: Protect Passwords originally covered advanced password issues;
it now provides only an updated list of Reference articles about Passwords
Weak Passwords? Stronger Passwords
- "Passwords are like underwear:...
- "The 25 Most Popular Passwords of 2018 Will Make You Feel Like a Security Genius:...
- During a recent password audit, an OLLI student was found using the following password:
"MickeyMinniePlutoHueyLouieDeweyDonaldGoofySacramento"
When asked why such a long password, the student replied...  "Don't use 'beef stew' as a computer password...
"Don't use 'beef stew' as a computer password... - Crossword (by Steve) with weak passwords theme
- Unique: don't reuse passwords on multiple sites; don't login to 3rd-party sites using Google or Facebook credentials (SSO)
- Uncommon, Unpredictable: avoid common words phrases, patterns, etc.; sharing
- Unchanging: change only if they're weak, reused or compromised
- Long: the longer the stronger: 20-64 characters
- Memorable / Typable: you should only need to remember 2+ passwords:
- one for each device: random 8+ digits passcode/PIN for phone;
random 4+ word passphrase for desktop/laptop, e.g.,correct horse battery staple
-- we'll discuss how/where to change these under Accounts - 1 primary password for a password manager, which can generate/store/fill-in everything else
- -- or, Complex / Pastable: normal upper/lowercase, digits, symbols, e.g.,
5iFt*b>Qyk[xpjrz@QoC2exanclhLvQ10izlX8hwxK6i=vwix14dwWVznQkvHrWh - Reinforced: passwords-alone are often not secure enough;
leverage other forms of authentication, if avail.: e.g., 'secret' answers, usernames, 2-Factor Authentication (2FA) - Unknown: other sections of this course will discuss other Privacy & Security practices to keep passwords private
Generate Memorable / Complex Passwords
- Three types of passwords:
- 1. phone PIN/passcode -- memorable & typable; 8+ digits; optional: alphanumeric
- 2. computer/tablet passcode; password manager; some online accounts
-- memorable and/or typable; 4+ word phrases; optional: customize w/ digits, puncutation - 3. most online accounts -- complex & pastable: 20-64 complex character sequences
- Possible random password generators:
- Your imagination -- not so random, really!
- Diceware: roll die 5 times to select a word from a list of 7776 (65) words in some language;
repeat 4+ times to generate a random phrase; e.g., "correct horse battery staple"
-- famous XKCD:cartoon - Diceware-like functionality in macOS and 1Password -- "Memorable"
 OS: e.g., macOS:
OS: e.g., macOS: System Preferences > Users & Groups > Password > Change Password > "key icon": Password Assistant : Numbers Only; Memorable; Random
 a password manager, e.g.,
a password manager, e.g., 1Password > Generate Password: PIN, Memorable, Random- Misc. web sites: quality varies; not so private if site logs trial passwords!
 Test Password Strength
Test Password Strength
- Different web sites can rate the same password differently: Poor, Good, Excellent.
- For more reliable, consistent result use one of these testers:
- OS: e.g., macOS Password Assistant; only up to 31-characters
 a password manager, e.g., 1Password, works for longer sequences
a password manager, e.g., 1Password, works for longer sequences- recommended online tester: zxcvbn
-- zxcvbn also directly embedded in P@s$w0rdz:Testing - optional: disconnect network after loading page to prevent possible password logging (not necessary for zxcvbn).
- below demo heading, enter password/passphrase into input field
- goal for important accounts: entropy value: 75+ -- with crack time: centuries; explanation provided.
Store Passwords Securely
- paper: ok for accounts if well-hidden? good for backup in Safety Deposit Box.
- human memory: good for 2+ strong passwords -- for devices, password file/manager
- browser autofill: avoid -- possible exception: if all Apple devices via iCloud?
- "Single Sign-On" -- avoid entering Google, Facebook, Twitter credentials on 3rd party sites
- computer file: fine if strongly encrypted, e.g., Excel doc via 7-Zip or Keka (AES-256); more manual step;s
- Password Manager (PM): best. features: strong encryption (AES-256); sync/share between devices & family members;
generate random passwords; autofill login credentials, organize/update passwords; credit cards; 2FA support; ...
downsides: learning curve, possible cost - recommended PMs: 1Password, LastPass, Dashlane
Updating Passwords
- Only change passwords if they're weak, reused or compromised -- or site insists on it.
- Check if any of your accounts have been hacked ('pwned')
- Plan an upgrade strategy for many passwords -- to avoid overload / procrastination.
- Use password manager, e.g., 1Password "WatchTower", to proactively identify Reused; Weak; Compromised; Vulnerable passwords.
Security Questions / Secret Answers
- "I don't have a bank account because...
- Some sites use so-called 'secret answers' to questions as a pseudo-authentication factor besides a password.
- However, an answer isn't secret if hackers can find it in public records, from breaches from other sites,
or on social media sites -- don't post such personal details widely, or participate in 'fun' quizzes that reveal this info! - Instead, supply untrue, opposite, misspelled, foreign language, or unpredictable answers -- even random phrases.
- If you're using a password manager, no need to remember these -- just store; then later, copy & paste
Recovery; User Names
- Include email address and possibly phone # in account information, to facilitate account access and possible recovery , e.g., password reset.
- For a primary email account, specify a secondary email address to receive notices about suspicious activity.
- Most sites require an email address as a 'username';
if so, provide a 'permanent' email address (rather than an ISP email address), or an email alias;
if not, provide a unique username (not email) that marketers and hackers can't use to easily correlate your information.
Biometrics
- You still need a strong passcode -- not only for initial setup and after updates / restarts,
but also if you want to grant access to someone you trust or if you injure your finger, face... - A fingerprint or facescan is fairly reliable, and fairly secure (though subject to spoofing).
- Biometrics can be a convenient shortcut to avoid entering device passcode too frequently, but use apprpriate timeouts.
- Be extra cautious if using with important applications / sites, e.g., password manager
- Legally you can be compelled to provide a fingerprint or facescan -- it's considered public;
a password/passcode is considered private ("self-incrimination"), but courts or border crossing agents may try to compel you anyway.
2-Factor Authentication (2FA)
- Although unique user names & random secret answers provide minor additional protection,
for especially important accounts, e.g., financial, email, use a different second "authentication factor" (2FA)
-- in addition to a strong password. - Generally, a good 2nd factor is a temporary code, provided via SMS (texting); issues: spoofing, service access
- Best 2FA is a TOTP (Time-based One Time Passcode) provided via an "authenticator app" or physical token
- Once set up, both the site and app generate -- in sync -- the same, new random code, which changes frequently.
- Examples of authenticator apps: 1Password (built-in), Authy, Google Authenticator, Microsoft Authenticator
Safer Internet: Offline: Accounts
Safer Internet: Offline: Accounts
Summary | Account Password | Permissions | Firmware/SIM |
References: General | Android | Apple ID / iCloud |
iOS | macOS | Windows
Summary
- [1] Set a strong account password / passcode:
on your computer, tablet, phone to protect access: - to still logged-in apps, e.g., messaging, email, browser windows;
- to files -- and encrypt also?
- to contacts
- to notifications, e.g., received (SMS/email) or generated (TOTP) account access codes (2FA).
- Don't forget other devices (IoT): home security/control systems, smart speakers/TV, ...
- [2] Setup separate accounts for each user to control access, e.g., non-admin, Parental Controls
- [2] Use non-admin account for everyday access -- require admin password for software install & updates
- [3] Set passwords for firmware and/or SIM
- References
[1] Set Account Password
- After setting a strong random password: 8+ digit PIN passcode for phone, 4+ word phrase for computers,
- set a suitable timeout to make sure it's required when others might try to access:
- longer: at home -- to minimize inconvenience;
- shorter: in public or travelling;
- immediate: when crossing border or leaving device unattended, e.g.,
- macOS:
(apple) > Lock Screen - There's no handy 'Lock Screen' button in the iOS Control Center;
however, there is a workaround to display the Lock Screen and require a passcode -- maybe simpler to just shutdown device?
in iOS 11, clicking power button quickly 5 times displayed Lock Screen-- now this sequence makes an Emergency Call - iOS:
Settings > Accessibility > Touch > Assistive Touch: on-- enable Assistive Touch (handy if power button broken) - iOS:
Settings > Touch ID & Passcode > iPhone Unlock: off-- disable Touch ID (so fingerprint can't be used on Lock Screen) - iOS:
(assistive button) > Device > Lock Screen-- Lock Screen appears; passcode required - Limit number of login attempts? Auto-erase?
- Add contact info maybe -- in case of loss (vs. Privacy) -- see Services: Location section
- Avoid giving your password to to government entities who might access files, plant files or add spyware
- -- or to tech support, esp. remote scammers; if you do, change it immediately afterwards, scan for malware, etc.
 macOS:
macOS: System Preferences > Security & Privacy > Change PasswordSystem Preferences > Users & Groups > Password > Change Password-- to set initial password, or change other accountsSystem Preferences > Security & Privacy > Require password > (time)- Use same strong admin password for whole disk encryption, i.e., encrypt main storage disk/SSD (FileVault) and backup drive/partitions: incremental (TimeMachine), clone(Carbon Copy Cloner via FileVault) -- see Backup section
 iOS:
iOS: Settings > Passcode > Turn Passcode On- iOS:
Settings > Passcode > Change Passcode > Passcode Options: Custom Alphanumeric Code, Custom Numeric Code, 6-Digit Numeric Code - This code automatically encrypts your information (ditto for Android)
- Use custom -- more than the default (4-6 digit); stronger, plus attacker won't even know length.
- Although letters and symbols can be included, a much longer numeric PIN can be entered more easily on larger number-only keypad;
it would still difficult to brute force, esp. if OS limits login attempts -- unless law enforcement has a bypass cracking device. - iOS:
Settings > Passcode > Require Passcode > After x minutes/hoursshorter when traveling? - iOS:
Settings > Passcode & gt; Allow Access When Locked : Today View, Recent Notifications, Control Center, Siri, Home Control, Return Missed Calls - iOS:
Settings > Passcode > Erase Dataafter 10 failed passcode attempts - iOS:
Settings > Touch ID & Passcodefingerprint sensor on selected models, e.g., iPhone 6 - Win:
Settings > Accounts > Sign-in Options > Password > Add/Change - Enable whole disk encryption, i.e., BitLocker
[2] Setup separate accounts/permissions for each user
- Admin account for installs/updates; 2nd admin backup account
- Non-admin accounts for routine use to avoid accidental malware
- Setup "Parental Controls" on shared computers?
- When: now, or the next time you upgrade your OS or replace hardware, and migrate user info
- macOS:
System Preferences > Users & Groups - Win:
Settings > Accounts
[3] Set Firmware password, SIM PIN
- Prevent booting with other OS, accessing file system (though risk lessened with whole disk encryption)
- Set a SIM PIN on cellular devices, e.g., iPhone, some iPads -- see Connection : WiFi section
References
- sections: Refs: Android; Apple ID; iOS; macOS; Windows
- While my son was tapping away on his home computer, his ten-year-old daughter sneaked up behind him.
Then she turned and ran into the kitchen, squealing to the rest of the family, "I know Daddy's password! I know Daddy's password!"
"What is it? they asked eagerly.
Proudly she replied,... - Wikipedia: User Account; System Administrator
- How to Set Up Lock Screens on All Your Devices Wired; 2/13/2022
- How Do I Get Into My Phone if I Forgot My PIN or Password? And, iOS; LH; 12/11/2020
- The Safest Ways to Log In to Your Computer Win, Mac, Chrome; passwords, key fobs, fingerprints; Wired; 9/13/2020
- How to Protect the Data on Your Laptop strong account authentication; system-wide encryption; use specific app protections (if they're available); enable 'Find My Laptop'; Wired; 8/30/2020
- US district court rules that turning on a phone to view its lockscreen without unlocking it qualifies as searching the phone and would generally need a warrant Ars; 5/22/2020
- District court judge rules that authorities don't have the right, even with a warrant, to force suspects to unlock devices via biometrics Forb; 1/14/2019
Android
- Anyone Can Unlock Your Android Without the Password LH; 11/14/2022
- You're Giving Your Android Apps Too Many Permissions CNet; 7/22/2022
- How to Reset an Apple ID Password from Mac OSXD; 5/19/2021
- How to Set Up 'Guest Mode' on Your Android LH; 6/27/2019
Apple ID / iCloud
- How to Find Your Apple ID, Even When All Seems Lost LH; 10/30/2023
- How to delete an Apple ID account MW; 9/22/2023
- Don't Remove a Stolen iPhone From Your Apple ID (Do This Instead)
scammers have found a new way to trick you into unlocking your stolen iPhone; LH; 12/19/2022 - You can't combine two Apple IDs -- but here's what you can do ApIn; 12/7/2022
- How to create an Apple ID MW; 9/9/22
- How to remove or change the phone number linked to your Apple ID MW; 9/7/2022
- Forgot Your Apple ID Password? Don't Panic, Here's How to Reset It CNet; 7/31/2022
- How to delete an Apple ID account ApIn; 2/23/2022
- How to set up a Legacy Contact for your iCloud account MW; 1/26/2022
- How to Use A Different Apple ID for Game Center on iPhone & iPad
or to Sign Out altogether; OSXD; 1/8/2022 - How to Remove Old Devices from Apple ID on Mac OSXD; 1/7/2022
- How to Get an Apple ID Recovery Key on Mac OSXD; 10/18/2021
- Trying to set a legacy contact for iCloud? You can't do it quite yet MW; 10/6/2021
- How to cut your ex out of your iCloud account MW; 9/23/2021
- How to properly log your devices out of iCloud MW; 9/17/2021
- How to Designate an 'Account Recovery Contact' So You Don't Get Locked Out of Your Apple ID Forever requires iOS 15; LH; 9/14/2021
- How to Delete a Child Account from Family Sharing OSXD; 9/14/2021
- How to Create an Apple ID Recovery Key OSXD; 8/31/2021
- How to Remove a Device from your Apple Account OSXD; 7/10/2021
- How to Change Apple ID Profile Picture on Mac OSXD; 3/19/2021
- Screen Time: How to log out of an Apple ID account when Sign Out is unavailable MW; 3/8/2021
- The Mystery of Dustin Curtis's Locked Apple ID TB; 3/5/2021
- How to set up an Apple ID without a payment method MW; 3/5/2021
- How to split up an Apple ID among family members and forward their email MW; 2/16/2021
- How to check if an unexpected prompt for your Apple ID password is legitimate
iOS: Settings > (account);
Mac: System Preferences > AppleID/iCloud;
Apple's services status web page
MW; 2/12/2021 - How to remove an Apple device from your iCloud account without the device MW; 2/3/2021
- What to do when you forgot your Apple ID password ApIn; 1/18/2021
- How to unify your Apple IDs in macOS for Media & Purchases MW; 12/14/2020
- Apple ID adds recovery key option, but it’s not yet ready for you to use MW; 11/25/2020
- How to merge two macOS accounts into one MW; 9/30/2020
- How to set up a second shared Apple ID for the App Store you can use one Apple ID for media and app purchases and another for email, contacts, calendars, and messaging; MW; 9/2/2020
- Using a school-owned iPad with 2FA? You might run into a problem MW; 8/12/2020
- How to Reset Lost Apple ID from iPhone or iPad OSXD; 7/12/2020
- How to Create an Apple ID without Credit Card OSXD; 6/14/2020
- Migrating to a new Apple ID? Be prepared to lose data for your games MW; 3/23/2020
- How to use Apple ID to create passwords for your 3rd party apps up to 25 app-specific passwords; MW; 1/10/2020
- [2] Why Apple Asks for Your iPhone Passcode or Mac Password with a New Login (and Why It's Safe) TB; 9/26/2019
- Apple ID: How to change your email address If you're about to leave a job or abandon an address, make changes first; MW; 8/30/2019
- Make sure you save your data before deleting an Apple ID account MW; 8/23/2019
- How to Fix a Disabled Apple ID OSXD; 5/11/2019
- How to Create a New Apple ID the Easy Way, from iPhone, iPad, Mac, or PC OSXD; 4/27/2019
iOS
- Apple: Use Touch ID instead of your passcode
- How to bypass a forgotten passcode on iPhone or iPad MW; 3/20/2023
- 4 ways to get into a locked iPhone without the Password ApIn; 12/13/2021
- [2] How to bypass iPhone passcode PassFab iPhone Unlocker; ApIn; 8/2/2021
- Forgot Apple Watch Passcode? Here's How to Reset It OSXD; 7/30/2021
- How to Fix 'maximum number of free accounts have been activated on this iPhone' Error OSXD; 4/26/2021
- How to Get Around Activation Lock on iPhone OSXD; 4/11/2021
- How to Use 6-Digit Passcode on Apple Watch or longer; OSXD; 12/1/2020
- How to See Accounts & Passwords on iPhone & iPad OSXD; 6/24/2020
- What to Do When You're Locked Out of Your iPhone used device? AppleID? LH; 12/13/2019
- How to Find iPad Model Name & iPad Model Number OSXD; 7/13/2019
macOS
- How to recover a forgotten Mac password MW; 1/31/2023
- How to reset a Mac without a password MW; 1/20/2023
- Debugging macOS: Use a fresh new user account to help isolate your problem MW; 12/15/2022
- You Need a New Admin Account on Your Mac
avoid losing admin access yourself from someone untrustworthy, e.g., an ex; LH; 11/11/2022 - How to migrate one user to another Mac MW; 7/1/2022
- New name? Here's how to change the username on your Mac to match MW; 5/23/2022
- Should I shut down my Mac every night? MW; 5/11/2022
- What to do if you can't log into your Google account on your Mac MW; 3/29/2022
- Mac Doesn't Have Admin Account in macOS Monterey or Big Sur? Here’s a Fix OSXD; 3/25/2022
- How to split a macOS account into two MW; 2/25/2022
- How to split a macOS account into two MW; 8/9/2021
- How to set up a guest account and guest sharing in macOS MW; 5/24/2021
- How to Change Keychain Password on Mac OSXD; 4/24/2021
- How to Reset MacOS Password in MacOS Big Sur, Catalina, Mojave OSXD; 4/21/2021
- [2] How to fix the wrong permissions on several files in macOS MW; 1/29/2021
- How to Set up a Used Mac When You Don't Know the User Name or Password LH; 9/13/2019
- How to buy a used Mac without being locked out accounts? firmware pw? FileVault? Find My Mac? iTunes? MW; 7/19/2019
- If macOS's Migration Assistant fails, here are other ways to move accounts MW; 1/7/2019
Windows
- Wife texts husband on a cold winter's morning: 'Windows frozen, won't open.'
Husband texts back: 'Carefully pour some lukewarm water over it and gently tap edges with hammer.'
Wife texts back 5 minutes later... - Microsoft: Create User Account
- How to Sign In to Your Windows PC Without a Password LH; 4/29/2022
- Lock down your Windows PC with a dedicated local administrator account PC; 4/5/2021
- Windows 10 basics: how to change your sign-in settings PIN, fingerprint, picture password; Verge; 5/20/2020
- How to remove your login password from Windows 10 though generally not recommended; PC; 12/20/2019
Safer Internet: Offline: Backups
Safer Internet: Offline: Backups
Quotes | Summary | Where? | Incremental | Complete | Offsite | What I Use | Other |
References: General | Android | Backblaze | Carbon Copy Cloner | Cloud | Death |
Dropbox | Future | Google | Hard Drive/SSD | iCloud | iOS | macOS |
Natural Disaster, esp. Cascadia Quake | OneDrive | Paper/Other | Photos |
Retrospect | SuperDuper | Thumb / USB Drive | TimeMachine | Windows
Quotes
- You can never be too rich, too beautiful,...
- "When was the last time you backed up your work?"...
- Back up my hard drive?...
- "Having been erased,
The document you're seeking
Must now be retyped.
Three things are certain:
Death, taxes, and lost data.
Guess which has occurred.
With searching comes loss
and the presence of absence:
"My Novel" not found.
A file that big?
It might be very useful.
But now it is gone.
Rather than a beep
Or a rude error message,
These words: 'File not found.'" ~Haiku Error Messages
Summary
- "Data loss is when you no longer have access to your own data...
- "Data theft is when someone else gets access to your data illicitly...
- Backup frequency poll (2020) -- never: 19%; annual: 39%; monthly: 20%; 12%: weekly; daily: 10%; ~Backblaze; 6/18/2020
- "3-2-1" backups: 3 copies of your data; 2 different, local methods (formats); 1 offsite
- Disks & solid state drives (SSDs) -- and CDs, DVDs and thumb drives -- will eventually fail /corrupt
- Recover from accidental deletions, theft, ransomware (Malware, Encryption), and incomplete system updates
- 3Rs: Redundancy, Resiliency, Reliability
- 1. Incremental: user files, settings -- to local or network external drive;
often maintains some older file versions -- hourly/daily/weekly; - 2. Complete: user files & settings plus system and applications
-- ideally an exact copy and bootable clone -- to local or network external drive -- weekly/monthly - 3. Offsite: cloud service -- ongoing (with internet connection), preferably automatically;
partial: email, photos, contacts, notes, calendar, e.g., iCloud;
selected files, folders (manually), e.g., iCloud, Dropbox, Google Drive, Microsoft OneDrive;
passwords: synced between cloud & devices via password manager, e.g., 1Password;
complete: cloud backup service such as Backblaze - Backups don't usually take long, e.g., < 30 minutes -- start before a coffee break or meal
- World Backup Day March 31st (just before April Fool's)
- International Verify Your Backups Day every Friday the 13th; TB
- Check periodically that your backups actually occurred and that you can restore files!
- When changing device settings, it's best to 'backup' the current settings, either via paper or screenshot, in case you change your mind.
- References
Where to Backup?
- Device or disk manufacturer may provide backup software, e.g., Time Machine, Retrospect
- What is the total size (used + available) of your internal disk/SSD?
- Option 1: Separate external drives, one for incremental, one for clone
-- if you're concerned about the risk of a single drive failing or disappearing;
some (newer) partitioned drives don't support bootable clones - Incremental (TimeMachine): size: 4x internal -- or more, if you'd like more versions and deleted files to be preserved
- format: Disk Utility > OS Extended Journaled -- Encrypted (recommended); save recovery key!
- you can enable encryption later:
Time Machine Preferences > Encrypt Disk, which uses FileVault also
-- however, enabling later is much s-l-o-w-e-r - Bootable clone(s) [Carbon Copy Cloner]: size: 1x internal -- or more, if you'd like multiple macOS versions, each in a separate partition
- format: Disk Utility > OS Extended Journaled -- not Encrypted; CCC will convert to AFPS format (encrypt later)
- before backing up [first time],
System Preferences > Spotlight > Privacy: exclude backup drives - before cloning [each time], disable any automatic cloud-based backup,
e.g.,Backblaze Preferences > Settings > Schedule > Only When I Click Backup Now - after cloning [each time], renable any automatic cloud-based backup,
e.g.,Backblaze Preferences > Settings > Schedule > Continuously - to encrypt bootable clone backup, option-Restart; in Startup Manager, select backup disk/partition
- after clone booted,
System Preferences > Security & Privacy > FileVault: Turn On; save recovery key! - after clone encrypted, option-Restart; re-select internal disk/SSD
- Option 2: [2] single local external disk partitioned to contain both incremental and clone backups -- convenient and economical; however, some cloned backups might not boot from newer partitioned drives?
- e.g., 1x: 250G (clone); 3x: 750G (incremental; multiple versions/deleted files accessible)
- Option 3: Cloud storage, e.g., iCloud, Backblaze. How secure is the cloud?
- Very -- depending on how files are encrypted and stored, and who has access.
- For brief explanation of different levels of security (via encryption) for Local and Cloud, see P@s$w0rdz:Storing:Encrypt
- Option 4: [2] Shared local network drive (possibly with redundant drive arrays, e.g., RAID)
[1] Incremental Backup
- Backup only what's changed, automatically: user files, multiple versions, settings, contacts, bookmarks
- Frequency: hourly/daily/weekly -- esp. if many files added/changed; also, before any system updates
- Alternatively, you could periodically backup selected files/folders manually to USB drive and/or cloud folder, e.g., DropBox, Box, Google Drive, Microsoft, OneDrive -- but, will you remember to do it?
- macOS:
Time Machine > Open Time Machine Preferences: select disk; Backup Now - (restore):
Time Machine > Enter Time Machine[image] - Win:
Settings > Update & Security > Backup > Backup Using File History - File History tool automatically saves multiple versions of a given file, so you can restore a file before it was changed or deleted
[1] Complete Backup
- A complete, bootable clone contains everything, including applications and system files, and can help you recover from incomplete software updates
- Frequency: weekly/monthly; also, before major system cleanup & updates -- and after successful updates
- iOS (USB):
Finder > Preferences > Sidebar > CDs, DVDs, and iOS Devices - macOS (to disk):
Carbon Copy Cloner - Due to increased security in macOS, backup apps need to be granted permission for 'full disk access':
- macOS:
System Preferences > Security & Privacy > Privacy > Full Disk Access--
apps provide directions, e.g., Carbon Copy Cloner, Backblaze; permission needed also for system cleanup tools like Titanium's Maintenance or Onyx - Win:
Settings > System & Security > Set up backup - Backup and Restore creates a single backup of the latest version of your files on a schedule. It can also create a “system image,” which is a snapshot of your entire system -- operating system, programs, documents, and all -- which makes it easy to restore everything
[1] Offsite: Cloud and/or Other Physical Location
- Store backup(s) somewhere other than your house/office in case your device and local backups are damaged, stolen, hacked, ...
- USB/external disk/DVD at a remote site, e.g., bank Safety Deposit box, trusted friend's house
- For desktop systems, a cloud provider can provide an automatic, complete backup with 'unlimited' storage for relatively small cost, e.g., ~$5/mo.
- Frequency: ongoing
- macOS (to cloud):
Backblaze - Initial backup may take days, depending on number/size of files, and speed of internet connection
- Restore selected files via download; since restoring everything from a remote backup could take awhile, service may ship a loaner drive, e.g., Backblaze
- see References for other products, e.g., Retrospect; Carbonite: Windows ok, but Mac not, due to lack of private keys
- Other cloud options are available for mobile devices and selected data and settings -- often free if default storage used, e.g., iCloud < 5GB
- A password manager can store/sync encrypted passwords, e.g., 1Password on 1password.com, iCloud or Dropbox
- Email backup may not be necessary if using IMAP, i.e., messages already stored on ISP's mail server and cached on each device
- Share -- and backup -- documents & photos via services like Dropbox, Google Drive, iCloud, Microsoft OneDrive
- Back up/sync system settings, bookmarks and certain types of documents and data via iCloud
- iOS:
Settings > (your acct) > iCloud: Photos, Mail, Contacts, Calendars, Reminders, Notes, Safari, News, Home, Game Center, Siri, Keychain, Find My iPad/iPhone, iCloud Backup - iOS:
Settings > (your acct) > iCloud > Storage > Manage Storage > Backups: device; Documents&Data - iOS:
Settings > (your acct) > Family Sharing-- setup - iOS:
Settings > (your acct) > iCloud > Manage Storage > Share With Family-- share iCloud storage - What's shared: Apple media purchases, Apple Music family plans, iCloud storage plans, Photo album, Calendar, Reminders, Locations, Find My iPhone family view
- Not shared: songs in iTunes Match (not purchased in the iTunes Store), in-app purchases, items hidden by a group member, some apps from the App Store (this is left up to each developer)
- macOS:
System Preferences > iCloud: Photos, Mail, Contacts, Calendars, Reminders, Safari, Notes, Keychain, Back to My Mac (File/Screen Sharing), Find My Mac - macOS:
System Preferences > iCloud > Manage... (lower right) - macOS:
icloud.com > Settings (home) > Storage - Is cloud storage safe?
- Encryption depends on the strength & security of the encryption key -- in addition to the password you use to login to cloud provider (plus its security practices)
- Encrypting in transit (via HTTPS:) is assumed; is file decrypted by provider before being re-encrypted?
- If cloud provider has that key, files are vulnerable to hacking or government request -- only you should know / control separate 'private key' (which is not same as login password)
- Conclusion: Extremely secure if file already encrypted 'end-to-end', e.g., password manager;
or cloud service uses a separate (non-account) key which only you have, e.g., Backblaze - Ideally, 2-step authentication is available to protect account login -- section: Passwords
 What I Use
What I Use
- two separate external drives: for TimeMachine and for Carbon Copy Cloner
- cloud services: iCloud, Backblaze
- incremental [ext disk]: macOS: TimeMachine -- files; several times/week
- incremental [cloud]: macOS, iOS: iCloud -- Safari, Settings, etc.; notes; ongoing; 1password.com
- incremental [cloud]: macOS: Backblaze -- all files; ongoing (also external non-backup partitions);
if you subscribe to Backblaze, use this referral link (or code:00gxf7) to receive a free month; Steve receives a free month credit. - complete [ext disk]: macOS: Carbon Copy Cloner -- files, apps, system; monthly, esp. before macOS updates
- complete (via macOS) iOS: files, settings, etc. (Manual) before iOS updates -- see screenshot on right {???}
Other
- [1] Paper: important device & account passwords (esp. for password manager!) in SD box
- [1] Save .pdf of various paper documents, e.g., manuals for devices & appliances from manufacturers sites
- [1] While travelling, backup digital photos to local drive, other device or cloud
- [2] Customize photo storage settings to optimize space, cost, sync time, esp. if you have many GB of photos & devices
- [3] If you host a blog or website, make backups, e.g.,
WordPress.com > Dashboard > Tools > Export
References
- sections: Refs: Android; Backblaze; Carbon Copy Cloner; Cloud; Death; Dropbox; Future; Google; Hard Drive; iCloud; iOS; macOS; Natural Disaster, esp. Cascadia Quake; OneDrive; Paper/Other; Photos; Retrospect; SuperDuper; TimeMachine; Windows; see also Mobile Privacy
- topics: hardware reliability, music, restore
- Wikipedia: Backup; List of backup software; ransomware
- Computer Backup Options pros & cons: manual, external, online (by Backblaze)
- How to Back Up Your Digital Life Time Macine, Backblaze, iDrive, Duplicati; Wired; 3/31/2024
- Back Up and Secure Your Digital Life
product reviews: Hard drive;
Online backup service; Cloud sync;
Local backup software; ... NYT; 3/7/2024 - A Reminder That Trusting Everything to Cloud Storage Can Screw You Over
having just one copy of your files stored anywhere -- even if it's in the cloud -- isn't safe; LH; 11/29/2023 - Start Looking for Drobo and Retrospect (StorCentric) Replacements TB; 5/16/2023
- How to Prepare for a Lost, Stolen or Broken Smartphone NYT; 2/8/2023
- Best file compression apps for macOS and iOS ApIn; 1/27/2023
- International Verify Your Backups Day TB; 1/13/2023
- How to Create a PDF From Any Website, on Any Device LH; 6/21/2022
- The Best Mobile Scanning Apps
Adobe Scan, SwiftScan, Microsoft Lens, Apple Notes; NYT; 5/27/2022 - Do I Really Need to Back Up All My Data? Wired; 4/25/2022
- Steps to Simple Online Security: 6: Backups NYT; 4/8/2022
- How to Back Up Your Computer NYT; 9/29/2021
- How You Can Lose a File Despite Three Layers of Backup (and How To Avoid It) TB; 9/27/2021
- What to do when your laptop is stolen (and how to prepare for it)
Before: Encrypt your data; Keep a current backup;
Enable your laptop’s tracking feature;
After: 1. Locate and lock your laptop (Find My Device);
2. Notify the authorities: File a police report, Tell your bank,
File a claim with your insurance company, Contact your computer manufacturer;
3. Protect your personal information: Wipe your data,
Change your passwords, Disable autofill and clear your browsing data,
Deauthorize your account and devices; PC; 7/14/2021 - The Best Ways to Compress PDFs for Free LH; 6/14/2021
- How to Back Up Your Most Important Emails Forward Emails to a Backup Account; Use POP and IMAP; Download Everything To a Desktop Client; Other Options; Wired; 1/24/2021
- How to Restore Apple Watch from Backup OSXD; 1/19/2021
- How to Backup Your Apple Watch automatically to iPhone; OSXD; 1/16/2021
- Poll Shows Backup Frequency Increasing, Results Still Depressing never: 19%; annual: 39%; monthly: 20%; 12%: weekly; 10%: daily; Backblaze's poll/report; TB; 6/19/2020
- How to create a backup strategy with terabytes of files MW; 1/29/2020
- We're Living in a Subscriptions World. Here's How to Navigate It. avoid losing control of content/data; Maintain Your Own Backups; Create a Personal Entertainment Cloud; NYT; 1/15/2020
- Get Those Records, Tapes and CDs Onto Your Smartphone NYT; 12/25/2019
- Unencrypted hard drives with payroll data, including names, bank account numbers, compensation info of 29,000 Facebook employees, stolen in a car break-in Bloom; 12/13/2019
- You Should Consider Replacing Your Old Surge Protectors every 3-5 yrs? LH 12/8/2019
- Myspace apparently lost 12 years’ worth of music, and almost no one noticed User uploads corrupted in server migration, and Myspace seemingly has no backups; Ars; 3/18/2019
- How to get your Mac or iPhone ready before you take it to Apple's Genius Bar AppleID email and password; device pw; sales receipt; backup! 3/16/2019
- How to Declutter and Organize Your Personal Tech in a Few Simple Steps NYT; 1/23/2019
- How to Delete Your Online Accounts but Keep Your Data Blogger, Facebook, Flickr, Foursquare, Google+, Instagram, LinkedIn, Livejournal, Myspace, Pinterest, Snapchat, Tumblr, Twitter, Whatsapp, YouTube; LH; 1/7/2019
Android
- Manage & restore your device backups in Google Drive
- How to Back Up Your Android Phone Wired; 3/31/2024
- How to share large video files on Android PC; 6/18/2020
Backblaze
- Reminder: if you subscribe to Backblaze, use this referral link (or code:
00gxf7) to receive a free month; and Steve receives a free month credit. - Backblaze 8.5 TB; 9/21/2022
- Backblaze Raises Prices to Address Changing Industry Conditions TB; 7/13/2021
- Backblaze review: No-hassle online backup is a no-brainer decision unlimited storage, no decisions on what to back up, no pressure; PC; 4/20/2021
- The Life and Times of a Backblaze Hard Drive TB; 11/4/2019
- Backblaze 7.0 Extends Version History, Supports Catalina extra $ for file versions beyond 30 days; TB; 10/8/2019
- Behind the Scenes of the Backblaze Price Hike amount of data being backed up increasing faster than the cost of storage was falling; TB; 9/18/2019
- Two Factor Verification via Auth Apps BB; 7/14/2019
- Introducing Furball -- Rapid Content Delivery ;-) BB; 4/1/2019
- Backblaze vs. Cloud Backup Services; Backblaze vs. Cloud Sync Services BB price increases 3/11/2019
- Backblaze Increases Pricing for Unlimited Backup higher prices after 3/11; TB; 2/12/2019
- Backblaze 6.0 Promises "Larger Longer Faster Better" Backups TB; 1/18/2019
Carbon Copy Cloner (Mac)
- Carbon Copy Cloner
- Carbon Copy Cloner 6.1.10 TB; 2/24/2024
- Carbon Copy Cloner Backs Up Cloud-Only Content TB; 10/6/2023
- Carbon Copy Cloner 5.1.26 TB; 5/10/2021
- [2] APFS Bug in macOS 10.15.5 Catalina Impacts the Creation of Bootable Backups MR; 5/28/2020
- Preparing your backup disk for a backup of macOS CCC; 10/29/2019
- Working with APFS Volume Groups CCC; 10/9/2019
Cloud
- Wikipedia: online backup; cloud storage; file hosting; Dropbox
- HowStuffWorks: How Cloud Storage Works; Cloud Quiz
- HowStuffWorks: Do I need to back up files that are already in cloud storage?
- HowStuffWorks: Are my files really safe if I store them in the cloud?
- Take Control E-Books: Cloud, Dropbox, iCloud
- free Take Control Cheat Sheets: Cloud
- The Best Cloud Storage Services Wired; 3/3/2024
- Online backup: We test the best services -- Carbonite, iDrive, Backblaze, Livedrive PC; 8/18/2023
- The best cloud storage services for Apple users Google One/Drive, Apple iCloud, Microsoft OneDrive, Dropbox?; MW; 3/8/2023
- The Best Online Cloud Backup Service Backblaze is top choice now; 1/24/2023
- Cloud Storage Forecast Unsettled, with Possible Storms TB; 2/4/2022
- 7 of the Best Cloud Storage Services That Are Cheaper Than iCloud, Google One, and OneDrive
Microsoft 365 Family: 6TB storage, split six ways;
iDrive: 5/10TB personal storage for the price of 1TB;
TeleDrive: Free, unlimited cloud storage via Telegram;
pCloud: Own cloud storage for your lifetime;
Icedrive: A lot of storage, but privacy first;
Mega: Take 20GB for free, and 8TB for cheap;
WeTransfer: Free, but short-lived data transfer;
LH; 1/12/2022 - How to Recover Any Version of a File
access to your edits in Google Docs, Microsoft Word, and Apple Pages are just a click away; Giz; 6/25/2021 - WD My Book Live users wake up to find their data deleted Ars; 6/25/2021
- How to Prepare for the Next Time the Cloud Goes Down Giz; 8/31/2020
- The Cheapest Cloud Storage Services of 2020 for All Your Files LH; 8/13/2020
- 9 Tips to Keep Your Cloud Storage Safe and Secure
1. Use Strong Passwords and Two-Factor Authentication;
2. Audit Your File and Folder Shares;
3. Clear Out Your 'Deleted' Files;
4. Check Your Connected Apps and Accounts;
5. Turn on Account Alerts;
6. Deactivate Old Devices That Still Have Access;
7. Enable Account Recovery Options; Wired; 7/26/2020 - Cloud storage plans you can use to replace your Mac’s external storage MW; 6/17/2020
- What's the Diff: Sync vs Backup vs Storage BB; 3/31/2020
- Cloud Computing More Energy Efficient Than Initially Thought TB; 3/3/2020
- Dropbox and iCloud Drive: How each service approaches cloud storage different approaches to reducing storage on a local drive; MW; 2/21/2020
- How to Deal with Running Out of iCloud, Google, and Dropbox Space TB; 2/17/2020
- How to Share Files Securely Online Firefox Send, Dropbox, WeTransfer, Google Drive, OneDrive, SendAnywhere, iCloud; Wired; 2/9/2020
- Google Drive vs. Microsoft OneDrive PC; 12/19/2019
- Stop paying monthly cloud storage fees with 3 lifetime options as low as $39.99 limited time; unknown companies? TNW; 11/11/2019
- More From Our Annual Survey: Choosing the Best Cloud for Backing Up types of backup: HD/NAS, cloud backup/drive/sync; BB; 7/16/2019
- [2] Backing Up VM Image Files to Internet Backup Services TB; 5/15/2019
- CloudBerry Backup for macOS: Feature-Rich but Unreliable TB; 3/7/2019
- Backblaze vs. Cloud Backup Services; Backblaze vs. Cloud Sync Services BB price increases 3/11/2019
Death, Divorce
- How to Keep Anyone From Accessing Your iCloud Data After You Die Advanced Data Protection (encryption); LH; 1/26/2024
- How to Close the Social Media Accounts of a Dead Relative LH; 1/3/2024
- Why You Need a Digital 'Dead Man's Switch'
from alerting your family to trouble to ensuring folks have access
to your accounts, there are several reasons to set one up; LH; 9/25/2023 - The Digital Fragments We Leave Behind After Death
the photos, texts, playlists and to-do lists that we find after loved ones die can offer poignant glimpses into their lives; NYT; 5/3/2023 - There may be a problem with Apple's Digital Legacy feature ApIn; 3/7/2023
- What Stories Have You Learned From Digital Messages Left Behind? NYT; 12/15/2022
- Here's What Happens to Your Crypto When You Die LH; 12/8/2022
- You can take it with you: How to destroy the data you leave behind MW; 8/15/2022
- How to Preserve Your Digital Legacy (and Why You Should) LH; 5/10/2022
- How to Leave Your Photos to Someone When You Die Wired; 3/17/2022
- The Morbid War Over Online Obituaries
'Obituary pirates' scrape websites and publish their own versions of death notices, reaping commissions on flowers and gifts; Wired; 12/26/2021 - How to arrange for your digital legacy Verge; 12/2/2021
- How to Decide What Happens to Your Data When You Die Giz; 12/2/2021
- Apple will soon let you pass on your iCloud data when you die
new program coming to iPhones, iPads and Macs, Digital Legacy allows you to
choose five Legacy Contacts who can see your stuff; MW; 11/10/2021 - What Should Happen to Our Data When We Die?
Anthony Bourdain’s A.I.-generated voice is just the latest example of a celebrity being digitally reincarnated.
These days, though, it could happen to any of us; NYT; 7/24/2021 - What to do about Apple devices and iCloud content when the owner dies ApIn; 1/2/2021
- How to recover data from a Mac with T2 or FileVault encryption and without a password short answer: it may not be possible; MW; 11/19/2020
- How to prepare your digital assets in case of death
someone's passing could leave their data and devices locked up forever. But there are some preparations and techniques you could try;
Make a plan before it's too late;
Manage hardware;
Retain account access; MW; 10/21/2020 - A look at startups that provide end-of-life services, from estate planning to online forums for grieving virtually, amid a surge in interest during the pandemic NYT; 7/16/2020
- How to Request Access to a Deceased Family Member's Apple Accounts TB; 6/17/2020
- Estate planning 101: Your guide to wills, trusts and all your end-of-life documents CNet; 6/8/2020
- Can I keep my partner’s Apple purchases and account after they die? MW; 6/4/2020
- What Happens to Your Domain When You Die? expires unless the hosting site exists and you've renewed ($); LH; 12/17/2019
- Twitter halts plan to remove inactive accounts until it can memorialize dead users Verge; 11/27/2019
- Get Your Digital Accounts Ready In Case of Death
1. Share your account logins and other secure information with a password manager
2. Record and save emergency info
3. Set up dead-man switches and assign custody for your digital accounts
4. Drill practice: teach your loved ones how to survive without you; NYT; 10/3/2019 - Please get your digital affairs in order password manager, backup codes; TC; 9/15/2019
- Who Gets Your Digital Assets: Heirs or Hackers? A digital executor can help ensure your heirs inherit online assets while protecting your privacy after death; NW; 8/29/2019
- Here's how billionaires are planning their immortality TNW; 6/28/2019
- We're all going to die -- what happens to our Facebook accounts? Verge; 6/12/2019
- Hacking My Mother's Phone to Save Her Memories After she died, breaking into her phone was the only way to put together the pieces of her digital life; NYT; 6/10/2019
- Dead Facebook users could outnumber the living by 2069 TNW; 4/29/2019
- R.I.P. to a Startling Facebook Feature: Reminders of Dead Friends' Birthdays NYT; 4/10/2019
- Facebook is introducing a new 'Tributes' section for memorialized accounts TC; 3/4/2019
- The weird rise of cyber funerals Digital undertaking is the act of erasing and tidying up your public data after you die -- contacting the social media companies, search engines or even media companies who publish personal information, and request for it to be deleted when their client dies; Wired; 2/17/2019
- What is a Facebook 'legacy contact' and why do you need one? allowed to have limited access to your account after your death; TNW; 2/15/2019
- Planning For Your Digital Legacy In Seven Easy Steps 1. Digital Executor; 2. Inventory Your Digital Assets and How to Access Them; 3. Determine the Terms of Service for Your Accounts; 4. Ensure Your Key Estate Planning Documents Contain Relevant Language; 5. Store Your Information in a Safe Place; 6. Decide and Document the Fate of Your Digital Assets After Your Death; 7. Consult Your Estate Planning Attorney; .pdf; IPPF; 2/2019
Dropbox
- HowStuffWorks: How the Dropbox Mobile App Works
- free Take Control Cheat Sheets: Dropbox
- Dropbox: What does Dropbox do to protect my stuff?
- Had It With the Dropbox App? Here Are Five Alternative Dropbox Clients
Maestral, CloudMounter, Mountain Duck 3,
Transmit 5, Strongsync; MR; 12/1/2021 - Replace a Shared Dropbox File without Changing Its Link TB; 12/13/2019
- Are Dropbox's Paid Plans Worth It? free: 2Gb; Plus($12/mo): 2Tb; Pro($20/mo): 3Tb; LH; 10/4/2019
Future
- A DNA-based storage system with files and metadata
queries can take days, but it's possible to pull out specific files; Ars; 615/2021 - Microsoft's Project Silica offers robust thousand-year storage high purity glass extends storage reliability goals from "decades" to "centuries"; Ars; 11/7/2019
- What Is Google One, and Should You Subscribe? Wired; 3/27/2022
- How to back up your Gmail Verge; 7/28/2021
- Google is finally doing something about Google Drive spam Ars; 7/23/2021
- How to Back Up All of Your Google Data LH; 3/11/2021
- How to Prepare For Google's New Cloud Storage Restrictions LH; 12/7/2020
- How to Access & Edit Google Drive Files from iPhone & iPad OSXD; 6/8/2020
- Google Drive gains an important security feature on iPhone Privacy Screen: authenticate using Touch ID or Face ID; PC; 5/5/2020
- How to get more space in your Google storage clear out the clutter; Verge; 3/19/2019
Hard Drive, SSD
- HowStuffWorks: How to Back Up a Hard Drive
- Best external SSD for Mac MW; 4/15/2024
- How to Choose the Right SSD to Buy LH; 2/21/2024
- Best external drives for backup, storage, and portability PC; 8/14/2023
- The best SSDs: Reviews and buying advice PC; 7/24/2023
- Best external hard drive for Mac MW; 6/26/2023
- Backblaze's 2022 Drive Stats Reveal Manufacturer and Model Reliability Trends drive failures by brand; BB; 1/31/2023
- Best external hard drive and SSD CNet; 11/17/2022
- Backblaze's 2020 Hard Drive Reliability Statistics TB; 2/12/2021
- How Do I Transfer Data When I Switch Out My Laptop's Hard Drive for an SSD? LH; 2/5/2021
- [2] Six Lessons Learned from Dealing with an iMac's Dead SSD TB; 4/27/2020
- The Shocking Truth -- Managing for Hard Drive Failure and Data Corruption BB; 7/11/2019
- How to Partition Your Hard Drive and Why You Would Want To dual-booting OS; emergency recovery partition; Mac: DiskUtility; Win: Disk Management; Giz; 1/22/2019
iCloud (Apple)
- Apple's Advanced Data Protection Gives You More Keys to iCloud Data
requires latest OS on all devices; TB; 12/8/2022 - Apple will finally encrypt iCloud Backups as part of major security push
iOS 16.2 and macOS 13.1 will include several new features to protect your data; MW; 12/7/2022 - How to use iCloud Folder Sharing and replace Dropbox ApIn; 5/30/2022
- Bad Apple #5: iCloud Drive Folder Sharing Risks Data Loss TB; 5/12/2022
- Apple turns off iCloud Documents and Data, but you can still find your files MW; 5/9/2022
- How to Make Sure You Can Recover Your iCloud Data Wired; 4/24/2022
- Apple will soon let you pass on your iCloud data when you die
new program coming to iPhones, iPads and Macs, Digital Legacy allows you to
choose five Legacy Contacts who can see your stuff; MW; 11/10/2021 - How to use iCloud Folder Sharing and replace Dropbox ApIn; 2/23/2022
- Apple releases iCloud for Windows version 13 update MW; 11/10/2021
- How to Share iCloud Storage with Family on Mac OSXD; 11/1/2021
- How to use iCloud Data Recovery Service MW; 10/11/2021
- Apple Outlines Security and Privacy of CSAM Detection System in New Document
Child Sexual Abuse Material (CSAM) scanning on iCloud; MR; 8/13/2021 - How to Share iCloud Storage with Family on iPhone & iPad OSCD; 7/29/2021
- How to Free Up iCloud Storage Space on iPhone & iPad OSXD; 4/21/2021
- Beware! iCloud Backups Deleted after 180 Days TB; 6/11/2020
- How to Sync and Access Your Data Across Devices switch between your phone and laptop seamlessly; Wired; 6/2/2020
- How to Access iCloud Drive Files from Windows PC OSXD; 5/27/2020
- How to use iCloud to cope with a Mac that's low on storage MW; 4/27/2020
- How use your Mac to get more info about your iCloud Drive storage Files for iOS and iPadOS omits nested information on folders; MW; 4/20/2020
- How to Recover Lost or Deleted iCloud Drive Files or Documents OSXD; 2/18/2020
- Folder sharing brings iCloud Drive closer to Dropbox, but there's work left to do MW; 2/7/2020
- How to restore deleted files, photos, bookmarks, and more from iCloud iCloud keeps many items you delete for up to 30 days; MW; 1/2/2020
- How to free up iCloud storage space MW; 1/1/2020
- Find the parts of iTunes now spread throughout different apps in macOS Catalina: Finder MW; 10/21/2019
- How iCloud Drive works with multiple users on a single Mac MW; 10/14/2019
- EFF Calls on Apple to Let Users Encrypt iCloud Backups as Part of 'Fix It Already' Initiative with user's own key; 2/28/2019
- Inside the illicit world of 'iCloud unlocking', where cybercriminals trick iPhone owners or Apple staff into removing an iCloud account to resell the iPhone MB; 2/6/2019
- iCloud storage plans and pricing if you need more than 5 GB of free storageApple; 1/18/2019
iOS
- Apple: Use Quick Start to transfer data from your previous iOS device to your new iPhone, iPad, or iPod touch
- How To Backup Your iPhone iCloud, iTunes, Google Photos; Wired; 3/31/2024
- How to back up an iPhone or iPad MW; 9/8/2023
- How restore an iPhone from a backup MW; 6/29/2023
- How to transfer all your data from an old iPhone to a new iPhone MW; 1/5/2023
- How to Borrow iCloud Storage for Free to Transfer Data to Your New iPhone temporary iCloud backup that can be deleted in 21 days; LH; 9/21/2021
- How to Restore an iPhone Without the Password LH; 9/10/2021
- How to Reduce Your iCloud Backup Data Size on iPhone / iPad OSXD; 5/19/2021
- How to Open & Extract RAR Files on iPhone & iPad iZip; OSXD; 4/16/2021
- Can't Remember Password for Encrypted iPhone Backup? Here's What To Do OSXD; 3/31/2021
- How to set up a backup plan for your Mac, iPhone, and iPad for your New Year's resolution ApIn; 12/31/2020
- iCloud Backup Failed on iPhone or iPad? Here’s How to Fix & Troubleshoot OSXD; 12/19/2020
- How to Restore iOS Backups in MacOS with Finder (Big Sur & Catalina) OSXD; 9/28/2020
- How to get back 'Other' storage on the iPhone or iPad ApIn; 9/7/2020
- How to Backup iPhone or iPad to Windows PC OSXD; 8/24/2020
- How to Delete iOS & iPadOS Device Backups from MacOS Finder in Catalina OSXD; 3/18/2020
- How to open zip files on your iPhone or iPad MW; 2/19/2020
- How to Backup iPhone or iPad to Mac in MacOS Catalina with Finder OSXD; 1/13/2020
- Documents 7 review: Free iOS file manager puts Apple’s Files app to shame Documents 7 is a free iOS app for reading PDF, EPUB, Word, and Excel documents, opening ZIP archives, viewing images, downloading; MW; 1/2/2020
- How to transfer all your data from an old iPhone to a new iPhone MW; 12/24/2019
- Locate backups of your iPhone, iPad, and iPod touch Apple; 12/4/2019
- macOS Catalina: How to make your iPhone and iPad appear on the Desktop
Finder > Preferences > Sidebar > CDs, DVDs, and iOS Devices(incl. iPadOS); MW; 11/11/2019 - How you back up your iPhone and iPad in macOS 10.15 Catalina iTunes app may be gone, but you can still back up your iOS device to your Mac; MW; 7/26/2019
- How to Archive an iTunes Backup of iPhone or iPad OSXD; 7/10/2019
macOS
- Wikipedia: FileVault
- Apple: FileVault 2
- Take Control: Backing Up Your Mac; Online Appendixes; free cheat sheet
- Carbon Copy Cloner; SuperDuper
- Proton Drive encrypted cloud storage service arrives on Mac TC; 11/23/2023
- Getting started with macOS Disk Utility: The basics ApIn; 5/13/2023
- What to do if your Mac is stolen
Preventative measures: enable Find My, strong Lock Screen password, encrypt with FileVault, TimeMachine backup;
Locate your device using Find My; Put your Mac into Lost Mode;
File a police report; File an insurance claim; Erase using Find My;
ApIn; 6/3/2022 - How much storage should you leave unused on a Mac’s SSD? MW; 5/30/2022
- How to Use Extra Space on an APFS Time Machine Drive TB; 5/20/2022
- Disk Utility in macOS 12 Monterey Manages APFS Snapshots TB; 11/11/2021
- How to copy a failing drive to a backup using Mac Recovery MW; 9/3/2021
- How to use Disk Utility in macOS to manage your hard drive MW; 8/25/2021
- How to check if your Mac has a Recovery partition installed MW; 8/20/2021
- How to verify your Mac's drive health using Disk Utility
Disk Utility: First Aid; MW; 7/14/2021 - The best ways to back up your Big Sur Mac
bootable external backup less feasible w/ protected system volume;
focus on Data volume; MW; 6/4/2021 - Apple's moves point to a future with no bootable backups, says developer ApIn; 5/24/2021
- The Role of Bootable Duplicates in a Modern Backup Strategy TB; 2/23/2021
- Can't find the Scheme menu in macOS's Disk Utility? for backwards or multi-platform compatibility; MW; 1/27/2021
- How to restore a previous version of your Pages, Keynote, and other documents in macOS autosave; MW; 12/23/2020
- [2] This quirky method could let you use drives that won’t mount on your Mac after a bad ejection MW; 9/14/2020
- How to Create a New Disk Partition in macOS OSXD; 6/29/2020
- How to clone a macOS Catalina drive Time Machine, Carbon Copy Cloner, SuperDuper; MW; 1/20/2020
- What's the difference between Save, Save As, and Duplicate in macOS apps? MW; 12/16/2019
- How to perform backups more complicated than Time Machine allows ChronoSync; MW; 12/12/2019
- Why you might see a new "Data" disk in Catalina Catalina now splits the operating system and data files into two volumes, but they should never appear on the desktop; MW; 11/6/2019
- How to manage the dance of disk images, Time Machine, and excessively large backups MW; 9/10/2019
- How to Show All Drive Devices in Disk Utility for MacOS OSXD; 8/16/2019
- Don't use cloud backup services to make copies of your Time Machine volumes MW; 8/2/2019
- You need a backup plan before you move to macOS Catalina TimeMachines, online backup services; AI; 7/20/2019
- [3] How to Work with and Restore APFS Snapshots TB; 5/9/2019
- ChronoSync 4.9.2 TB; 3/6/2019
- The most important thing to do if your Mac has a Fusion Drive: Backup your data the Fusion Drive combines data on an SSD and hard drive, so the loss of either is a huge problem; MW; 1/11/2019
Natural Disaster
- OLLI Course: Disaster Preparedness: Almeda, Cascadia, Zombies
- The Best Emergency Preparedness Supplies reviews; 12 essentials; WireCutter (NYT); 10/7/2020
- Disaster Preparedness For Your Finances 10/7/2020
- To Prepare for a Natural Disaster, Call Your Bank LH; 10/14/2019
- Safe Deposit Boxes Aren't (Completely) Safe no federal protection; NYT; 7/19/2019
- The 7 Most Important Supplies for a Starter Earthquake Kit
assembling relevant tools piecemeal is a better bet than buying a premade kit;
water storage; gas shut-off tool; emergency radio; portable headlamp; first aid kit;
phone chargers or battery packs; emergency contact numbers; NYT; 7/18/2019 - Keep These Financial Records in Your 'Go Bag' LH; 7/1/2019
OneDrive (Microsoft)
- Microsoft to Kill OneDrive for Windows 7, 8, 8.1 in Early 2022 11/6/2021
- OneDrive simplifies document sharing by making it even more complex PC; 7/1/2020
- Microsoft's OneDrive Personal Vault locks down a portion of your OneDrive cloud storage with time-limited two-factor authentication; PC; 9/30/2019
Paper, Other
- Prey an app designed to help you find a stolen or lost tablet, laptop or phone. The app will help you locate these items by taking pictures from the camera on the device, screenshots from the computer or even wipe data remotely from the device. Prey is a type of software installed on your devices and then tracked with an online system. There is a free version as well as various pay versions available.
- Stolen Property an international stolen property database. It allows users to report that their item has been stolen. You can also search the database to see if any device you are considering purchasing was stolen.
- Stolen Lost Found Another online database offered to track, find and report found, lost or stolen property
- Take Control of Your Paperless Office digitize your documents while reducing incoming and outgoing paper
- Should You Keep That Document or Shred It? LH; 9/18/2020
- What to Do If You Lose Your Credit or Debit Card While Traveling LH; 1/24/2020
- How to Scan Documents into Notes App on iPhone & iPad OSXD; 1/21/2020
- How to Go Paperless in Your Home Office NYT; 4/9/2019
Photos
- Apple: iCloud: Photos FAQs, Setup: iCloud Photo Library; My Photo Stream; iCloud Photo Sharing
- Apple: Reduce the size of -- your iCloud Photo Library: delete photos; optimize storage; buy more storage; your Photo Library: use just Camera Roll; manual backup of photos
- Apple: iCloud Photo Library FAQ esp. Can I use iCloud Photo Library to save space on my device?
- How to move photos to iCloud to save space on an iPhone MW; 1/12/2024
- How to Transfer Photos from iPhone to Mac Without iCloud OSXD; 12/6/2023
- How to Transfer Your iPhone Photos to a Windows PC Wired; 10/18/2022
- How to Keep Photos and Videos from Taking Up Space on Your Phone Wired; 10/17/2022
- How to Leave Your Photos to Someone When You Die Wired; 3/17/2022
- How to Batch Convert HEIC to JPG (Mac & Windows PC) OSXD; 1/25/2022
- The Easiest Ways to Shrink Large Image Files on Your Mac LH; 1/19/2022
- How to Rescue Your Photos From an Old Computer Wired; 12/28/2021
- How to Lock Up Your Photos and Videos in Google Photos LH; 12/3/2021
- How to back up iPhone photos and video with iCloud Photos turned off MW; 10/14/2021
- How to copy your Photos library from one Mac to another MW; 8/25/2021
- Stingle is a privacy-focused open source photo backup application Ars; 8/8/2021
- How to Back Up All Your Photos Without a Cloud Subscription Giz; 3/11/2021
- Apple now lets you automatically transfer your iCloud Photo Library to Google Photos some things won't xfer; Verge; 3/3/2021
- How to Save All Photos from Facebook on iPhone, iPad, Mac, Windows PC OSXD; 2/27/2021
- How to Back Up and Move Your Photos Between Services leaving Google Photos now that it's no longer free and unlimited? Considering Apple Photos or OneDrive? Here's how to take your library with you; Wired; 12/1/2020
- How to Manage Your Google Photos or Move Them Somewhere Else LH; 11/13/2020
- Understanding how iCloud Photos optimizes photo storage and keeps your originals MW; 7/29/2020
- What the HEIC? Apple's Highly Compressed Image Format Still Confuses High Efficiency Image Container? HEIF and HEVC; TB; 6/26/2020
- Your Google Photos video backups may have been sent to complete strangers CNet; 2/4/2020
- iOS: What to do if iCloud Photos uploads are paused due to a low battery, but you’re actually near a full charge MW; 1/14/2020
- How to Access iCloud Photos from Windows PC OSXD; 1/8/2020
- How to switch from iCloud Photos to just plain Photos local only; MW; 10/15/2019
- Thoughts on Sharing Vacation Photos TB; 8/26/2019
- Can't download photos from your iPhone to your Mac? it could be a trust issue; MW; 7/3/2019
- How to use iCloud to help manage Photos libraries too large for an internal Mac drive MW; 4/12/2019
- Organizing Your Unwieldy Photo Collection Is Easier Than You Think on smartphone; People; Places; NYT; 4/10/2019
- How to cope with a Photos library too big to fit on an internal Mac drive MW; 4/2/2019
Retrospect
- Retrospect site
- Retrospect 18.5.2 TB; 3/27/2022
- Retrospect 17 Solo review: Backup software that gives you everything Win, macOS, Linux; PC; 4/23/2020
SuperDuper (Mac)
- SuperDuper
- SuperDuper 3.8 TB; 10/2/2023
Thumb / USB Drives
- How to format a thumb drive for both Mac and Windows ExFat format allows larger file sizes than the old FAT32; MW; 10/8/2020
- How to Back Up All the Devices That You're Not Backing Up Kindles; Games consoles; Memory cards and USB sticks; Media streamers and boxes; LH; 12/23/2019
- USB Storage with iOS 13: The FAQ TB; 10/16/2019
TimeMachine (Mac)
- Wikipedia: Time Machine
- Apple: Time Machine
- How to manage Time Machine snapshots using Disk Utility in macOS Monterey MW; 11/24/2021
- How to encrypt Time Machine backups MW; 8/27/2021
- How to delete Time Machine local snapshots in macOS ApIn; 6/26/2021
- Take control of Time Machine backups with the TimeMachineEditor utility free; advanced options; MW; 5/4/2021
- How to format a drive for networked Time Machine access
use OS Extended (Journaled) (HFS+) -- APFS prevents networked access; PC; 4/26/2021 - How to reserve Time Machine space on an APFS drive MW; 1/19/2021
- macOS Big Sur supports Time Machine on APFS-formatted drives, but there are a few catches MW; 12/15/2020
- What to do when a Time Machine copy to an external drive is enormously larger than expected it's all about the hard links; MW; 7/8/2020
- Howard Oakley's Deep Dive into Time Machine TB; 1/23/2020
- [2] How to set your Mac as a shared backup destination for Time Machine MW; 11/18/2019
- Can't find your Time Machine backup after upgrading to Catalina? Look for a backupbundle MW; 10/17/2019
- Why you're prompted to erase an external drive when you use it with Time Machine not in the supported format; MW; 10/8/2019
- Time Machine: No FAT or exFAT drives, only HFS+ and APFS MW; 9/12/2019
- Understanding how Time Machine manages its file archive and how it affects what you can restore the deletion process only removes older versions of files; MW; 8/15/2019
- How to Use Multiple Hard Drives With Time Machine BB; 3/7/2019
Windows
- How to Reset Your Windows PC for a Fresh Start LH; 12/4/2023
- The best Windows backup software PC; 8/28/2023
- The best free backup software and services: Reviews and buying advice for protecting your data iDrive, iDrive Online Cloud Backup; PC; 12/6/2022
- How to Read Mac Formatted Drives on Windows PC OSXD; 9/16/2000
- How to check and monitor your hard drive's health PC; 7/31/2020
- How to Install & Setup iCloud for Windows PC OSXD; 11/29/2019
- How to partition a hard drive PC; 6/11/2019
- [2] Update WinRAR on Your PC Right Now LH; 3/16/2019
Safer Internet: Offline: Software Updates
Safer Internet: Offline: Software Updates
Quotes | Summary | When, What | OS | Apps | Add-ons |
Incremental Updates | Major Upgrades | Replace? |
References: General | Android | Apps | ChromeOS/Book |
Drivers, Firmware | iOS / iPadOS | macOS | Meltdown/Spectre |
Office Suites (and other apps) | Replace / Switch Devices | Windows
Quotes
- Definition. software upgrade:...
- A client calls to hotline of internet service provider.
Client: "I have a problem, internet stopped working two days ago, neither I nor my son nor anyone else can access it now."
Hotline: "I see. Do you know what's the operating system on your PC?"
Client: "Of course I do,... - "Chaos reigns within.
Reflect, repent, and reboot.
Order shall return.
Program aborting:
Close all that you have worked on.
You ask far too much.
Windows NT crashed.
I am the Blue Screen of Death.
No one hears your screams.
Yesterday it worked.
Today it is not working.
Windows is like that.
First snow, then silence.
This thousand-dollar screen dies
So beautifully.
A crash reduces
Your expensive computer
To a simple stone.
Serious error.
All shortcuts have disappeared.
Screen. Mind. Both are blank.
There is a chasm
of carbon and silicon
the software can’t bridge.
To have no errors
Would be life without meaning
No struggle, no joy.
Seeing my great fault
Through darkening blue windows
I begin again.
The code was willing,
It considered your request,
But the chips were weak.
Errors have occurred.
We won’t tell you where or why.
Lazy programmers.There is a chasm
of carbon and silicon
the software can’t bridge.
To have no errors
Would be life without meaning
No struggle, no joy.
Seeing my great fault
Through darkening blue windows
I begin again.
The code was willing,
It considered your request,
But the chips were weak.
Errors have occurred.
We won’t tell you where or why.
Lazy programmers.
I'm sorry, there's -- um --
insufficient -- what's-it-called?
The term eludes me." ~Haiku error messages - Dear Tech Support,
Last year I upgraded from Boyfriend 5.0 to Husband 1.0 and noticed a slowdown in the overall performance, particularly in the flower and jewelry applications that had operated flawlessly under Boyfriend 5.0.
In addition, Husband 1.0 uninstalled many other valuable programs, such as Romance 9.5 and Personal Attention 6.5, but installed undesirable programs such as NFL 5.0 and NBA 3.0. And now...
Summary
- "If it ain't broke, don't fix it"?
- Even if you don't care about bug fixes or new features, privacy & security updates are very important.
- It's a myth (procrastination excuse?) that newer versions are always larger, slower, buggier.
- Take note of software upgrade/update notifications, e.g., popups, emails -- -- but don't interact directly with them.
- It's better not to click on links/buttons in unexpected notifications, even if they seem from legitimate sources;
browser popups about Flash are a notorious avenue for malware - Instead, check/update officially via app store, vendor, OS/app or settings.
- Although most updates are generally reliable, it's a good idea to backup first anyway.
- [1] Install Minor/Incremental Updates: System, Apps, Add-ons/Extensions -- within a few days
- [2] Install Major Upgrades -- within a few weeks
- [2] Consider replacing your device or browser -- if security updates are no longer offered; in the meanwhile, exercise extra caution when online; or run selected apps on a different more secure device.
- [2] Don't forget other network(ed) devices, e.g., router, smart TV, IoT
- [3] Run software and hardware diagnostics/repair utilities
- References
When, What to Update: System, Apps, Add-ons
- Backup!
- If you minimize number of applications and add-ons, esp. if infrequently or not used (see Erasing section), there will be fewer items to update.
- Each user will have different risk vs. benefit tradeoffs for what & when to update
- Most tech-savvy user in family might do updates for everyone (whose accounts lack admin privileges)
- Update sooner if the system or app security fixes are critical, i.e., browser, email, network, cloud
- It's usually ok to wait a few days -- for a few weeks for major versions -- if you're travelling or extra busy, or to research incompatibilities.
- Many bugs have already been detected and fixed during wider beta testing by developers (and daring users)
- Any problem with a software update itself is usually remedied in a day or two -- plus, upgrade servers will be more responsive
- Current/recent OS versions:
- Usually, the latest version numbers/dates will be listed below -- and on Course Updates page:
- The labels and color-coding suggest status/urgency for upgrading:
- green: up to date
- lighter green: Recent; incremental; upgrade soon
- orange: Old; major; upgrade when convenient
- red: Obsolete; upgrade asap, or replace -- if internet is used and security upgrades no longer avail
Operating System
- system: e.g., Android, iOS, macOS (formerly "OS X"), Windows
- for checking version / installing system update:
- iOS:
Settings > General > About : Version - iOS:
Settings > General > Software Update - macOS:
[apple] > About - macOS:
System Preferences > Software Update - Win:
Settings > System > About - Win:
Settings > Update & Security > Windows Update - [2] Update software/firmware on other connected devices, e.g., router, smart TV
- [3] Test/beta official OS versions -- only if you are a developer, bugged by a bug, can't live without a new shiny feature, or crave living on the 'bleeding edge'.
Apps
- Individual apps: check for updates via app store, upon startup (app preference), or manually (via menu)
- Ok to ignore updates for apps that you never use, e.g., built-in apps like GarageBand -- but why not remove if unneeded, or offload if easily re-downloaded?
- Install system & application updates only from official store, from within apps, or reputable developers
- Some apps offer option of automatically downloading and installing updates; it's up to you; I prefer to backup before installing most updates.
- [2] Generally, don't download from 3rd party sites, e.g., CNet, Soft32, ZDNET, download.com, etc.
- [3] Don't jailbreak your device with an unofficial OS, so that you can install nifty but questionable apps.
- iOS:
App Store > Updates - iOS:
Settings > iTunes & App Store > Automatic Downloads > Music, Apps, Books & Audiobooks, Updates: ? - iOS:
Settings > iTunes & App Store > Use Cellular Data: ? - macOS:
App Store > Updates: apps installed from store - macOS:
Adobe Reader > Help > Check For Updates - macOS:
Backblaze > Check For Updates - macOS:
Carbon Copy Cloner > Carbon Copy Cloner > Check For Updates - macOS:
Firefox > Firefox > About Firefox - macOS:
Google Chrome > Chrome > About Google Chrome - macOS:
System Preferences > Java > Update - macOS:
LibreOffice > Help > Check For Updates - macOS:
Microsoft Excel/Word/Powerpoint > Help > Check For Updates - macOS:
Skype > Skype > Check For Updates - macOS:
Zoom > Check for Updates - Allow easier installation of free apps?
- iOS:
Settings > (your acct) > iTunes & App Store > Password Settings > Free Downloads > Require Password: off - [2] Save $ by purchasing apps only once for each family device via accounts usually sharing same payment method
- iOS:
Settings > (your acct) > Family Sharing - macOS:
System Preferences > iCloud > Manage Family - [3] macOS:
System Preferences > Security & Privacy > 'app was blocked from opening because it is not from an identified developer' > Open Anyway
Add-ons: Plugins, Extensions
- add-ons customize/extend an app, esp. a browser
- Once installed, most browsers check/update automatically, or via sytstem preference
- Do not update browser extensions, e.g., Flash, or apps when prompted via a browser popup -- use app store, or app or extension's own 'Check for Updates' command
- Look for install options -- often checked by default -- that might install unwanted extensions or adware, or change settings (home page, search engine); e.g., Oracle's Java installer
- plugins: e.g., Adobe Flash; Oracle Java -- or consider uninstalling altogether
- extensions: e.g., Adblock Plus, HTTPS Everywhere
- macOS:
Safari > Preferences > Extensions > Updates : Install Updates Automatically - macOS:
System Preferences > Flash Player > Advanced > Updates
[1] Install Minor/Incremental Updates, e.g., #.1
- Backup -- both incremental and clone -- before cleanup; again before actual installation;
see When, What to Upgrade; Backup section - If you always keep your device up-to-date, it should be easier to migrate to future system & app releases
- You can usually wait a day or two -- or even longer if there are no security fixes for your particular device
- Update may contain bug fixes, and minimal new features
- Allow enough time for backup, download and install -- probably not before a trip or big presentation; updates usually go smoothly, but allow a little more time in case you need to troubleshoot or restore a previous system version.
- General update info in previous sections, specific directions for different OS in subsequent subsections -- and References
Android
iOS
- [Refs:iOS]
- iOS:
Settings > General > Software Update - iOS:
App Store > Updates - iOS users may want to use iTunes to update iOS: easy to backup first
- for OTA (over the air) updates via WiFi or cellular
- < iOS9: update can fail due to low device memory
- ≥ iOS9: update can be slower; apps are removed/reinstalled if needed to create temporary space
macOS
- [Refs:macOS]
- Out-of-cycle Security or Supplemental Updates may also be available, with no change to system version #
- macOS:
[apple] > About > Software Update - macOS:
App Store > Updates-- macOS and selected apps - macOS (10.14):
System Preferences > Software Update - macOS:
System Preferences > App Store: download/install, password
Windows
- [Refs:Windows]
- Win:
Settings > Update & Security > Windows Update
[2] Install Major OS Updates, e.g., #.0
- Backup -- both incremental and clone -- before cleanup or running diagnostics;
again before actual installation; see When, What to Upgrade; Backup section - Install incremental or other updates to current OS and apps -- including Safari, iTunes for macOS -- before installing major updates
- Allow even more time for backup, download and install -- to anticipate and remedy incompatibilities -- and if things don't go smoothly, for troubleshooting or restoring previous system version
- Usually released about once/year: more major fixes, new features and possible incompatibilities
- iOS: you should upgrade 'as soon as possible'; usually less complex than desktop upgrades; security fixes sometimes available for previous iOS version
- macOS: incremental security fixes are still provided for previous system and browser for 1-2 years, so if there are really major changes, e.g., app incompatibility, user interface makeovers, missing features, performance issues, you could delay your upgrade -- though not indefinitely
- Generally, you could wait a week or two for ".1" version to be released to avoid major bugs, especially if there are no critical security fixes and there are significant changes, e.g., file system
- If there are multiple devices in a family, upgrade one first to test the process & outcome before upgrading others.
- When you are ready to upgrade:
- Read articles here about latest version, e.g., Android, iOS, macOS, Windows, or buy Take Control e-books to find out more about what's changed, compatibility/adequacy of your hardware (to run new os) and of apps (with new os), cleanup & backup steps, new features that you might actually like to have (or old features that might be removed that you can’t live without), installation advice
- Remove unused applications and browser add-ons -- see Erasing section
- Check if new OS version is incompatible with any important applications you have, e.g., upgrade info, release notes, vendor sites
- Apple: macOS versions, compatibility; iOS, iPadOS updates
- macOS:
(apple) > About This Mac > System Report > Software > Applications: 64-bit(Intel)-- some 32-bit apps may still continue to work under High Sierra. - iOS10:
Settings > About > Applications: 'these apps may slow down your iPad and will not work with iOS 11 if they are not updated' - For incompatible apps, consider upgrading version or finding a (free) alternative.
- For example, instead of Microsoft Office 2011, which may not work with macOS 10.13 (High Sierra): HS 32-bit app incompatibility; plus, Microsoft has stopped providing support and security patches
- offline apps: Microsoft Office 2016 -- $$; Steve's spouse upgraded to this
- macOS/iOS iWork suite: Pages, Numbers, Keynote -- free; Steve switched to these
- Open Office, LibreOffice, NeoOffice -- free
- SoftMaker: Free Office (free); Softmaker Office: Std ($20+) / Pro; comparison
- cloud-based storage & office suite (via browser): Microsoft: OneDrive: Word, Excel, PowerPoint Online -- free;
Microsoft 365 -- subscription; includes apps (And,iOS,Mac,Win), 1Tb OneDrive cloud storage, 60 Skype minutes/mo. - Google Drive: Docs, Sheets, Slides -- free
- Apple's iCloud: iWork (Pages, Numbers, Keynote) -- free
- [2] Check disk permissions, repair (less necessary recently)
- macOS (< 10.10):
Disk Utility > Repair Permissions-- or run Maintenance (or Onyx) utility - [3] Restart from Recovery partition; check main disk; repair (if necessary)
- macOS:
restart w/ cmd-R > OS X Utilities > Disk Utility > Repair Disk - [3] Check hardware, e.g., memory
- macOS:
restart w/ D key; diagnostic runs automatically
[2] Replace Device?
- Strongly consider replacing your device if security/privacy problems are no longer patched in your OS version -- and you can't upgrade, e.g.,
- if your computer OS is more than 1-2 major versions behind -- see macOS, Win
- usually if your tablet/phone OS is 1 or more major versions behind -- see Android, iOS
- Your device doesn't support a newer OS -- or needs extra memory that you cannot (or do not want to) add
- Apps you rely on are no longer provided/supported on your old OS (e.g., 32-bit when 64-bit will be required) -- and no updates are available
- In the meanwhile, use an actively maintained browser, e.g., Firefox, Chrome -- rather than built-in browser, i.e., macOS Safari, Windows IE; and consider using the device only for casual (non-encrypted) browsing
- Do you need just browsing, email, basic document creation/editing, and simple photo manipulation? If so, you might consider a tablet (iPad) or Chromebook -- less expensive, and much simpler to maintain/update than a full-blown desktop or laptop computer with macOS, Windows or Linux.
- When purchasing a new device, especially a subsidized or less expensive one, request that vendor remove pre-installed bloatware, crapware, adware
- If you're switching between different OS (versions or vendors), check if migration tools are available for contacts, bookmarks, settings, photos, accounts, etc.
- When donating / discarding old device -- see Erasing section
References
- sections: Refs: Android; Apps including browsers, but not Microsoft Office; ChromeOS/Book; Drivers, Firmware; iOS; macOS; Windows; Meltdown/Spectre; Microsoft Office (and other apps); Replace / Switch Devices
- course section: Connection : Malware
- topics: beta testing, bloatware, emulators, lifecycle
- Wikipedia: Operating System (OS); firmware
- Wikipedia: Mobile OS; App Store; "sandbox"
- Wikipedia: plug-in software component that adds a specific feature to an existing software application
- Wikipedia: browser extension extends the functionality of a web browser in some way. Depending on the browser and the version, the term may be distinct from similar terms such as plug-in or add-on
- HowStuffWorks: How Operating Systems Work
- Why You Should Reset Your PC for the New Year LH; 11/30/2023
- 4 Helpful iPhone and Android Tricks You May Not Know About
Point the Way (map/camera); Scan Stuff;
Name That Tune; Emergency Help; NYT; 8/3/2022 - Steps to Simple Online Security: 3: Enable Automatic Updates Everywhere NYT; 4/1/2022
- How to Use Your Phone's Privacy-Protection Tools
iOS 15; Android 12; NYT; 12/8/2021 - Emergency software patches are on the rise
zero-day flaws have become more common; NBC; 9/14/2021 - Definitely not Windows 95: What operating systems keep things running in space? the updates don't come every spring and fall; Real-Time Operating System (RTOS); Ars; 10/2/2020
- Boeing 747s Still Use Floppy Disks to Get Critical Software Updates Giz; 8/11/2020
- Reset Your Computer Once a Year for a Happier Life restore your Mac, PC, or Chromebook to factory conditions; Wired; 3/8/2020
- How Updates in iOS 13 and Android Q Will Change Your Smartphone dark mode; speed; privacy enhancements; NYT; 6/5/2019
- Stop Ignoring Those "Update Your Device" Messages even though the Asus malware attack was spread through software updates, the best way to protect yourself online is to keep your software updated; NYT; 3/27/2019
- Trick Your Friends Into Installing Smartphone Updates LH; 2/18/2019
- [2] GPS devices with a poorly implemented GPS Time-to-UTC conversion algorithm may provide incorrect UTC following a week number rollover newer receivers built after, say, 2010 should be fine, provided they follow the specs and notice the rollover; older devices may fail after April 6 unless they've been suitably updated; Reg; 2/12/2019
- How to Submit a Bug Report to Apple, Google, Facebook, Twitter, Microsoft plus Adobe, AMD, Asana, Dropbox, DuckDuckGo, Evernote, Facebook, Instagram, Lyft, Mozilla, Nintendo, Nvidia, Paypal and Venmo, Reddit, Slack, Snapchat, Sony, Trello, Tumblr, Twitch, Twitter, Uber, Valve, Wordpress; LH; 2/5/2019
- 42 of the Best Troubleshooting Guides from 2018 Mac, iOS; OSXD; 1/5/2019
Android
- "Imagine if Windows patches had to...
- Wikipedia: Android; Android versions 1.5-8.x: 1.5 Cupcake; 1.6 Donut; 2.0 Eclair; 2.2 Froyo; 2.3 Gingerbread; 3.0 Honeycomb; 4.0 Ice Cream Sandwich; 4.1 Jelly Bean; 4.4 KitKat; 5.0 Lollipop; 6.0 Marshmallow; 7.0 Nougat; 8.0 Oreo; 9.0: Pie; 10, 11, 12
- Wikipedia: Google Play (app store); Rooting
- Google: android.com
- HowStuffWorks: How Android Tablets Work; How do I upgrade the version of Android on my tablet?
- Android 14 review Ars; 10/29/2023
- The Android 13 Privacy Settings You Should Update Now Wired; 8/17/2022
- Do This Android App Privacy Audit LH; 7/7/2022
- These Android features will help protect your digital privacy TC; 4/30/2022
- The Android 12 Privacy Settings You Should Update Now Wired; 11/28/2021
- 10 Practical Privacy Tips for Your Android Phone NYT; 10/19/2021
- How to Speed Up Your Old Android Phone LH; 9/8/2021
- Switching from Android to iPhone made easy MW; 3/9/2021
- Samsung Promises 'At Least Four Years' of Security Software Updates for Recent Galaxy Devices MR; 2/23/2021
- This Android 12 leak looks an awful lot like iOS 14 PC; 2/9/2021
- 7 Simple Ways to Make Your Android Phone More Secure Wired; 12/1/2020
- Play Store identified as main distribution vector for most Android malware ZD; 11/11/2020
- On Older Versions of Android, Many Let's Encrypt-Secured Sites May Stop Working in 2021 < 7.1.1; 11/6/2020
- The Android 11 Privacy and Security Features You Should Know Wired; 9/27/2020
- Android 11: The Ars Technica Review Ars; 9/21/2020
- Android 11 is final with day-one updates from Google, betas for other OEMs Ars; 9/8/2020
- The 11 Best New Features in Android 11 Wired; 9/8/2020
- Android 11 is here, bringing minor changes to Pixel phones (and others soon) PC; 9/8/2020
- Samsung's Android update guarantee might actually be better than Google's PC; 8/8/2020
- Google says Android 11 Beta 1 is being pushed back to June 3 about a month behind schedule, but the final release is still on track for Q3; 5/6/2020
- Install the October 2019 Android Security Update ASAP LH; 10/7/2019
- Attackers exploit 0-day vulnerability that gives full control of Android phones Vulnerable phones include 4 Pixel models, devices from Samsung, Motorola, and others; Ars; 10/3/2019
- Android 10: The Ars Technica Review Ars; 9/5/2019
- Android 10 launches; Pixel phones get update Ars; 9/3/2019
- Take These Steps Before Installing Android 10 on Your Phone LH; 9/3/2019
- The Android 10 Privacy and Security Upgrades You Should Know About Wired; 8/22/2019
- Buying an old Android phone? What you should know about privacy and security if your Android phone is not running the latest software OS, your security and privacy might be in jeopardy; CNet; 5/10/2020
- Your old Android phone isn't dead yet: 7 ways to make it run faster and last longer PC; 5/4/2020
- How Spies Snuck Malware Into the Google Play Store -- Again and Again malicious Android apps from the so-called PhantomLance campaign targeted hundreds of users, and at least two slipped past Google's defenses; Wired; 4/28/2020
- Use Permissions to Keep Scammy Apps Off Your Android LH; 4/23/2020
- How to Update Your Super-Old Android So It Doesn't Get Hacked Update your device (as much as you can); Get antivirus protection; Switch to a third-party OS; Or just get a new phone; LH; 3/9/2020
- Google slams Samsung for 'unnecessary changes' to the Android kernel decreased security; 2/17/2020
- Google & Samsung fix Android spying flaw. Other makers may still be vulnerable Camera and mic could be controlled by any app, no permission required; Ars; 11/19/2019
- 146 New Vulnerabilities All Come Preinstalled on Android Phones The dozens of flaws across 29 Android smartphone makers show just how insecure the devices can be, even brand-new; Wired; 11/15/2019
- The Verge Guide To Android comprehensive resource that will help you learn how to use your Android phone's best features and further educate you about this popular and flexible mobile operating system; Verge; 10/14/2019
- Your Samsung Device May Now Be Getting Less Frequent Software Updates LH; 10/8/2019
- Inexpensive, unpatched phones put billions of users' privacy at risk users who connect only with cheap Android phones pay with their personal info; Ars; 10/7/2019
- The Internet's horrifying new method for installing Google apps on Huawei phones Just make a Chinese website your device's remote administrator. It'll be fine! Ars; 10/2/2019
- Goodbye Android Q, hello Android 10 Google's dessert-based code names are over; PC; 8/22/2019
- The Open Source Project That Keeps Google's Hands Off Your Android Data MicroG gives users control over what data is used, where, when, and how; MB; 6/7/2019
- Google bans 29 apps downloaded 4.3M+ times from the Play Store after researchers discovered they were being used to perform malicious acts like serve scam ads hard for many infected users to uninstall; Ars; 2/1/2019
Apps
- see also: Office
- How to Spot an App You Shouldn't Trust
check the user reviews -- carefully; check the developer's history;
check how the app is funded; check the permissions the app needs;
check the apps you're already using; Giz; 6/19/2023 - Until further notice, think twice before using Google to download software
malvertising; use device's app store; Ars; 2/3/2023 - Apps can pose bigger security, privacy threat based on where you download them countries; Ars; 9/27/2022
- 13 Reasonable Alternatives to Adobe's Expensive Apps LH; 4/19/2021
- Unsecured Cloud Configurations Exposing Information in Thousands of Mobile Apps 3/4/2021
- Declutter Your Devices to Reduce Security Risks
Summon your willpower and delete those apps you haven't used, but keep telling yourself
you will, because the odds are high that you won't use them; LH; 1/5/2021 - More Android 'Fleeceware' to Uninstall From Your Phone an app hides its terms, fees, and/or subscription costs, or otherwise has some clever way to cajole you into signing up for a 'free trial' that actually expires very soon and costs you a lot more than you expected when it's over; LH; 9/4/2020
- [2] How to Install Apps From Outside Your Phone's App Store sideloading apps removes the security protections that Google and Apple give you; better to stay within the 'walled gardens' most of the time; Wired; 8/9/2020
- The Internet's Most Censored Space app stores; NYT; 6/17/2020
- Alternatives for Adobe Acrobat, Photoshop and more PDF editors; PC; 6/15/2020
- Fleeceware apps discovered on the iOS App Store Android earlier, now iOS; abuse of free trials and trial cancelation; ZD/ 4/9/2020
- How to set up Family Sharing on your iPhone, iPad, or Mac
Purchase Sharing: Media you buy on iTunes, Books, and most App Store purchases (but not in-app purchases!)
iCloud Storage: If you have the 200GB or 2TB storage plan, you can share it with your family.
Location Sharing: Family members share location or the location of their devices. You can always just share location to an individual in the Find My app.
Screen Time: If you have a Child account in your family, you can set screen limits and view reports for it.
Apple Music: You need a family plan on Apple Music to share with your family (it costs $15 per month, rather than $10 for an individual account).
TV Channels: If you subscribe to a premium streaming service through the TV app you can share it with your whole family at no cost. This includes Apple TV+, which is technically a Channel.
Apple Arcade: Apple’s gaming subscription service includes Family Sharing at no cost.
Apple News+: If you have the premium magazine and newspaper subscription in the News app, you can share it with your family at no cost; MW; 1/8/2020 - How to Change the Default Apps on All Your Devices Wired; 10/27/2019
- More Than Half of PC Applications Installed Worldwide Are Out-of-Date Shockwave, VLC and Skype top the list; 1/22/2019
ChromeOS/Book
- The Best Chromebook NYT; 8/2/2023
- The best Chromebook to buy CNet; 7/21/2023
- The Best Chromebooks To Buy Verge; 6/27/2023
- Chromebooks vs. Windows laptops: Which should you buy? PC; 12/4/2022
- How to uninstall apps from a Chromebook Verge; 9/9/2022
- Why a Chromebook Is Probably All You Need They do almost everything you want, but cost less; CNet; 7/2/2022
- Google announces early access to Chrome OS Flex, a version of Chrome OS for businesses and schools that is designed to run on old PCs and Macs
Chrome OS Flex; Verge; 2/15/2022 - The world's second-most popular desktop operating system isn't macOS anymore Ars; 2/17/2021
- Google updates Chrome OS (88) with security, smart display and personalization features PC; 1/27/2021
- How to Run Alternative Browsers on Your Chromebook Linux (Beta): Firefox, Vivaldi; or Android Play Store; Giz; 11/6/2020
- Is this Chromebook about to die? Why Google's expiration dates matter don't get stuck with a short-lived lemon; PC; 8/31/2020
- How to use a Chromebook: 10 must-know tips, tricks, and tools for beginners PC; 12/4/2019
- How to check which version of Chrome OS you're running Verge; 10/16/2019
Drivers, Firmware
- How to Check Your USB Devices for Unsafe Firmware LH; 2/19/2020
- [2] Getting Drivers for Old Hardware Is Harder Than Ever At least one major provider of hardware-level BIOS drivers is actively deleting old stuff it no longer supports, while old FTP sites where vintage drivers are often found are soon going to be harder to reach; MB; 12/12/2019
iOS / iPadOS
- Wikipedia: iPhone/iPad iOS; iOS versions: 1.0 - 17.x; App Store; "jail breaking"
- Apple: Manuals, Specs, and Downloads
- Apple: security updates for all products: macOS, iOS, AppleTV, etc.
- Apple: [3] Beta Software Program macOS, iOS;
[3] About iOS beta software Archive an iOS backup with iTunes; Download the final version of iOS; Go back to the current version of iOS - HowStuffWorks: How the iPhone Works; How the iPad Works
- Take Control: iOS 9: A Take Control Crash Course
 Q. How can you tell which one of your friends has the new iPhone 6 plus?...
Q. How can you tell which one of your friends has the new iPhone 6 plus?...- iOS 18: Everything you need to know about the next iPhone update MW; 4/3/2024
- iOS 17 superguide MW; 4/3/2024
- Apple Releases iOS and iPadOS 17.4.1 and 16.7.7 TB; 3/22/2024
- iOS/iPadOS 17.4 Update Released OSXD; 3/5/2024
- iOS/iPadOS 16.7.6, iOS/iPadOS 15.8.2 Released for Older iPhone & iPad Models OSXD; 3/5/2024
- iOS versions: Every version of iOS from the oldest to the newest MW; 2/28/2024
- OS Updates: iOS 17.3, iPadOS 17.3 TB; 1/22/2024
- iOS 17 Cheat Sheet: Everything on Apple's Latest iPhone Update CNet; 1/9/2024
- iOS/iPadOS 17.2
Apple's End-of-Year OS Updates Add Promised Features, Security Updates; TB; 12/11/2023 - iOS 16 superguide MW; 9/23/2023
- iOS compatibility: Find out the latest version your iPhone can run MW; 9/11/2023
- iPadOS 17: Everything you need to know MW; 9/6/2023
- Apple Releases 24-Jul-2023 Security Updates for All Active Operating Systems TB; 7/24/2023
- iOS 16.6 has been released with a bunch of important security updates MW; 7/24/2023
- Rapid Security Responses for iOS/iPadOS 16.5.1 (c) TB; 7/13/2023
- iOS 16.5.1 is released with important security updates and a Camera Adapter fix
older devices get iOS 15.7.7; MW; 6/21/2023 - The Real System Requirements for Apple's 2023 Operating Systems TB; 6/19/2023
- iOS/iPadOS 16.5 TB; 5/18/2023
- iOS/iPadOS 15.7.6 Incorporate Rapid Security Response Fixes TB; 5/18/2023
- What Are Rapid Security Responses and Why Are They Important? TB; 5/2/2023
- How Apple's commitment to software upgrades for older iPhones allowed the company to capture a part of the US market once cornered by inexpensive Android phones
the Unexpected Reason Apple Is Dominating the U.S. Smartphone Market; WSJ; 4/15/2023 - Why You Should Enable Apple's New Security Feature in iOS 16.2 Right Now NYT; 12/14/2022
- How to get apps for old iPhones and iPads
Account > Purchased > MyPurchases > Download an older version of this app?; ApIn; 9/1/2022 - The top new iOS 16 features coming to your iPhone this fall MW; 6/6/2022
- iOS 16 vs iOS 15: Should you update this fall? MW; 6/6/2022
- Apple Releases iOS 15.5, iPadOS 15.5, ... TB; 5/16/2022
- How to Get Software and Security Updates on Your Old iPhone LH; 2/22/2022
- The Macworld iOS 15 superguide: Tips, how-tos, new features, and more MW; 1/20/2022
- How to Read Your iOS 15 App Privacy Report Wired; 1/9/2022
- iPhone setup guide: How to transfer data and master your new phone MW; 12/25/2021
- iOS 14.8.1 and iPadOS 14.8.1 Address Security Vulnerabilities TB; 11/2/2021
- iOS 15: Update now or wait? MW; 9/27/2021
- Apple Releases iOS 12.5.5 to Block Exploited Vulnerabilities TB; 9/23/2021
- iOS 15, iPadOS 15 Now Available and watchOS 8, and tvOS 15; TB; 9/20/2021
- Apple Issues Emergency Security Updates to Close a Spyware Flaw
Researchers at Citizen Lab found that NSO Group, an Israeli spyware company,
had infected Apple products without so much as a click;
upgrade iOS 14.8; NYT; 9/13/2021 - iOS 14.8, iPadOS 14.8 Fix Security Flaws
and macOS 11.6 Big Sur, watchOS 7.6.2, Security Update 2021-005 Catalina; TB; 9/13/2021 - iOS 14: Guides, tips, tricks, and everything you need to know about Apple's new iPhone OS MW; 9/13/2021
- [3] How to Install AltStore on iPhone & iPad
sideloading unofficial apps from desktop; OSXD; 6/15/2021 - How iOS 15 transforms the way we think of iPhone updates
older iOS security updates; MW; 6/16/2021 - [2] Run iOS 4 on a Modern iPhone with OldOS OSXD; 6/16/2021
- Apple Releases iOS 12.5.4 to Block Security Vulnerabilities in Older iOS Devices TB; 6/14/2021
- Apple announces iOS 15 and iPadOS 15 Ars; 6/7/2021
- Here are the devices that can run iOS 15, iPadOS 15, macOS Monterey, and watchOS 8 Verge; 7/7/2021
- iOS 14.6, iPadOS 14.6, macOS 11.4 Big Sur, watchOS 7.5, and tvOS 14.6 TB; 5/24/2021
- Apple Releases iOS 14.5.1, iPadOS 14.5.1, macOS 11.3.1, and watchOS 7.4.1 TB; 5/3/2021
- Apple Releases iOS 14.5, iPadOS 14.5, macOS 11.3, watchOS 7.4, and tvOS 14.5 TB; 4/26/2021
- Fix 'Unable to Install Update' Error for iOS & iPadOS OSXD; 3/24/2021
- iOS 14.4.1, iPadOS 14.4.1, macOS 11.2.3 Big Sur, and watchOS 7.3.2 Address WebKit Security Vulnerability TB; 3/8/2021
- How to Limit Google's Apps From Tracking You on Your Apple Devices LH; 2/25/2021
- watchOS 7.3, iOS 14.4, iPadOS 14.4, and tvOS 14.4 Address Serious Security Exploit TB; 1/26/2021
- Apple fixes another three iOS zero-days exploited in the wild ZD; 1/26/2021
- iOS 12.5.1 Released for Older iPhones with Exposure Notification Bug Fix OSXD; 1/11/2021
- iOS 14: Tips, guides, tricks, and everything you need to know about Apple's new iPhone OS MW; 12/18/2020
- Surprise iOS 12.5 and watchOS 6.3 Updates Bring Exposure Notification and a Security Fix TB; 12/15/2020
- Apple Releases iOS 14.3, iPadOS 14.3 TB; 12/14/2020
- iOS Update Failed? Here's How to Troubleshoot Failed Software Updates on iPhone & iPad OSXD; 12/6/2020
- Apple developers can now let you share free copies of your in-app purchases with your family iOS & Mac; Verge; 12/4/2020
- Apple Releases iOS 14.2, iPadOS 14.2, watchOS 7.1, HomePod Software 14.2, and tvOS 14.2 TB; 11/5/2020
- Apple Updates Numerous Operating Systems for Exploited Security Vulnerabilities: iOS 12.4.9 TB; 11/5/2020
- A bevy of new features makes iOS 14 the most secure mobile OS ever Ars; 9/18/2020
- iOS 14, iPadOS 14, watchOS 7, and tvOS 14 Now Available TB; 9/16/2020
- iOS 13.7 Integrates Apple's COVID-19 Exposure Notifications TB; 9/1/2020
- iOS 13.6.1, iPadOS 13.6.1 TB; 8/13/2020
- iOS 13.6, iPadOS 13.6, macOS 10.15.6, watchOS 6.2.8, and tvOS 13.4.8 add News Features, Car Keys, Symptom Tracking; TB; 7/15/2020
- Apple releases iOS and iPadOS 13.6, macOS 10.15.6, and watchOS 6.2.8 Ars; 7/15/2020
- iOS 14 Will Completely Change the Way You Use Your iPhone Giz; 7/9/2020
- How to Fix Your iPhone When an iOS Update Causes Issues LH; 7/2/2020
- iOS 14, iPadOS 14 Features & Screenshots; OSXD; 6/22/2020
- Kernel Vulnerability Causes Apple to Update All Operating Systems TB; 6/1/2020
- Apple releases important security patches: iOS and iPadOS 13.5.1, watchOS 6.2.6, tvOS 13.4.6, and macOS 10.15.5 MW; 6/1/2020
- [3] Jailbreak iOS 13.5 with unc0ver, Available to Download Now OSXD; 5/26/2020
- Why You Shouldn’t Make a Habit of Force-Quitting iOS Apps or Restarting iOS Devices TB; 5/21/2020
- iOS and iPadOS 13.5 now available with COVID-19 contact API, FaceTime and Face ID tweaks MW; 3/20/2020
- Apple releases iOS 12.4.7, iOS 13.5, iPadOS 13.5, tvOS 13.4.5 updates ApIn; 5/20/2020
- iOS 13.4.1 and iPadOS 13.4.1 Fix FaceTime Bug TB; 4/7/2020
- iOS 13.4 and iPadOS 13.4: Trackpad Support, iCloud Drive Folder Sharing, and More TB; 3/24/2020
- Apple Releases iOS 13.3.1, iPadOS 13.3.1, watchOS 6.1.2, and tvOS 13.3.1 TB; 1/28/2020
- Apple Pushes Out iOS 13.3, iPadOS 13.3, iOS 13.3 for HomePod, macOS 10.15.2 Catalina, watchOS 6.1.1, and tvOS 13.2 TB; 12/10/2019
- [3] What the newly released Checkra1n jailbreak means for iDevice security There are reasons to embrace it. There are reasons to be wary of it. Here's the breakdown; Ars; 11/15/2019
- iOS 13.2.2 Stops Killing Background Apps TB; 11/7/2019
- Quickly Access App Updates in iOS 13 tap&hold on App Store icon; TB; 11/7/2019
- iOS 13.2 and iPadOS 13.2 Serve Up Deep Fusion, HomeKit Enhancements, and HomePod Features TB; 10/28/2019
- 16 Useful Gems in Apple's New iOS 13 NYT; 10/24/2019
- iOS 13.1.3, iPadOS 13.1.3, and Catalina Supplemental Update Tackle Bugs TB; 10/15/2019
- Four More Apple Updates: iOS 13.1.2, iPadOS 13.1.2, watchOS 6.0.1, and watchOS 5.3.2 TB; 9/30/2019
- How to Make the Most of Apple's New Privacy Tools in iOS 13 minimizing location sharing, silencing robocalls, 'Sign in with Apple'; NYT; 9/28/2019
- iOS 13.1.1 Fixes Bugs and Keyboard Security Issue TB; 9/27/2019
- iOS 12.4.2 Provides Important Security Fix to Older iOS Devices TB; 9/26/2019
- Here's What Sets iPadOS Apart from iOS TB; 9/25/2019
- Apple releases iPadOS 13.1, iOS 13.1, and tvOS 13 Ars; 9/24/2019
- iPadOS: 5 best new security and privacy features for your iPad new permission controls; sharing pictures w/o location; Bluetooth permissions; Sign in with Apple; HomeKit upgrades; CNet; 9/24/2019
- iOS 13.0 Now Available; iOS 13.1 and iPadOS 13.1 Moved Up to 9/24 TB; 9/19/2019
- iOS 13: The first 6 things to do after you upgrade MW; 9/19/2019
- 19 Things You Can Do in iOS 13 That You Couldn't Before Giz; 9/19/2019
- iOS 13: Here are the new security and privacy features you need to know TC; 9/19/2019
- iOS 12.4.1 Update Available to Download Now OSXD; 8/26/2019
- Apple Releases macOS 10.14.6, iOS 12.4, watchOS 5.3, tvOS 12.4 -- plus iOS 10.3.4 and 9.3.6 TB; 7/22/2019
- How to Enter Recovery Mode on iPhone 7 Plus & 7; iPad, iPad Air, iPad Mini, Early iPad Pro; iPhone XR, XS, XS Max, X; iPhone 8 & 8 Plus OSXD; 6/13/2019
- iOS 13 Compatible Devices List: All iPhone & iPad Supporting iOS 13 & iPadOS 13 OSXD; 6/5/2019
- How to Check iOS Feature Availability Per Country OSXD; 5/25/2019
- Apple releases iOS 12.3.1 fixes VoLTE & Messages issues; Ars; 5/24/2019
- Apple Agrees to Tell Users If an iOS Update Will Slow Down Their iPhones MB; 5/23/2019
- Apple Releases iOS 12.3, macOS 10.14.5, watchOS 5.2.1, and tvOS 12.3 and Debuts New Apple TV App TB; 5/13/2019
- You Need to Update to iOS 12.2 Right Now to Fix More Than 50 Security Holes Giz; 3/26/2019
- iOS 12.2 and macOS 10.14.4 Add Apple News+ and Enhance Apps; TB; 3/25/2019
- How to Prioritize App Downloads in iOS requires 3D Touch: force-press on a grayed-out app to activate a context menu, and tap on the "Prioritize Download" option; LH; 3/20/2019
- How to download prior versions of apps onto an older iPhone or iPad that can't run iOS 12 ApIn; 3/10/2019
- Apple removes VoIP app clones from the App Store App Store Review Guidelines aren't always enforced; other duplicate apps for printing photos in Walgreens or CVS stores; TC; 2/27/2019
- How to Completely Google-ify Your iPhone if you prefer Google's apps and services -- and can manage privacy settings; Giz; 2/25/2019
- Get more familiar with your iPhone with this list of 30 easy to follow tips ApIn; 2/23/2019
- How to Check What iOS Version is Installed on an iPhone or iPad Settings > General > About : Version; OSXD; 2/18/2019
- How to Enable Automatic iOS Updates for System Software on iPhone or iPad OSXD; 2/15/2019
- Dozens of porn and gambling apps found using iOS Enterprise Certificates to get to users outside the App Store, likely violating Apple's terms TC; 2/12/2019
- Apple Re-Enables Group FaceTime with iOS 12.1.4 and macOS 10.14.3 Supplemental Update and other security fixes; TB; 2/7/2019
- Apple issues Group FaceTime bug mea culpa, promises software update next week MW; 2/1/2019
- Apple Releases iOS 12.1.3 with Bug Fixes and macOS 10.14.3, watchOS 5.1.3, and tvOS 12.1.2; TB; 1/22/2019
- How to Cancel an Over-the-Air iOS Update in Progress MR; 1/20/2019
- How to Passcode Lock an App in iOS Settings > ScreenTime; MR; 1/18/2019
- How to See the Size of App Store Updates on iPhone or iPad App Store > Updates > more; OSXD; 1/9/2019
macOS
- Wikipedia: macOS / OS X; Apple Software Update; App Store
- Wikipedia: macOS (OS X) versions
10.0: Cheetah; 10.1: Puma; 10.2: Jaguar; 10,3: Panther; 10.4: Tiger; 10.5; Leopard; 10.6: Snow Leopard; 10.7: Lion;
10.8: Mtn. Lion; 10.9: Mavericks; 10.10: Yosemite; 10.11: El Capitan; 10.12: Sierra; 10.13: High Sierra; 10.14: Mojave;
10.15: Catalina; 11.x: Big Sur; 12: Monterrey; 13: Ventura; 14: Sonoma - Apple: Manuals, Specs, and Downloads
- Apple: Identify Legitimate Emails From the App Store or iTunes Store tips about whether an email about an App store, iTunes store, iBooks store, or Apple Music purchase is legitimate; 2/23/2018
- Apple: security updates for all products: macOS, iOS, AppleTV, etc.
- Apple: [3] Beta Software Program macOS, iOS
- Apple: How to reinstall OS X on your Mac from Recovery; from a Time Machine backup
- HowStuffWorks: How Mac OS X Works
- Application compatibility table
- dosdude1: 10.12-10.15 patchers for unsupported hardware
- macOS 15: Everything you need to know about the next big Mac update MW; 4/8/2024
- macOS 14 (Sonoma) superguide MW; 4/3/2024
- Every macOS and Mac OS X version -- including the latest update MW; 4/1/2024
- Safari 17.4.1 TB; 3/26/2024
- macOS 14.4.1 Sonoma and macOS 13.6.6 Ventura Fix Bugs and Vulnerabilities TB; 3/25/2024
- Best virtual machine software for Mac 2023 MW; 3/22/2024
- How to speed up a slow Mac MW; 3/19/2024
- macOS Ventura 13.6.5 & macOS Monterey 12.7.4 Updates Available OSXD; 3/8/2024
- macOS 14.4 is now available new Emoji, Podcast app updates, security and bug fixes; MW; 3/7/2024
- Safari 17.3.1 Update for macOS Ventura & Monterey Fixes Overlapping Text Bug OSXD; 2/10/2024
- MacOS Ventura 13.6.4 & MacOS Monterey 12.7.3 Released with Security Fixes OSXD; 1/23/2024
- OS Updates: macOS 14.3 TB; 1/22/2024
- macOS 14.2 Sonoma
Apple's End-of-Year OS Updates Add Promised Features, Security Updates; TB; 12/11/2023 - macOS Sonoma can be installed on 83 unsupported Macs with this tool ApIn; 10/2/2023
- macOS 14 Sonoma: The Ars Technica review
a better stab at usable widgets, an improved password manager, promising
gaming enhancements, but fewer new features for Intel Macs; Ars; 9/26/2023 - macOS 14 Sonoma Now Available TB; 9/26/2023
- How to Update macOS MW; 9/26/2023
- macOS compatibility: Find out the latest version your Mac can run MW; 9/26/2023
- How to get your Mac ready for new macOS update MW; 9/26/2023
- How to clean install macOS MW; 9/25/2023
- macOS Sonoma compatibility: The Macs that run macOS 14 MW; 9/25/2023
- macOS Monterey 12.6.9 & macOS Big Sur 11.7.10 Released OSXD; 9/11/2023
- macOS 13 Ventura superguide MW; 9/7/2023
- OS Security Updates Plug Image and Wallet Vulnerabilities macOS Ventura 13.5.2; TB; 9/7/2023
- Safari 16.6 macOS 12 Monterey and macOS 11 Big Sur; TB; 7/26/2023
- Apple Releases 24-Jul-2023 Security Updates for All Active Operating Systems TB; 7/24/2023
- Apple releases macOS Ventura 13.5 with nearly 30 security updates MW; 7/24/2023
- Rapid Security Responses for macOS Ventura 13.4.1 (c) TB; 7/13/2023
- Safari 16.5.2 Monterey; TB; 7/11/2023
- Apple releases macOS Ventura 13.4.1 update with critical security fixes
for older Macs, updates to macOS Monterey (12.6.7) and macOS Big Sur (11.7.8) address the kernel issue; Safari 16.5.1; MW; 6/21/2023 - The Real System Requirements for Apple's 2023 Operating Systems TB; 6/19/2023
- macOS Monterey 12.6.6 and Big Sur 11.7.7, Safari 16.5 TB; 5/19/2023
- macOS 13.4 Ventura TB; 5/18/2023
- How to run multiple copies of the same app on your Mac Terminal or multiple users; MW; 5/16/2023
- A detailed record of macOS and its security updates macOS 10.12 -; 5/8/2023
- What Are Rapid Security Responses and Why Are They Important? TB; 5/2/2023
- You Can Run Windows 11 on Your Apple Silicon Mac for Free with workarounds; LH; 4/19/2023
- macOS Monterey 12.6.5 and Big Sur 11.7.6, Safari 16.4.1 TB; 4/10/2023
- macOS 13.3.1 Addresses Serious Security Vulnerabilities, Fix Bugs TB; 4/7/2023
- How to remove startup and login items on your Mac MW; 4/7/2023
- How to download an old version of macOS: Get Monterey, Big Sur -- back to 10.7 Lion MW; 3/22/2023
- Run MacOS Ventura on Unsupported Mac with OpenCore OSXD; 2/17/2023
- macOS Big Sur 11.7.4, Safari 16.3.1 TB; 2/15/2023
- You can run Mac OS 9 on your new Mac MW; 2/13/2023
- How to use classic Mac, Lisa, NeXT, Apple II software on your Mac emulators; ApIn; 1/31/2023
- Apple Releases macOS 13.2 Ventura with Hardware Security Key Support TB; 1/23/2023
- macOS Monterey 12.6.3 and Big Sur 11.7.3, Safari 16.3 TB; 1/23/2023
- Lock down your Mac with these 10 security tips
Choose a strong login password;
Change your Lock Screen settings;
Use Apple's password manager (or other PM);
Turn on Find My Mac; Set up multiple users;
Lock down your Mail; Limit your app downloads;
Keep your software up to date; Use a VPN;
Augment Apple’s XProtect antivirus; MW; 1/5/2023 - Got a new Mac? Do these 10 things first MW; 12/25/2022
- Run Mac OS 8 in Your Browser OSXD; 12/10/2022;
Run System 7 in a Web Browser with Infinite Mac OSXD; 11/22/2022 - How to Allow Apps to be Downloaded & Opened from Anywhere on MacOS Ventura
modify System Settings via Terminal; or ctrl-click > Open; OSXD; 11/17/2022 - Apple Releases macOS 13 Ventura, ... TB; 10/24/2022
- macOS 13 Ventura: The Ars Technica review Ars; 10/24/2022
- macOS Monterey 12.6 and Big Sur 11.7, Safari 16 TB; 9/12/2022
- There's hope that older Macs will be able to run macOS Ventura
unsupported/slow via OpenCore Legacy Patcher; ApIn; 8/22/2022 - Safari 15.6.1 for macOS 11 Big Sur and 10.15 Catalina; TB; 8/19/2022
- macOS 12.5.1 Monterey and ... Address Serious Security Vulnerabilities TB; 8/17/2022
- macOS Monterey superguide: How to update your Mac with the latest features MW; 7/29/2022
- Ars Technica Tracks Mac Update Lifespans TB; 7/27/2022
- macOS Big Sur 11.6.8 and Security Update 2022-005 Catalina, Safari 15.6 TB; 7/22/2022
- Apple's Lockdown Mode offers extreme security for iPhone, iPad, and Mac
feature in iOS 16, iPadOS 16, and macOS Ventura is meant to protect those targeted by state-sponsored mercenary spyware; MW; 7/6/2022 - Some Macs are getting fewer updates than they used to. Here's why it's a problem Ars; 7/1/2022
- macOS 11.6.7 Big Sur Fixes Email Attachment Bug TB; 6/23/2022
- Take a stroll through the history of Mac OS from 1984’s System 0.97 to Ventura MW; 6/21/2022
- macOS Big Sur 11.6.7 update is now available MW; 6/9/2022
- Apple Releases macOS 12.4, ... TB; 5/16/2022
- macOS 12 Monterey: Features, known problems and fixes in the latest version MW; 5/16/2022
- macOS Big Sur 11.6.6 and Security Update 2022-004 Catalina Safari 15.5 TB; 5/16/2022
- Boot up classic Mac OS in your browser window with the “Infinite Mac” project System 7, Mac OS 8; Ars; 4/1/2022
- Monterey 12.3.1 brings bug fixes and patches a critical security hole MW; 3/31/2022
- Apple thinks macOS security is unacceptable -- here's how to keep your Mac safe
Keep your Mac updated;
Only downloads apps you trust (from places you trust);
Use a strong Mac password; Develop better online habits;
Enable FileVault encryption, and the firewall;
Review your privacy & security settings;
Turn on 'Find My'; Disable automatic Wi-Fi joining;
Back up your Mac; Consider security apps; Use a VPN;
ApIn; 3/31/2022 - macOS 12.3 Monterey Bricking Some Repaired 14- and 16-inch MacBook Pros TB; 3/17/2022
- Apple Releases macOS 12.3 Monterey, etc. TB; 3/14/2022
- macOS Big Sur 11.6.5 and Security Update 2022-003 Catalina TB; 3/14/2022
- A Practical Guide to Securing Your Mac NYT; 3/4/2022
- Google announces early access to Chrome OS Flex, a version of Chrome OS for businesses and schools that is designed to run on old PCs and Macs
Chrome OS Flex; Verge; 2/15/2022 - What you need to know: macOS Big Sur, macOS Catalina MW; 2/14/2022
- Apple might have to break some of its biggest 2021 promises
iOS, macOS feature delays; MW; 12/12/2021 - [2] How to download an old macOS installer ApIn; 12/3/2021
- Apple isn’t actually patching all the security holes in older versions of macOS Ars; 11/12/2021
- macOS Monterey: Update now or wait? MW; 11/5/2021
- Apple fixes bug that caused macOS Monterey update to brick some Apple T2 Macs Ars; 11/5/2021
- macOS 12 Monterey Upgrade Issues TB; 11/3/2021
- macOS Big Sur 11.6.1 and Security Update 2021-007 Catalina, Safari 15.1 TB; 10/30/2021
- Microsoft reports SIP-bypassing "Shrootless" vulnerability in macOS
patched in all three currently supported versions of macOS:
Monterey 12.0.1, Catalina with Security Update 2021-007, Big Sur 11.6.1; Ars; 10/29/2021 - macOS 12 Monterey: The Ars Technica review Ars; 10/25/2021
- Apple Releases macOS 12 Monterey TB; 10/25/2021
- Device Software Updates Now Appear in Software Update Too TB; 10/20/2021
- [3] How to Install the Latest macOS on an Unsupported Mac
OpenCore Legacy Patcher; limitations; LH; 10/6/2021 - Apple releases rare Device Support Update for macOS
update ensures proper updating and restoring for iOS and iPadOS devices with a Mac; MW; 9/30/2021 - Apple Releases Security Update 2021-006 for Catalina to Block Exploited Vulnerabilities TB; 9/23/2021
- Safari 15 for macOS now available: New macOS tabs will transform your workflow for Big Sur & Catalina; MW; 9/21/2021
- macOS 11.6 Big Sur and Security Update 2021-005 Catalina Fix Security Flaws and iOS 14.8, iPadOS 14.8, watchOS 7.6.2; TB; 9/13/2021
- How to reset the NVRAM, PRAM, and SMC on any Mac MW; 8/17/2021
- Apple releases macOS Big Sur 11.5.1 with a security update MW; 7/27/2021
- Apple Releases iPadOS 14.7 and macOS 11.5 with Security Notes for Recent OS Updates TB; 7/22/2021
- Security Update 2021-004 Catalina and 2021-005 Mojave TB; 7/22/2021
- Safari 14.1.2 TB; 7/22/2021
- Apple issues Safari update for macOS Catalina and macOS Mojave ApIn; 7/19/2021
- Apple Makes OS X Lion and Mountain Lion Free to Download
previously $20; MR; 6/30/2021 - How to Install Safari Extensions on Mac OSXD; 6/26/2021
- Apple announces macOS Monterey, the next Mac desktop operating system Ars; 6/7/2021
- Here are the devices that can run iOS 15, iPadOS 15, macOS Monterey, and watchOS 8 Verge; 7/7/2021
- Security Update 2021-003 Catalina and 2021-004 Mojave, Safari 14.1.1 TB; 5/26/2021
- iOS 14.6, iPadOS 14.6, macOS 11.4 Big Sur, watchOS 7.5, and tvOS 14.6 TB; 5/24/2021
- Clear Space to Fix Catalina Update Restart Loop TB; 5/12/2021
- Apple Releases iOS 14.5.1, iPadOS 14.5.1, macOS 11.3.1, and watchOS 7.4.1 TB; 5/3/2021
- Safari 14.1 TB; 4/30/2021
- Apple Releases iOS 14.5, iPadOS 14.5, macOS 11.3, watchOS 7.4, and tvOS 14.5 TB; 4/26/2021
- Is It Safe to Upgrade to macOS 11 Big Sur? TB; 3/10/2021
- How to revive or restore an unresponsive Mac from another Mac MW; 3/10/2021
- iOS 14.4.1, iPadOS 14.4.1, macOS 11.2.3 Big Sur, and watchOS 7.3.2 Address WebKit Security Vulnerability TB; 3/8/2021
- Safari 14.0.3 Catalina, Mojave; TB; 3/8/2021
- macOS 11.2.2 Protects MacBook Pro and MacBook Air from Non-Compliant USB-C Hubs and Docs TB; 2/26/2021
- Mac App Frozen? 9 Tips for How to Handle Freezing Mac Apps OSXD; 2/22/2021
- macOS Catalina 10.15.7 Supplemental Update and Security Update 2021-002 (Mojave) TB;2/9/2021
- macOS 11.2.1 Big Sur Fixes MacBook Pro Charging Bug and sudo Vulnerability TB; 2/9/2021
- New features in macOS Big Sur 11.3: Safari customization options, enhanced support for iPhone/iPad apps on M1 Macs, and more MW; 2/3/2021
- macOS 11.2 Big Sur Improves Bluetooth, Squashes Bugs TB; 2/1/2021
- Security Update 2021-001 (Catalina and Mojave) TB; 2/1/2021
- How to Download MacOS Installers for New & Old Versions if App Store is overloaded; OSXD;
- macOS Big Sur Slow or Laggy? 8 Tips to Help Speed Up the Mac Again OSXD; 1/20/2021
- [3] Can You Install macOS Big Sur on Unsupported Macs? Yes, But It's Not Simple; OSXD; 1/15/2021
- macOS Big Sur: Guides, how-tos, tips, and everything you need to know about Apple's new Mac OS MW; 12/28/2020
- Some Big Sur users are unable to update macOS due to an MDM bug Ars; 12/18/2020
- 35 free macOS apps every Mac user should have MW; 12/18/2020
- Apple Releases macOS 11.1 Big Sur TB; 12/14/2020
- Security Update 2020-001 (Catalina) and 2020-007 (Mojave) Safari 14.0.2 TB; 12/14/2020
- How to check a Mac's OS upgrade history in System Profiler MW; 12/9/2020
- How to upgrade from an older Mac operating system to macOS Catalina or Big Sur MW; 12/3/2020
- How to set up a Mac to run either macOS Mojave or macOS Big Sur for 32-bit apps; MW; 12/1/2020
- Safari 14.0.1 TB; 11/17/2020
- Security Update 2020-006 (Mojave and High Sierra) TB; 11/17/2020
- macOS Big Sur telling Apple what app you've opened isn't a security or privacy issue GateKeeper; ApIn; 11/15/2020
- Big Sur Is Here, But We Suggest You Say 'No Sir' for Now TB; 11/13/2020
- How to create a bootable macOS Big Sur (11.0) installer drive also macOS 10.7 - 10.15; MW; 11/13/2020
- How to Prepare for MacOS Big Sur OSXD; 11/12/2020
- macOS 11.0 Big Sur: The Ars Technica review Ars; 11/12/2020
- Apple Updates Numerous Operating Systems for Exploited Security Vulnerabilities: MacOS Catalina 10.15.7 Supplemental TB; 11/5/2020
- macOS 10.14.6 Mojave Supplemental Update Fixes Problems with an Updated Safari 14.0 TB; 10/2/2020
- Security Update 2020-005 (Mojave and High Sierra) TB; 9/28/2020
- Safari 14 macOS Catalina & Mojave; TB; 9/17/2020
- All Your Questions on Apple’s Move Away from Intel, Answered Wired; 9/7/2020
- Moving to a New Mac: What's Left to Do After Migration? TB; 9/7/2020
- What the 'Legacy System Extension' Mac Message Means & What To Do About It OSXD; 8/8/2020
- This app lets you experience Mac OS (8.1) like it was 1991 all over again TNW; 7/29/2020
- Security Update 2020-004 (Mojave and High Sierra); Safari 13.1.2 TB; 7/20/2020
- iOS 13.6, iPadOS 13.6, macOS 10.15.6, watchOS 6.2.8, and tvOS 13.4.8 add News Features, Car Keys, Symptom Tracking; TB; 7/15/2020
- Apple releases iOS and iPadOS 13.6, macOS 10.15.6, and watchOS 6.2.8 Ars; 7/15/2020
- Kernel Vulnerability Causes Apple to Update All Operating Systems TB; 6/1/2020
- Safari 13.1.1, Security Update 2020-003 (Mojave and High Sierra) OSXD; 5/27/2020
- The macOS Catatina 10.15.5 update is now available with Battery Health Management, FaceTime updates and more MW; 5/26/2020
- How to share downloaded apps across users on a Mac MW; 5/9/2020
- How to use Mac Recovery Mode whether it's to fix problems with your Mac, or get it ready to sell on to someone else, macOS Recovery, also known as Mac Recovery Mode, is a powerful tool to help you; ApIn; 4/28/2020
- How to Display User ~/Library Folder in MacOS Catalina OSXD; 4/23/2020
- Apple Releases macOS 10.15.4 Catalina, watchOS 6.2, tvOS 13.4, and iOS 13.4 for HomePod TB; 3/24/2020
- Security Update 2020-002 (Mojave and High Sierra), Safari 13.1 TB; 3/24/2020
- [3] How to Downgrade a New Mac to Mojave from Catalina TB; 1/3/2020
- [2] Solving the Mac OS 8’s Y2K20 Bug TB; 1/3/2020
- Apple Pushes Out iOS 13.3, iPadOS 13.3, iOS 13.3 for HomePod, macOS 10.15.2 Catalina, watchOS 6.1.1, and tvOS 13.2; Safari 13.0.4 TB; 12/10/2019
- How to get an old macOS installer from Apple ApIn; 11/23/2019
- [2] How to Install MacOS Catalina on Unsupported Macs DosDude Catalina Patcher utility; OSXD; 11/8/2019
- [3] How to Download and Install Older macOS Versions With Terminal LH; 11/6/2019
- Security Update 2019-001 (Mojave) and 2019-006 (High Sierra), Safari 13.0.3 TB; 10/30/2019
- Apple Releases macOS 10.15.1 Catalina, watchOS 6.1, and tvOS 13.2 TB; 10/29/2019
- Six Reasons Why iOS 13 and Catalina Are So Buggy TB; 10/21/2019
- iOS 13.1.3, iPadOS 13.1.3, and Catalina Supplemental Update Tackle Bugs TB; 10/15/2019
- Review: MacOS 10.15 Catalina Wired; 10/14/2019
- The MacOS Catalina Privacy and Security Features You Should Know Improved Data Protection (more app permissions); Weak Password Warnings; Sender-Block in Mail; Better Screen Time Limits; Enhanced Gatekeeper Technology; View-Only Notes Sharing; 'Find My' Mac Location Smarts; Secure Activation Lock; Apple ID Access; Secure Home Video; Wired; 10/13/2019
- Why macOS Catalina is breaking so many apps, and what to do about it 32-bit compat for legacy/obsolete apps; Verge; 10/12/2019
- Should You Update to MacOS Catalina? Or Wait? Or Not At All? OSXD; 10/9/2019
- Troubleshooting MacOS Catalina Problems OSXD; 10/9/2019
- 8 hidden features of macOS Catalina
Home theater at last; Revert after a bad upgrade;
Quick picture in picture; Stop typing passwords;
Make time lapses and animations in QuickTime Player; Find your missing devices
Copy files to iOS devices in Finder; Open unapproved software; MW; 10/9/2019 - macOS 10.15 Catalina Ships, Upgrade with Caution backup apps; 32-bit compatibitility; likely bugs; TB; 10/7/2019
- macOS 10.15 Catalina: The Ars Technica review iPad apps come to the Mac and old 32-bit apps go away in a wide-ranging update; Ars; 10/7/2019
- [2] How to make your own bootable macOS 10.15 Catalina USB install drive Ars; 10/7/2019
- How to find out if your Mac's software is 32- or 64-bit if you plan to use macOS beyond Mojave, you need to upgrade any 32-bit apps on your Mac to 64-bit; MW; 10/7/2019
- MacOS Mojave 10.14.6 Supplemental Update 2 Released Security Update 2019-005 for High Sierra, Sierra; OSXD; 9/26/2019
- Apple's Fall OS release schedule is weird -- here's when your device will be updated Fall 2019 operating system updates for Mac, iPhone, iPad, Apple Watch, and Apple TV are staggered all over the place; MW; 9/24/2019
- Safari 13 Released for Mac Mojave, High Sierra; get 13.0.1 (or later); OSXD; 9/20/2019
- [3] Moving to Catalina: Keep Your 32-Bit Mac Apps Running with Parallels TB; 9/18/2019
- How to Selectively Install Updates from MacOS Software Update OSXD; 9/17/2019
- [2] What to do if you’re worried about the legitimacy of a downloaded software installer Apple developers get an extra layer of security that you can check; MW; 9/4/2019
- New Supplemental Update for MacOS Mojave 10.14.6 Released OSXD; 8/26/2019
- macOS Mojave 10.14.6 Supplemental Update wakeup from sleep issue; TB; 8/2/2019
- Security Update 2019-004 (High Sierra and Sierra) TB; 7/29/2019
- MacBook Pro vs MacBook Air: Which is the better buy? AI; 7/27/2019
- Safari 12.1.2 for 10.13.6 High Sierra and 10.12.6 Sierra; TB; 7/25/2019
- Apple Releases macOS 10.14.6, iOS 12.4, watchOS 5.3, tvOS 12.4, and More TB; 7/22/2019
- Go64 review: Free utility preps Mac users for 64-bit Catalina app-ocalypse quickly scans your internal drive for 32-bit applications that won't be compatible after installing macOS Catalina and helps find potential upgrades to keep software working; MW; 7/15/2019
- Browse Dozens of Retro Classic Mac OS Screen Shots from 1984 to 1999 OSXD; 6/30/2019
- [2] Apple to Deprecate Scripting Languages in Future Versions of macOS Python, Ruby, Perl; TB; 6/25/2019
- Can't download an app update? If you're using an older version of macOS, you may run into problems when trying to install the latest version of an app, so update OS; MW; 6/18/2019
- MacOS Catalina Compatibile Macs List OSXD; 6/4/2019
- How to Enable Automatic App Updates in macOS Mojave OSXD; 5/30/2019
- [3] How to Turn a Windows Laptop Into the Touchscreen Hackintosh of Your Dreams MB; 4/26/2019
- macOS Mojave 10.14.5 Supplemental Update for MacBook Pro (2018, 2019) TB; T2 security chip; 5/23/2019
- Apple Releases iOS 12.3, macOS 10.14.5, watchOS 5.2.1, and tvOS 12.3 and Debuts New Apple TV App mitigates ZombieLoad; TB; 5/13/2019
- iOS 12.2 and macOS 10.14.4 Add Apple News+ and Enhance Apps; TB; 3/25/2014
- How to Check What Mac OS Version is Running on a Mac OSXD; 2/16/2019
- [2] How to Fix App 'is damaged and can’t be opened. You should move it to the Trash' Error on Mac OSXD; 2/13/2019
- Apple Re-Enables Group FaceTime with iOS 12.1.4 and macOS 10.14.3 Supplemental Update and other security fixes; TB; 2/7/2019
- How to reinstall macOS if macOS Recovery is unavailable with internet connection; MW; 2/4/2019
- Apple Releases macOS 10.14.3 with Bug Fixes and iOS 12.1.3, watchOS 5.1.3, and tvOS 12.1.2; TB; 1/22/2019
Meltdown / Spectre / ZombieLoad (hardware CPU flaws)
- Apple Patches ZombieLoad Vulnerabilities in macOS 10.14.5 and Security Update 2019-003 for Sierra and High Sierra; TB; 5/15/2019
- A side-channel flaw called ZombieLoad affects nearly all post-2011 Intel chips; Apple, Microsoft, Google release fixes today that, like Spectre, hit performance Zombieload; TC; 5/14/2019
- All Intel chips open to new Spoiler non-Spectre attack Don't expect a quick fix; researchers say Intel won't be able to use a software mitigation to fully address the problem Spoiler exploits; ZD; 3/5/2019
- [3] Google: Software is never going to be able to fix Spectre-type bugs Ars; 2/23/2019
Office Suites (Microsoft & others)
- Ethical.net: Office
- BBEdit 15.0.2 TB; 3/21/2024
- Microsoft Office For Mac buying guide
Microsoft 365 and Office 2021; MW; 3/20/2024 - Office 2024 for Mac is coming and you won’t need a subscription to get it 'perpetual' (5 year) standalone license; MW; 3/20/2024
- Microsoft Office for Mac 16.83 TB; 3/13/2024
- How to Use Microsoft Office (365) on the Web for Free login with free account into office.com; limited functionality; Giz; 2/19/2024
- BBEdit 15 Adds ChatGPT, Minimap, Cheat Sheets, and More TB; 1/11/2024
- Pages 13.2, Numbers 13.2, and Keynote 13.2 TB; 9/25/2023
- How to get Microsoft Word for free on Mac Office 365; MW; 3/17/2023
- Microsoft Office Updates Now Require macOS 11 Big Sur or Later TB; 12/10/2022
- Pages 12.2, Numbers 12.2, and Keynote 12.2 TB; 10/31/2022
- These G Suite Alternatives Are Cheaper or Free LH; 6/23/2022
- How to Use Microsoft Word for Free Wired; 6/14/2022
- How to Password Protect Pages, Keynote & Numbers Documents on Mac, on iPhone/iPad OSXD; 3/11/2022
- LibreOffice, OpenOffice bug allows hackers to spoof signed docs update; BC; 10/11/2021
- Pages 11.2, Numbers 11.2, Keynote 11.2 TB; 10/1/2021
- Office 2021 will be available for non-Microsoft 365 subscribers on October 5 Ars; 9/16/2021
- The best free office suites PC; 8/16/2021
- BBEdit 14 Adds Simple Notes Management TB; 7/21/2021
- How to set the default settings in TextEdit for macOS ApIn; 7/5/2021
- [2] The Best Mac Site-Specific Browser for Google Docs
site-specific browser (SSB)—a utility turns a site/set of sites into a standalone app;
Coherence X; Chromeless; Flotato; Fluid; Unite; Wavebox; WebCatalog;
extensions: BrowserFairy, Choosy; TB; 6/18/2021 - iWork update brings major changes to Mac, iPhone, and iPad apps
Keynote, Numbers, and Pages 11.2; MW; 9/28/2021 - Microsoft 365 and Office 2019 updates arrive with Apple Silicon and Big Sur support ApIn; 11/12/2020
- Fix 14 Security Issues by Updating Adobe Acrobat and Reader LH; 11/4/2020
- Office 2019 vs. Office 365: Microsoft Office plans compared sStandalone Office is still available, but Microsoft makes its subscriptions far more appealing; PC; 10/12/2020
- How to upgrade from Office 2010 to Office 365 PC; 10/5/2020
- Microsoft ends support for Office 2010: What you can do lots of options, and some are even free: Microsoft 365 online (free), subscription ($); Office 2019 ($); Google, LibreOffice, FreeOffice; PC; 9/14/2020
- Apple updates iWork apps with video embeds, iBooks Author book support macOS, iOS; ApIn; 7/9/2020
- How to open ancient Pages, Numbers, and Keynote documents in macOS MW; 6/12/2020
- How to recover your Pages, Numbers, or Keynote document password probably in your keychain; MW; 6/11/2020
- How to Convert from: Pages to Word, Numbers to Excel, Keynote to Powerpoint with iCloud; OSXD; 5/24/2020
- Adobe patches Acrobat Reader security flaw that could allow root access on Mac ApIn; 5/14/2020
- Pages 10, Numbers 10, and Keynote 10 TB; 4/3/2020
- BBEdit 13 review: A lucky number indeed for revered macOS text editor MW; 11/11/2019
- WPS Office: Full-featured Microsoft-style productivity suite for less review; MW; 10/21/2019
- A look at LibreOffice's new 6.3.0 'fresh' release better import and export of Microsoft Office documents; performance increases, new features, e.g., redaction; Ars; 8/13/2019
- Pages, Numbers, and Keynote productivity apps for iOS and macOS get major update MW; 6/25/2019
- This Amazingly Simple Google Docs Hack Is a Game-Changer doc.net, slide.new, sheet.new; MF; 6/21/2019
- iWork Update Brings iOS Apps Closer to Parity TB; 4/3/2019
- Microsoft really, really, really doesn’t want you to buy Office 2019 Microsoft 365 is a subscription vs. Office 2019 (perpetual license); TC; 2/7/2019
Replace, Switch
- see also: Backup and Erasing your devices
- Apple: Use Quick Start to transfer data from your previous iOS device to your new iPhone, iPad, or iPod touch
- How to troubleshoot migrating from an older Mac to a new one MW; 1/5/2024
- You can now access Apple's official diagnostics tool online for DIY repairs iOS 17+, macOS 14+; Ars; 12/13/2023
- Which Mac laptop is best? MW; 11/17/2023
- The Best Tablets NYT; 11/15/2023
- The iPad Is the Best Tablet NYT; 11/13/2023
- MW; 9/27/2023
- iPhone comparison chart: Every iPhone compared MW; 9/15/2023
- How to sell or trade in your old iPhone
You can get cash for your iPhone from buyback sites, trade it in to your wireless carrier for a credit on future bills,
or even swap it for a gift card to Target, Best Buy, Amazon, or Walmart.
Get an old iPhone ready for sale: Save your data; Unpair your Apple Watch; Sign out of your Apple account; Reset the phone;
Sell your iPhone online to a buyback site: Gazelle, Swappa, Amazon;
Trade in your iPhone for retail store credit: Apple, Target, Best Buy, Walmart;
How to sell your iPhone back to your carrier: AT&T, Verizon, T-Mobile, Sprint;
Tips for selling your phone; MW; 9/6/2023 - Best laptops we recommend CNet; 9/5/2023
- The best laptops: Premium laptops, budget laptops, 2-in-1s, and more PC; 8/30/2023
- The Best Laptops NYT; 8/22/2023
- Best place to buy a refurbished iPad MW; 8/10/2023
- The Best Laptops Verge; 8/7/2023
- How much can you save at Apple's Refurbished Store? MW; 7/6/2023
- Why you should buy a refurbished Mac MW; 7/4/2023
- Best MacBooks: Which Model Should You Actually Buy? Wired; 6/20/2023
- Every Apple Mac and MacBook compared MW; 6/12/2023
- The Best MacBooks NYT; 6/12/2023
- Which iPad You Should Actually Buy (and Which to Avoid); Wired; 3/29/2023
- Does your laptop feel sluggish? Try these 9 things before you give up PC; 3/9/2023
- When Does an Old iPhone/Android Become a Security Risk? LH; 1/25/2023
- iPad Buying Guide MW; 1/5/2023
- Stop Buying New Apple Devices
buy Certified Refurbished devices instead; LH; 12/8/2022 - Thinking about taking your computer to the repair shop? Be very afraid
Not surprisingly, female customers bear the brunt of the privacy violations; Ars; 11/22/2022 - Where to buy refurbished products LH; 11/21/2022
- How to Revive an Old Computer for Your Kid -- or Decide on a New One NYT; 8/24/2022
- 11 Ways to Repurpose an Old Phone or Tablet LH; 7/19/2022
- How to switch from PC to Mac and migrate your data from Windows to macOS ApIn; 5/30/2022
- Yes, You Can Make Your Tech Survive Obsolescence
Keep your browser up to date;
As always, avoid suspicious behavior; Avoid shady apps;
Secure your online accounts;
Install a Different Operating System;
Repurpose Your Old Device; NYT; 3/23/2022 - Reset Your Computer Once a Year for a Happier Life
it's easier than ever to restore your Mac, PC, or Chromebook to factory conditions
-- and you'll be surprised at how much zip it'll add; Wired; 1/8/2022 - How to sell or trade in your old iPhone MW; 12/27/2021
- 8 Ways to Make Your Old Laptop Feel New Again LH; 10/27/2021
- The True Cost of Upgrading Your Phone
buying a $1,000 phone can be equivalent to giving up $17,000 in retirement savings or 2,500 cups of coffee; NYT; 10/20/2021 - The iPhone 13: An upgrader's guide 9/23/2021
- Upgrading? Here’s What You Can Do With an Old Mobile Device. NYT; 9/22/2021
- Buy or Wait? Here’s a Guide to Phone Upgrades NYT; 8/25/2021
- Best laptop 2021: 15 best laptops we recommend in 2021 CNet; 7/7/2021
- Consumer Desktop Mac Buying Guide: Which Is Right For You? TB; 6/23/2021
- What to do with an old laptop: 10 clever ideas PC; 6/11/2021
- How to make an old PC useful for someone else PC; 5/5/2021
- How to Know When to Upgrade Your PC Giz; 12/25/2020
- The Best Alternatives to Apple's MacBook and Mac Wired; 12/14/2020
- How to transfer all your data from an old iPhone to a new iPhone MW; 12/4/2020
- How to switch an old Windows laptop to Linux Verge; 11/6/2020
- How to Shop for a Used Computer NYT; 10/29/2020
- 10 cheap or free ways to make your old PC run faster PC; 10/28/2020
- When should you replace your PC? | Ask an expert PC; 10/15/2020
- When You Shouldn't Repair Your Mac damage superficial? repairs > $1K? LH; 9/15/2020
- How to test a used Mac before you buy it iCloud lock, firmware passwords, MDM (Mobile Device Management); diagnostics; battery; display; SSD; ApIn; 9/6/2020
- How to Make Your Tech Last Longer NYT; 7/1/2020
- What to Do if Your Old Device Can't Run a New Apple Operating System LH; 6/24/2020
- iPadOS vs Windows vs Chrome OS: Which is the Best Tablet Experience Right Now? Giz; 5/25/2020
- What Happened When I Switched From Macs to Windows Wired; 5/17/2020
- Switching from Android to iPhone made easy MW; 5/7/2020
- Apple's T2 Security Chip Has Created a Nightmare for MacBook Refurbishers previous owner needs to factory reset their machine before selling it or turning it in; MB; 5/4/2020
- How Do I Get My Data Off an Old Computer? LH; 4/10/2020
- Switching from Android to iPhone: Here's where Apple's phone wins and fails PC; 3/26/2020
- Which MacBook Should You Buy? Wired; 2/21/2020
- How to disable accounts on an iPhone, iPad, or iPod touch you sold or gave away MW; 11/22/2019
- What to do when your old iPhone or iPad doesn't run iOS 13 or iPadOS TR; 10/28/2019
- [2] 'Collapse OS' Is an Open Source Operating System for the Post-Apocalypse MB; 10/8/2019
- The iPad Can Finally Replace a Laptop for Most People iPadOS; LH; 9/19/2019
- The Joys of Being a Late Tech Adopter new doesn’t always necessarily mean better, or better in ways that will matter; NYT; 8/29/2019
- The 10 Best Laptops We've Tried favorite Windows Notebooks, MacBooks, and Chromebooks; Wired; 8/15/2019
- A School Laptop Under $500 That Isn't Junk NYT; 8/6/2019
- How to pick the perfect iPhone for you MW; 6/17/2021
- The Best Phone You Can Buy Right Now Verge; 6/16/2021
- 7 ways to make use of your old iPhone
Make it a dedicated music player
Turn it into a kid's entertainment device
Make it an Apple TV remote
Make it a permanent car, bike, or kitchen fixture
Use it as a baby monitor
Turn it into your bedside buddy; MW; 6/10/2019 - 5 signs that you need to replace your iPhone
You can't get iOS updates any longer;
Your screen is trashed but isn't worth fixing;
You're embarrassed by your photos;
You can't find accessories for it anymore;
You're always out of storage space; MW; 5/15/2019 - How to choose between iPad, iPad mini, iPad Air, and iPad Pro 5 models; Verge; 3/30/2019
- Why Does My Laptop Take 30 Minutes to Start Up? TaskManager; check for malware; startup/helper apps? LH; 3/1/2019
- Guidemaster: The least-awful Android phones over 400 Android devices were released in 2018; Ars; 2/21/2019
- How to Save on Your Next Apple Purchase products are more expensive to make; trade in your old device; buy last year's model; wait for sales; buy used or refurbished gadgets; skip the upgrade altogether; NYT; 1/30/2019
Windows
- Wikipedia: Windows; versions: 1.0-11.x; Windows Update; App Store
- Microsoft: Downloads Center
- HowStuffWorks: How Windows 8 Works
- There was once a young man who, in his youth, professed his desire to become a great writer. When asked to define "great" he said, "I want to write stuff that the whole world will read, stuff that people will react to on a truly emotional level. Stuff that will make them scream, cry, and howl in pain and anger!"
He now... - "There are no significant bugs in our released software...
- Microsoft Lifecycle Policy
- Windows-as-a-nuisance: How I clean up a "clean install" of Windows 11 and Edge Ars; 2/23/2024
- How to Stop Programs From Loading When Windows Starts Up
Apps > Startup; Autoruns; Wired; 4/2/2023 - Support for Windows 7 and 8 fully ends in Jan. 2023, including Microsoft Edge Ars; 12/12/2022
- Microsoft releases Windows 11 22H2, formally dubbed the "2022 Update" Ars; 9/20?2022
- Windows 11 22H2 update will be released on September 20
22H2 includes security upgrades, redesigned Task Manager, and other refinements; Ars; 8/16/2022 - How to upgrade to Windows 11 (whether your PC is supported or not) Ars; 8/12/2022
- Windows 10 tips and tricks that help you get stuff done faster PC; 5/30/2022
- How to get Windows 10 cheap (or even for free) PC; 5/20/2022
- How to Use Windows Security to Keep Your PC Protected Wired; 5/1/2022
- The Easiest Ways to Install and Update All Your Windows Apps LH; 4/18/2022
- How to Run Windows 11 on M1 Mac, for Free OSXD; 4/14/2022
- These Windows Apps Are Outdated, Risky, or Scammy LH; 4/4/2022
- Google announces early access to Chrome OS Flex, a version of Chrome OS for businesses and schools that is designed to run on old PCs and Macs
Chrome OS Flex; Verge; 2/15/2022 - Major Windows 11 update, with taskbar tweaks and Android apps, coming in February Ars; 1/26/2022
- Microsoft will now update Windows 10 annually with new features
matches Windows 11 update cadence; Verge; 11/16/2021 - Windows 11 superguide: News, tips, reviews and more PC; 11/11/2021
- Windows 11 FAQ: Everything you need to know PC; 11/10/2021
- It's Windows XP's 20th birthday and way too many still use it BC; 10/25/2021
- 11 Security Settings You Should Know About in Windows 11 Wired; 10/24/2021
- The Windows 11 upgrade checklist PC; 10/6/2021
- You shouldn't upgrade to Windows 11 yet PC; 10/5/2021
- This is what your PC will need to run Windows 11 PC; 10/5/2021
- Windows 11: The Ars Technica review Ars; 10/4/2021
- [2] How to update your PC's BIOS
only if needed; PC; 9/24/2021 - Want Windows 11? Your PC better have these specs PC; 9/8/2021
- Windows 11 arrives on October 5, Android apps will come later
phased rollout will see all compatible PCs updated by ~mid-2022; Ars; 8/31/2021 - Why Windows 11 has such strict hardware requirements, according to Microsoft
security and stability are both much better on newer PCs; Ars; 8/27/2021 - You'll be able to run Windows 11 on older PCs -- if you install the update manually
you won't see it in Windows Update, but Microsoft won't stop you from running it; Ars; 8/27/2021 - When will Windows 11 ship? PC; 6/16/2021
- Make way for Windows 11? Windows 10 end-of-life is 10/14/2025 Ars; 6/15/2021
- 10 truly helpful Windows 10 tools you might not know about PC; 5/24/2021
- Windows 10: The best tricks, tips, and tweaks PC; 5/20/2021
- Dell is issuing a security patch for hundreds of computer models going back to 2009 Verge; 5/4/2021
- How to disable start up programs in Windows 10 to make boot times faster PC; 4/7/2021
- Windows 10: Guides, tips, tricks, and everything you need to know about Microsoft's OS PC; 4/5/2021
- Windows Turns 35: A Visual History from Windows 1.0 to Windows 10; Verge; 11/20/2020
- Reviewed: Windows 10 October 2020 Update inches in the right direction PC; 10/20/2020
- Windows 95 turns 25: Relive the glory days with this nostalgic app PC; 8/24/2020
- How to manage Windows 10 updates to prevent them from ruining your life PC; 6/30/2020
- Homeland Security warns over ‘wormable’ Windows 10 bug TC; 6/8/2020
- Microsoft releases the Windows 10 May 2020 Update PC; 5/27/2020
- The Best Way to Update Windows 10 and All of Your Apps LH; 5/11/2020
- Black wallpaper bug from Windows 7's 'final' update will get fixed PC; 1/27/2020
- N.S.A. Takes Step Toward Protecting World's Computers, Not Just Hacking Them Windows vulnerability; NYT; 1/14/2020
- The Easiest Way to Switch from Windows 7 to Linux LH; 1/14/2020
- Rumors mount that a major bug could be disclosed on the day Microsoft ends support for Windows 7 PC; 1/14/2020
- Windows 7 is dead: How to stay as safe as possible after the security updates stop PC; 1/14/2020
- How to remove your login password from Windows 10 PC; 12/20/2019
- [3] How to Extend Your Windows 7 Security Updates Past January LH; 12/9/2019
- [2] How to remove your login password from Windows 10 PC; 11/26/2019
- What To Do If Your Antivirus Apps or Wifi Drivers Are Blocking Window 10 Updates update Avast/AVG; update Qualcomm drivers; LH; 11/25/2019
- How to See Which Features Microsoft Killed in Every Windows 10 Update LH; 11/14/2019
- The Best Features in Windows 10 Version 1909 LH; 11/13/2019
- If You're Still Using Windows 7, You Need This Security Update BlueKeep miner; LH; 11/4/2019
- Windows 10 November 2019 Update review: Fewer features now, bigger changes later Windows Search-powered File Explorer, some notifications improvements, and easy calendar appointment creation; PC; 10/17/2019
- The Best Free MS-DOS Games Now Available From the Internet Archive LH; 10/16/2019
- Windows 7 popup warnings to update to Windows 10 will soon reappear PC; 10/15/2019
- Microsoft's next Windows 10 feature update gets a name: the Windows 10 November 2019 Update PC; 10/10/2019
- The Best Features Coming in Windows 10 Version 1909 LH; 10/7/2019
- Windows 10: What to expect in the next two releases 19H2, 20H1; PC; 9/24/2019
- The Windows 10 Privacy Settings You Should Check Right Now Wired; 9/7/2019
- How to 'Refresh' Your PC When Windows Says There's a Problem LH; 8/22/2019
- Four wormable bugs in newer versions of Windows need your attention now Exploits against Windows 7 to 10 could spread from PC to PC--no user interaction needed; Ars; 8/13/2019
- The Best Ways to Get Windows 10 for Free install & run w/o activating; upgrade from older version; student/alumni; cheap OEM key; LH; 8/13/2019
- How To Undo and Prevent Windows Updates LH; 7/16/2019
- Microsoft's 'Stranger Things' Gag Doesn't Make Sense Because No One Used Windows 1.0 cultural nonentity in 1985; MB; 7/8/2019
- Microsoft is teasing Windows 1.0 and other 1980s software get MS-DOS Executive, Paint, and Reversi; Ars; 7/2/2019
- Microsoft's fall release of Windows 10 will be deliberately anticlimactic PC; 7/1/2019
- Microsoft Patches ‘Wormable' Flaw in Windows XP, 7 and Windows 2003 Krebs; 5/14/2019
- You Can Run Windows 1.0 Right Now, in a Web Browser OSXD; 4/19/2019
- Hackers Hijacked ASUS Software Updates to Install Backdoors on ~500K Windows computyers for at least five months last year, after its live software update tool was compromised; MB; 3/25/2019
- Microsoft: Windows 10 can now automatically uninstall buggy updates along with blocks on releasing Windows 10 to certain users, Microsoft will now remove updates that aren't compatible with the installed version of Windows 10; ZD; 3/12/2019
- Windows 7 end-of-life nag messages will start showing up next month Microsoft promises you'll be able to turn them off; Ars; 3/12/2019
- Windows 10 should never reboot your PC without your express permission, researchers conclude What Microsoft could do better: Educate users, improve Windows Update controls, and commit to rebooting only when the PC is not in active use; PC; 2/26/2019
- Mandatory update coming to Windows 7, Server 2008 to kill off weak update hashes phasing out SHA-1; Ars; 2/19/2019
- How to Rediscover the Windows Start Menu's Utility Giz; 2/6/2019
- How to Install Windows 10 on Mac with Boot Camp OSXD; 2/1/2019
- Windows 10's April 2019 Update should be as straightforward as its name PC; 1/25/2019
- Microsoft: Switch to iOS or Android because Windows 10 Mobile is ending Ars; 1/18/2019
- Latest Windows Service Packs and Updates 1/15/2019
- Windows 7 enters its final year of free support Up to three years of paid support will be available after the cut-off: 1/14/2020; Ars; 1/14/2019
Safer Internet: Offline: Encryption
Safer Internet: Offline: Encryption
Quotes | Summary | Intro | Device | Cloud | Notes | Indiv. Files |
References: General | Android | FBI (vs. Apple) | Government; Backdoor |
iOS | macOS | Quantum | Windows
Quotes
- "Dear Dr. Weyer: Thank you for contacting me about the Federal Bureau of Investigation's (FBI) request...
- Must you surrender a password to law enforcement?...
- "The Constitution sometimes insulates the criminality of a few in order to protect the privacy of us all"...
- "The Supreme Court and all courts established by Act of Congress may issue all writs necessary...
- "There are two types of encryption:...
- "Encryption should be enabled for...
- "The government does things like insisting that...
- "You can't distinguish a properly encrypted communication from random behaviour...
Summary
- [1] Use a password manager to encrypt, store and access all of your passwords;
e.g., 1Password; see: P@s$w0rdz course - [1] Encrypt device and backups with a strong password to prevent access to sensitive files,
e.g., Mac: FileVault, Win: BitLocker - [1] Check encryption on cloud files/backups, i.e., private key?
- Very secure-- depending on how files are encrypted and stored, and who has access.
- For brief explanation of different levels of security (via encry ption) for Local and Cloud, see P@s$w0rdz:Storing:Encrypt
- [2] Encrypt notes (less necessary if device & backups encrypted)
- [3] Encrypt individual files or folders (ditto)
- References
Encryption: Intro
- We'll cover various kinds of encrypted internet connections later under Internet Connection: Wi-Fi, VPN and Web Browsing: HTTPS, shopping, Email, Talk and Chat
- With today's faster processors, there's no perceptible delay for encryption/decryption.
- For strong encryption, look for "AES-128" or "AES-256" (Advanced Encryption Standard) -- and create a strong password!
- Avoid weak encryption, i.e., weak password (even with AES-128,-256), or older .zip format; standard .pdf or Office file
- Backup any encryption or recovery key somewhere secure, e.g., password manager, SD box
- If you also save recovery key in cloud (iCloud, Microsoft), you could conveniently access it, but so could government (legally or illegally) or hackers
- Encryption becomes more vulnerable over time with faster processing, better algorithms, uncovered backdoors, more invasive laws / exceptions, quantum computers.
- As a last resort, if you must share sensitive info, e.g., key, credit card, password, and end-to-end encryption is not available (email is typically decrypted at server, or your recipient may not be as careful as you are), communicate the information in fragments, e.g., separate emails, or use an alternate channel, e.g., text or phone
[1] Encrypt Entire Device / Disk -- and Backups
- It's simpler to just encrypt entire drive rather than selected files.
- iOS9+: automatic -- assuming strong (> 6 digit) passcode; also for recent Android
- macOS:
System Preferences > Security & Privacy > FileVault;
i.e., FileVault 2; not recommended: "Legacy" FileVault (version 1) -- see Mac: FileVault references - You'll have to re-enter password after Logout / Shutdown, or sleep timeout; if you have a very strong macOS account password, you could encrypt using that same password and have it saved in KeyChain for convenience
- Encrypt backup (incremental & clone) partitions/drives, e.g.,
- macOS:
Time Machine > Open Time Machine Preferences > (partition/disk) > Encrypt backups-- note much faster to encrypt during original partition/erase, rather than later - macOS: Carbon Copy Cloner: boot backup system, enable File Vault -- see Mac: Carbon Copy Cloner, FileVault references
[1] Encrypt Cloud Files & Backups
- See Backups for earlier discussion of cloud storage
- Files are normally encrypted in transit -- from your device to the cloud server
- Many cloud services then encrypt the files based on their key and/or your account password;
the files are accessible not only to you, but also to the provider, and by subpoena, to the government;
also, if file/folder URL is shared or discovered, anyone could access file - More secure cloud services, e.g., BackBlaze, support use of a private key known only to you (different from your password).
- The cloud service cannot decrypt files without this key, even under government demand -- more secure and preferable.
[2] Encrypt Notes
- If you have a strong device password and full device encryption, this may be unnecessary
- iOS:
Notes > (share icon) > Lock Note - macOS:
Keychain Access > Secure Notes
[3] Encrypt Individual Files / Folders
- For individual files / folders, use "zip" utility w/ strong encryption, e.g., 7-Zip (Win, Linux) or Keka (macOS ), or recent WinZip -- not older original zip format
- 'Password protection' provided by some apps, e.g., Word, .pdf, may be weak
- If you want to encrypt more than a few files, and don't want to encrypt entire disk (or have an older Mac system), you can create a 'Disk Image' (embedded, compressed volume)
- macOS:
Disk Utility > File > New > Blank Image > encryption, image format: sparse bundle
References
- sections: Refs: Android; FBI (vs. Apple); Government; Backdoor; iOS; macOS; Quantum; Windows
- see sections: Anonymity:NSA; Backup:Cloud, Backup:iCloud; Malware; Mobile:Border; Who:Government
- topics: AES, backdoors, Cellebrite, certificates, CIA, DOJ, FISA, Graykey, NSA, PGP, public key cryptography, TLS, Wyden
- EFF: What Should I Know About Encryption
- Wikipedia: Cryptography; encryption; Multiple encryption; cryptographic privacy and authentication for data communication
- Wikipedia: Steganography concealing a (secret) file, message, image, or video within another (ordinary) file, message, image, or video;
intended secret message does not attract attention to itself; example: cat hidden within tree image - Wikipedia: Symmetric Key e.g., AES; use the same cryptographic keys for both encryption of plaintext and decryption of ciphertext; for communication, requires secure initial exchange of one (or more) secret keys between the parties
- Wikipedia: Advanced Encryption Standard (AES) 128-, 192-, 256-bit
- Wikipedia: Data Encryption Standard (DES) obsolete, insecure 56-bit; target of 3/2015 FREAK attack
- Wikipedia: Public Key aka asymmetric cryptography; e.g., SSL/TLS, S/MIME, PGP, and GPG; requires two separate (but mathematically linked) keys, one of which is secret (or private) and one of which is public; public key is used to encrypt plaintext or to verify a digital signature; whereas the private key is used to decrypt ciphertext or to create a digital signature; computationally infeasible for a properly generated private key to be determined from its corresponding public key
- Wikipedia: Transport Layer Security (TLS); RC4 (Rivest Cipher 4)
- Wikipedia: RSA; Certificate authority; digital, public key certificates
- Wikipedia: postal analogy: symmetric vs. asymmetric
- Wikipedia: Cryptanalysis Cryptanalytic attack; Key size; Brute-force attack; Backdoor
- Wikipedia: Kleptography stealing information securely and subliminally, e.g., via cryptographic backdoor
- Wikipedia: Pretty Good Privacy (PGP); Bitcoin: digital currency; Blockchain
- HowStuffWorks: How Encryption Works; What is a digital signature?; How Code Breakers Work
- Wikipedia: .zip file format; 7-zip
- 7-zip free; Windows; macOS (Keka); AES-128, AES-256; How to Use 7-Zip to Encrypt Files and Folders
- WinZip commercial; Windows, macOS; AES-128, AES-256
- SCIpher - A Scholarly Message Encoder encodes (not encrypts) text message within a fake "Call for Papers"; ;-)
- Eight Secure Ways to Share Sensitive Information over the Internet
Data at Rest and in Transit?
Secure service like DocuSign
iMessage/Signal/WhatsApp
1ty.me or One-Time Secret self-destructing link
1Password limited link
Password-protected PDF
Password-protected disk image
Password-protected Zip archive
Cloud storage link that can be expired
TB; 1/23/2024 - A Popular Password Hashing Algorithm (bcrypt) Starts Its Long Goodbye Wired; 5/25/2023
- How to Encrypt any File, Folder, or Drive on Your System Wired; 1/22/2023
- How to Password Protect Any File
Microsoft Word, Excel, and PowerPoint;
Google Docs, Sheets, and Slides;
Apple Pages, Numbers, and Keynote; Wired; 6/19/2022 - Steps to Simple Online Security: 4: Encrypt Your Computer's Storage NYT; 4/8/2022
- Math That Helped Solve Fermat's Theorem Now Safeguards the Digital World
elliptic curve cryptography; NYT; 1/31/2022 - What is encryption? PC; 10/1/2021
- How to Encrypt Your Own Windows and Mac Devices (and Why You Need To)
FileVault, BitLocker, USB drives; LH; 8/17/2021 - 7-Zip developer releases the first official Linux version BC; 3/11/2021
- NSA urges system administrators to replace obsolete TLS protocols ZD; 1/20/2021
- How law enforcement gets around your smartphone's encryption Ars; 1/15/2021
- How Law Enforcement Gets Around Your Smartphone's Encryption
iOS, Android: Complete Protection (when off) vs. Protected Until First User Authentication
-- aka After First Unlock (AFU); Wired; 1/13/2021 - Zodiac Killer message known as '340 Cipher' solved after 51 years
the coded message was sent to the San Francisco Chronicle in 1969; CNet; 12/11/2020 - Microsoft Office encryption evolution: from Office 97 to Office 2019 10/31/2019;
- Dangerous SHA-1 crypto function will die in SSH linking millions of computers Ars; 5/28/2020
- How to Get the Most Out of Your Smartphone's Encryption both iPhones and Androids are encrypted by default. But there are steps you can take to safeguard your data on backups and messaging apps; Wired; 1/29/2020
- [2] PGP keys, software security, and much more threatened by new SHA1 exploit Ars; 1/7/2020
- What Is End-to-End Encryption? Another Bull’s-Eye on Big Tech; NYT; 11/19/2019
- [2] PDF flaw lets hackers read password-protected documents, researchers say TNW; 10/2/2019
- [3] A Plan to Stop Breaches With Dead Simple Database Encryption MongoDB, Field Level Encryption; Wired; 6/18/2019
- Cellebrite Says It Can Unlock Any iPhone for Cops Wired; 6/14/2019
Android
- Google wants to bring encryption to all with Adiantum every Android device can be encrypted, even those with low-end processors; Verge; 2/11/2019
FBI (vs. Apple)
- The FBI wanted to unlock the San Bernardino shooter’s iPhone. It turned to a little-known Australian firm. Azimuth; WaPo; 4/14/2021
- iPhone crypto hid al-Qaida link to naval base shooting, AG fumes investigators say they spent 4 months and huge sums to decrypt suspected iPhones; Ars; 5/18/2020
- What Apple surrenders to law enforcement when issued a subpoena AI; 1/21/2020
- Apple dropped plan for encrypting backups after FBI complained Reut; 1/21/2020
- Apple Takes a (Cautious) Stand Against Opening a Killer's iPhones NYT; 1/14/2019
Government; Backdoor
- US courts have generally accepted that telling the government a password or encryption key is "testimony." A police officer cannot force or threaten you into giving up your password or unlocking your electronic devices. However, a judge or a grand jury may be able to force you to decrypt your devices in some circumstances.
- Wikipedia: Right to silence; self-incrimination; 5th Amendment; passwords; U.S. v. Fricosu
- Wikipedia: Key disclosure law; key escrow; National security letter
- NSA Says 'No Backdoor' for Spies in New US Encryption Scheme
NIST agency running competition for new encryption standards;
Quantum computing comes with risks for modern data protection; 5/13/2022 - Another Illinois Appeals Court Handles Compelled Password Production, Says There's No Fifth Amendment Issue Here TD; 12/23/2021
- NSA ducks questions about 'back doors' in tech products Reut; 10/28/2020
- The Police Can Probably Break Into Your Phone
phone-hacking tools typically exploit security flaws to remove a phone's limit on passcode attempts and then enter passcodes until the phone unlocks. Because of all the possible combinations, a six-digit iPhone passcode takes on average about 11 hours to guess, while a 10-digit code takes 12.5 years; NYT; 10/21/2020 - Russia wants to ban the use of secure protocols such as TLS 1.3, DoH, DoT, ESNI amendment to IT law would make it illegal to use encryption protocols that fully hide the traffic's destination (ok: https:); ZD; 9/22/2020
- Iranian Hackers Can Now Beat Encrypted Apps, Researchers Say the hackers use a variety of infiltration techniques, including phishing, but the most widespread method is sending what appear to be tempting documents and applications to carefully selected targets; NYT; 9/18/2020
- NJ Supreme Court ruled that compelling a suspect to unlock their cell phone doesn't violate Fifth Amendment following opposite ruling by Indiana SC in June; Ars; 8/11/2020
- Is It Legal for Cops to Force You to Unlock Your Phone? Because the relevant Supreme Court precedents predate the smartphone era, the courts are divided on how to apply the Fifth Amendment; Wired; 6/27/2020
- It's unconstitutional for cops to force phone unlocking US courts disagree; forcing people to provide computer or smartphone passwords would violate the Fifth Amendment (right against self-incriminating testimony, not the production of incriminating documents); Ars; 6/24/2020
- Senators Launch Full On Nuclear War Against Encryption: Bill Will Require Broken Encryption, Putting Everyone At Risk TD; 6/24/2020
- Law enforcement can crack iPhones just fine without a backdoor ApIn; 3/11/2020
- The EARN IT Act Is a Sneak Attack on Encryption Wired; 3/6/2020
- Trump Administration Targets Your 'Warrant-Proof' Encrypted Messages NPR; 2/21/2020
- Man who refused to decrypt hard drives is free after four years in jail Court holds that jail time to force decryption can't last more than 18 months; Ars; 2/12/2020
- Sources: CIA secretly owned Crypto AG, the leading supplier of encryption systems globally, and could read allies' and adversaries' communications for decades WaPo; 2/11/2020
- US officials claim Huawei has, for over a decade, been able to covertly access mobile-phone networks globally through back doors designed for law enforcement WSJ; 2/11/2020
- How Attorney General Barr's War On Encryption Will Harm Our Military TD; 2/7/2020
- Microsoft CEO says encryption backdoors are a 'terrible idea' Verge; 1/13/2020
- The CIA's Infamous, Unsolved Cryptographic Puzzle Gets a 'Final Clue' Kryptos sculpture; MB; 1/31/2020
- Suspect can’t be compelled to reveal “64-character” password, court rules Ars; 11/23/2019
- A technical critique on why even a well-intentioned effort to build a client-side scanning system for messaging will break key promises of end-to-end encryption EFF; 11/1/2019
- The broken record: Why Barr's call against end-to-end encryption is nuts Barr, DHS Secretary, UK, and Australia say end-to-end encryption will help child abusers; Ars; 10/4/2019
- Barr says the US needs encryption backdoors to prevent "going dark." Um, what? Ars; 8/4/2019
- Here We Go Again: GCHQ's Ghost User Proposal to Circumvent Encryption ACLU 4-part series; TB; 7/30/2019
- The Encryption Debate Is Over -- Dead At The Hands Of Facebook Forbes; 7/26/2019
- Barr says Americans should accept security risks of encryption backdoors Sen. Ron Wyden (D-OR) AG's remarks: "outrageous, wrongheaded and dangerous... If we give this attorney general and this president the unprecedented power to break encryption across the board burrow into the most intimate details of every American's life -- they will abuse those powers"; TC; 7/23/2019
- Sen. Wyden to NIST: recommendations for securely transmitting information not regular .zip; .pdf; 6/19/2019
- Did Australia Poke a Hole in Your Phone's Security? NYT; 1/22/2019
iOS
- How to Open 7z Files on iPhone & iPad OSXD; 3/10/2023
macOS
- Wikipedia: FileVault; Time Machine
- Apple: FileVault 2; Time Machine
- Take Control: FileVault
- Unarchiver extract only, including zip, 7-zip
- Keka macOS version of 7-zip; see Malware section on how to download & open 'untrusted' app
- Carbon Copy Cloner; how to create an encrypted, bootable volume using FileVault
- How protected is your Mac without FileVault enabled? MW; 9/28/2023
- Keka review: Compress, archive, and expand any Mac archive MW; 2/25/2022
- How to unlock your Mac with its Recovery Key and FileVault active MW; 8/6/2021
- How to encrypt files and folders on your Mac TR; 5/26/2021
- How to encrypt a Mac storage device MW; 4/29/2021
- How to recover data from a Mac with T2 or FileVault encryption and without a password
short answer: it may not be possible; MW; 11/19/2020 - Migrated your FileVault-enabled Mac? Clean up and regenerate your Recovery Key MW; 8/24/2020
- How FileVault and the T2 Security Chip work together in newer Macs MW; 8/21/2020
- How to check a Mac's free hard drive space MW; 3/26/2020
- Can't enable FileVault? An errant set of files may be blocking you
'A recovery key has been set by your company, school or institution' -- leftover from earlier installation? MW; 2/26/2020 - How to cope with a FileVault recovery key disappearing while you write it down MW; 1/7/2020
- [3] How to make FileVault work again when you're missing a 'secure token' MW; 6/11/2019
[2] Quantum; Future
- see {TCYOP-3: 43}
- Wikipedia: Quantum computing; Graphics Processing Unit (GPU)
- How Quantum Cryptology Works
- New iMessage PQ3 Encryption Protocol Protects Against Post-Quantum Attacks TB; 2/23/2024
- Quantum Computing’s Hard, Cold Reality Check hype is everywhere, skeptics say, and practical applications are still far away;
challenges in making fault-tolerant systems; qubits' slow operating speeds; IEEE; 12/22/2023 - U.S. and China race to shield secrets from quantum computers harvest data now, decrypt later after 'Q-day'; Reut; 12/14/2023
- The Race to Save Our Secrets From the Computers of the Future
Q-Day: the day when a quantum computer factors very large numbers,
hundreds of digits long, into their prime factors; NYT; 10/22/2023 - An illustrated guide to quantum computing, including qubits, algorithms, challenges,
government support, and “Q-day”, when a quantum computer cracks encryption FT; 5/3/2023 - A deep dive into the race to develop a quantum computer
which could help address climate change and food scarcity, break current encryption protocols, and more; NYkr; 12/19/2022 - NSA Says 'No Backdoor' for Spies in New US Encryption Scheme
NIST agency running competition for new encryption standards;
Quantum computing comes with risks for modern data protection; 5/13/2022 - Cryptocurrency faces a quantum computing problem
cracking public key cryptography; CNet; 11/12/2021 - Post-Quantum Cryptography Standardization NIST; 10/29/2021
- Hackers are stealing data today so quantum computers can crack it in a decade MIT; 11/3/2021
- NSA does not know when or even if a quantum computer of sufficient size and power
to exploit public key cryptography (a CRQC) will exist 9/4/2021 - Fact Sheet: Does quantum computing put our digital security at risk?
symmetric vs. asymmetric; # of qubits; Internet Society; 7/2021 - What Makes Quantum Computing So Hard to Explain?
To understand what quantum computers can do -- and what they can't -- avoid falling for overly simple explanations; 6/8/2021 - 2 Win Abel Prize for Work That Bridged Math and Computer Science
lattice-based schemes based on the LLL algorithm which seem to be uncrackable by quantum computers
vs. current prime number-based encryption systems; NYT; 3/17/2021 - IBM completes successful field trials on Fully Homomorphic Encryption
FHE allows computation of still-encrypted data, without sharing the secrets; Ars; 7/31/2020 - U.S. hatches plan to build a quantum Internet that might be unhackable
new network would sit alongside the existing Web, offering a more secure way to send and process information; WaPo; 7/23/2020 - Status Report on the Second Round of the NIST Post-Quantum Cryptography Standardization Process NIST; 7/2020
- China Reports Progress in Ultra-Secure Satellite Transmission
quantum physics used to send a 'secret key' for encrypting and decrypting messages between two stations 700 miles apart; NYT; 6/15/2020 - Q&A: The Pioneers of Web Cryptography on the Future of Authentication
Martin Hellman, Taher Elgamal, and Tom Jermoluk were instrumental in shaping how the Internet works.
Now they're looking at what’s next for web security; IEEE; 6/5/2020 - IBM releases toolkit aimed at keeping data encrypted even while in use fully homomorphic encryption; ZD; 6/5/2020
- New crypto-cracking record reached, with less help than usual from Moore’s Law
795-bit factoring and discrete logarithms achieved using more efficient algorithms; Ars; 12/3/2019 - Snake oil or genius? Crown Sterling tells its side of Black Hat controversy; Ars; 8/29/2019
- Encryption technology: 11 potential next big things TNW; 5/3/2019
- Fear the Man in the Middle (MitM)? This company wants to sell quantum key distribution Ars; 4/28/2019
- [3] Searchable encryption and the ever-expanding leakage function 2/11/2019
- Cryptography after the Aliens Land Schneier; 10/2018
Windows
- Tested: Windows 11 Pro's On-By-Default Encryption Slows SSDs Up to 45% 10/19/2023
- Windows Is Finally Getting Support for RAR and 7z Archives Windows 11; LH; 5/26/2023
- Microsoft is scanning the inside of password-protected zip files for malware
Why You Should Never Use the Native .Zip Crypto in Windows -- use other tools; Ars; 5/15/2023 - 5 great security tools built right into Windows
Windows Defender: manual scan;
Parental controls;
System restore point;
Memory Integrity;
Dynamic Lock; PC; 4/22/2021 - How to Hide Important Files on Your Windows PC difficult to 'hide'; safest to encrypt (and not rely on device password); LH; 10/29/2020
- [2] WinRAR patches 19-year-old security vulnerability that put millions at risk ACE format; Verge; 2/21/2019
Safer Internet: Offline: Erasing Your Device
Safer Internet: Offline: Erasing Your Device
Summary | Apps | Device | Files | Redacting |
References: General | Android | iOS | macOS | Photos |
Recycling/Reselling | Redacting | Windows
Summary
- "Having been erased,...
- Secure erasing of files is a non-issue for encrypted hard drives, e.g., Mac: FileVault; Win: BitLocker
- [2] Erasing apps, settings and data to free up space on your device
- [2] Securely Erasing Device before donating or discarding computer, phone, hard drive, printer or other device
- [3] Securely erasing files on a non-encrypted hard drive
- [3] Redacting (securely hiding/removing) content and metadata from documents and photos
- References
[2] Erasing Apps -- and associated settings, and maybe data
- Removing an unused app can free up storage, and reduce software update nags
- To find out how much storage is used on your device: (esp. for apps, movies, videos, podcasts, music, photos, iOS backups)
- iOS10:
Settings > General > Storage&Cloud Usage > Storage > Manage Storage - iOS:
Settings > General > iPad/iPhone Storage: Offload Unused Apps; iCloud Photo Library; individual apps - iOS:
Settings > iTunes & App Store: Offload Unused Apps - macOS:
[apple] > About This Mac > Storage > Manage - To remove not only an app, but also its settings, storage caches, etc.:
- iOS: press down on app icon to enter move / delete ('jiggly') mode
- tap "x" in upper left corner
- popup: "Deleting (app) will also delete all of its data"
- (press Home button to exit 'jiggly' mode)
- To immediately delete related iCloud data:
- iOS10:
Settings > iCloud > Manage Storage > (device) > disable old app - iOS:
Settings > (your acct) iCloud > Manage Storage > (app) > Delete Documents & Data - macOS: just dragging an app (from Applications folder) to Trash does not remove extra preference/library files
- Use app's uninstaller (if one is provided) or an app removal utility, e.g., App Cleaner
- [2] macOS: 3rd party utilities can find duplicate and large files, e.g., Disk Cleanup Pro (free; in the Mac App Store)
"Disk Cleanup Pro automatically cleans up the big offenders, Caches and Logs, plus it allows you to scan for duplicate files and large files. You can set the threshold for file size (e.g. bigger than 50 MB) in preferences, and can set separate thresholds for different types of files (Movies, Photos, Text, etc.). It tells you broadly what type of file it is dealing with (Photos, Music, Documents, etc.); fileinfo.com can help you identify the kind of file for a file extension you don't recognize." ~Peter DeGroot, AshMUG - [3] macOS:
(select files/folders) > File (ctrl-click) > Compress-- to reduce size of files you want to keep, but access infrequently; rename .zip if desired; delete originals when done - [3] macOS: Monolingual removes unused languages (and processor architectures) from System/Apps , e.g., just keep English yields ~2Gb
- [3] macOS: (HD/SSD) : "Previous System" folder (if present: ~1-2Gb) can be deleted, but it can be very difficult/tricky to actually Empty Trash
[2] Securely Erasing Device / Disk
- Securely erase drive before donating, discarding, recycling, selling or transferring your device; to be nice, re-install OS
- This assumes that you've already backed up anything you care about, and migrated files/settings to any new device.
- iOS:
Settings > General > Reset > Erase All Content and Settings - Trigger auto-erase if lost or stolen?
- iOS:
Settings > Passcode > (passcode) > Erase Data-- after 10 failed passcode attempts - iOS:
Settings > (your acct) > iCloud > (device) > Find My iPhone/iPad-- allows you to erase remotely - [3] macOS: erase disk and install OS
- Boot from Recovery Partition (option-R during Restart); or your bootable clone; for older macOS, boot from DVD or USB
Utilities: Disk Utility > (select drive) > Erase-- generally use Format: Mac OS Extended (Journaled) (for now, don't use High Sierra's APFS); for older macOS, and non-SSD, use option to Erase Free Space: 3 (or more times), if availableUtilities: Reinstall macOS/OS X
[3] Securely Erasing Files
- Even if you empty Trash / Recycle Bin, various utilities might be able to recover file content -- unless it's encrypted.
- macOS: (≥ 10.10) use FileVault: erased file sectors are still encrypted -- thus unreadable; see Encryption section
- macOS (< 10.10):
Finder > Secure Empty Trash
[3] Redacting Files
- Some source files (e.g., .doc, .pdf, .jpg) can retain layers / versions of info, i.e., metadata, or track changes;
it might be recoverable via copy/paste or tools; just deleting it or overlaying an annotation may not be enough! - So, omit sensitive info from files in the first place: content as well as metadata such as Author, Organization
- or, save edited document or selected screen area as an image
- or, copy/paste selected (non-sensitive) info into a simpler format, i.e., one that removes any hidden info -- or use redaction tools
- Remove photo metadata; e.g., phone location via iOS: Photo Investigator
- Redact a .pdf or source document to remove sensitive info -- using proper tools, i.e., Adobe Acrobat Pro; otherwise, simple annotations / changes can be selected, copied, revealed
References
- sections: Refs: Android; iOS; macOS; Photos; Recycling; Redacting; Windows
- topics: catalogs, junk mail, NSA, printers, repurposing
- How to Organize Desktop Apps creating a clean workspace; NYT; 3/2/2023
- Digital Clutter Can Be Overwhelming. Here's How to Clean Up. NYT; 2/24/2023
- How To Delete the Data Your Smartwatch or Fitness Tracker Has on You Giz; 8/15/2022
- You can take it with you: How to destroy the data you leave behind MW; 8/15/2022
- Why You Should Do a Factory Reset on All Your Older Tech LH; 5/9/2022
- Steps to Simple Online Security: 5: Track or wipe a lost device;
Securely sell or donate old electronics NYT; 4/22/2022 - How to Securely Wipe Your Computer, Phone, or Tablet NYT; 1/31/2022
- How to remove your iCloud account and Apple ID from a transferred computer MW; 1/27/2020
- Remember to Delete and Unlink Your Accounts Before Deleting an App LH; 1/6/2020
- Don't Just Uninstall Old Apps -- Delete Your Accounts As Well Giz; 7/10/2019
- How to Declutter and Speed Up Your Phone And, iOS; Delete apps you don't use; Free up storage; NYT; 4/18/2019
- How to Declutter and Organize Your Personal Tech in a Few Simple Steps NYT; 1/23/2019
Android
- Google: Back up or restore data on your Android device; Reset your Android device to factory settings
- How to wipe your Android phone before selling it or trading it in Verge; 3/24/2022
- 10 quick ways to clear space on an overstuffed Android device PC; 6/29/2020
iOS
- Apple: How to erase your iOS device and then set it up as a new device or restore it from backups
- Apple: Back up iPhone; Erase iPhone
- Run out of space? Free up your iPhone storage with these tips MW; 9/11/2023
- iPhone Other storage: What is it and how do you delete it? system files, caches (streaming music/video; Safari; Messages), Siri voices, logs, updates; MW; 8/9/2023
- How to reset a locked iPhone without needing a Mac
easier in iOS/iPadOS 15.2; MW; 3/20/2023 - How to free up iPhone storage without deleting your apps or photographs ApIn; 5/18/2022
- How iOS 15 Makes It Much Easier to Back Up and Wipe Your iPhone Before Selling It LH; 11/17/2021
- How to erase your iPhone, iPad, or Mac remotely after a theft MW; 7/26/2021
- Accidentally Deleted Photos Off Your iPhone? Here's How to Get Them Back MF; 2/25/2021
- iPhone Other storage: What is it and how do you clear it? MW; 12/18/2020
- How to recover deleted text messages on iPhone it might be tricky; MW; 12/8/2020
- What to do before you sell, give away, or trade in your iPhone, iPad, or iPod touch Apple; 10/18/2019
- After 10 failed logins, Giuliani had Apple Store wipe his iPhone
The 2017 incident occurred shortly after Trump named Rudy cybersecurity advisor; Ars; 10/31/2019 - How to delete iOS apps 1. Tap and wiggle; 2. Settings > General > Storage & iCloud Usage > Manage Storage;
3. iTunes > Apps > Delete; 4. iTunes (during update) > Delete from Library; MW; 7/30/2019 - iOS 13 will remind you to cancel your subscription when you delete an app Ars; 6/18/2019
macOS
- Apple: Disk Utility Help
- Follow These Steps to Clear Space on Your Mac
1: Empty the Trash;
2: Restart, Possibly in Safe Mode;
3: Scan for Large Files and Huge Folders;
4: Delete 32-bit Apps and Duplicate Apps;
5: Delete macOS Installers;
6: Delete old iPhone and iPad Backups;
7: Remove the GarageBand Sound Library;
8: Remove Opened Mail Attachments;
9: Remove Unwanted Podcasts;
10: Remove Watched TV Shows and Movies;
11: Remove Downloaded Copies of Apple Music and iTunes Match Songs;
12: Remove Local Copies of Apple Books;
13: Select Optimize Mac Storage and Remove Local iCloud Drive Files;
14: Delete iPhoto Libraries;
15: Delete Time Machine Snapshots;
16: Delete Unwanted Contents of the Downloads Folder;
17: Delete Photo, Song, and File Duplicates;
18: Delete Already-Imported Folders of Photos;
19: Use DevCleaner to Delete Xcode Caches;
20: Compress Large Files; 21: Get External Storage; TB; 3/18/2024 - How to recover deleted files from emptied trash on a Mac
1: Recover emptied Trash on a Mac with data recovery software;
2: Recover accidentally emptied Trash on a Mac from Time Machine backup;
3: Recover deleted files after emptying Trash on a Mac with iCloud backup;
4: Recover files from emptied Trash on a Mac using Terminal; MW; 2/22/2024 - How to use macOS Erase Assistant to reset your Mac ApIn; 12/24/2023
- How to Wipe Your Mac Without Reinstalling the OS LH; 12/1/2023
- How to delete 'Other' storage on a Mac pre-Monterey; MW; 11/12/2023
- How to clear disk space on a Mac MW; 9/26/2023
- How to delete system data on a Mac Monterey and later; MW; 7/26/2023
- Boost Mac performance with one of these top cleaner apps MW; 3/9/2023
- Easy tips for cleaning up your Mac MW; 3/2/2023
- Don't wait for spring to start cleaning up your Mac device MW; 12/11/2022
- How to clear disk space on a Mac MW; 10/18/2022
- How to Securely Erase a Mac's SSD or Hard Drive TB; 8/15/2022
- How to delete System storage on Mac MW; 5/18/2022
- How to find & delete duplicate files on Mac MW; 5/16/2022
- How to erase a Mac's drive in macOS Catalina, Big Sur, or Monterey
both data and system volumes; MW; 11/25/2021 - [2] How to use Terminal to securely erase free space on a Mac’s drive MW; 9/19/2021
- CCleaner review: A flexible Mac utility for clearing clutter MW; 8/12/2021
- How to erase your iPhone, iPad, or Mac remotely after a theft MW; 7/26/2021
- Save Mac storage space by cleaning out abandoned log files MW; 4/9/2021
- How to erase and prepare a Mac for gifting, recycling, or selling ApIn; 12/27/2020
- How to erase an encrypted Mac volume if you don't need its contents you don't need a password if you're just trying to erase a drive; MW; 11/27/2020
- What Are Relocated Items in macOS Catalina & Can I Delete Them? OSXD; 6/15/2020
- Apple’s Activation Lock Will Make It Very Difficult to Refurbish Macs iFix; 12/2/2019
- How to Delete Microsoft AutoUpdate from Mac OSXD; 7/20/2019
- How to Delete Specific Files from Trash on Mac Without Emptying Entire Trash
Trash: ctrl-click > Delete Immediately; OSXD; 7/18/2019 - Can't erase your Mac's startup disk? Try Internet Recovery as a last resort MW; 6/25/2019
- What to do if your Mac's hard drive starts unmounting itself unexpectedly MW; 5/8/2019
- How to delete a file that macOS says is in use MW; 2/13/2019
Photos
- How to remove metadata from your photos on iOS TNW; 6/27/2019
- How to recover deleted photos from an iPhone or iPad MW; 2/1/2019
Recycling / Reselling
- HowStuffWorks: 10 Things to Do Before You Wipe Your Computer;
How to Donate Your Computer to Charity - Manufacturer or store may recycle, e.g., Apple iPhone, iPad, Mac, or PC; BestBuy (OR)
- RV Habitat for Humanity: ReStore -- recycling electronics: 10-4 daily
- Oregon E-Cycles environmentally responsible recycling program for computers, monitors and TVs
- E-cycling Central (OR)
- Green Guide to Recycling Appliances and Electronics
- Catalog Choice eliminate unwanted catalogs, phone books, credit card offers
- Trade-in programs: Amazon; Best Buy; Gazelle
- How to sell your old tech gear PC; 8/10/2023
- How to trade in your MacBook, macOS desktop, iPhone, or iPad Verge; 6/29/2023
- This Hidden Amazon Page Makes It Easier to Fix, Recycle, or Trade in Your Old Tech Gadgets Second Chance; MF; 2/16/2023
- How to (Ethically) Get Rid of Your Unwanted Stuff Wired; 1/31/2022
- The best online marketplaces for selling your used devices PC; 8/10/2021
- Thinking about selling your Echo Dot—or any IoT device? Read this first
deleting data is hard; factory reset; encryption? Ars; 7/2/2021 - How to Repurpose Your Old Gadgets Wired; 10/18/2020
- Three Worthwhile Buy-Back Programs for iPhones TB; 3/3/2020
- How To Buy Hardware That's Likely to Last TB; 7/2/2019
- How to Get Your MacBook Ready to Sell
Turn off FileVault;
Turn off Find My Mac;
Deauthorize your computer;
Unlink other accounts;
Sync your Messages to iCloud;
Log out of iCloud; Back up your stuff;
Erase all your stuff;
Reinstall macOS; LH; 6/10/2019 - How to Sell or Recycle Your Old Electronics LH; 5/2/2019
- It's Scary How Much Personal Data People Leave on Used Laptops and Phones, Researcher Finds Giz; 3/19/2019
Redacting
- Wikipedia: Data erasure
- Sanitization: removing sensitive information from a document; redaction: blacking out or deletion of text to allow selective disclosure
- How to easily redact text in a PDF on your Mac MW; 12/5/2023
- Redacted Documents Are Not as Secure as You Think Wired; 11/25/2022
- NYT Crossword Thu, 9/23/21
67A: “Redacts, as sensitive information (suggested by three of this puzzle’s answers)"
BLACKSOUT (certain black squares hide SSN, DOB, PIN) - How to easily redact text in a PDF on your Mac
Preview (Big Sur), Acrobat, PDFPen and PDFPen Pro;
MW; 5/26/2021 - Metadata Left in Security Agency PDFs 3/12/2021
- We Cracked the Redactions in the Ghislaine Maxwell Deposition Here’s what it says about Bill Clinton, Alan Dershowitz, and Prince Andrew. Plus: Help us decode more names; Slate; 10/22/2020
- Frontier bungles redaction of network audit that it doesn’t want you to see Blacked-out text is readable, revealing 952,000 potential network problems; Ars; 4/9/2020
- The best PDF apps to use for editing, redacting, and for OCR in macOS Mojave ApIn; 2/25/2019
- How a Simple Copy/Paste Revealed Explosive New Detail in Manafort's Case Redacted court documents keep getting unredacted because of simple, relatively easy to avoid errors. Here's how to better redact PDFs; MB; 1/10/2019
Windows
- How to securely erase your hard drive or SSD
plus thumb drives; PC; 6/14/2021 - How to get rid of old files and clean up your PC with Windows' Storage settings PC; 7/20/2020
- Microsoft's new Windows File Recovery tool lets you retrieve deleted documents Verge; 6/29/2020
- How to Quickly Free Up Space on Your Windows PC LH; 5/7/2019
- Don't erase, overwrite: How to avoid being that person who resells a drive with data on it PC; 4/25/2019
Safer Internet: Keep Your Internet Connection Private
Safer Internet: Keep Your Internet Connection Private
Summary | Preview | References
Summary
- "Stay the patient course...
- "Give a person a fish and you feed them for a day...
- [1] Use WPA2 for Wi-Fi networks; improve DNS lookups/privacy
- [1] Use a VPN when you're on any open or unfamiliar network
- [1] Use HTTPS: for web browsing (and SSL/TLS for email) when available
- [1] Avoid malware
- [2] Turn off unnecessary services, e.g., location
- [2] Turn on your computer's firewall
Preview: privacy / security / anonymity via encryption / indirection
- Recall the letter / post office analogy in Privacy, Security, Anonymity section?
- We're mostly concerned about content (postcard vs. letter) -- encryption
- The address (actual vs. PO Box) could be important too -- anonymity via indirection
- The following figures show the effect of encryption from various techniques
- What's not shown: which information might be added, e.g., ads, tracking, malware
- which information might be saved on client or servers, e.g., history, logs, caches
- how secure your data is on their server, e.g., passwords, medical records, credit card, social security no.
- how someone else accesses information you've 'published', e.g., email recipient, blog reader
 None: {Figure 1. TCYOP-4: 56; TCYOP-3: 44} -- at right
None: {Figure 1. TCYOP-4: 56; TCYOP-3: 44} -- at right- [1] Wi-Fi (WPA2) [device-to-router]:
{Figure 3. TCYOP-4: 58; TCYOP-3: 46} - [1] HTTPS: for browser, SSL/TLS for email [device-to-final specific site]
{Figure 6. TCYOP-4: 67; TCYOP-3: 55} - [1-2] VPN [device-to-intermediate server; some address]
{Figure 4. TCYOP-4: 60; TCYOP-3: 48} - [3] Tor [device-to-intermediate servers; most of address]
{Figure 14. TCYOP-4: 104; TCYOP-3: 87}
References
- {TCYOP-4: 51-77; TCYOP-3: 39-63; Wi-Fi connections, Cellular connections, DNS disruptions, ISP monitoring, Router monitoring, Malware, Location discovery, Quantum Computing and Encryption, Prevent Snooping}
- Crosswords: Connection; Malware
Safer Internet: Connection: Encrypt Wi-Fi
Safer Internet: Connection: Encrypt Wi-Fi
Quotes | Summary | Connecting | Encrypting | Admin | Remote Admin |
DNS | Conn. Problems | Backup | Firmware | SIM Pin |
References: General | Android | Cellular | DNS, IP | iOS |
ISP | macOS | Modem, Router | Wi-Fi | Windows
Quotes
- I used to like my neighbors,...
- Today my Wi-Fi suddenly stopped working...
- Interesting Wi-Fi network names:...
- What not to name your personal hotspot on an airplane to avoid arrest:...
- "A teenager at a funeral...
- "People think that data is in the cloud, but...
- "Stay the patient course
Of little worth is your ire
The network is down." ~Haiku error messages
Summary
- [1] Don't connect to unknown public networks, such as "Free WiFi", or hotspots with no/weak/public passwords -- to reduce data interception, ISP injections (ads), and MITM (man-in-the-middle) attacks. Read privacy policy. Some providers may track location across multiple Wi-Fi networks.
- [1] Connect to Wi-Fi networks securely
- [1] Set a strong memorable/typable password for your Wi-Fi network with WPA2 (encryption level) -- or WPA3 if available
- [1] Router Maintenance: Set an Admin password (long random); Disable Remote Admin & UPnP
- [1] Change DNS servers
- [2] Troubleshoot common connection problems
- [2] Router Maintenance: Backup settings; Update firmware
- [3] Set phone/tablet SIM PIN
- References
[1] Connecting to a Wi-Fi Network
- Connect to known networks using WPA2 -- unless you're already encrypting traffic using a Virtual Private Network (VPN), and/or HTTPS: for all web sites and TLS/SSL for email.
- This assumes that your device, router and destination web server have the latest security updates installed;
there are exceptions depending on your risk tolerance. - WEP (Wired Equivalency Protocol) is old and easily cracked -- barely better than no encryption
- WPS (Wi-Fi Protected Setup) lets you use WPA without having to enter a long password; however, you may be vulnerable if you have not changed the pre-shared WPA key from the factory default setting, and PIN feature is enabled -- one reason why WPS is less secure than WPA2
 Network figures
Network figures- with no encryption (Wi-Fi, SSL/HTTPS): {Figure 1. TCYOP-4: 56; TCYOP-3: 44}
- with Wi-Fi encryption: {Figure 3. TCYOP-4: 58; TCYOP-3: 46}
- Connect intentionally -- not automatically -- to open (insecure) Wi-Fi networks.
- By default, macOS & iOS connect automatically only to "known" networks, i.e., open or password-protected networks that you've connected to before
- Automatic connections might occur in older systems or on other platforms?
- For a new, unknown network, you can be prompted to join it, or to select it manually. it won't connect automatically
- macOS:
System Preferences > Network > Wi-Fi > Ask to Join New Networks : "on" (prompt you when a new network is avail) or "off" (you'll select manually) - iOS:
Settings > Wi-Fi > Ask to Join Networks(same as macOS) - iOS:
Settings > Wi-Fi > (select network > 'i' > Auto-Join-- customize for individual networks  iOS: If a friend's iOS 11 device tries to connect to your Wi-Fi network, you’ll receive a prompt that lets you send over the password by tapping Send Password
iOS: If a friend's iOS 11 device tries to connect to your Wi-Fi network, you’ll receive a prompt that lets you send over the password by tapping Send Password- To remove a network from the list of automatically connecting "known" networks (that you've connected to previously)
- macOS:
System Preferences > Network > Wi-Fi > Advanced > W-Fi > (select network) > "-" - iOS:
Settings > Wi-Fi > "i" (for network) > Forget This Network  Check encryption level from client: none?, WEP?, WPA? WPA2?
Check encryption level from client: none?, WEP?, WPA? WPA2?- macOS:
menubar > [option-click] Wi-Fi icon: current network stats displayed; other networks: hover to display stats - iOS:
Settings > Wi-Fiinsecure connection warning (right) - You could also use a utility, e.g., NetSpot (Mac, Win) that displays encryption level for nearby networks -- and signal/noise, etc.
- Android, macOS, Windows: How to Check WiFi Security Encryption Type 1/24/2014
[1] Encrypting your Wi-Fi Network
- Encrypt Wi-Fi networks you control WPA2 (Wi-Fi Protected Access) -- not WPA or WPA2/WPA combo -- certainly not WEP; eventually WPA3 -- with a strong password: memorable / typable occasionally by you & your guests
- Weak/no password could create problems if neighbors use your connection (& IP address)
for illicit activities or excessive downloads -- not an issue (e.g., hackers in your driveway)
if your WiFi range does not extend outside, or for hard-wired devices (via Ethernet cable) - Check your router's manual (download .pdf) to locate settings and router IP address, e.g.,
http://192.168.1.1 - Connect via web browser to router's local web server, or use manufacturer's configuration app
 Use WPA2/AES rather than TKIP encryption (note: old Netgear figure shows incorrect combo setting)
Use WPA2/AES rather than TKIP encryption (note: old Netgear figure shows incorrect combo setting)- Apple Airport config {Figure 2. TCYOP-4: 47; TCYOP-3: 45}
- Netgear:
Wireless Settings > Security Options > WPA2 - TP-Link:
Wireless (freq) > Wireless Security > WPA2[screenshot] - [2] To make your network freely available to others, e.g., during a disaster, set up a separate Guest network (with no password), rather than disabling security on your regular network, if possible [screenshot]
- If you set up your smartphone to share its data connection via Wi-Fi (aka 'Personal Hotspot' or 'tethering'), be sure to set a password for security and to avoid others using your data allocation.
- iOS:
Settings > Personal Hotspot (if Cellular Data on) > On (Wi-Fi,Bluetooth,USB); Wi-Fi Password: xxx
[1] Router: Admin Password
- Set a strong admin password -- this protects the router itself -- different from the Wi-Fi password you use or supply to guests; long, random -- save in password manager!
- If password is required to be short (older routers?), also change admin user name
- Netgear:
Maintenance > Set Password - TP-Link:
System Tools > Password[screenshot]
 [1] Router: Disable Remote Admin and UPnP
[1] Router: Disable Remote Admin and UPnP
- Turn off ability to log in and administer your router remotely -- hopefully, it was already off by default
- Netgear:
Advanced > Remote Management - TP-Link:
Security > Remote Management[screenshot] - [3] Re-enable if you have need / expertise
- Disable UPnP (Universal Plug and Play) -- hopefully, it was already off by default
- TP-Link:
Forwarding > UPnP(or maybe Advanced > NAT Forwarding?) - Check if disabled: F-Secure's Router Checker or ShieldsUp!! Instant UPnP Exposure Test
 [1] Router/Device DNS
[1] Router/Device DNS
- "What does a network administrator say after returning from work?...
- DNS (Domain Name System) is a directory service that returns an IP address corresponding to a domain name, e.g., www.google.com (analogous to telephone white pages)
- Change DNS name servers; e.g., Netgear w/ OpenDNS (right)
- suggested servers (below) usually faster than your ISP's DNS
- reliability/speed: these servers generally better than what your ISP provides
- privacy: reduce ISP logging of sites visited
- security: avoid ISP redirecting non-existent addresses to promotional ad sites
- Several free DNS services, and their primary and secondary name servers: {TCYOP-4: 69}
- CloudFlare:
1.1.1.1; 1.0.0.1 - Cloudflare: malware blocking
1.1.1.2; 1.0.0.2; + adult content blocking:1.1.1.3; 1.0.0.3; - Google Public DNS:
8.8.8.8; 8.8.4.4 - OpenDNS (Cisco):
208.67.222.222; 208.67.220.220 - Quad9:
9.9.9.9; 149.112.112.112 - Recursive DNS:
156.154.70.1; 156.154.71.1 - If set centrally in your router, all your connected devices will use the DNS servers
- Netgear:
Basic Settings > DNS Address - TP-Link:
DHCP > DHCP Settings[screenshot];Network > WAN[screenshot] - If you have no router (or it's someone else's), you can change DNS directly on individual devices via "Network > DNS settings"
- iOS:
Settings > WiFi > (network: "i") > Configure DNS - For iOS (and Android) devices, an app can manage DNS more simply, esp. for cellular data. e.g., "1.1.1.1 Faster Internet" (Cloudflare) sets up a VPN connection for DNS lookups.
- macOS:
System Preferences > Network > Advanced > DNS > DNS Servers - macOS: If possible, create separate network profile, e.g., Home, Travel?
- You can also hide -- and encrypt -- DNS lookups by using a VPN (next section)
[2] Wi-Fi Connection Problems?
- If your Wi-Fi connection seems 'stuck', first try toggling Wi-Fi connection off/on; check that expected router reconnects
- macOS:
(Wi-Fi icon) > Turn Wi-Fi Off/On - iOS:
Settings > Wi-Fi: off/on-- note: disabling via iOS11 Control Center does not completely turn off! - If just one app not working, e.g., browser ok, but not email, close/reopen app
- [2] Reset/get new device IP address
- iOS:
Settings > Wi-Fi > (current network "i" icon) > Renew Lease - macOS:
System Preferences > Network > Advanced > TCP/IP > Renew DHCP Lease - Basic troubleshooting (step 1): Disconnect/Reconnect to router (Mac: option-click Wi-Fi icon); Turn Wi-Fi Off/On; reboot computer/device
- Basic troubleshooting (step 2): Turn Off cable/DSL modem & Router; wait ~60 seconds; Modem On; wait ~30-60 seconds (for internet connection to be established); Router On; wait until Wi-Fi connection reappears on device
[2] Router: Backup Settings
- If you have made numerous changes, back up router settings to ease restoration after any 'factory reset'.
- Netgear:
Maintenance > Backup Settings - TP-Link:
System Tools > Backup & Restore
[2] Router: Update Firmware
- Check your router manufacturer's web site periodically (or automatically upon login) for firmware (i.e., low-level software) upgrades -- and install them
- Beyond having a good admin password, and disabling remote admin, this should further minimize security problems and attempts to weaken or hijack router, e.g., WPA2 protocol vulnerability (KRACK: Key Reinstallation Attacks) 10/16/2017; VPNFilter 5/23/2018
- Netgear:
Maintenance > Router Upgrade - TP-Link:
System Tools > Firmware Upgrade[screenshot] - If you rent a router from your ISP, check with them about updates.
- [3] Firmware in a cable modem should be updated automatically by your ISP.
- Check current modem version by browsing (usually) to: http://192.168.100.1 to access diagnostic page;
check manufacturer site for recommended version; contact ISP if major discrepancy.
[3] Set Device SIM PIN
- On some devices, e.g., iPhone, iPad*, you can lock your SIM card so that cellular data can't be used without entering a PIN -- whenever you swap SIM cards or restart. To enable, disable or change your SIM PIN:
- iPhone:
Settings > Phone > SIM PIN - iPad:
Settings > Cellular Data > SIM PIN(*Wi-Fi + Cellular models)
References
- {TCYOP-4: 55-77; {TCYOP-3: 44-47}
- sections: Refs: Android; Cellular; DNS, IP; iOS; ISP; macOS; Modem, Router; Wi-Fi; Windows
- topics: DNS hijacking, domains, IPv4 address crisis, KRACK, radiation, speed tests
- "If a packet hits a pocket on a socket on a port,
And the bus is interrupted as a very last resort... - "Oh, the network outside is frightful,
But on campus, it's so delightful... - Wikipedia: router; Network Address Translation (NAT); Internet of Things (IoT)
- Wikipedia: NAT: telephone number extension analogy
- HowStuffWorks: How Routers Work; Router Quiz; How Network Address Translation Works
- HowStuffWorks: How Home Networking Works; Home Networking Quiz
- Home Networking (Wydea): intro video: 0:44; modem; router; longer video 3:16; cables; Wi-Fi range; WPA; switch vs. router; powerline; sharing
- Wikipedia: IP (Internet Protocol) address; IPv4 (IP version 4): ~4.3 billion (232); adopted: 1981; currently, running out of addresses
- Wikipedia: IPv6 2128 (~3.4x1038) addresses; spec. published 1998; this amounts to approximately 5x1028 addresses for each of the 6.8 billion people alive in 2010. While these numbers are impressive, it was not the intent of the designers of the IPv6 address space to assure geographical saturation with usable addresses. Rather, the longer addresses simplify allocation of addresses, enable efficient route aggregation, and implementation of special addressing features.; World IPv6 Launch
- HowStuffWorks: What is an IP address?
- Wikipedia: Subscriber Identity Module (SIM card)
- Steps to Simple Online Security: 10: Secure Your Wi-Fi NYT; 4/15/2022
- How to Turn Off Amazon Sidewalk
opt out Echo and Ring devices from internet-sharing mesh network; Wired; 6/8/2021 - Why Public Wi-Fi is a Lot Safer Than You Think due to the widespread deployment of HTTPS encryption on most popular websites, advice to avoid public Wi-Fi is mostly out of date and applicable to a lot fewer people than it once was -- assuming software up to date; domain lookups still visible; EFF; 1/29/2021
- Speed Up Your Internet by Limiting Bandwidth-Hungry Apps LH; 7/16/2019
- The Land Where the Internet Ends To find real solitude, you have to go out of range. But every year that's harder to do, as America's off-the-grid places disappear; Green Bank, WV; 6/21/2019
- Why Do Internet Speed Tests Report Different Results? LH; 5/17/2019
- The Top 10 Ways to Deal with a Slow Internet Connection
10. Check your speeds (and your internet plan);
9. Give your hardware the universal fix (turn off/on);
8. Know your hardware's limitations;
7. Fix your WiFi signal;
6. Turn off or limit bandwidth-hogging apps;
5. Try a new DNS server;
4. Call your internet provider;
3. Optimize your web for a slow connection;
2. Work smarter;
1. Don't worry about it; LH; 5/16/2019 - How the Internet Travels Across Oceans NYT; 3/10/2019
- Military Carrier Pigeons in the Era of Electronic Warfare transport data on microSD cards; 1/24/2019
Android
- See the Wi-Fi Passwords for Every Network You've Connected to With this Android App LH; 5/5/2019
- Researcher finds that a popular hotspot finder app for Android exposed the Wi-Fi network passwords for 2M+ networks including tens of thousands in the US; WiFi Finder; TC; 4/22/2019
- Scan for Competing Wifi Networks With This Free Android App LH; 3/7/2019
Cellular
- How Secure are Personal Hotspot Connections from iPhone? OSXD; 3/23/2024
- Guide to 5G: Here's everything you'll ever want to know about the spectrum, millimeter-wave technology Wired; 12/31/2022
- What Is 5G, and Does It Actually Make a Difference? NYT; 8/11/2022
- How to Use Wi-Fi Calling on Your Smartphone
iPhone, Android; Wired; 11/18/2021 - 2G Connection Encryption Deliberately Weakened To Comply With Cryptowar Export Restrictions TD; 6/21/2021
- How to Set Up a 4G LTE Wi-Fi Network as an Alternative to Broadband Wired; 2/27/2021
- How 5G Could Replace Your Home Broadband Connection Giz; 2/11/2021
- How to turn your phone hotspot into a home broadband network read the fine print before you do so; MW; 11/23/2020
- Can My Phone's Hotspot Be My Only Internet Connection? data plan costs? LH; 5/22/2020
- How to share your iPhone’s mobile connection by tethering or hotspot MW; 4/10/2020
- Broadband engineers threatened due to 5G coronavirus conspiracies Guard; 4/3/2020
- Stop Your Phone From Using So Much Data Connect to Wi-Fi Whenever Possible; See Which Apps Are Using the Most Data; Tweak Your Apps; Settings; Get a Better Deal on Your Data; NYT; 3/5/2020
- How to disable Wi-Fi on an iPhone or iPad and always use cellular data MW; 3/2/2020
- What You Need to Know About 5G in 2020 NYT; 1/8/2020
- Worried about 5G and Cancer? Here’s Why Wireless Networks Pose No Health Risk TB; 12/6/2019
- 5G decoded: Here's how to tell real 5G from the marketing fluff 3 versions (& multiple marketing names): millimeter wave (mmWave; speed vs. distance); Low-band (better coverage than 4G); midband (in between); CNet; 11/21/2019
- New 5G flaws can track phone locations and spoof emergency alerts TC; 11/12/2019
- [3] How to see your true cellular signal strength with the iPhone Field Test app turn off WiFi, call: *3001#12345#*; MW; 3/4/2019
- [2] Ubiquitilink advance means every phone is now a satellite phone TC; 2/25/2019
- [2] New flaws in 4G, 5G allow attackers to intercept calls and track phone locations 1. Torpedo; 2. Piercer; 3. IMSI-Cracking; TC; 2/24/2019
DNS, IP Addresses
- Wikipedia: Domain Name System (DNS); OpenDNS; Google Public DNS
- HowStuffWorks: How Domain Name Servers Work; How Internet Infrastructure Works: Internet Protocol: Domain Name System
- Wikipedia: List of Internet top-level domains; generic top-level domains (gTLDs)
- Wikipedia: Internet Corporation for Assigned Names and Numbers (ICANN)
- HowStuffWorks: Who owns the Internet?; What are the standard top-level domain names and who controls them?
- HowStuffWorks: Where are all the Internet domain names registered and maintained?
- Wikipedia: DNS hijacking or DNS redirection is the practice of subverting the resolution of Domain Name System (DNS) queries
- Wikipedia: DNS spoofing or DNS cache poisoning; data is introduced into a Domain Name System (DNS) resolver's cache, causing the name server to return an incorrect IP address, diverting traffic to the attacker's computer (or any other computer).
- Wikipedia: Pharming cyber attack intended to redirect a website's traffic to another, fake site
- How to fix your network when you see 'Another device is using your IP address' on a Mac MW; 9/10/2022
- What is BGP, and what role did it play in Facebook’s massive outage
DNS tells you where you're going, and BGP (Border Gate Protocol)
tells you how to get there ~Cloudflare; Verge; 10/5/2021 - How to Use Private Relay in Safari to Hide Your IP address on iPhone & iPad OSXD; 10/4/2021
- Apple announces iCloud+ with privacy-focused features
Private Relay: combines DNS-over-HTTPS with proxy servers);
Hide my email: generate random email addresses;
TC; 6/7/2021 - The NSA warns enterprises to beware of third-party DNS resolvers possible issues: false sense of security, bypassing of DNS monitoring and protections, concerns for internal network configurations and information, and exploitation of upstream DNS traffic; Ars; 1/15/2021
- Cloudflare and Apple design a new privacy-friendly internet protocol Oblivious DNS-over-HTTPS (ODoH); only the proxy knows the identity of the internet user and that the DNS resolver only knows the website being requested; TC; 12/8/2020
- Cloudflare's 23-Minute Outage Today Also Took Down Major Web Sites bad router rather than DoS attack; TC; 7/17/2020
- [2] Microsoft urges patching severe-impact, wormable server vulnerability 17-year-old DNS flaw requires no user interaction; Ars; 7/15/2020
- Apple says iOS 14 and macOS 11 will support the DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) protocols ZD; 6/25/2020
- It's Long Past Time To Encrypt The Entire DNS TD; 6/22/2020
- Block Malware With Cloudflare's New DNS Options LH; 4/2/2020
- How to Enable DNS Over HTTPS in Your Web Browser Firefox, Chrome, Edge, Brave (not Safari); LH; 2/25/2020
- Firefox turns encrypted DNS on by default to thwart snooping ISPs Ars; 2/25/2020
- The Digital Colonialism Behind .tv and .ly Wired; 2/7/2020
- Mozilla to add second DNS-over-HTTPS (DoH) provider in Firefox NextDNS joins Cloudflare as second built-in Firefox DoH provider; ZD; 12/17/2019
- Here's why the internet will always have enough space for all our devices IP addresses; TNW; 11/17/2019
- DNS-over-HTTPS will eventually roll out in all major browsers, despite ISP opposition DoH support is already present in all major browsers. Users just have to enable it and configure it; instructions: Brave, Chrome, Edge, Firefox, Opera, Safari(?), Vivaldi; ZD; 11/8/2019
- DNS over HTTPS can increase user privacy by obfuscating web traffic, but it's no silver bullet as DNS resolving services will still see unencrypted requests Wired; 10/9/2019
- Firefox will encrypt web domain name requests by default Eng; 9/7/2019
- The Infrastructure Mess Causing Countless Internet Outages Border Gateway Protocol; Wired; 6/28/2019
- How to Find Your Local and External IP Address And, iOS, Mac, Win; LH; 5/13/2019
- Ongoing DNS hijackings target unpatched consumer routers Ars; 4/4/2019
- Cloudflare expands its government warrant canaries when the government comes for your data, tech companies can’t always tell you. But thanks to a legal loophole, companies can say if they haven't had a visit yet (and then remove it if they have); TC; 2/25/2019
- [3] Inside the DNSpionage hacks that hijack domains at an unprecedented scale Ars; 2/18/2019
- [2] DHS issues security alert about recent DNS hijacking attacks from Iran; ZD; 1/22/2019
iOS
- How to Share a Wi-Fi Password with QR Code from iPhone or iPad OSXD; 7/8/2021
- Bug in iOS can break iPhone Wi-Fi using rogue hotspot name
don't try %p%s%s%s%s%n; ApIn; 6/19/2021 - How to Enable & Disable Private Wi-Fi Address on iPhone & iPad to Increase Privacy OSXD; 2/16/2021
- How to use the Wi-Fi button in the iOS Control Center to deal with weak networks 'soft off'; MW; 11/5/2020
- How to Switch Wi-Fi Networks from Control Center on iPhone & iPad iOS/iPadOS 13; OSXD; 2/4/2020
- What the new iOS 13 Wi-Fi message means about nearby available networks 'popular' networks; MW; 12/4/2019
- That's right: You can't turn off Personal Hotspot in iOS 13 and iPadOS 13 MW; 10/11/2019
- How to Connect to Wi-Fi Networks Faster in iOS 13 4 ways; TB; 10/7/2019
- How to Check Current Wi-Fi Networks Signal Strength in iOS OSXD; 9/6/2019
- How to share your Wi-Fi password as a QR code on iOS TNW; 6/21/2019
- iOS 12.1.3 No Service or Cellular Data Problems on iPhone? Try These Fixes OSXD; 1/26/2019
- How iOS's Wi-Fi Assist works and how it can affect your cellular bill a bad Wi-Fi connection can still cause your iPhone (or iPad) to use cellular data; MW; 1/3/2019
ISP; Satellite
- Best Satellite Internet Providers for 2022
HughesNet, Viasat, Starlink; CNet; 6/2/2023 - Best Internet Speed Tests CNet; 5/31/2023
- Consider the Connection Type When Comparing Internet Providers
fiber; cable; 5G; fixed wireless; DSL; satellite; CNet; 5/6/2023 - Comparing the available home internet connection types CNet; 4/4/2023
- What's the Difference Between SpaceX's Starlink and OneWeb? Giz; 3/31/2023
- Starlink RV Review: The Dawn of Space Internet to Go Verge; 6/25/2022
- Does Bad Weather Really Affect Your Internet? MF; 10/3/2021
- Jared Mauch didn’t have good broadband -- so he built his own fiber ISP "I had to start a telephone company to get [high-speed] Internet access."; Ars; 1/12/2021
- US Falls Out Of Top 10 Fastest Broadband Speeds and ranked 33rd in average mobile download speeds; TD; 6/15/2020
- New Cloudflare tool can tell you if your ISP has deployed BGP fixes Is BGP (Border Gateway Protocol) Safe Yet; Ars; 4/19/2020
- How to Easily Test Internet Connection Speed on Mac fast.com; OSXD; 4/19/2020
- How to test your home Internet speed PC; 3/31/2020
- How to stop Spectrum junk mail Verge; 2/29/2020
- Why big ISPs aren't happy about Google's plans for encrypted DNS DNS over HTTPS will make it harder for ISPs to monitor or modify DNS queries; Ars; 9/30/2019
- What Would It Take to Shut Down the Entire Internet? Giz; 9/30/2019
- Stop Renting Your Cable Modem: Buy One Instead TB; 2/21/2019
- Frontier demands $4,300 cancellation fee despite horribly slow Internet Internet was often unusable, but ISP charges giant fee to one-person business; Ars; 2/22/2019
- If 5G Is So Important, Why Isn’t It Secure? Tom Wheeler, former FCC chairman; NYT; 1/21/2019
macOS
- Get Network Utility on macOS Ventura, Monterey, & Big Sur copy from macOS Catalina; OSXD; 12/16/2022
- How to test your Mac's internet speed and quality MW; 1/24/2022
- [2] How to use your Mac's Wi-Fi menu to sort out weak areas of Wi-Fi coverage
option-click WiFi icon; Tx Rate: raw data rate;
PHY Mode: layer, e.g., 802.11ac; Channel & Freq.;
BSSID (Basic Service Set IDentifier);
Solving weak spots; MW; 7/2/2021 - [2] How to Flush DNS Cache in MacOS Catalina & Big Sur OSXD; 8/27/2020
- How to share a Wi-Fi connection via macOS MW; 6/8/2020
- How to Prevent Mac from Remembering Wi-Fi Networks Joined OSXD; 6/7/2020
Modem, Router
- The Best Wifi Routers to Buy in 2024 LH; 1/24/2024
- Here's the Difference Between a Modem and a Router LH; 11/7/2023
- Why It's Still Worth It to Wire Your House for Ethernet faster; LH; 9/30/2023
- The Best Wi-Fi Routers NYT; 8/22/2023
- Best Mesh Routers CNet; 8/14/2023
- Best Wi-Fi Extenders CNet; 8/10/2023
- How to fix your network when you see 'Another device is using your IP address' Mac; Renew DHCP lease, etc. MW; 8/3/2023
- The Best Wi-Fi Routers Wired; 6/12/2023
- Do Routers Collect Data? I Read 30,000 Words of Privacy Policy to Find Out
all of them collect and share user data for marketing; CNet; 5/31/2023 - What is Ethernet? Everything You Need to Know About Wired Networks Wired; 4/20/2023
- The Gear to Get Reliable Wi-Fi in Any Home NYT; 4/6/2023
- Best Mac Router MW; 3/23/2023
- The Best Cable Modem NYT; 2/8/2023
- Why Your Wifi Router Needs a 'Guest Mode' more private and secure; LH; 9/23/2022
- Comcast says 2-gig speeds are rolling out now to 'millions'
with multi-gig symmetrical speeds set for 2023; Verge; 9/10/2022 - Best mesh Wi-Fi routers: Reviews and buying advice PC; 9/8/2022
- Modem vs. Router: What's the Difference? NYT; 9/7/2022
- The Best Wi-Fi Extender and Signal Booster NYT; 8/15/2022
- How to Tell If Someone Is Stealing Your Wifi (and Boot Them Off) LH; 3/18/2022
- Why We Love the TP-Link Archer A7 Wi-Fi Router NYT; 1/31/2022
- Which internet speed test should you use to test your connection at home? Ookla, Fast.com, MLab, Speedof.me, Testmy.net; CNet; 12/26/2021
- Nine WiFi routers used by millions were vulnerable to 226 flaws BC; 12/2/2021
- How to secure your home Wi-Fi network and router PC; 9/7/2021
- Wi-Fi extenders vs. boosters vs. repeaters: Major differences explained PC; 8/27/2021
- Point-to-point Wi-Fi bridging between buildings—the cheap and easy way Ars; 8/20/2021
- Improve Your Home Wi-Fi with Mesh, Powerline, MoCA, or More Routers TB; 8/19/2021
- Shopping for a Router Sucks. Here's What You Need to Know Wired; 8/16/2021
- Slow Wi-FI? Changing your Wi-Fi network channel and bandwidth settings might fix it PC; 7/19/2021
- How to set up a Wi-Fi extender PC; 7/8/2021
- Run out of ethernet ports on your router? network switches; TNW; 3/29/2021
- Is your internet connection driving you mad? Here's what might be behind it TNW; 3/21/2021
- AT&T scrambles to install fiber for 90-year-old after his viral WSJ ad from 3Mbps DSL to 300Mbps fiber: Aaron Epstein's newspaper ad gets amazing result; Ars; 2/12/2021
- Huzzah, Now ISPs Can't Charge Rental Fees for Your Own Dang Modem Frontier; Giz; 12/21/2020
- Comcast working toward 10Gbps to your home DOCSIS 4; ZD; 10/4/2020
- How home router manufacturers dropped the ball on security PC; 7/6/2020
- Disable UPnP on Your Wireless Router Already LH; 6/12/2020
- The 10 Best Ways to Boost Your Home Wifi LH; 6/8/2020
- Everything You Need to Know About Slow Internet Speeds comprehensive guide to what to do about them; NYT; 5/20/2020
- How to Regain Access to a Locked Linksys Account Smart Wi-Fi” service; LH; 4/21/2020
- You Need to Lock Down Your Router's Remote Management Options LH; 3/27/2020
- New attack on home routers sends users to spoofed sites that push malware DNS hijacking of Linksys, D-Link; Ars; 3/25/2020
- Hundreds of millions of cable modems are vulnerable to new Cable Haunt vulnerability Broadcom chips; ZD; 1/10/2020
- How to Secure Your Wi-Fi Router and Protect Your Home Network change passwords: admin and Wi-Fi (WPA2); update firmware; disable Remote Access, UPnP, and WPS; use a Guest Network (if avail); Wired; 1/4/2020
- Update These TP-Link Routers to Fix a Critical Password Vulnerability Archer C5 v4; Archer MR200v4; MR6400v4; Archer MR400v3; LH; 12/19/2019
- [2] How to Address Security Bugs in Your Old Router LH; 12/6/2019
- What's the Difference Between a Router and a Modem? MF; 3/15/2019
- Is your router's Wi-Fi working but ethernet has gone bad? Here’s how to check MW; 3/8/2019
- Amazon's acquisition of eero is met with concerns over data privacy and disappointment that eero will integrate with the tech giant's own ecosystem mesh WiFi router; Verge; 2/12/2019
 Wi-Fi
Wi-Fi
- Wikipedia: Wi-Fi: Wireless Local Area Network (WLAN); 802.11
- Wikipedia: WPA/WPA2 (Wi-Fi Protected Access); WEP (Wired Equivalency Protocol) obsolete
- Wikipedia: WPS (Wi-Fi Protected Setup) avoids long passcodes; convenience for users; can be vulnerable if PIN feature enabled
- HowStuffWorks: How WiFi Works; Quiz
- Take Control: Apple Wi-Fi Network
- 11 Ways to Upgrade Your Wi-Fi and Make Your Internet Faster
1. Move Your Router; 2. Use an Ethernet Cable;
3. Change the Channel or Band; 4. Upgrade Your Router;
5. Get a Wi-Fi Extender; 6. Use Your Electrical Wiring;
7. Add a Password to Your Wi-Fi; 8. Cut Off Unused Devices;
9. Check Your PC; 10. Restart Your Router?
11. Call Your ISP; Wired; 1/22/2024 - What is Wi-Fi 7? Everything You Need to Know Wired; 1/8/2024
- Your Computer Secretly Stores All Your Wi-Fi Passwords. Here's How to Find Them CNet; 3/22/2023
- Do This to Seamlessly Connect Guests to Your Wifi NFC, QR; LH; 11/21/2022
- How to Share Your Wi-Fi Password Wired; 8/7/2022
- Traveling? Beware of Unsecured Hotel Wi-Fi Networks OSXD; 7/28/2022
- How to Force Open a Public Wi-Fi Login Page (Captive Portal) OSXD; 6/26/2022
- How to make sure your hotel's Wi-Fi is fast enough USA; 5/27/2022
- These Things Are Blocking Your Home’s Wifi Signal LH; 5/26/2022
- Wi-Fi 7 Is Coming, and Here's Why You Should Care
IEEE 802.11be Extremely High Throughput (EHT); Giz; 2/16/2022 - The Best Ways to Boost Your Wifi Signal for Free LH; 2/2/2022
- How to Share Your Wifi Password
And, iOS, Mac, Win; LH; 12/20/2021 - The Truth About the Quietest Town in America
The National Radio Quiet Zone limits wireless communications.
But a journey to its center in Green Bank, West Virginia reveals a town at odds with itself.
Wired; 8/3/2021 - How to Share Your Wi-Fi Password
between Apple devices with visitor in your Contacts and vice versa;
QR code; Wired; 7/25/2021 - Did weak wi-fi password lead the police to our door?
BBC; 5/23/2021 - How to name your Wi-Fi networks for best Mac, iPhone, and iPad roaming
WPA2 settings; separate names useful if you have a lot of older equipment that bogs down the 5 GHz network; MW; 5/5/2021 - Wi-Fi's biggest upgrade in decades is starting to arrive Wi-Fi 6E (6GHz) devices are now being certified; Verge; 1/7/2021
- Check If the Wifi Is Going to Suck Before You Arrive Lag app; LH; 9/15/2020
- 5 Simple Ways to Improve Your Wi-Fi
1. Reposition your router;
2. Use an Ethernet cable instead;
3. Buy a new Wi-Fi router, extender or mesh networking kit;
4. Consider using a Wi-Fi hot spot (or your phone);
5. Upgrade your internet plan;
NYT; 8/24/2020 - How to turn your home Wi-Fi password into a QR code for easy sharing TNW; 7/20/2020
- Desperate for Wi-Fi, Many Have Nowhere to Go but a Parking Lot With cafes and libraries closed, Americans without internet access are sitting outside them to get free and fast connections; NYT; 5/5/2020
- How to Check Your Wifi Signal Strength LH; 4/27/2020
- What You Need to Know About Wifi 6E LH; 4/24/2020
- Flaw in billions of Wi-Fi devices left communications open to eavesdroppng Cypress and Broadcom chip bug; Ars; 2/26/2020
- [2] Ten rules for placing your Wi-Fi access points Ars; 2/24/2020
- You Need More Than HTTPS to Stay Safe on Public Wifi hackers can see metadata: domain names, size of files/pages, non-https sites & services; LH; 2/21/2020
- Find the WiFi Password For Almost Any Airport Lounge Using This Free Map LH; 1/20/2020
- [2] How to Find the Login Page on Public Wifi LH; 1/13/2020
- Tired of hearing about Wi-Fi 6? Great, let’s talk about Wi-Fi 6E doubling Wi-Fi's usable spectrum; Ars; 1/6/2020
- How Can I Find Out If Someone's Stealing My Wifi?
Low-tech method: Check your wireless router lights;
Network admin method: Check your router device list;
Detective method: Use a network monitoring software tool;
Moving forward: Beef up your wifi security; LH; 10/4/2019 - [2] How to Reveal Your Saved Wifi Passwords in Windows or macOS LH; 9/19/2019
- Wi-Fi 6 is barely here, but Wi-Fi 7 is already on the way in 2024; CNet; 9/3/2019
- Wi-Fi 6 Will Be Here Soon. What Is It? Wired; 8/29/2019
- Ask About a Hotel or Airbnb's WiFi Before You Book speed, caps, cost; LH; 8/25/2019
- With 'warshipping', hackers ship their exploits directly to their target's mail room Wi-Fi devices in packages; TC; 8/6/2019
- 82% of People in Study Say They Connect to Any Free WiFi That's Available in a Public Place 8/1/2019
- Never Commit a Crime When Your Phone Is Connected to a Wi-Fi Network Four students who left racist graffiti on their high school were caught when their smartphones betrayed them; Slate; 7/12/2019
- 6 Ways to Identify If You're Using Fraudulent Wi-Fi
1. The Wi-Fi Network Has A Vague Name.
2. You Haven't Confirmed The Network Name With Someone Trustworthy.
3. The Network Name Looks Almost Identical To Another One In The Area.
4. There Wasn't An Opt-In Page When You Logged On.
5. The Network Required You To Install Something Before You Could Use It.
6. The Network Isn't On A Reliable Database Of Vetted Networks; MF; 7/2/2019 - Wi-Fi 6: Better, faster internet is coming -- here's what you need to know CNet; 5/11/2019
- How Do I Share My Neighbor's Wi-Fi Connection? with permission; LH; 4/12/2019
- [2] Serious flaws leave WPA3 vulnerable to hacks that steal Wi-Fi passwords Ars; 4/11/2019
- How Do I Block My Neighbor's Wifi? LH; 3/22/2019
- A brief history of Wi-Fi security protocols from "oh my, that's bad' to WPA3 ~1997: WEP(RC4); ~1999:WPA(TKIP); ~2004:WPA2(AES-CCMP); ~2018:WPA3(NFC, PFS, SAE); Ars; 3/10/2019
- Do My Devices Have to Use the Same Wi-Fi Band to Talk to Each Other? LH; 3/8/2019
- [2] Which Wi-Fi Channels Should I Use for My Wireless Network?
2.4GHz (2400-2500MHz): 14 channels @ 20MHz each, all overlapping -- ideally, channels 1, 6, or 11;
5GHz (5200-5400MHz): 25 channels @ 20MHz each, though you’ll only typically see up to 12 options, each 40MHz wide;
you want your wireless networks to live on channels that have as few competing networks as possible;
wireless scanning app: Wifi Analyzer Win: free;
Wifi Explorer Mac: $20;
NetSpot: And, Mac, Win: free, $; LH; 2/22/2019 - Wi-Fi 6: is it really that much faster? WPA3; theoretical max speed: 9.6 Gbps vs. 3.5 Gbps on Wi-Fi 5; more about improving the network when many devices are connected; Verge; 2/21/2019
- Which Wi-Fi Band Should I Use for My Devices? 2.4GHz band: better range; 5GHz band: fastest speeds; congestion, number of devices? LH; 2/15/2019
- [2] WiFi firmware bug affects laptops, smartphones, routers, gaming devices lets attacker hijack devices without any user interaction; list of impacted devices includes PS4, Xbox One, Samsung Chromebooks, and Microsoft Surface devices; "patches are in the works"; ZD; 1/18/2019
Windows
Safer Internet: Connection: Use a VPN
Safer Internet: Connection: Use a VPN
Summary | Choosing | Configuration |
References: General | Android | Government | iOS |
Products/Reviews | macOS | Windows
Summary
- [1] Choose and Configure a Virtual Private Network (VPN) to connect to the Internet:
- To keep info extra private or secure:
when your device (or remote site) lacks the latest security updates
-- https: (normally secure) might be vulnerable,
or when communicating insecurely with a site via plain (unencrypted) http:
-- block ad injections/tracking by ISPs,
or when you're on an open, public, insecure non-WPA Wi-Fi network
(including Wi-Fi with a widely distributed password, e.g., coffee shop -- though https: is usually enough)
-- avoid MITM (man-in-the-middle) attacks from nearby,
or when using a foreign cell carrier or SIM card (whose encryption might be compromised),
or when plugging into a public ethernet jack, e.g., hotel cabling and/or switches may have been compromised. - If travelling, esp. internationally -- avoid monitoring and bypass content/service blocking,
e.g., [1] location-based "geofencing", e.g., streaming services, banks? [2] government censorship of sites/apps - Potential disadvantages: configuration, slower, sites may detect/block VPN access
 How much of connection is encrypted / anonymous?
How much of connection is encrypted / anonymous?
{Figure 4. TCYOP-4: 60; TCYOP-3: 48}- Connection between you and the VPN uses your IP address
-- everything is encrypted. - Connection between VPN and destination site uses VPN's IP address
-- content still encrypted, if https: used initially - Site does not see original IP address -- however, anonymity not guaranteed
if government or hacker can obtain VPNs server logs - [1] Reduce monitoring/logging by network providers (ISPs, cell companies) and governments
- If not using a full VPN, at least encrypt web address (DNS) lookups?
- "1.1.1.1 Faster Interet" (free Cloudflare app; iOS, Android) uses a VPN
to enable faster more secure DNS lookups (only) -- not content) (section: WiFi: DNS) - [2] If working remotely -- company info very attractive to hackers/spies
- [2] Reduce recording of your searches by search engines, e.g., Google
-- there are easier ways, e.g., see :Browsing:Search Privately - [3] For more anonymity (IP address), see Browsing:Anonymity, e.g., Tor, TAILS
- [3] If you're a high-profile target: dissident, whistleblower, executive, celebrity, wealthy, cryptocurrency speculator, ...
- [3] Supplement your firewall protection
- References
Choose a VPN Service
- paid version vs. free (ads, limits)
- performance -- it can be somewhat -- or a lot -- slower
- company experience, longevity, privacy policy, trustworthiness
- anonymity decreased by server logs?
- network reliability, availability
- bandwidth/transfer limits
- configuration ease & support
- trustworthiness & accuracy of product reviews
-- there are many mediocre or bad services; don't choose only because of an 'incredible' (life-time) price. - country of company's servers and operations?
some believe their government can't obtain their logs if a VPN company is based 'offshore';
if ownership and security policies of a VPN are not transparent, can you trust that it isn't run by a government agency, or ? - Joe's recommendations {TCYOP-4: 60-61; TCYOP-3: 49-50} -- all platforms, unless otherwise noted
- [1] Free, ad-supported, usage caps, e.g., Hotspot Shield; privacy risk?
- [1] Free, specific browser, e.g., Opera; Mac, Win
 [1] Paid services/subscriptions:
[1] Paid services/subscriptions:- Cargo VPN (Mac-only)
- Encrypt.me (formerly Cloak)
- Disconnect Premium; browser only? includes other privacy and security features
- IVPN
- personalVPN / WiTopia* (also: jumpthewall.net);
Why Use a VPN?; Why We're the Best VPN;
[1] And, iOS, Mac, Win; [2] others -- on right: "Quick Connect" screen;
*if you subscribe to personalVPN, please use this referral link (or code: Q8Hg3YRM)
-- you'd receive an immediate 15% discount, and Steve receives a similar credit! - Private Internet Access (PIA)
- [3] NordVPN; also routes your connections through Tor
- [3] Hardware VPN router, e.g., WiTopia Cloakbox Pro, e.g., for all home devices
 Configure and Use a VPN Service
Configure and Use a VPN Service
- Example personalVPN (Witopia): all platforms: apps & manual setup
- personalVPN apps available: Android; iOS; macOS, Windows
- others (manual setup): Chromebook, Fire, Linux, Surface, etc.
- In app, login using separate VPN username and password
-- different from main account credentials. - iOS:
Settings > VPN; right: configurations: "1.1.1.1" & personalVPN 
 Instead of default (Quick) connection, change to
Instead of default (Quick) connection, change to
a gateway/server in a different country or specific city,
e.g., on right: iOS and Mac screens- [2] comparison of protocols;
setup: IPsec; L2TP; IKEv2;
[3] OpenVPN/OpenSSL most secure/customizable;
[3] PPTP older, not recommended
References
- {TCYOP-4: 59-66; TCYOP-3: 47-57; Recommendations, Beware VPN Review Sites, The Problem of End-to-End Privacy, Using a VPN Router, SSL Implementation Bugs and Issues, Avoid DNS Mischief}
- sections: Refs: Android; Government; iOS; Products/Reviews; macOS; Windows
- topics: censorship, China, IPSec, L2TP, PPTP, OpenVPN
- Wikipedia: VPN; proxy server
- Wikipedia: Tunneling Protocol; Internet Protocol Security (IPsec); Point-to-Point Tunneling Protocol (PPTP); Layer 2 Tunneling Protocol (L2TP); OpenVPN
- table: PPTP vs L2TP/IPSec vs OpenVPN
- HowStuffWorks: How VPNs Work
- dnsleaktest.com, ipleak.net check if IP address private
- Don't Fall for These 7 VPN Myths
1. VPNs are mostly for illegal activity
2. VPNs make you completely anonymous
3. Free VPNs are just as good as paid VPNs
4. VPNs speed up your internet
5. VPNs can bypass any geo-restrictions
6. VPNs are too complex to use
7. VPNs protect against malware and viruses
CNet; 11/9/2023 - 5 Reasons to Use a VPN CNet; 9/29/2023
- VPN Obfuscation: What It Is and Why You Might Need It CNet; 8/17/2023
- Why You Should Use a VPN When Booking a Hotel it's travel industry standard to use dynamic pricing, location is one of the many factors that affect prices
-- one of the few you can control; LH; 8/9/2023 - Browser-Based VPNs: 3 to Try if You Want to Improve Online Privacy
easier and speedier to use than typical VPNs (router, apps), these lightweight privacy boosts are handy to have around;
Brave Firewall + VPN; Firefox Private Network; Chrome w/ a VPN extension; CNet; 10/7/2022 - What You Need to Know About Google's VPN
if you pay for Google's cloud storage, you might be able to take advantage of it; Giz; 2/25/2022 - 3 companies control many big-name VPNs: What you need to know
Kape Technologies Plc (Formerly Crossrider Plc): CyberGhost VPN (Crossrider), ZenMate VPN, Private Internet Access, ExpressVPN;
Ziff Davis (Formerly J2 Global, Inc.): IPVanish, Strong VPN (Encrypt.me, ibVPN, SaferVPN);
Nord Security (Tesonet): NordVPN, Atlas VPN, Surfshark;
CNet; 2/5/2022 - Here's why you probably don't need to rely on a VPN anymore
the widespread use of encryption has made public internet connections far less of a security threat, cybersecurity experts say; NBC; 12/31/2021 - A New Report on VPNs Shows They're Often a Mixed Bag for Privacy
Consumer Reports white paper; Giz; 12/8/2021 - iCloud+ Private Relay explained: Don't call it a VPN
'public beta' feature this fall for paid iCloud accounts;
VPN differences: works only w/ Safari, not all traffic;
easily identifiable as a 'proxy server' (VPNs usually aren't);
can't hide your region; MW; 11/17/2021 - It’s Time to Stop Paying for a VPN
more sites use https: and/or support MFA; NYT; 10/6/2021 - NSA, CISA Release Guidance on Selecting and Hardening Remote Access VPNs 9/28/2021
- Can ISPs, Websites, and Your Boss Tell If You're Using a VPN? LH; 9/10/2021
- VPN Hacks Are a Slow-Motion Disaster
recent spying attacks against Pulse Secure VPN are just the latest example of a long-simmering cybersecurity meltdown;
Wired; 4/25/2021 - Is your VPN secure? How to make sense of VPN encryption PC; 3/24/2021
- Three VPNs popular with criminals and active for over a decade have had their servers and web domains seized by law enforcement from US, Germany, France, others safe haven for cybercriminals to carry out ransomware attacks, web skimming operations, spearphishing, and account takeovers; ZD; 12/22/2020
- Researchers say seven Hong Kong-based 'no log; VPNs have left 1TB+ of user logs and personally identifiable info exposed on the internet Reg; 7/17/2020
- VPNs: 3 things they can't help you with Let you game at work without the boss knowing; Protect you from viruses and tracking; Get you online during an internet shutdown; CNet; 3/10/2020
- Popular VPN And Ad-Blocking Apps Are Secretly Harvesting User Data Android: Free and Unlimited VPN, Luna VPN, Mobile Data, Adblock Focus; iOS: Adblock Focus, Luna VPN; BF; 3/9/2020
- NordVPN users' passwords exposed in mass credential-stuffing attacks Ars; 11/1/2019
- How to Protect Your Data in the NordVPN, TorGuard and VikingVPN Breaches LH; 10/22/2019
- Hackers steal secret crypto keys for NordVPN. Here's what we know so far Breach happened 19 months ago; Ars; 10/21/2019
- Cloudflare Launches Its Security-Focused Mobile VPN, Again WARP; Wired; 9/25/2019
- Opera 60 debuts with a free, faster VPN, and Netflix hasn't blocked it yet PC; 4/10/2019
- Cloudflare 1.1.1.1 with Warp Accelerates Internet Privacy 4/1/2019
Android
- Best Android VPN CNet; 10/9/2023
- The 5 best VPNs for Android PC; 6/17/2023
- 7 Android VPN apps you should never use because of their privacy sins Yoga, proXPN, Hola, oVPNSpider, SwitchVPN, Zoog, Seed4.Me; CNet; 9/9/2019
- Opera adds unlimited VPN service to its Android browser for free 256-bit encryption and no data logging; 3/20/2019
- Check if Your Android VPN Is Collecting Personal Data LH; 3/7/2019
- Facebook VPN that snoops on users is pulled from Android store Onavo Protect VPN (removed for iOS 8/2018); Ars; 2/22/2019
- How to Set Up Opera's Mobile VPN for Secure Browsing on Android LH; 2/7/2019
Government
- Russians Need VPNs. The Kremlin Hates Them Wired; 3/30/2022
iOS
- All iOS VPNs are worthless and Apple knows it, claims researcher
long-time bug in iOS prevents any VPN from fully encrypting all traffic; ApIn; 8/17/2022 - Security researchers warn of scam VPN apps on iOS Buckler VPN, Hat VPN, Beetle VPN; fake reviews, expensive subscriptions; ApIn; 6/3/2020
- Researcher: a vulnerability affecting iOS 13.3.1 and later prevents VPNs from encrypting some traffic, potentially exposing user data or leaking IP addresses BC; 3/26/2020
- How to View VPN Connect Time on iPhone or iPad OSXD; 2/5/2020
- How to Delete a VPN from iPhone or iPad OSXD; 12/14/2019
macOS
- How to use a VPN on a Mac MW; 12/7/2022
- Apple has removed a controversial feature in macOS 11.2 beta 2 that allowed its own apps to bypass third-party firewalls, security tools, and VPNs ZD; 1/14/2021
- Apple apps on Big Sur bypass firewalls and VPNs TNW; 11/16/2020
- How to Delete a VPN Configuration from Mac OSXD; 2/2/2020
Products / Reviews
- Witopia sometimes is not listed in (paid) product reviews, or given a bad rating (possibly since based in US). Witopia Support responded to me: "Honestly we are not sure where they are getting a lot of their data from as it is not accurate. They are even giving a bad rating for companies that have offices in the USA which is odd. We have reached out to them many times to try and get them to correct the bad data but they refuse to reply or correct. We do not store any logs of users. We do not share data with other parties about your usage, sites, services etc. We do not limit anything (bandwidth, filters throttles etc)."; About; Why We Are the Best VPN
- Best VPN services: Reviews and buying advice for Mac users MW; 11/6/2023
- Best VPN service CNet; 8/28/2023
- Best Mac VPN CNet; 8/20/2023
- Best VPN Services: Reviews and Buying Advice PC; 8/10/2023
- The Best VPNs to Protect Yourself Online Wired; 7/9/2023
- TunnelBear 5.0.1 TB; 4/21/2023
- Best VPN Service NYT; 3/14/2023
- NordVPN review: A great choice for Netflix fans, but who's running the show? NordVPN has good performance, great features, and it suits novices and power users alike. But who is running the show down there? PC; 9/29/2021
- You Should Probably Stop Using ExpressVPN
Kape Technologies (an Israeli technology firm with a controversial past) owns ExpressVPN, Private Internet Access (PIA), CyberGhost, ZenMate; Giz; 9/24/2021 - Which VPN Providers Really Take Privacy Seriously in 2021? 6/14/2021
- Is a free VPN safe? What to look for
Who runs the VPN?
What data does the VPN collect?
What does the VPN do with your data?
How does the VPN make money?
How does the VPN secure your data?
Best free VPNs to start with; PC; 3/15/2021 - Hackers are actively trying to steal passwords from two widely used VPNs Fortigate, Pulse Secure; Ars; 8/24/2019
- Risky free VPNs still available in Apple App Store & Google Play despite warnings AI; 8/13/2019
- Do You Trust Your VPN? Are You Sure?
what's 'reputable'? US vs. offshore location/ownership? some VPNs are scams, shady/biased review sites, slow performance, ads; Slate; 2/28/2019
Windows
- Malwarebytes releases new VPN service for Windows Malwarebytes Privacy. in future: Mac, iOS, Android, ChromeOS versions; BC; 4/23/2020
Safer Internet: Connection: Avoid Malware
Safer Internet: Connection: Avoid Malware
Quotes | Summary | Types | User Practices | Apps | Plugins | Flash | Java | Anti-Virus | Advanced |
References: General | Android | Anti-virus | Cyberattacks/Cyberwar |
Extensions, Plug-ins | Flash, Shockwave | iOS | Java | JavaScript | macOS |
Microsoft Office | Ransomware | Spyware | Web Servers | Windows
Quotes
- "In God we trust,...
- "If you spend more on coffee than on IT security,...
- Amish Virus...
- Disney Virus...
- Prozac Virus...
- Airline Virus...
- Health Care Virus...
- Dr. Jack Kevorkian Virus...
- Viagra Virus...
- Viagra 2 Virus...
Summary
- [1] Understand different types of malware, by transmission and action
- [1] Improve user practices: "be-aware"
- [1] Install and update approved apps: software
- [1] Manage / Minimize Plugins, Extensions, Add-ons
- [1] Flash: Update, Block or Uninstall
- [1] Java: Update, Block or Uninstall (but keep JavaScript enabled)
- [1] Install & Maintain AntiVirus tools -- if available / applicable
-- lower priority than updating software and safer user behaviors. - [2] Disable programming functionality in apps, e.g., Microsoft Office macros
- [3] Advanced Settings: JavaScript, WebGL, web admin
- References
[1] Understand Different Types of Malware
- Malware can access, compromise local files -- and online identities and accounts.
- Viruses Wreak Havoc On Your Files
- Spyware Steals Your Information
- Scareware Holds Your PC for Ransom
- Trojan Horses Install a Backdoor
- Worms Infect Through the Network
- There's often overlap
[1] Improve User Practices
- Pay attention -- most malware requires active user involvement
- Don't click on links or open attachments in an unexpected email from "friends", "boss", "family"
- Use browser Bookmarks / Favorites or a password manager to access web sites -- see later section: Browsing: Go To Correct Site
- Don't click on links in popups, or unknown links in web pages, esp. ads
- Do not respond to popups that "hijack" your browser, esp. those that "found malware" or download unexpected 'Flash updates' -- just quit browser (see Block Ads section if you can't close/quit); reputable companies do not use such annoying / scare tactics
[1] Install and Update Approved Apps
- Backup your Devices; install & update your software -- system and applications -- by downloading only from vendor's app store (if screened), app's own Update preference or control panel, other reputable sites
- [3] macOS: System Integrity Protection (SIP) is enabled by default, which aims to protect critical system folders by locking them down; temporarily disable SIP only if you know what's you're doing
- [3] Don't "jail break" or "root" your device, i.e., don't install unofficial or pirated system/application software -- or visit "warez" or "dark" sites
- macOS:
App Store - iOS:
App Store - macOS:
System Preferences > Security & Privacy > General > Allow Apps Downloaded From:[screenshot] - [1]
Mac App Store - [2]
Mac App Store and Identified Developers - [3]
Anywhere-- note: option hidden by default in 10.12 - [2] To open an "unidentified" app that you're sure about:
- macOS:
Applications > (ctrl-click app) > Open > Open - iOS: use the TestFlight app to accept expected invitations from known developers
- Enable phishing/malware/plugin warnings
- macOS:
Safari > Preferences > Security > Fraudulent sites; Internet plug-ins[screenshot] - macOS:
Firefox > Preferences > Security > Block reported attack sites / web forgeries / add-ons - macOS:
Chrome > Settings > Advanced Settings > Privacy > Protect you and your device from dangerous sites - iOS:
Settings > Safari > Privacy & Security > Fraudulent Website Warning[screenshot] - [2] Don't automatically open downloaded files (check file types)
- macOS:
Safari > Preferences > General > Open "safe" files after downloading[screenshot]
[1] Manage / Minimize Plugins, Extensions, Add-ons
- macOS:
Safari > Preferences > Security > Allow plugins[screenshot]; [screenshot: Plug-in Settings] - macOS:
Firefox > Preferences > Applications - macOS:
Firefox > Preferences > Security > Warn me when sites try to install add-ons - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Content Settings > Plugins; also Unsandboxed Plugins - Consider disabling problematic, obsolete, infrequently-used plugins
- most sites, e.g., YouTube, default to HTML5 for video if Flash not present; Java less popular -- covered next
- iOS: unnecessary -- since plugins are not generally allowed
- configure to selectively load a plug-in if desired, or re-install if needed
- remove obsolete plugins, e.g., Microsoft Silverlight
- macOS:
Finder > (disk/user) > Library > Internet Plugins
[1] Flash: Update, Block or Uninstall
- iOS: NA
- macOS: I generally recommend uninstalling Flash from system; if necessary to use for some Flash-based sites, selectively use Google Chrome, which keeps Flash up-to-date automatically (at least for a little while longer), provides "sandboxing", and also auto-pauses certain videos / ads
- macOS:
Chrome > chrome://plugins > Enable, Always Allow to Runmaybe possible to run on-demand selectively via ctrl-click? - If you do need to use Flash more frequently / conveniently, make sure it's always up to date and control using a flash blocker
- macOS:
System Preferences > Flash Player > Advanced > Updates - macOS:
System Preferences > Flash Player > Storage > Delete All - macOS:
Safari > Preferences > Extensions > Get Extensions : ClickToFlash - macOS:
Safari (ctrl-click) > ClickToFlash Preferences - macOS should automatically disable insecure versions, and display message: 'Blocked plug-in', 'Flash Security Alert' or 'Flash out-of-date'
 [1] Java: Update, Block or Uninstall
[1] Java: Update, Block or Uninstall
- iOS: NA
- macOS:
System Preferences > Java > Update[screenshot] - macOS:
System Preferences > Java > Security > Security Level - macOS:
Safari > Preferences > Security > Allow Plugins > Website Settings : Java : Ask[screenshot] - If installer wants to install any crapware or change settings by default, e.g., Yahoo homepage, search engine -- uncheck anything you don't want! -- installer now seems to be 'clean'
[1] Install Anti-Virus (AV)
- Install & maintain antivirus software on your device, if applicable & desired
- Be careful where you obtain malware protection software -- some may be malware / adware itself -- especially if obtained via ad links, popups, pop-under windows
- Having AV installed is no excuse to be careless
- iOS: unnecessary
- macOS: optional -- to avoid distributing infected files to others, e.g., Windows friends, or if still using external portable media from unknown sources: USB drives, CD/DVD, floppies, etc.
- virus definitions may not include newest threats; scanning may slow down, interfere with system
- examples: Avast; Avira; ClamXav; Comodo; Sophos
- note: if you're running Windows on macOS (using Boot Camp, or virtualization software like VMware Fusion or Parallels Desktop), you should absolutely run Windows anti-malware software -- Mac anti-malware won't help
- Windows:
Windows Settings > Update & Security > Windows Defender - If you must use others' devices to access your accounts, make sure they're well-protected (antivirus) and maintained (software updates) -- see Mobile Privacy section, esp. to avoid keyloggers or other spyware
[3] Advanced Settings: JavaScript, WebGL, web admin
- JavaScript: on
- JavaScript (not the same as 'Java') is essential for most modern sites; most browsers don't provide an option to disable
- macOS:
Safari > Preferences > Security > Enable JavaScript - You can generally remove tracking scripts by using a Content/Ad Blocker -- see Block Ads section
- WebGL: on
- WebGL (Web Graphics Library) JavaScript-based graphics using GPU
- macOS:
Safari > Preferences > Security > Allow WebGL - If administering your own website, check system log for suspicious activity, e.g., logins to non-existent or unauthorized accounts, unexpected accesses to admin pages or to non-existent modules / pages / directories; add suspicious IP addresses to a 'deny list'
References
- {TCYOP-4: 70-71; TCYOP-3: 57-58}
- sections: Refs: Android; Anti-virus; Cyberattacks/cyberwar; Extensions, Plug-ins; Flash, Shockwave; iOS; Java; JavaScript; macOS; Microsoft Office; Ransomware; Spyware; Web Servers; Windows
- topics: airgap, botnet, cryptojacking, keylogger, social engineering, USB drives, zombie
- other computer virus jokes: politicalhumor.about.com; ahajokes.com
- Wikipedia: Malware: short for malicious software, is a general term used to refer to a variety of forms of hostile or intrusive software, e.g, to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Only some is internet-related.
- HowStuffWorks: How to Detect Online Scams
- Wikipedia: Zero day attack exploits a previously unknown vulnerability in a computer application or operating system, one that developers have not had time to address and patch
- Wikipedia: Worm: malware that actively transmits itself (automatically, w/o user intervention) over a network to infect other computers
- Wikipedia: Virus: malware that has infected some executable software and, when run (usually by user opening a program, email or document), causes the virus to spread.
- HowStuffWorks: How Computer Viruses Work; How to Know if Your Computer is Infected with a Virus
- HowStuffWorks: How do viruses and worms spread in e-mail?
- HowStuffWorks: 10 Worst Computer Viruses of All Time
- Wikipedia: Trojan Horse: malware that appears benign/desirable but conceals malicious code; e.g., Zeus (2007-)
- HowStuffWorks: How Trojan Horses Work
- Viruses, Trojans and Worms video: 2:31
- Wikipedia: Botnet: collection of Internet-connected programs communicating with other similar programs in order to perform tasks -- some may be malware
- Wikipedia: Zombie computer: malware used to send email spam, to host contraband data such as child pornography, or to extort via distributed denial-of-service attacks.
- Wikipedia: Denial of Service Attack (DoS): make a machine or network resource unavailable to its intended users
- HowStuffWorks: How Zombie Computers Work; How to Fix Your Zombie Computer
- Wikipedia: air gap physically isolate a secure computer network from unsecured networks
- Wikipedia: Rootkits modify the host's operating system so that the malware is hidden from the user.
- Wikipedia: man in the middle attach (MITM) requires an attacker to have the ability to both monitor and alter or inject messages into a communication channel
- Wikipedia: Logic bomb: malware triggered by certain conditions, e.g., programmer fired
- HowStuffWorks: How does a logic bomb work?
- Wikipedia: social engineering obtaining confidential information by manipulating and/or deceiving people
- Wikipedia: Hacker (black hat); Firewall
- Wikipedia -- conferences/conventions: Black Hat Briefings; DEF CON
- HowStuffWorks: How Hackers Work; How Firewalls Work; Could hackers devastate the U.S. economy?; Computer Security Quiz
- That QR Code You’re About to Scan Could Be Risky, F.T.C. Warns NYT; 12/11/2023
- How to Not Get Hacked by a QR Code "quishing"; Wired; 12/3/2023
- It's Safe to Scan QR Codes (If You're Careful) LH; 5/12/2023
- FBI Advising People to Avoid Public Charging Stations 4/12/2023
- How to Recover From a Browser Hijacking Attack LH; 3/9/2023
- Why You Should Never Plug In an Unknown USB Device LH; 7/7/2022
- How to Use Microsoft Defender on All Your Devices
the security tool for Apple, Android, and Windows is now
available to any Microsoft 365 subscriber; Wired; 6/27/2022 - Steps to Simple Online Security: 8: Free Antivirus Software Is Good NYT; 4/15/2022
- FCC puts Kaspersky on security threat list, says it poses "unacceptable risk"
Moscow-based firm joins Huawei and ZTE on the same US security threat list; Ars; 3/25/2022 - The Log4J Vulnerability Will Haunt the Internet for Years Wired; 12/13/2021
- Hacker Lexicon: What Is a Watering Hole Attack?
two types of victims: the legitimate website or service that attackers compromise
to embed their malicious infrastructure, and the users who are then compromised
(usually via browser bug) when they visit; Wired; 11/28/2021 - 'Stalkerware' Apps Are Proliferating. Protect Yourself.
these spyware apps (mostly Android, some iOS) record your conversations, location and everything you type,
all while camouflaged as a calculator or calendar; NYT; 9/29/2021 - Feds list the top 30 most exploited vulnerabilities. Many are years old Ars; 7/29/2021
- Amnesty International researchers published a toolkit to help anyone scan their iPhone and Android devices for evidence of compromise by NSO's Pegasus spyware TC; 7/19/2021
- No, open source Audacity audio editor is not "spyware"
the community's telemetry concerns were received and addressed two months ago;
new privacy policy; Ars; 7/6/2021 - Google App Engine feature abused to create unlimited phishing pages malicious subdomains; BC; 9/20/2020
- How to Check Your Devices for Stalkerware Wired; 7/19/2020
- TikTok says it will stop clipboard snooping after iOS 14 reveals when apps attempt to read the clipboard; TikTok claims it was used to identify spammy behavior Tel; 6/25/2020
- Hacker Lexicon: What Is a Side Channel Attack? computers constantly give off more information than you might realize—which hackers can use to pry out their secrets; Wired; 6/21/2020
- UPnP flaw exposes millions of network devices to attacks over the Internet Windows; printers, modems, routers; best defense is to disable UPnP altogether; Ars; 6/11/2020
- The Curious Case of Copy & Paste -- on risks of pasting arbitrary content in browsers 6/2/2020
- Major security flaw found in Thunderbolt Macs and PCs: Should you be worried? for Mac, only if physical access to powered on Mac; MW; 5/16/2020
- Filipino Onel de Guzman, author of the Love Bug worm that infected millions of PCs in May 2000, talks about his creation and claims he regrets writing it BBC; 5/3/2020
- Meet the white-hat group fighting Emotet, the world's most dangerous malware Cryptolaemus group; from banking trojan to malware loaded; ZD; 2/29/2020
- Microsoft to bring its Defender antivirus software to iOS and Android malware and phishing attack protection; CNet; 2/20/2020
- One of the most destructive botnets can now spread to nearby Wi-Fi networks weak WiFi passwords; Ars; 2/11/2020
- There's a scary new reason not to borrow a stranger's iPhone cable FC; 10/8/2019
- How Can You Tell If an App Is Malware? LH; 9/20/2019
- How to Find Spyware Your Employer Installed on Your Computer and What to Do About It Giz; 8/5/2019
- The Worm That Nearly Ate the Internet Conflicker infected 10 million computers in 2010. So why did cybergeddon never arrive? NYT; 6/29/2019
- A Computer Afflicted With 6 Infamous Viruses Has Passed $1 Million at Auction art project: The Persistence of Chaos; MB; 5/21/2019
- Hard-to-detect credential-theft malware has infected 1,200 and is still going Separ's 'living-off-the-land' approach (spartan malware that's built on legitimate apps and utilities) bypasses many antimalware providers; starts by end user clicking on a disguised executable; Ars; 2/20/2019
Android
- How Hackers Tricked 300,000 Android Users into Downloading Password-Stealing Malware LH; 12/1/2021
- Uninstall These Malicious Android Apps That Stole Facebook Passwords LH; 7/4/2021
- How to Get Rid of Android's Most Annoying Malware: xHelper LH; 2/18/2020
- This New Android Malware Can Survive a Factory Reset LH; 10/30/2019
- Double-Check That Your Android Antivirus App Actually Works some underperform or may even pose serious security risks; LH; 3/20/2019
- In a test of 250 Android antivirus apps in the Google Play Store, only 80 could detect more than 30% of malware, and only 23 had 100% detection rate ZD; 3/14/2019
- Delete These Malware-Laden Apps From Your Android Right Now LH; 3/14/2019
Anti-Virus
- HowStuffWorks: Is there any free anti-virus software?
- Avast shutters data-selling (Jumpshot) subsidiary amid user outrage Users were not happy to learn "security" software sold their browsing habits; Ars; 1/30/2020
- Antivirus Maker Avast Sold Data on Millions of Users TB; 1/29/2020
- Are You One Of Avast’s 400 Million Users? This Is Why It Collects And Sells Your Web Habits. Forbes; 12/9/2019
- Recent antivirus tests are bad news for paid security suites Windows; their basic AV capabilities are being equaled by free apps; PC; 1/30/2019
Cyber Attacks, CyberWar
- Wikipedia: Anonymous loosely associated international network of activists and hacktivists; well-known for distributed denial-of-service (DDoS) attacks on government, religious, and corporate websites
- Wikipedia: Hacktivism; Denial of Service Attack make a machine or network resource unavailable to its intended users
- HowStuffWorks: How Anonymous Works
- Wikipedia: Computer Emergency Response Team Internet security incidents and cyberthreats
- Wikipedia: cyberterrorism; cyberwar Kosovo 1998; US Cyber Command; CISPA: Cyber Intelligence Sharing and Protection Act proposed: 2011
- HowStuffWorks: Is cyberwar coming?; How CISPA Works
- HowStuffWorks: What does the U.S. cybersecurity czar do?; Could a single hacker crash a country's network?; Could hackers devastate the U.S. economy?
- Could Cyberwar Make the World Safer? NYT; 8/22/2021
- The Untold History of America's Zero-Day Market lucrative business of dealing in code vulnerabilities is central to espionage and war planning; Wired; 2/14/2021
- With Hacking, the United States Needs to Stop Playing the Victim the U.S. also uses cybertools to defend its interests. It’s the age of perpetual cyberconflict; NYT; 12/23/2020
- Journalist’s phone hacked by new 'invisible' technique: All he had to do was visit one website. Any website. NSO Group; 6/21/2020
- China's Military Is Tied to Debilitating New Cyberattack Tool Aria-body (embedded in MS Office files) had been deployed against governments and state-owned companies in Australia and SE Asia; NYT; 5/7/2020
- A Critical Internet Safeguard Is Running Out of Time Shadowserver; Wired; 3/16/2020
- The Untold Story of the 2018 Olympics Cyberattack, the Most Deceptive Hack in History Wired; 10/17/2019
Extensions, Plug-ins
- see sections: Flash, Java
- Wikipedia: Silverlight; Adobe (Macromedia) Shockwave
- Ethical.net: Browser extensions
- Our Favorite Ad Blockers and Browser Extensions to Protect Privacy NYT; 9/30/2021
- Our Favorite Ad Blockers and Browser Extensions to Protect Privacy
Ad blocker: uBlock Origin;
Tracking blocker: Privacy Badger;
Secure connections: HTTPS Everywhere;
Cleaner links: ClearURLs;
Local resources: Decentraleyes;
Login protection: Use a password manager;
Firefox Multi-Account Containers;
Extra-credit tools: Use a VPN, Enable DNS over HTTPS (DoH), Change your default search engine;
NYT; 3/11/2021 - How to Make Sure Your Browser Extensions Are Safe Wired; 6/27/2021
- Teams behind Chrome, Safari, Firefox, and Edge unveil a development forum at W3C to standardize and build a unified, more secure foundation for extensions CNet; 6/4/2021
- Up to 3 million devices infected by malware-laced Chrome and Edge add-ons 28 malicious extensions hosted by Google and Microsoft; Ars; 12/16/2020
- What You Need to Know About the Latest Chrome Extension Malware Campaign LH; 6/24/2020
- Check Chrome and Remove Any of These 70+ Malware Extensions LH; 2/14/2020
- Mozilla removes four Firefox extensions made by Avast and AVG after reports that they were harvesting user data and browsing histories still available on the Chrome Web Store; ZD; 12/3/2019
- DuckDuckGo Privacy Essentials extension returns to Safari ApIn; 11/7/2019
- Mozilla to stop supporting sideloaded extensions in Firefox starting March 2020, with Firefox 74; ZD; 11/1/2019
- Google to Minimize the Data Collected by Chrome Extensions PC; 7/23/2019
- Uninstall These Eight Browser Extensions That Stole Data from Millions
Branded Surveys (Chrome); FairShare Unlock (Chrome and Firefox)
HoverZoom (Chrome); Panel Community Surveys (Chrome)
PanelMeasurement (Chrome); SaveFrom.net Helper (Firefox)
SpeakIt! (Chrome); SuperZoom (Chrome and Firefox); LH; 7/18/2019 - My browser, the spy: How extensions slurped up browsing histories from 4M users Have your tax returns, Nest videos, and medical info been made public? DataSpii: How extensions hide their data grabs -- and how they're discovered; Ars; 7/18/2019
- A third of all Chrome extensions request access to user data on any site 35.4% ask users for permission to access and read all their data on any site, 84.7% had no privacy policy; check privacy/security of any Chrome extension: CRXcavator; ZD; 2/22/2019
- [2] How Web Apps Can Turn Browser Extensions Into Backdoors TP; 1/22/2019
- It's Time to Audit All the Extensions You've Installed on Your Browser Chrome, Firefox, Safari, Edge; Giz; 1/18/2019
Flash, Shockwave [Adobe]
- Wikipedia: plugin; Flash; Flash cookies
- Microsoft to fully remove Adobe Flash from Windows 10 in July PC; 5/4/2021
- Flash Is Dead -- but Not Gone Zombie versions of Adobe’s troubled software can still cause problems in systems around the world; Wired; 1/24/2021
- Adobe just released the last Flash update ever Flash Player will block playback starting on 1/21/2021; Verge; 12/9/2020
- Flash Animations Live Forever at the Internet Archive no plugin required, just WebAssembly support; 11/19/2020
- Flash on Firefox will die completely in 55 days Firefox 83 is the penultimate version of Mozilla's browser to support the once ubiquitous plug-in. Security and battery life concerns hastened its demise; CNet; 11/17/2020
- Microsoft Is Finally Purging Flash From Windows Giz; 10/28/2020
- Porn surfers have a dirty secret. They’re using Internet Explorer -- and Flash Ars; 9/12/2020
- The rise and fall of Adobe Flash Ars; 7/7/2020
- Adobe Flash Is Actually Going to Die This Time, For Real [12/31/2020] Giz; 6/16/2020
- How to Enable Flash on Chrome Browser OSXD; 2/17/2020
- How to Avoid the Most Popular Mac Malware, 'Shlayer' fake Flash Player download; LH; 1/24/2020
- Google's Chrome 76, now in beta, will block Flash by default a Google employee claims Chrome 76 will prevent sites from detecting users in Incognito Mode; 9to5; 6/13/2019
- Adobe Shockwave will be discontinued on 4/9/2019 interactive content has moved to platforms like HTML5 Canvas and WebGL in recent years; Verge; 3/11/2019
- Microsoft culls secret Flash allow list after Google points out its insecurity Previously, some 58 sites were given special treatment. Now it's only Facebook; Ars; 2/20/2019
- [2] Malvertisers target Mac users with steganographic code stashed in images via HTML5 coding; underlying link if clicked directs to fake Flash update site; Ars; 1/24/2019
- Mozilla: Firefox 69 will disable Adobe Flash plugin by default ZD; 1/14/2019
iOS
- How NSO Group's iPhone-Hacking Exploit Works Giz; 12/22/2021
- Using Extensions in Safari in iOS 15 and iPadOS 15 TB; 10/2/2021
- Pegasus spyware: How to check your iPhone and why you shouldn't worry MW; 7/22/2021
- This App (iVerify) Will Tell You if Your iPhone Gets Hacked with caveats; MB; 11/14/2019
- How 18 Malware Apps Snuck Into Apple's App Store phony ad clicks; Wired; 10/25/2019
- Make Sure You Didn't Download One of These 17 Malicious iOS Apps LH; 10/24/2019
- [2] Checkm8 creator says his iPhone exploit requires physical device access and lacks persistence after reboot but will make jailbreaking more accessible and safer; Ars; 9/28/2019
- [2] Unpatchable bug in millions of iOS devices exploited, developer claims "Checkm8" jailbreak exploit works on devices from iPhone 4s to iPhone X, developer claims; Ars; 9/27/2019
- Mysterious iOS Attack Changes Everything We Know About iPhone Hacking For two years, a handful of websites have indiscriminately hacked thousands of iPhones; Wired; 8/30/2019
- These Legit-Looking iPhone Lightning Cables Will Hijack Your Computer MB; 8/10/2019
- It's Almost Impossible to Tell if Your iPhone Has Been Hacked MB; 5/14/2019
- Cybersecurity 101: Five settings to secure your iPhone or iPad
1. Turn on USB Restricted Mode to make hacking more difficult:Settings > Touch ID & Passcode > USB Accessories : Off
2. Make sure automatic iOS updates are turned on:Settings > General > Software Update > Automatic Updates : On
3. Set a stronger device passcode;Settings > Touch ID & Passcode > (old passcode) > Change Password > Options > Custom Numeric Code
4. Switch on two-factor authentication;Settings > (your name) > Password & Security > Two-Factor Authentication : On
5. Change your reused passwords -- use your password manager; or if using iCloud Keychain:Settings > Passwords & Accounts > Website & App Passwords > (enter passcode) > (choose site) > Change Password on Website; TC; 2/19/2019
Java
- Wikipedia: Java
- HowStuffWorks: How Java Works; Quiz
JavaScript (JS)
- Wikipedia: JavaScript; JS Security; Virtual machines
- Wikipedia: Cross-site scripting (XSS) enables attackers to inject client-side script into Web pages viewed by other users
- Wikipedia: code injection caused by processing invalid data on server
- Wikipedia: same origin policy if content from one site (such as https://mybank.example1.com) is granted permission to access resources on the system, then any content from that site will share these permissions
- Wikipedia: Cross-site request forgery unauthorized commands are transmitted from a user that the website trusts; previous cookie
- Wikipedia: buffer overflow overwrites adjacent memory -- affecting security and other programs
- Wikipedia: sandbox executes software in a restricted operating system environment, thus controlling the resources accessed (files, etc.)
- JS blockers: Wikipedia: NoScript Firefox; JavaScript Blocker Safari
- How to Block JavaScript on Your iPhone or Android (and When You Should) LH; 10/6/2021
- FSF announces JShelter browser add-on to combat threats from nonfree JavaScript 9/30/2021
macOS
- Best antivirus software for protecting your Mac from viruses and malware MW; 3/4/2024
- Is Apple's Built-in Antivirus Enough XProtect, Gatekeeper; 3rd party? MW; 2/16/2024
- How to know if your Mac has been hacked MW; 12/11/2023
- What to do if you think your Mac has a virus
Bitdefender Virus Scanner; AVG Antivirus for Mac;
Avira Free Security for Mac; MW; 12/5/2023 - New malware strain stealing business data from Intel Macs ApIn; 9/16/2023
- 'Downfall' and Intel Macs: What you need to know about the flaw and fix Macs (from 2015 on) use affected processors,
but it's unclear if they are subject to the attack or not; MW; 8/12/2023 - Complete list of Mac attacks: Every Mac virus, malware and trojan MW; 8/2/2023
- How to Identify and Eliminate Abusive Web Notifications "Website ___ would like to send you notifications in Notification Center" -- Don't Allow;
Safari > Settings > Websites > Notifications > Allow websites to ask for permission to send notifications (deselect)
(similar settings for other browser); TB; 6/26/23 - Macs can get viruses, but do Macs need antivirus software? MW; 6/14/2023
- Help Prevent Evil Maid Attacks & Unknown Tampering of MacBooks with Nail Polish OSXD; 6/4/2023
- Your Mac might not be safe from ransomware for much longer MW; 4/19/2023
- New malware (MacStealer aka "weed") steals Mac passwords incl. credentials and cookies from Firefox, Google Chrome, and Brave browsers;
and also extracts the Keychain database, and other files; ApIn; 3/27/2023 - The best antivirus for Mac is none at all ApIn; 3/18/2023
- ClamXAV review: Basic antivirus protection for an annual price MW; 3/14/2023
- Checking your Mac for viruses. Wait, what? MW; 2/24/2023
- Avira Free Security for Mac review MW; 1/19/2023
- AVG AntiVirus for Mac review: Basic but solid protection for free MW; 12/8/2022
- Study: Almost 50% of macOS malware comes from only one app = MacKeeper; 11/16/2022
- macOS's New XProtect Remediator Now Regularly Scans for Malware
macOS 11 and later; TB; 9/2/2022 - macOS's New XProtect Remediator Now Regularly Scans for Malware
macOS 11 and later; TB; 9/2/2022 - A Single Flaw Broke Every Layer of Security in MacOS Wired; 8/12/2022
- Good Mac security goes beyond antivirus ApIn; 7/22/2022
- CleanMyMac review: Some handy tools but its malware dictation still falls short MW; 7/7/2022
- Macs can get viruses, but do Macs need antivirus software? MW; 6/27/2022
- Mac malware spreading for ~14 months installs backdoor on infected systems
UpdateAgent; Ars; 2/2/2022 - Booby-trapped sites delivered potent new backdoor trojan to macOS users DazleSpy; Ars; 1/25/2022
- CleanMyMac X review: A solid scrubber with hit-or-miss malware removal MW; 8/19/2021
- Malwarebytes Reports on the State of Mac Malware in 2020 TB; 2/19/2021
- Apple Platform Security Guide Reveals Focus on Vertical Integration TB; 2/18/2021
- [2] Mac malware spreads through Xcode projects, abuses WebKit, Data Vault vulnerabilities ZD; 8/14/2020
- New Mac ransomware is even more sinister than it appears ThiefQuest's spyware capabilities: exfiltrate files from an infected computer, search the system for passwords and cryptocurrency wallet data, and run a robust keylogger to grab passwords, credit card numbers, or other financial information as a user types it in; need to install piracted apps; Ars; 7/5/2020
- Malwarebytes: Macs Outpaced PCs in Number of Malware Threats Detected Per Endpoint in 2019, But Most Are Adware MR; 2/11/2020
- Airo Antivirus review: A promising start for a Mac-focused antivirus MW; 2/2/2020
- How to Avoid the Most Popular Mac Malware, 'Shlayer' fake Flash Player download; LH; 1/24/2020
- F-Secure Safe for Mac review: No-frills quality protection MW; 12/4/2019
- How to Install Malwarebytes on Mac to Scan for Malware & Adware Uninstall OSXD; 8/9/2019
- Microsoft is bringing its Defender antivirus software to the Mac Defender Advanced Threat Protection (ATP); for businesses (only?); Verge; 3/21/2019
- [2] Hackers keep trying to get malicious Windows file onto MacOS clever trick may be designed to bypass Gatekeeper protections built into macOS; uses Little Snith Mono framework; Ars; 2/11/2019
- [3] How to Bypass 'Safari no longer supports unsafe extension' Error in Mac OS Mojave OSXD; 2/8/2019
Microsoft Office
- see section: Flash
- Now Microsoft Office is blocking macros by default Verge; 7/22/2022
- How to protect yourself from the new Microsoft Office hack
don't click on risky docs; make sure Protected View is still switched on in Office; PC; 9/9/2021 - An '80s File Format Enabled Stealthy Mac Hacking now-patched vulnerability would have let hackers target Microsoft Office using Symbolic Link, an old file type; Wired; 8/5/2020
- Ex-NSA Hacker Finds a Way to Hack Mac Users Via Microsoft Office now fixed for the latest version of Office on Mac, and for MacOS 10.15.3; MB; 8/5/2020
- G Suite's lack of end-to-end encryption means US agencies could force Google to hand over unreleased reporting, even unpublished info about journalistic sources 10/9/2019
- How Hackers Turn Microsoft Excel's Own Features Against It Wired; 6/27/2019
Ransomware
- Wikipedia: Ransomware: restricts access to the system that it infects, and demands a ransom paid to the creator of the malware in order to remove the restriction.
- No More Ransom! Need Help unlocking your digital life without paying your attackers?
- What experts think companies should do when ransomware strikes NPR; 8/12/2022
- GoodWill ransomware forces victims to donate to the poor and provides financial assistance to patients in need 5/24/2022
- Winning the War on Ransomware
DOJ’s task force; Verge; 12/9/2021 - Ransomware gangs are complaining that other crooks are stealing their ransoms ZD; 9/30/2021
- Why ransomware hackers love a holiday weekend Ars; 9/5/2021
- The history of hacking ransoms and cryptocurrency CNet; 7/30/2021
- How REvil Ransomware Took Out Thousands of Business at Once
automated updates via supply chain network; Wired; 7/4/2021 - Don't Ignore Ransomware. It's Bad.
govt actions; backups; uptodate software;
if companies, government agencies and organizations required all employees and others who access their computer networks
to use strong passwords, password managers and multi-step authentication, it would go a long way to prevent cyberattacks; NYT; 4/29/2021 - How Did ‘Ransomware’ Get So Bad? NYT; 10/5/2020
- When coffee makers are demanding a ransom, you know IoT is screwed watch along as hacked machine grinds, beeps, and spews water; Ars; 9/26/2020
- Ransomware Has Gone Corporate. Where Will It End? the DarkSide operators are just the latest group to adopt a veneer of professionalism—while at the same time escalating the consequences of their attacks; Wired; 8/26/2020
- Researchers detail the increasingly prevalent LockBit ransomware, which may one day reach parity with other feared ransomware packages like Maze or Ryuk Ars; 4/30/2020
- The Covid-19 Pandemic Reveals Ransomware's Long Game hackers laid the groundwork months ago for attacks; Wired; 4/28/2020
- Ransomware Gangs to Stop Attacking Health Orgs During Pandemic BC; 3/18/2020
- Ransomware Attacks Grow, Crippling Cities and Businesses Hackers are locking people out of their networks and demanding big payments to get back in. New data shows just how common and damaging the attacks have become; NYT; 2/9/2020
- Why you can't bank on backups to fight ransomware anymore they still will face demands for payment in order to avoid the publication or sale of information stolen by the attackers before the ransomware was triggered; Ars; 2/7/2020
- New ransomware doesn't just encrypt data. It also meddles with critical infrastructure Ekans represents a "new and deeply concerning" evolution in malware targeting control systems; Ars; 2/3/2020
- Experts: Don't reboot your computer after you've been infected with ransomware Rebooting may lead to restarting a crashed file-encryption process, potential loss of encryption keys stored in-memory; ZD; 11/5/2019
- Profile of Michael Gillespie, who has cracked the encryption of 100+ types of ransomware and helped thousands of ransomware victims recover their files for free ProPub; 10/29/2019
- FBI warns of major ransomware attacks as criminals go "big-game hunting" Ars; 10/7/2019
- How insurance companies are fueling a rise in ransomware attacks Insurers prefer to pay the ransom. Why? ProPublica says attacks are good for business; Ars; 8/27/2019
- Don't Pay the Ransom The F.B.I. should follow the example of European law enforcement and help victims of ransomware decrypt their data; No More Ransom initiative, toolsNYT; 8/14/2019
- Cybersecurity officials warn state and local agencies (again) to fend off ransomware three steps urged by CISA, MS-ISAC, NGA, NASCIO: run daily backups, train staff on "cybersecurity awareness," and "revisit and refine cyber incident response plans"; Ars; 7/30/2019
- No More Ransom project has prevented ransomware profits of at least $108 million 82 tools that can be used to decrypt 109 different types of ransomware; ZD; 7/26/2019
- How to protect yourself from online scams including ransomware and more PC; 7/16/2019
- Georgia's courts hit by ransomware Ryuk; Ars; 7/1/2019
- Florida LAN: Someone clicks link, again, giving Key Biscayne ransomware Ars; 6/28/2019
- Sting Catches Another Ransomware Firm -- Red Mosquito -- Negotiating With "Hackers" rather than high-tech ransomware solutions; PP; 6/24/2019
- A tale of two cities: Why ransomware will just get worse Deal or no deal, either way cities pay through the nose because of failed IT practices; Ars; 6/21/2019
- [2] Zero-day attackers deliver a double dose of ransomware—no clicking required Oracle WebLogic; Ars; 4/30/2019
- Arizona Beverages, one of the largest drink suppliers in the US, is reeling after a ransomware attack FBI warned them beforehand of a malware infection; TC; 4/2/2019
- Here's how personalized ransomware attacks work, and how to protect yourself TNW; 3/28/2019
- New ransomware rakes in $4 million by adopting a "big game hunting" strategy Ryuk lies in wait for as long as a year, then pounces on only the biggest prey; Ars; 1/12/2019
Spyware
- Wikipedia: Spyware: malware that monitors users' web browsing, displays unsolicited advertisements, or redirects affiliate marketing revenues to the spyware creator.
- Wikipedia: Keystroke logging: action of recording (or logging) the keys struck on a keyboard, typically in a covert manner, e.g., passwords
- HowStuffWorks: How Spyware Works; How to Avoid Spyware; How to Scan for and Remove Spyware
- Spyware Maker NSO Promises Reform but Keeps Snooping recent revelations in India show that the threat from the company’s spyware to activists and journalists isn’t limited to autocratic regimes; NYT; 11/9/2019
- Fake veteran hiring site downloads spyware instead of jobs Ars; 9/25/2019
- El Chapo Trial: Kingpin Used Spyware to Obsessively Monitor His Wife and Mistress NYT; 1/10/2019
[3] Web Servers
- Apache, Drupal, Joomla, WordPress, etc.
- Many websites threatened by highly critical code-execution bug in Drupal Drupal is the third most-widely used CMS behind WordPress and Joomla; Ars; 2/21/2019
- How to Run a Web Server on iOS with iSH and python OSXD; 2/20/2019
Windows
- Best antivirus: Keep your Windows PC safe from spyware, Trojans, malware, and more PC; 8/2/2023
- The best antivirus protection CNet; 12/19/2022
- Hackers Are Exploiting a Flaw Microsoft Fixed in 2013
optional update; ZLoader; Wired; 1/5/2022 - AVG Internet Security review much improved interface along with good protection and solid pricing; PC; 2/3/2021
- What you need to know about Windows Security in Windows 10 PC; 1/6/2021
- Windows Security review: There are better options, but not for the 'price' PC; 12/12/2019
- Why you can stop paying for antivirus software Microsoft's Windows Security (formerly Windows Defender) is now on a par with paid solutions such as McAfee and Norton; PC; 9/24/2019
- Why You Should Use Windows Defender's Ransomware Prevention LH; 8/16/2019
- How to remove malware from your Windows PC PC; 5/6/2019
Safer Internet: Connection: Turn Off Unnecessary Services
Safer Internet: Connection: Turn Off Unnecessary Services
Summary | Sys. Prefs | Login Screen | Find My ... |
Location | Camera, etc. | Bluetooth | Notifications | Speech |
References: General | Android | Bluetooth | Camera | iOS | Location |
macOS | Microphone | Notifications | Screens | Video | Windows
Summary
- [1] Review System Preferences to control what information is shared between apps and over the internet
- [1] Add Contact Info to Login ('Lock') Screen -- useful for medical emergency or if device found
- [1] Enable Find My xx to locate, and optionally erase, your lost/stolen device
- [1] Control Access to your Location by apps and sites: maps, local stores, advertisers?
- [1] Control Access to your Computer, Keyboard, Camera, Microphone, Screen by apps and sites
- [1] Limit Bluetooth Access, e.g., to known contacts only, esp. with AirDrop
- [2] Control System and App Notifications
- [2] Control Sharing of Speech & Analytics Data, e.g., Siri, Alexa; app crashes
- Later sections: Internet of Things (SmartTVs; Game boxes; Amazon Alexa, Apple Siri, Google Home); Share Files Privately
- References
[1] Review System Preferences
- Besides exploring every option under Preferences / Settings, you can use Search
- macOS:
System Preferences > Security & Privacy > Privacy : Location Services, Contacts, Calendars, Reminders, Accessibility, Diagnostics & Usage[screenshot] - macOS:
System Preferences > Sharing : Screen, Files, Printer, Remote, Internet, Bluetooth[screenshot] - macOS:
System Preferences > Extensions : All, Actions, Finder, Photos Editing, Share Menu, Today - iOS:
Settings > Privacy : (many)[screenshot] - iOS:
Settings > General > Restrictions: (many) - Windows: (File Sharing) {Figure 7. TCYOP-4: 72; TCYOP-3: 59}
[1] Add Contact Info to Login ('Lock') Screen
- macOS:
System Preferences > Security & Privacy > General (lock message)[screenshot]  iPhone:
iPhone: Health > Medical ID: Medical Conditions, Spouse, Child, Blood Type, Organ Donor- result: "Emergency" link on lock screen
- iOS: add a message to your Lock Screen by overlaying text* on an image
- You can also set this (or a different) image as your Home Screen (background for app icons).
- iOS:
Settings > Wallpaper > Choose a New Wallpaper > Camera Roll >[screenshot] - ... (tap lock image)
> (iPhone:Set) > Set Lock Screen - ... (tap home image)
> (iPhone:Set) > Set Home Screen - *[2] Use an image app on desktop or iOS to add text to an image; tradeoffs: cost, simplicity, flexibility.
- e.g., use Preview on Mac to create 2 appropriately-sized images: one for use with Home Screen, one with text for Lock Screen
- macOS:
Finder > (select original image) > File > Duplicate; rename with suffix, e.g., 'home' - macOS:
Preview > File > Open: 'home' image, e.g., my-ipad-screen-home.jpg - Preview: use rectangular selection tool to highlight a square area corresponding to device's smaller dimension
- e.g., iPad Air: 2048x2048, iPhone 7: 750x750; square wallpaper will work with both portrait and landscape screen orientations
- macOS:
Preview > Tools > Crop; File > Save - macOS:
Finder > (select 'home' image) > File > Duplicate; rename with suffix, e.g., 'lock' - macOS:
Preview > File > Open: 'lock' image, e.g., my-ipad-screen-lock.jpg - macOS:
Preview > Tools > Annotate > Text - add text, e.g., name, email, phone: yours(iPad), spouse(iPhone); customize font, size, etc.
- macOS:
Preview > File > Save - transfer lock (& home) image file(s) to Photos (iOS) via AirPlay, Messages, Mail, ...
- set wallpaper(s) -- per earlier instructions
- iOS:
Settings > Control Center > Access on Lock ScreenIf on, someone would be able to enable Airplane Mode on a lost/stolen phone, which would disable Find My iPhone - iOS:
Settings > Passcode (or Touch ID & Passcode) > Allow access when locked: Notifications, Siri, Wallet, etc.[screenshot]
[1] Enable Find My iPhone, iPad, Mac, Windows
- To use: login to iCloud account
- macOS:
System Preferences > iCloud > Find My Mac[screenshot] - iOS:
Settings > (my acct) > iCloud > Find My iPad/iPhone[screenshot] - [2] iOS:
Settings > Privacy > Location Services > System Services > Status Bar Icon: offIf your phone is lost/stolen, and you're tracking it, it's better not to advertise it, though this turns off for all location services? - Windows:
Windows Settings > Update & Security > Find my Device - Windows iCloud setup for iOS devices
[1] Control Access to your Location
- Before
- And:
Settings > Security & Location > Location > App-Level Permissions: on, off - macOS:
System Preferences > Security & Privacy > Privacy : Location Services[screenshot] - macOS:
... Location Services > System Services > Details > Show location icon in menu bar when System Services request your location - macOS:
Safari > Preferences > Privacy > Website use of Location Services[screenshot] - macOS:
Firefox -- none? - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Content Settings > Location - iOS:
Settings > Privacy : Location Services: Share My Location; Apps; System Serviceschoices: Never, Always, While Using [screenshot] - iOS:
Settings > (your acct) > iCloud > Share My Location - After: allow/deny for specific web sites that request access on an adhoc basis
[1] Control Access to your Computer, Keyboard, Camera, Microphone, Screen
- An entrepreneur has made a device that can prevent the NSA from spying on you by blocking your laptop's camera. This new high-tech device is...
- Avoid snooping on your keyboard and screen over your shoulder in public places; control remote access
- macOS:
System Preferences > Security & Privacy > Privacy > Accessibility > Allow apps to control your computer[screenshot] - macOS:
System Preferences > Sharing > Screen Sharing; Remote Login[screenshot] - macOS:
System Preferences > Security & Privacy > Privacy > Camera
older versions: use a piece of cardboard & tape except for specific apps! - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Content Settings > Mouse cursor; Media (camera, microphone) - iOS:
Settings > Privacy > Microphone, Camera, Motion[screenshot] - iOS:
Settings > Safari > Camera & Microphone Access - Windows:
Windows Settings > System > Remote Desktop
[1] Limit Access to Bluetooth
- a wireless technology standard for exchanging data over short distances between "paired" devices, e.g., for keyboard, headset, AirDrop (file sharing), share Internet connection
- range: 30-300' depending on device power Class and environmental factors
- most modern devices and implementations support encryption
- however, if you enable only temporarily when you need it, your device will be more secure, use less power, etc.
- macOS:
System Preferences > Bluetooth > Turn Bluetooth: On/Off[screenshot] - iOS:
[swipe up] > AirPlay - iOS:
General > AirDrop: Contacts Only-- or Receiving Off; if Everyone then just temporarily - iOS:
Settings > Bluetooth: On/Off[screenshot] -- note: disabling via iOS11 Control Center does not completely turn off!
[2] Control System and App Notifications
- Messages that appear in the 'Notification Center' can be useful vs. annoying
- risk if someone sees screen, e.g., verification codes via SMS; allow/deny for web sites that request access?
- macOS:
System Preferences > Notifications[screenshot] - macOS:
Safari > Preferences > Websites > Notifications: Allow websites to ask for permission to send push notifications - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Content Settings > Notifications - iOS:
Settings > Notifications[screenshot] - iOS:
Settings > Notifications > Show Previews > When Unlocked - Windows:
Windows Settings > System > Notifications & Actions
[2] Control Sharing of Speech & Analytics Data
- Collecting data about crashes and usage of services can improve system services and applications
- Is it anonymized? Read privacy policies
- iOS:
Settings > General > Siri > About Siri and Privacy (read) - Dictation online: spoken words are recorded and uploaded to Apple's servers for translation
- Enhanced (offline) mode more private but requires software install
- macOS:
System Preferences > Dictation & Speech > Dictation > Use Enhanced Dictation - iOS:
Settings > Privacy > iPad/iPhone Analytics: [none/all] Share iPad Analytics (with Apple), Share With App Developers, Share iCloud Analytics (with Apple) - macOS:
System Preferences > Security&Privacy > Privacy > Analytics: [select] Share Mac Analytics (with Apple), Share with App Developers, Share iCloud Analytics (with Apple)
References
- {TCYOP-4: 72-73; TCYOP-3: 59-60}
- sections: Refs: Android; Bluetooth; Camera; iOS; Location; macOS; Microphone; Notifications; Screens; Video; Windows
- see also VPN section (for hiding location), Mobile Privacy section
- topics: AirDrop, Alexa, autoplay, geofencing, maps, Medical ID, photos, Siri, tape
- Wikipedia: Location-based service; Geo-fence; Find My iPhone/Mac
- HowStuffWorks: How Location Tracking Works
- The Best Thing About Apple's AirTags Is Also the Scariest abusers installing unwanted trackers; Giz; 4/30/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing; DuckDuckGo for Search; OsmAnd for Maps (OpenStreetMap); ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020
- macOS systems abused in DDoS attacks Apple Remote Desktop enabled; ZD; 10/3/2019
- Researcher: devices can be tracked across apps and sites with info from sensors like gyroscope patched on iOS; a minor issue on Android, given poor calibration; ZD; 5/22/2019
- iOS 12.2 will be able to block Web access to your iPhone's motion sensors ad agencies are reportedly worried about the change; ApIn; 2/4/2019
Android
- Google: Choose which apps use your Android device's location
- More than 1,000 Android apps harvest data even after you deny permissions e.g., location; CNet; 7/8/2019
- Here's the easiest way to find, lock, or wipe your lost Android phone TNW; 7/1/2019
- How to stop location tracking Verge; 4/12/2019
Bluetooth
- Wikipedia: Bluetooth; Bluetooth Security
- HowStuffworks: How Bluetooth Works; How Bluetooth Surveillance Works
- Thieves Are Using Bluetooth to Target Vehicle Break-Ins How to keep your devices safe when you park at a trailhead -- or anywhere; power off or Airplane mode; Out; 12/9/2019
- New Attack exploiting serious Bluetooth weakness can intercept sensitive data Key Negotiation of Bluetooth (KNOB) forces devices to use encryption keys that are trivial to break; attacker within 10-400m; Ars; 8/17/2019
Camera
- Can Someone Really Spy on Me Through My Webcam or Phone Camera? LH; 12/16/2021
- How to Stop Apps from Using Camera on Mac OSXD; 7/11/2019
iOS
- Apple: Privacy: Siri and Dictation; Maps; Health
- Apple: iOS Security Network security pp. 27-30; 9/2015
- Apple: iOS: Supported Bluetooth profiles 3/5/2015
- Jamf's Quick Guide to Which iOS Permissions Apps Really Need TB; 8/26/2021
- How to Manage Which Apps Access Location Data on iPhone & iPad OSXD; 12/29/2020
- How to set up Medical ID on your iPhone MW; 10/21/2020
- Double-Check Your iPhone's Medical ID Emergency Contacts TB; 2/18/2020
- Stop AirDrop in iOS with Screen Time MW; 2/13/2020
- How to See & Change What Apps Can Access Health Data on iPhone OSXD; 1/30/2020
- What is the Screen Time Passcode in iOS 12? OSXD; 3/30/2019
Location
- How to find, block, and disable an unknown AirTag moving with you MW; 5/2/2023
- How to Make Sure You're Not Accidentally Sharing Your Location Wired; 2/12/2023
- How the Find My App Became an Accidental Friendship Fixture
introduced 10 years ago, the app has slowly become a popular way to keep track of friends.
But it comes with considerable privacy concerns; NYT; 8/20/2022 - Your Phone's Location Access Reveals a Lot. Here's How to Turn It Off. NYT; 6/29/2022
- How to find, block, and disable an unknown AirTag moving with you MW; 5/1/2022
- Can Controlling Vehicles Make Streets Safer and More Climate Friendly?
geofencing, Sweden; NYT; 3/28/2022 - How to Hide / Blur Your Home on Google Maps & Apple Maps OSXD; 3/1/2022
- How to find, block, and disable an unknown AirTag moving with you MW; 2/18/2022
- How to find, block, and disable an unknown AirTag moving with you MW; 2/11/2022
- An update on AirTag and unwanted tracking Apple; 2/10/2022
- Apple's New 'Personal Safety Guide' Helps You Deal With AirTag Stalkers Giz; 1/25/2022
- Are Apple AirTags Being Used to Track People and Steal Cars? NYT; 12/30/2021
- What to do when you find an AirTag, or are told by your iPhone that one is following you ApIn; 12/20/2021
- Life360 Family Tracking App Is Selling Its Customers’ Precise Location Data TB; 12/15/2021
- How to opt out of the Find My network
participating in Apple’s crowdsourced network for devices and AirTags is optional; MW; 5/28/2021 - Six Reasons Why Google Maps Is the Creepiest App On Your Phone
1. Google Maps Wants Your Search History
2. Google Maps Limits Its Features If You Don't Share Your Search History
3. Google Maps Can Snitch On You
4. Google Maps Wants to Know Your Habits
5. Google Maps Doesn't Like It When You're Offline
6. Google Makes It Seem Like This Is All for Your Own Good;
Vice; 11/12/2020 - What are geofence warrants? TNW; 9/5/2020
- Beware of find-my-phone, Wi-Fi, and Bluetooth, NSA tells mobile users plus ad tracking; Ars; 8/4/2020
- How to Remove Location Data from Photos Before Sharing on iPhone & iPad OSXD; 5/29/2020
- How to Find a Lost iPhone, iPad, Mac with FindMy on Mac OSXD; 11/25/2019
- Find My: How to use Apple's new all-in-one app to find friends and devices MW; 10/14/2019
- How to Set Your Google Data to Self-Destruct
option to set search and location data to automatically disappear after a certain time;
myactivity.google.com; NYT; 10/2/2019 - How Incognito Google Maps Protects You -- and How It Doesn't Wired; 10/2/2019
- How to Disable Location Based Apple Ads on Mac OSXD; 8/30/2019
- Researchers find that in four dating apps, including Grindr, any user's location can be determined using the apps' public APIs, if the username is known 8/12/2019
- The Terrible Anxiety of Location Sharing Apps Wired; 7/28/2019
- EFF Hits AT&T With Lawsuit Over Sale Of User Location Data TD; 7/16/2019
- Secret Palantir User Manual Sheds Light on How ICE and Law Enforcement Track Families Vice; 7/12/2019
- How Apple's New Find My Service Locates Missing Hardware That's Offline TB; 6/21/2019
- iOS 13 will show you where apps have tracked your location, on a map TNW; 6/10/2019
- [2] The Clever Cryptography Behind Apple's 'Find My' Feature Wired; 6/5/2019
- Study: many iOS apps, including the Washington Post's, use "background app refresh" to send tracking info like location and IP address, even late at night Our privacy experiment showed 5,400 hidden app trackers guzzled our data — in a single week; WaPo; 5/28/2019
- Google Is Probably Tracking Your Location Right Now -- Here's How to Stop That MF; 5/5/2019
- How to Return a Lost Phone Contact Info (on case; ICE (in case of emergency); Voice Assistant; NYT; 4/24/2019
- Tracking Phones, Google Is a Dragnet for the Police NYT; 4/13/2019
- Google's Sensorvault Is a Boon for Law Enforcement this Is How It Works; NYT; 4/13/2019
- The Chicken Is Local, But Was It Happy? GPS Now Tells The Life Story Of Your Poultry NPR; 2/24/2019
- Your phone and TV are tracking you, and political campaigns are listening in 'digital fence' pushed ads onto the iPhones and Androids of all those attending the meeting. Not only that, but because the technology pulled the unique identification numbers off the phones, a data broker could also use the digital signatures to follow the devices home. Once there, the campaign could use so-called cross-device tracking technology to find associated laptops, desktops and other devices to push even more ads; possible solutions? VPN, ad blocking, app settings (or safer apps), TV settings; LAT; 2/20/2019
- How to stop Facebook from tracking your location And, iOS; TNW; 2/21/2019
- Apple, Google Criticized For Carrying App That Lets Saudi Men Track Their Wives Absher, an app from the Saudi government, helps men in the country track and dictate where women can travel; Sen. Ron Wyden, D-Ore., sent a letter to both companies asking them to remove the app; NPR; 2/12/2019
- 'Find my iPhone' warned murder victim of assailant's location minutes before death she was shot to death, but it gave her enough time to save her son; ApIn; 2/6/2019
- How to Change IP Address & GeoLocation for Web Browsing with Epic OSXD; 1/30/2019
- AT&T and T-Mobile say they will stop selling customers' location data to 3rd-party service providers by March; Verizon says it's winding down sharing agreements WaPo; 1/10/2019
- Los Angeles sues the company behind the Weather Channel app, which is owned by IBM, for slyly using location data for commercial purposes NYT; 1/3/2019
macOS
- How to find out which Mac apps are tracking your location MW; 6/14/2021
- How to Prevent Microphone & Camera Access for Websites in Safari on Mac OSXD; 4/22/2021
- Feeling Paranoid? Micro Snitch Tells You If Your Mac Is Spying on You TB; 7/22/2020
- How to Delete Siri & Dictation History on Mac and Opt-Out of Audio Recording Storage OSXD; 11/21/2019
- Apple's AirDrop and password sharing features can leak iPhone numbers AirDrop: Contacts Only? disable Bluetooth? Ars; 8/1/2019
- Best Mac remote access apps MW; 7/4/2019
- Know When Malware Tries to Access Your Mac's Camera or Mic With This App Oversight; LH; 3/9/2019
Microphone
Notifications
- How to Take Control of Your Notifications NYT; 2/5/2020
Screens
- The Sometimes Catastrophic, but Mostly Just Embarrassing Consequences of Screen Sharing at Work NYT; 3/21/2019
- How to Not Ruin Your Life (or Just Die of Embarrassment) With a Screen Share NYT; 3/21/2019
Video
- Apple says it has notified app developers to remove code that lets them record how a user interacts with their apps without explicit user consent Glassbox 'session replay' records taps, button pushes and keyboard entry; TC; 2/7/2019
- Microsoft introduces background blur feature to Skype, which uses AI to detect the user's hair, hands, and arms, and blur distracting objects in the background Giz; 2/7/2019
Windows
Safer Internet: Connection: Use a Firewall
Safer Internet: Connection: Use a Firewall
Summary | Built-in Software | Block Ports | Other Software |
References: General | macOS | Windows
Summary
- Routers typically provide some hardware firewall protection, plus a layer of anonymity.
- [1] Enable your device's built-in software firewall; default (mostly inbound) settings are usually adequate
- [2] Block/unblock specific ports/services via router or OS, e.g., if you're a gamer or server admin
- [3] Install 3rd party software for more advanced inbound and/or outbound firewall
- References
[1] Enable your device's built-in software firewall
- iOS: not necessary
- macOS:
System Preferences > Security & Privacy > Firewall > Turn On
[screenshot] you'll need to click the lock and provide your admin password - macOS: {Figure 9. TCYOP-4: 76; TCYOP-3: 62}; Win: {Figure 8. TCYOP-4: 75; TCYOP-3: 61}
[2] Block/unblock specific ports/services
- macOS:
System Preferences > Security & Privacy > Firewall > Firewall Options[screenshot]
[3] Install 3rd party software
- Install 3rd party software for more advanced inbound and/or outbound firewall {TCYOP-4: 66}
- macOS: Little Snitch; Lulu; others: Intego NetBarrier; Murus; Norton Security; Radio Silence
- macOS: access secondary built-in firewall pf via Terminal, or GUI: Murus
- Windows: ZoneAlarm; Windows 8 Firewall Control
References
- {TCYOP-4: 74-77; TCYOP-3: 61-63; Use an Outbound Firewall; Beware Analog Snooping, Too}
- sections: Refs: macOS, Windows
- Wikipedia: Firewall controls incoming and outgoing network traffic; router
- Wikipedia: Firewalls and Internet security; Personal firewall
- HowStuffWorks: How Firewalls Work
macOS
- Apple: firewall
- Little Snitch 5.7 TB; 8/24/2023
- How to Enable or Disable Firewall on MacOS Ventura OSXD; 5/17/2023
- Apple has removed a controversial feature in macOS 11.2 beta 2 that allowed its own apps to bypass third-party firewalls, security tools, and VPNs ZD; 1/14/2021
Win
- Wikipedia: Windows firewall
Safer Internet: Connection: Crossword #1
Safer Internet: Connection: Crossword #1
The Puzzle
 Interactive version [below]
Interactive version [below]
Check button: Check puzzle for errors; Reveal button: reveal current word
Web version created by Crossword Compiler Print versions [.pdf]: puzzle; solution
Print versions [.pdf]: puzzle; solution Download for a crossword app [.puz]: puzzle w/ solution
Download for a crossword app [.puz]: puzzle w/ solution
open it in a crossword app, e.g., Mac, Windows: Across Lite (free); Android, iOS: Crosswords
Safer Internet: Connection: Crossword #2
Safer Internet: Connection: Crossword #2
The Puzzle
 Interactive version [below]
Interactive version [below]
Check button: check puzzle for errors; Reveal button: reveal current word
Web version created by Crossword Compiler Print versions [.pdf]: puzzle; solution
Print versions [.pdf]: puzzle; solution Download for a crossword app [.puz]: puzzle w/ solution
Download for a crossword app [.puz]: puzzle w/ solution
open it in a crossword app, e.g., Mac, Windows: Across Lite (free); Android, iOS: Crosswords
Safer Internet: Browse the Web Privately
Safer Internet: Browse the Web Privately
Quotes | Summary |
References: General | Chrome (Google) | Crosswords | DuckDuckGo |
Edge, Internet Explorer (Microsoft) | Firefox (Mozilla) | Opera | Safari (Apple)
 Quotes
Quotes
- "The Internet 'browser' is the...
- Internet Explorer is the #1 browser...
- "The ten thousand things
How long do any persist?
Netscape, too, has gone.
Server’s poor response
Not quick enough for browser.
Timed out, plum blossom." ~Haiku error messages
Summary
- Although these next sections are primarily about web browsers, keep in mind that the advice also applies to any application, esp. mobile, that accesses the network
- [1] Go to the right site, e.g., email links vs. bookmarks / password manager
- [1] Use HTTPS (addresses) for sending login or sensitive info to sites
- [1] Manage Local Storage of Private Data: cookies, history, private browsing
- [1] Block ads and tracking via browser extensions such as AdBlock Plus and Ghostery
- [1] Keep sensitive data in a password manager; use 2-Factor Authentication
- [1] Search privately: try other search engines, e.g., DuckDuckGo or StartPage instead of Google or Bing
- [2] Browse anonymously; Censorship; NSA; Tor
- [2] Shop privately
- It's a good idea to have a second browser (e.g., Firefox) handy when your default browser (e.g., Safari, Edge) 'misbehaves' with certain sites, or no longer receives security updates (e.g., ancient OS)
- macOS:
Safari > Preferences > Advanced > Show Develop menu in menu bar-- sets up access to 2nd browser; later... - macOS:
Safari > Develop > Open Page With > (other browser) - Some browsers provide more privacy than others {TCYOP-4: 77}:
- worse: Chrome; Internet Explorer
- good: Firefox; Safari; Tor
- better: Brave; Comodo Dragon and IceDragon (Windows); Epic
- Travel Back to 1990 With the Original World Wide Web Browser: no images, JavaScript, etc.;
Internet Timeline: in 2019, 50 years for Internet, ~30 for World Wide Web
References
- {TCYOP-4: 78-109; TCYOP-3: 64-68; Understand the Privacy Risks of Web Browsing: On Your Device, In Transit, On a Web Server}
- sections: Refs: Chrome (Google); Crosswords; Edge, Internet Explorer (Microsoft); Firefox (Mozilla); Opera; Safari (Apple)
- oldweb.today visit past web sites for different browsers, OS
- Cover Your Tracks analyze how well your browser and add-ons protect you against online tracking techniques. check if your system is uniquely configured -- and thus identifiable -- even if you are using privacy-protective software
- Wikipedia: web page; web site; web server; web browser; Comparison of web browsers; mobile app
- HowStuffWorks: What's the difference between the Internet and the World Wide Web?
- HowStuffWorks: How Web Pages Work; Quiz; How Web Servers Work; Quiz
- HowStuffWorks: How do I create my own Web site?
- HowStuffWorks: Can the government see what Web sites I visit?
- Ethical.net: Browsers; Browser extensions
- Best Privacy Browsers (2024): Brave, Safari, Ghostery, Firefox, DuckDuckGo Wired; 4/6/2024
- Your Browser Has a Hidden Setting That Will Speed Up the Web Giz; 12/9/2023
- How to Switch Browsers Without Losing Your Bookmarks and Passwords Wired; 7/30/2023
- Arc Will Change the Way You Work on the Web TB; 5/1/2023
- Browse the Web Without CSS, JS, or Images with the Kristall Browser OSXD; 2/18/2023
- Download This App If You Use Multiple Browsers on Your Mac Velja; LH; 2/7/2023
- Tor Browser for Apple Silicon Macs is Now Available OSXD; 12/17/2022
- Best web browser for Mac MW; 12/16/2022
- How to Make Your Web Browser as Secure as Possible Giz; 7/15/2022
- How to Navigate Away From a Website That Disabled the 'Back' Button
hold down Back button for site menu; LH; 6/16/2022 - This Browser Can Use Chrome and Firefox Extensions at the Same Time
Orion is based on WebKit and claims to be privacy-focused; LH; 6/9/2022 - Steps to Simple Online Security: 9: Secure Your Web Browser NYT; 4/15/2022
- The Fastest Browsers on Windows (and the Downsides of Each) LH; 3/15/2022
- Apple, Google, Microsoft, and Mozilla create Interop 2022, a browser benchmark
to resolve compatibility issues identified by web developers in 15 specifications; Reg; 3/4/2022 - Google and Mozilla are ready for Chrome and Firefox version 100 to break some websites
User-Agent parsing libraries for 2- vs. 3-digit numbers; Verge; 2/17/2022 - Harken back to the late 1990s with this re-creation of the dialup Internet experience
what happens when you try to visit modern websites using Windows 98; Ars; 1/14/2022 - Browse the Web from Your Wrist with µBrowser
Apple Watch; limited functionality; TB; 12/12/2021 - 6 of the Best Internet Browsers for Protecting Your Privacy
settings: ad-tracking, third-party cookies, and fingerprinting;
Firefox, Brave, Safari, Microsoft Edge, DuckDuckGo Privacy Browser, Tor;
LH; 9/8/2021 - If You Care About Privacy, It’s Time to Try a New Web Browser Firefox Focus, DuckDuckGo,j Brave; NYT; 3/31/2021
- Google and Microsoft team up to fix compatibility issues between browsers cross-browser effort called #Compat2021; Eng; 3/23/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing; DuckDuckGo for Search; OsmAnd for Maps; ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020
- How to Run Alternative Browsers on Your Chromebook Linux (Beta): Firefox, Vivaldi; or Android Play Store; Giz; 11/6/2020
- How to Change Your Default Browser on iOS/iPadOS iOS14; LH; 9/14/2020
- Hidden Browser Games Easter Eggs; Chrome: dinosaur game, Edge: surfing, Firefox: unicorn pong; 9/12/2020
- How to Wipe Your Viewing History on Any Streaming Service Giz; 7/13/2020
- This tiny game runs directly in your browser's title bar -- and it's kinda fun How to save web articles for reading at a later time MW; 6/5/2020
- How to Unlock Hidden Browser Games in Edge, Firefox and Chrome
edge://surf;chrome://dino; LH; 5/27/2020 - Vivaldi browser gets built-in options to block ads and tracking with a blocklist powered by DuckDuckGo's Tracker Radar, and comes out of beta on Android; TC; 4/22/2020
- Best web browser: Chrome, Edge, Firefox, and Opera go head-to-head PC; 4/17/2020
- Study ranks the privacy of major browsers Ars; 3/17/2020
- How to Add a Website to Home Screen of iPhone & iPad in iOS 13 (share icon) > Add to Home Screen; OSXD; 2/26/2020
- How your browser protects your privacy Brave, Chrome, Edge, Firefox, Safari, Vivaldi; Verge; 2/20/2020
- Tired of Web Sites Blocking Standard Browser Controls? StopTheMadness! extension; TB; 2/17/2020
- The Fractured Future of Browser Privacy Better anti-tracking measures have become the norm for Chrome, Firefox, Safari, and other modern browsers. But they still disagree on how exactly they should work; Wired; 1/30/2020
- Why Your Web Browser is Running Slowly and How to Fix It Giz; 10/25/2019
- Before Netscape: The forgotten Web browsers of the early 1990s WorldWideWeb, Erwise, ViolaWWW, Midas, Samba, Mosaic, Lynx, Cello; Ars; 5/26/2019
- Travel Back to 1990 With the Original World Wide Web Browser worldwideweb.cern.ch; Giz; 2/19/2019
Chrome: Google
- Wikipedia: Chrome
- Google: desktop, mobile
- How to Update Chrome also: Chrome > About
- 9 Ways to Make Google Chrome Safer and More Private LH; 11/7/2023
- Sunsetting support for Windows 7 / 8/8.1 in early 2023 Google; 10/27/2022
- 9 Default Chrome Settings You Should Change If You Care About Your Privacy LH; 2/22/2022
- Chrome 88 lays Flash and FTP to rest end of two eras; PC; 1/20/2021
- Google Chrome sucks -- here's why you should stop using it TNW; 1/2/2021
- Google launches Chrome 86 with stronger password protections on iOS and Android, VP9 video codec for macOS Big Sur 10/6/2020
- How to make your cheap Chromebook look and feel like a high-priced MacBook MW; 9/8/2020
- Quit Chrome. Safari and Edge Are Just Better Browsers for You and Your Computer. switch from Google’s browser to one from Apple or Microsoft, and you’ll notice immediate improvements in performance, battery and privacy; WSJ; 7/12/2020
- Google Chrome Is Getting a Bunch of New Privacy Features Wired; 5/27/2020
- Google launches Chrome 83 with updated safety and privacy settings, third-party cookies blocked in Incognito mode, DNS-over-HTTPS support, and new dev features Verge; 5/19/2020
- Chrome 81 arrives with Web NFC Origin Trial, AR features, and mixed images autoupgraded to HTTPS 4/7/2020
- Google Chrome will block insecure downloads in coming months Verge; 2/10/2020
- I finally switched from Chrome to Mozilla Firefox -- and you should too 1/11/2020
- Chrome rolls out new protections preventing password and data theft Site isolation debuts in Android Chrome while desktop versions extend it to new fronts; Ars; 10/17/2019
Crosswords
- Steve: Browsing
- Crossword: Safer Internet Day (Feb 5) about safety generally, not internet; NYT Archive: Monthly Bonus; Feb 2019
- Cyberspace cryptic crossword Internet-and-computer-themed; browser, pdf; 3/2019
- Solve the Internet (index): article We're Launching a weekly Crossword Puzzle About the Internet; 1st puzzle: MB; June 6, 2018
- NYT Learning Network: Internet Safety .puz; 5/15/2003; Social Media 11/7/2011
- Misc.: Internet Safety; Protecting Internet Privacy
DuckDuckGo
- The Best Privacy Features in DuckDuckGo's New Web Browser LH; 10/18/2022
- DuckDuckGo is building a privacy-first desktop browser for macOS
based on Apple WebKit; MW; 12/21/2021
Edge: Microsoft
- Wikipedia: Edge; Internet Explorer
- Microsoft: Edge; Internet Explorer
- The Most Annoying Microsoft Edge Features Everyone Should Disable LH; 8/8/2022
- Even in Death, Internet Explorer Lives On in South Korea NYT; 7/8/2022
- 5 ways Microsoft Edge is better than Chrome PC; 6/16/2022
- Internet Explorer Is Shutting Down in a Burst of Nostalgia NYT; 6/15/2022
- How to Change Your Web Browser in Windows 11 (It's Not Easy) Wired; 10/6/2021
- Internet Explorer, The Love-To-Hate-It Web Browser, Will Die Next Year NPR; 5/22/2021
- Why Microsoft has blocked hundreds of sites in Internet Explorer Microsoft is 'encouraging' users to abandon Microsoft's legacy browser and adopt Edge instead; how to enable Internet Explorer Mode within Edge; PC; 10/29/2020
- Why Your Edge Browser Installed Microsoft Office Without Asking LH; 10/15/2020
- Porn surfers have a dirty secret. They’re using Internet Explorer -- and Flash Ars; 9/12/2020
- Microsoft is using ransomware-like tactics to force-feed its new Chromium Edge browser to users through an automatic Windows update Verge; 7/2/2020
- Why Microsoft's new Edge could eventually win the browser wars convenience, compatibility w/ Chrome; PC; 2/11/2020
- Microsoft says it will fix an Internet Explorer security bug under active attack TC; 1/18/2020
- Microsoft's Chromium Edge browser now available on Windows 7 and Windows 8 Verge; 6/19/2019
- Microsoft really doesn't want you to use Internet Explorer anymore Microsoft calls it a compatibility solution, not a browser; Verge; 2/8/2019
- Internet Explorer 10 termination set for January 2020 Reg; 1/29/2019
Firefox: Mozilla
- Wikipedia: Firefox
- Mozilla: Firefox
- How to Download Firefox
- Tor Browser -- based on Firefox
- for older Macs: TenFour Fox Power PC Mac (G3,G4,G5 processors); OS X 10.4-10.5; forked from Mozilla Firefox 38; Classila Mac OS 8.6-9.2.2 (and compatible with 10.1.5-10.3.9); not actively maintained?
- Firefox 95 TB; 12/10/2021
- PowerPC fork of Firefox that lasted for over a decade has reached the end of the road
TenFourFox; Ars; 10/14/2021 - Firefox 91 TB; 8/16/2021
- An endangered internet species: Firefox even with another infusion of cash from Google, you have to wonder just how long Firefox will survive as a viable, mainstream web browser; ZD; 8/14/2020
- Firefox 78 last release that will support macOS 10.9 Mavericks, 10.10 Yosemite, and 10.11 El Capitan; TB; 7/3/2020
- The Firefox 76 password manager now tells you when you use leaked passwords Firefox Lockwise; Firefox Monitor: checks whether a website has suffered a security breach; ZD; 5/5/2020
- How to Disable Firefox 75's New Address Bar LH; 4/7/2020
- Firefox 75 overhauls the browser's address bar Ars; 4/7/2020
- Firefox 72.0 TB; 1/8/2020
- Tweak These Firefox Settings to Power Up Your Browsing
1. Restore previous session;
2. Reach your favorite features quickly;
3. Forget what just happened;
4. Customize the new tab page;
5. Share large, encrypted files;
6. Add tags to your bookmarks;
7. Clean up your view of a page;
8. See if you're affected by data breaches: Firefox Monitor;
9. Save articles to read later;
10. See how Firefox is protecting you (Privacy Protections);
11. Lock down website permissions;
12. Take back control of your tabs;
13. Manage multiple accounts more easily;
14. Give Firefox a refresh (reset except for bookmarks and passwords); Wired; 12/22/2019 - Firefox 70 brings Enhanced Tracking Protection and longer battery life Ars; 10/23/2019
- Firefox 67 arrives with faster performance and enhanced Private Browsing features PC; 5/21/2019
Opera
- Wikipedia: Opera
- Opera: desktop, mobile
- Opera 64 desktop browser launches with inbuilt tracking protection using the EasyPrivacy Tracking Protection List a powerful screenshot tool, and more; Eng; 10/8/2019
- Opera Reborn 3: No modern browser is perfect, but this may be as close as it gets while not as innovative as its mobile brethren, new release closes the gap with Vivaldi; Ars; 5/19/2019
Safari: Apple
- Wikipedia: Safari
- Apple (macOS): Safari (apple) > App Store > Updates
- Safari alternatives: Five Mac web browsers worth trying Chrome, Firefox, Opera, Edge, Brave; MW; 12/16/2022
- Five reasons why you might want to try out another browser on your Mac
You use mostly Google apps and services;
You want to customize your browser;
You're a web developer;
You value your privacy (a lot);
You use more than just Apple devices;
MW; 8/28/2022 - Essential Safari tips to help you browse smarter and faster on your Mac MW; 2/24/2022
- Safari and iOS users: Your browsing activity is being leaked in real time Ars; 1/18/2022
- Apple's Safari browser runs the risk of becoming the new Internet Explorer -- holding the web back for everyone
WebKit engine is well behind the competition; Reg; 10/22/2021 - 13 Safari Settings You Should Change to Make It a Better Browser
View > Show Status Bar
Preferences > Advanced > Show full website address
Preferences > Advanced > Show Develop menu in menu bar
Develop > Show Page Source
Preferences > Websites > Auto-Play
Preferences > Websites > Camera, Microphone, Screen Sharing, Location
Preferences > Websites > Reader
Preferences > Websites > Notifications
Preferences > Advanced > Never use font sizes smaller than
Preferences > Search > Search engine
Bookmarks > Show Start Page (customize)
Preferences > Tabs (and kbd shortcuts)
Safari > Safari Extensions
LH; 7/6/2021 - The Safari Settings You Should Tweak Right Now macOS, iOS;
1. Run a password audit (if not using password manager);
2. Pop out videos (picture in picture);
3. Set permissions for each website;
4. Brighten up your browsing with favicons;
5. Tidy up after yourself (remove history items);
6. Show the full URLs of websites;
7. Know your keyboard shortcuts;
8. Control Safari with your voice;
9. Give yourself more options (Develop menu);
10. Clear out the cache;
11. Split the display;
12. Find open tabs on your other devices;
13. Build up your reading list;
14. Customize your toolbar; Wired; 12/8/2019 - WebKit's new anti-tracking policy puts privacy on a par with security TC; 8/15/2019
- How to Handoff Safari from iPhone to iPad and Vice Versa OSXD; 4/10/2019
- The web at 30: Apple's place in history MW; 3/13/2019
- The 7 best free Safari extensions for the Mac MW; 2/14/2019
Safer Internet: Browsing: Go to the Correct Site
Safer Internet: Browsing: Go to the Correct Site
Quotes | Summary | Navigating | Malicious | Fraudulent Warnings |
URL status | Shortened URLs | Web Archives |
References: General | Dark Patterns | Fake, Hoax |
Shortening Services | Web Archives
Quotes
- What kind of doctor fixes broken websites?...
- "You step in the stream,
but the water has moved on.
This page is not here.
The Web site you seek
cannot be located but
endless others exist.
This site has been moved.
We'd tell you where, but then we'd
have to delete you." ~Haiku error messages - "The truth is that these companies [social media behemoths]...
Summary
- [1] Navigate to Valid Sites via bookmarks, password managers, search engines
- [1] Avoid Impostor and Malicious Sites, e.g., don't type in URLs, don't click on links in emails or popups
- [1] Enable Fraudulent Site Warnings, e.g., Phishing, Malware, Plugins
- [1] Learn to Examine and Recognize URLs in status bar; prefer HTTPS:
- [2] Access Shortened URLs Cautiously
- [3] Find Old Versions of Pages or Sites via Web Archives e.g., "Wayback Machine" or search engine caches
- References
[1] Navigate to Valid Sites
- Use browser bookmarks/favorites or a password manager to navigate, rather than type or click on links
- Use browser's built-in Search box, or combo Address field, rather than typing "google.com"
- In search results, look for "Official Site" or at actual URL to determine if expected destination
- Some search engines hide addresses in favor of more human readable names.
- Avoid fake/conspiracy news sites (and this includes a lot of social media)
-- besides disinformation and wasting your time, they can be an avenue for malware. - Avoid DNS problems -- see section: Connection : Wi-Fi (Router)
[1] Avoid Insecure, Impostor and Malicious Sites
- Typos & look-alike characters in site addresses (URLs) could lead you
to malicious, impostor sites -- or insecure versions (HTTP: vs. HTTPS:) - Think twice before clicking on links in an email
- Think twice before clicking on links in popups, or unknown links in web pages,
esp. ads which might redirect you to look-alike sites - Quiz: Can you identify a phishing web site login?
[1] Enable Fraudulent Site Warnings
- macOS:
Safari > Preferences > Security > Fraudulent sites[screenshot] - macOS:
Firefox > Preferences > Security >
Block reported attack sites / web forgeries / add-ons - macOS:
Chrome > Settings (advanced) > Privacy >
Protect you and your device from dangerous sites - iOS:
Settings > Safari > Privacy & Security > Fraudulent Website Warning[screenshot] - Enable phishing/malware/plugin warning: -- see section: Connection : Malware
[1] Learn to Examine and Recognize URLs
- Show links in status bar; inspect before you click
- macOS:
Safari > View > Show Status Bar - Display full address (URL) in address/location bar
- macOS:
Safari > Preferences > Advanced > Show Full Website Address - iOS:
Safari > (tap in address bar) - For secure sites, check HTTPS: and verify status (lock icon or certificate) -- see next section: Use HTTPS:
[2] Access Shortened URLs Cautiously
- Due to shortening or normal redirects, you may not be seeing the 'real', final URL,
e.g.,https://communicrossings.com/olli - https://bit.ly/20ICWYg, https://tinyurl.com/hg8776o
- There are several sites that follow any redirects and display the final destination
- e.g., CheckShortURL, Unshorten
- If the URL was generated by:
- Bitly: add a plus sign ('+') to the URL and Bitly will display a preview
- TinyURL: place 'preview' in front of the shortened URL
- Instead of this manual process, you could install a browser extension that displays final URL
via popup, status area (if overlap, hide regular status bar), or in-line (in page itself) - Safari: Ultimate Status Bar
- Firefox: No Redirect, Long URL Please Mod
- Chrome: LongURL
[3] Find Old Versions of Pages or Sites via Web Archives
- What if a page or site has disappeared, or you want to see an older version?
- e.g., some versions of my web site (currently: communicrossings.com) from past ~25 years --
most courtesy of the Internet Archive (aka Wayback Machine) - 1993?-1998?: http://www.netaxs.com/~weyer
- 1999-2000: http://members.bellatlantic.net/~sweyer/
- 2001-2005: http://members.home.net/saweyer/
- 2001-2005: http://users.aol.com/steveweyer/DOS
- 2002-2004: http://home.comcast.net/~saweyer/
- 2002-2006: http://www.kagi.com:80/weyer;
http://mywebpages.comcast.net:80/saweyer/;
http://home.comcast.net:80/~saweyer/cc/index.htm - 2010: http://communicrossings.com:80/
- 2011: http://communicrossings.com:80/
- 2015: http://communicrossings.com/ archive.is
References
- {TCYOP-4: 84-85; TCYOP-3: 68-69}
- sections: Refs: Dark Patterns; Fake,Hoax; Shortening Services; Web Archives
- topics: cybersquatting, DNS hijacking, homographs, Snopes
- Wikipedia: typosquatting aka URL hijacking; e.g., googl.com; URL redirection
- HowStuffWorks: How to Detect Online Scams
- Ever wonder how good you are at telling the difference between a legitimate website
and one that's a phishing attempt? fake vs. real login pages; OpenDNS - Google-hosted malvertising leads to fake Keepass site that looks genuine punycode; Google-verified advertiser + legit-looking URL + valid TLS cert = convincing look-alike; 10/19/2023; Ars
- Google Chrome now detects typos in your URLs Verge; 5/18/2023
- MapQuest and Other Internet Zombies NYT; 6/21/2022
- The Ghost of the Soviet Union Still Haunts the Internet .su domain; Wired; 3/29/2022
- The Best of 404PageFound, and Other Primitive '90s Websites That Still Exist LH; 12/14/2021
- Bitflips when PCs try to reach windows.com: What could possibly go wrong?
domain names that vary by a single mutated character; Ars; 3/4/2021 - New Research Reveals the Hidden Downsides of Link Previews
it can also leak sensitive data, consume bandwidth, and drain batteries; Wired; 10/28/2020 - Researcher discovers address bar spoofing bugs in Safari, Opera, and Yandex,
all now fixed, but other popular browsers, like UC Browser, have not issued a patch TC; 10/20/2020 - How to Block Bad Websites—or Just Get Things Done
block distractions and temptations: BlockSite, LeechBlock NG, Cold Turkey, Freedom; Wired; 10/11/2020 - Wikipedia Is the Last Best Place on the Internet Wired; 2/17/2020
- The .Org Mirage You don’t have to be a nonprofit
— or meet any special criteria at all (compared to .gov, .edu); NYT; 12/5/2019 - Scammers favor malicious URLs over attachments in email phishing TNW; 11/8/2019
- Who owns that shady website? using ICANN:WhoIs and other databases; PC; 6/20/2019
- How to Spot a Fake Address Bar in Chrome on Android LH; 4/29/2019
Dark Patterns
- Stopping the Manipulation Machines
hidden unsubscribe links; recurring subscriptions;
examples: Trick questions; Bait and switch;
Roach motel; Friend spam; Sneak into basket; NYT; 4/30/2021 - How to Spot -- and Avoid -- Dark Patterns on the Web UX ploys designed to trick you
into spending money, or make it nearly impossible to unsubscribe; Wired; 7/29/2020
Fake News, Hoaxes
- Wikipedia: Fake news; Fake news website; Snopes (aka Urban Legends Reference Pages)
- How To Use Google's Fact Check Explorer To Verify Claims on the Web
True? False? Somewhere in between? Google's online tool will tell you
Giz; 1/23/2024 - Fact Checkers Take Stock of Their Efforts: "It's Not Getting Better" NYT; 9/29/2023
- A Better Way to Think About Conspiracies people will always be interested in conspiracy theories.
They need a tool kit for discriminating among different fringe ideas; NYT; 3/2/2021 - Don't Go Down the Rabbit Hole
critical thinking, as we’re taught to do it, isn’t helping in the fight against misinformation; NYT; 2/18/2021 - In a post-truth world, we need Wikipedia more than ever CNet; 1/15/2021
- At 20, Wikipedia has become a refuge from Big Tech's misinformation CNet; 1/15/2021
- Have Trump’s Lies Wrecked Free Speech? a debate has broken out over whether the
once-sacrosanct constitutional protection of the First Amendment has become a threat to democracy; 1/6/2021 - It's only fake-believe: how to deal with a conspiracy theorist
1. Hunting an invisible dragon
2. Fake authority
3. Coincidence or covert operations?
4. False equivalence
5. The thought-terminating cliche
The art of pre-suasion; Guard; 11/29/2020 - How to Talk to Friends and Family Who Share Conspiracy Theories NYT; 10/25/2020
- Recognize Misinformation on the Internet
identifying reliable information online is especially urgent, and especially for seniors; NYT' 8/28/2020 - How QAnon Creates a Dangerous Alternate Reality
conspiracy theory parallels the immersive worlds of alternate reality games; NYT; 8/5/2020 - [2] Adobe's plans for an online content attribution standard could have big
implications for misinformation mostly images; TC; 8/3/2020 - The anatomy of a fake news headline TNW; 7/12/2020
- How to Spot a Conspiracy Theory
Contradictory ideas
Overriding suspicion
Nefarious intent;
"Something must be wrong";
Persecuted victim;
Immune to evidence;
Reinterpreting randomness; LH; 5/14/2020 - Democrats counter Trump’s fake coronavirus news with AI that fought ISIS propaganda TNW; 5/4/2020
- These Students Are Learning About Fake News and How to Spot It NYT; 2/20/2020
- Reuters launches a new Reuters Fact Check business unit and blog and partners
with Facebook to review news headlines, deepfakes, and user generated content TC; 2/12/2012 - Do Not Click OR DOJ; 1/2020
- How to fight lies, tricks,and chaoso nline Verge; 12/3/2019
- How blockchain will kill fake news NYT is one of the first major news publications to test blockchain
to authenticate news photographs and video content, according to Gartner; CW; 12/2/2019 - How to Tell If an Online Review Is Fake LH; 10/21/2019
- Apple's Tencent privacy controversy is more complicated than it looks
Fraudulent Website Warning checks URLs in a list; it doesn't share with Google or Tencent; Verge; 10/14/2019 - Why People Keep Falling for Viral Hoaxes
when confronted with new information, humans don't always do the logical thing and evaluate it on its own merits, Phillips says.
Instead, we often make snap decisions based on how the information adheres with our existing world views; Wired; 8/22/2019 - Behold, the most (intentionally) poorly designed website ever created User Inyerface; Ars; 7/4/2019
- How to Tell if a News Site Is Reliable UnNews list; LH; 5/1/2019
- Marking 30 years of the web, Tim Berners-Lee calls for a joint fight against disinformation TC; 3/12/2019
- Fun iOS Safari Bug Lets You Trick Your Friends With Fake Website Headlines MR; 2/21/2019
- Google publishes 30-page paper on how it combats disinformation across YouTube, Search, News, Ads
product improvements, experience with spam, context for users; 2/18/2019 - Facebook struggles to deal with vaccine deniers
many users have trouble distinguishing between reliable sources and unreliable ones; 2/13/2019 - Snopes quits and AP in talks over Facebook’s fact-checking partnership TC; 2/1/2019
- Fake news sites are simply changing their domain name to get around Facebook fact-checkers Mash; 1/31/2019
- Google Chrome to get warnings for 'lookalike URLs' when accessing mistyped domains; ZD; 1/30/2019
- People older than 65 share the most fake news, a new study finds
NYU and Princeton study of 3,500 US adults: 11% of those over 65 have shared a hoax article on Facebook,
while just 3% of those 18 to 29 have done so; and the finding holds true across party lines; Verge; 1/9/2019
Shortening Services
- Wikipedia: URL shortening service;
- Wikipedia: Bit.ly; TinyURL; Tr.im
- sites: bit.ly; tinyurl.com; tr.im
- How to Know if a QR Code or a Short URL Is Safe
avoid QR codes until phone OS offers preview; LH; 1/13/2022
Web Archives
- Wikipedia: Internet Archive, Wayback Machine;
Wikimedia Downloads - Internet Archive (aka Wayback Machine); 1996-
- Library of Congress Web Archives 1997-
- archive.is, perma.cc: submit individual pages (similar to the "save page now" feature at the Internet Archive)
- conifer: create personal web archives (previously webrecorder.io)
- Los Alamos National Laboratory Time Travel Service: query multiple web archives; 2002-
- newspapers
- timesmachine: 150 years of New York Times journalism
- newspapers.com
- Library of Congress: Chronicling America: Historic American Newspapers
- The British Newspaper Archive
- Google Won't Let You View Cached Web Pages Anymore (But You Still Can)
cached:URL; LH; 2/8/2024 - Google will no longer make site backups while crawling the web: Cached webpages are dead Ars; 2/2/2024
- 7 Fun Ways to Use the Internet Archive MF; 1/11/2024
- The Dream Was Universal Access to Knowledge. The Result Was a Fiasco. Internet Archive vs. publishers; NYT; 8/13/2023
- Wikipedia's Moment of Truth
can the online encyclopedia help teach A.I. chatbots to get their
facts right -- without destroying itself in the process? NYT; 7/18/2023 - The World's Digital Memory Is at Risk NYT; 6/21/2023
- A look at four publishers' lawsuit against the Internet Archive, which hinges on defining the legal ownership of ebooks
Just Because ChatBots Can’t Think Doesn’t Mean They Can’t Lie;
Or that they haven’t already started to pollute Google searches.
And if publishers win their lawsuit against the Internet Archive,
verifying facts and quotes will get a lot harder; Nation; 3/17/2023 - Lost something? Search through 91.7 million files from the ’80s, '90s, and 2000s Discmaster; Verge; 10/19/2022
- 'Wayforward Machine' provides a glimpse into the future of the web
ongoing threats; Verge; 10/1/2021 - A look at the Internet Archive, a preservation project that grew from 2TB in 1997 to ~100PB now
issues with scraping paywalled news sites and social media; FT; 10/4/2022 - How to Read a Blocked Website
hide your real IP address with a proxy connection, e.g., VPN;
try using TOR (The Onion Browser); LH; 9/2/2022 - Good Luck if You're Forced to Use These Hideous Federal Websites
throwbacks to the MySpace era; Giz; 7/16/2022 - Travel Back in Time With Street View and Map Archives Wired; 7/10/2022
- Russians Are Racing to Download Wikipedia Before It Gets Banned Slate; 3/21/2022
- A profile of Brewster Kahle and the Internet Archive, which marked
its 25th anniversary earlier this year and is now home to over 70 PB of data TR; 12/19/2021 - How to Get Past a Paywall to Read an Article for Free
Paste the headline in Google;
Try a Facebook redirect: https://facebook.com/l.php?u=URL
Open the link in an incognito window;
Disable JavaScript in your browser;
Edit a couple of elements on the webpage;
Use an annotation service, e.g., Outline;
Try browser add-ons;
Check out paywall bypass shortcuts on iPhone;
LH; 10/5/2021 - The Wayback Machine's First Crawl 1996 video: 2:05; 8/6/2021
- With the removal of Trump's Twitter account, many of his tweets embedded
on thousands of web pages were wiped out, creating an ultimate case of 'link rot' Verge; 1/9/2021 - The Internet Archive starts adding banners on some Wayback Machine pages
with links that provide contextual information from fact-checking organizations 10/30/2020 - How to Link Websites Without the Eventual Broken Links using WBM; LH; 9/8/2020
- You Can Download the Entirety of English Wikipedia to Browse Offline Kiwix; CNet; 7/10/2020
- The Internet Archive's VHS Vault will send you on a 90s nostalgia trip 20,000+ recordings; Verge; 2/28/2020
- Brave browser now automatically points to Wayback Machine on 404 Verge; 2/26/2020
- The Geocities Archive Is Bringing the Early Internet to Life MB; 1/27/2020
- The Archive Team, which wants to save Yahoo Groups content by uploading it to Internet Archive,
says Verizon has blocked the email addresses of its volunteers ZD; 12/9/2019 - The Internet Archive Is Making Wikipedia More Reliable
check citations from books as well as the web; Wired; 11/3/2019 - Internet Archive recovers half a million 'lost' MySpace songs 4/4/2019
- Delete Never: The Digital Hoarders Who Collect Tumblrs, Medieval Manuscripts,
and Terabytes of Text Files Giz; 3/4/2019 - Meet the man archiving the internet Wayback Machine Director Mark Graham; TNW; 2/5/2019
Safer Internet: Browsing: Use HTTPS
Safer Internet: Browsing: Use HTTPS
Summary | Update | https: | Vulnerable Sites | Insecure Connection | TLS |
References: General | Apple | Certificates | Firefox |
Google/Chrome | OpenSSL, Freak, Heartbleed
Summary
- [1] Update System/Browser Software
- [1] Use https: (HyperText Transport Protocol Secure) instead of regular http: whenever a site supports it
- [2] Check for Vulnerable sites
- [2] Use VPN and 2FA to Compensate for an Insecure Connection
- [3] Test Your Browser's TLS; Use sftp:; Install a Certificate
- References
[1] Update System/Browser Software
- Check that your system, browser and application software have latest security updates -- see section: Software Updates
- Otherwise, content could be exposed if security vulnerabilities have not been patched on both ends.
[1] Use https: (HyperText Transport Protocol Secure) instead of regular http:
- More and more sites default/redirect to HTTPS:, e.g.
- wider availability of free certificates for sites, e.g., Let's Encrypt
- automatically from http: paypal.com
- via browser extension, e.g., HTTPS Everywhere for Chrome, Firefox; not avail for IE, Safari -- maybe not needed
- via preference, e.g., linkedin.com:
Account > Security - Some password managers, e.g., 1Password, can check for non-https and vulnerable sites
- Check browser Address Bar: lock icon and/or URL beginning with "https://"
- Be especially aware on login pages and shopping and finance sites.
- Some browsers, e.g., Chrome, will flag 'insecure' sites: any http: page in "incognito" (private browsing) mode, or any http: page with an input field
- Client-server connection with HTTPS: {Figure 6. TCYOP-4: 67; TCYOP-3: 55}.
[2] Check for Vulnerable sites
- Although you can't update the security software on sites, you can minimize your exposure
- Change passwords on any sites with unpatched security vulnerabilities, e.g., Heartbleed; use a password manager to monitor, e.g., 1Password: Watchtower; also PM can flag any non-https: logins
- Otherwise, content could be exposed if security vulnerabilities have not been patched on both ends.
[2] Use VPN and 2FA to Compensate for an Insecure http: Connection
- If insecure site requires login over insecure http:, esp. over WiFi -- see VPN section and Passwords section (2FA)
[3] Test Your Browser's TLS; Use sftp:; Install a Certificate
- Test Your Browser's TLS(SSL): How's My SSL?
- Safari(macOS,iOS) may include some fallback older 'insecure cipher suites' I'm checking if this is serious and/or being fixed; Firefox, Chrome better?
- File transfer: use sftp: instead of ftp:
- Web site admin: free certificate: letsencrypt.org; possible installation cost, configuration issues depending on web host
References
- {TCYOP-4: 66-68; TCYOP-3: 54-56}
- sections: Refs: Apple; Certificates; Firefox; Google/Chrome; OpenSSL, Freak, Heartbleed
- Wikipedia: Uniform Resource Locator (URL): Hyperlink; network location (address) plus access method, e.g., http:
- Wikipedia: hypertext; HyperText Transfer Protocol (HTTP)
- HowStuffWorks: Internet Infrastructure: URL; Ports and HTTP
- Wikipedia: Secure Sockets Layer (SSL), aka Transport Layer Security (TLS)
- Wikipedia: HyperText Transfer Protocol Secure (HTTPS) protocol for secure communication
- Wikipedia: HTTPS Everywhere browser extension
- Wikipedia: File Transfer Protocol (FTP) standard network protocol used to transfer files from one host to another
- Wikipedia: Secure Shell (SSH); SSH FTP (SFTP)
- Wikipedia: SHA-2 (Secure Hash Algorithm 2) used in certificates
- Wikipedia: RC4 (Rivest Cipher 4) stream cipher
- [3] SSL Cipher Suite Details of Your Browser test page
- EFF to deprecate HTTPS Everywhere extension as HTTPS is becoming ubiquitous 9/25/2021
- Hackers can mess with HTTPS connections by sending data to your email server Ars; 6/9/2021
- Security Researchers Take Advantage of Insecure HTTP to Display Fake Videos on TikTok iOS, Android; 4/18/2020
- DuckDuckGo Will Automatically Encrypt More Sites You Visit If a site offers HTTPS, DuckDuckGo's Smarter Encryption will take you there; Wired; 11/19/2019
- Cloudflare, Google Chrome, and Mozilla Firefox add support for HTTP/3, the next major version of the HTTP protocol uses the QUIC (Quick UDP Internet Connections) protocol instead of TCP; built-in TLS (encryption) support; ZD; 9/26/2019
- [2] HTTPS Isn't Always As Secure As It Seems TLS site vulnerabilities; Wired; 3/28/2019
Apple
- How to Fix Safari 'This Connection Is Not Private' Warnings OSXD; 3/17/2021
- Why Does Safari Say 'Not Secure' for Some Webpages on iPhone, iPad, or Mac? http://; OSXD; 3/29/2019
Certificates
- Wikipedia: certificate authority
- Let's Encrypt comes up with workaround for abandonware Android devices Ars; 12/22/2020
- Kazakhstan spies on citizens’ HTTPS traffic; browser-makers fight back Google, Mozilla, Apple, and Microsoft block Kazakhstan's self-signed root certificate; Ars; 12/21/2020
- Kazakhstan government is intercepting HTTPS traffic in its capital third time since 2015 that the Kazakh government is mandating the installation of a root certificate on its citizens' devices; ZD; 12/6/2020
- On Older Versions of Android, Many Let's Encrypt-Secured Sites May Stop Working in 2021 < 7.1.1; 11/6/2020
- Let's Encrypt discovers CAA bug, must revoke customer certificates Ars; 3/3/2020
- HTTPS for all: Let's Encrypt reaches one billion certificates issued Ars; 2/27/2020
- Safari to snub new security certs valid for more than 13 months Reg; 2/20/2020
- Apple, Google, and Mozilla block Kazakhstan's HTTPS intercepting certificate ZD; 8/21/2019
- The Kazakhstan government is making ISPs force users to install a government-issued certificate on all devices and in every browser to intercept HTTPS traffic ZD; 7/18/2019
- [3] Cloudflare aims to make HTTPS certificates safe from BGP hijacking attacks Ars; 7/18/2019
Firefox
- Firefox 83 will automatically switch you to secure HTTPS sites HTTPS-Only Mode will display a warning if a website doesn't have an HTTPS version the browser can load; Eng; 11/18/2020
Google / Chrome
Microsoft
OpenSSL, Freak, Heartbleed
- Wikipedia: OpenSSL; Heartbleed; FREAK
Safer Internet: Browsing: Manage Storage of Private Data
Safer Internet: Browsing: Manage Storage of Private Data
Summary | Where/When | Private Browsing | Cookies | Autofill |
Do Not Track | Browser 'Fingerprinting' | Browser History |
Search History | Download History | Caches | Statistics |
References: General | Bookmarks / Favorites | Cookies | FingerPrinting | Google |
History | iOS | macOS | Microsoft | Private (Incognito) Browsing | Tracking
Summary
- [1] Understand When and Where Data is Stored Locally by OS, Apps, Browsers, e.g., site history, download history, cookies, flash cookies, web caches, search, passwords; other data might be stored remotely by ISP or visited sites
- [1] Consider Private Browsing to reduce data collected in the first place
- [1] Reduce Cookies, esp. from 3rd parties
- [1] Minimize Browser AutoFill: Passwords, Credit Cards, Contacts
- [2] Reduce Web Site Tracking
- [2] Reduce Browser 'Fingerprinting' based on unique system/browser properties
- [2] Reduce / Clear Browsing History
- [2] Reduce Search History / Suggestions; to reduce remote search history, use a more privacy-oriented search engine, e.g., DuckDuckGo -- see upcoming section Search Privately
- [2] Clear Download History
- [2] Clear Caches: Pages & Images
- [3] Reduce Browser Statistics
- References
[1] When: Before, After; Where: OS, Apps, Browsers
- Some data can be useful to you: speed, convenience, even necessary, e.g., for logins
- Other data could be damaging in the wrong hands
- Two strategies (or combo of both) to minimize this data:
- Before: prevent data from being stored on your device or on servers in the first place -- settings or private browsing
- After: remove stored data later -- manual commands or automatically upon exit from browser / app
- [2] System utilities can remove some caches, history, e.g., macOS: Maintenance, Onyx; Win: CCleaner
- Android:
Settings - iOS:
Settings > Notifications, Control Center, Privacy - macOS:
System Preferences > Security & Privacy, Sharing, Parental Controls - Win:
Control Panel / Settings - Applications that access the internet, e.g., Facebook, Maps, Skype, etc.; also see Email section
- for Location, Notifications: Connection: Unnecessary Services section
- Browsers -- settings vary; meanings of 'history' and 'web data' may vary
- macOS:
Safari > Preferences > Privacy, Security Firefox > Preferences > Privacy, SecurityChrome > Preferences (or address: chrome://settings)- iOS:
Settings > Safari - Windows: IE:
Control Panel > Internet Options - [3] Some browsers come with pre-sets for more privacy/security settings, e.g., Epic, WhiteHat Aviator
[1] Consider Private Browsing
- Typically stored locally & temporarily -- until tab/window closed: cookies; browsing, download, and search histories; form/autofill data; page or image caches
- What's stored / hidden / erased may vary by browser; tradeoffs: performance, convenience
- Another possible benefit: ability to exceed n-article/month limits on certain paywalled sites.
- Potential loopholes: data from plug-ins / extensions; downloaded files still on disk; bookmarks; search engine might store terms on server; cached DNS lookups
- Despite 'private/incognito' label, it does not provide anonymity per se -- just more temporary / compartmentalized browser storage; see VPN, anonymous browsing, e.g., Tor
- Before (all windows by default)
- Possible in some browsers, but not too practical since some sites won't work well; would there still be a way to open a new window in non-private mode?
- macOS, iOS: Safari: not avail
- macOS:
Firefox > Preferences > Privacy > History > Always Use Private Browsing Mode - [3] Chrome -- involves starting with "-incognito" switch in AppleScript (macOS), Properties (Win) or command line
- After (specific new window & tabs)
- macOS:
Safari > File > New Private Window - macOS:
Firefox > File > New Private Window - macOS:
Chrome > File > New Incognito Window{Figure 10: TCYOP-4: 91; TCYOP-3: 74}
- iOS:
Safari > [rects] > Private
[1] Reduce Cookies
- Cookies are usually erased by Private Browsing, but some browser settings are useful anyway
- Recommended: blocking "3rd-party" cookies
- Blocking all cookies means some sites won't work well (or at all)
- Allowing all cookies is a bad idea
- Some badly implemented web sites may require use of 3rd-party cookies and/or cross-site tracking
-- if you need to use that site: temporarily disable settings, finish your work, then re-enable - Erasing cookies means you'll have to re-login to sites, and perhaps re-enter a security answer or 2FA code
- Before
- macOS:
Safari > Preferences > Prevent Cross-Site Tracking: on; Block All Cookies: off - macOS(older):
Safari > Preferences > Privacy > Cookies and website data > Allow from websites I visit[screenshot] - macOS:
Firefox > Preferences > Privacy > History > Accept Third-party Cookies > Never; Keep until:(expire, close Firefox); {Figure 11: TCYOP-4: 93; TCYOP-3: 76;} - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Content Settings > Cookies > Block third-party cookies and site data - iOS:
Settings > Safari > Prevent Cross-Site Tracking: on; Block All Cookies: off - iOS10:
Settings > Safari > Privacy & Security > Block Cookies > Allow from websites I visit[screenshot] - After
- macOS:
Safari > History > Clear History and Website Data (cookies, history, other data) - macOS:
Safari > Preferences > Privacy > Cookies and website data > Remove All Website Data[screenshot] - macOS:
Firefox > History > Clear Recent History - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Clear Browsing Data - macOS:
System Preferences > Flash Player > Storage > Delete All (flash cookies) - iOS:
Settings > Safari > Clear History and Website Data (cookies, history, other data)[screenshot] - [2] macOS:
System Preferences > Flash Player > Storage > Delete All, i.e., "Flash Cookies" - see section Malware : Flash for more about Flash cookies or uninstalling Flash
[1] Minimize Browser AutoFill: Passwords, Credit Cards, Contacts
- Most browsers can provide autofill; however, info is only as secure as device admin password
- Backup? Share between browsers on same device?
- Share between devices -- esp. if different vendors?
- Generally, it's better to use a password manager
- Before
- macOS:
Safari > Preferences > Autofill (contacts, passwords, credit cards) - macOS:
Firefox > Preferences > Security > Logins > Remember Passwords for Sites - macOS:
Chrome > Preferences > Advanced Settings > Passwords and forms > Enable AutoFill to fill out web forms in a single click; Offer to save your web passwords - iOS:
Settings > Safari > Passwords & AutoFill (contact, passwords, credit cards) - iOS:
Settings > Accounts & Passwords: edit - Win:
Edge > Settings > View Advanced settings > Autofill: Save Passwords/Cards: off; Manage - After
- macOS:
Safari > Preferences > Passwords > Remove All (or selected) - macOS:
Firefox > Preferences > Security > Logins > Saved Logins - macOS:
Chrome > Clear Browsing Data - iOS:
Settings > Safari > Passwords & AutoFill > Saved Passwords / Credit Cards
[2] Reduce Web Site Tracking
- Turn off tracking in browser, even though some web sites may ignore this (optional) request;
Apple has removed this setting in latest macOS & iOS (see below for older) --
since it wasn't effective, and perhaps gave false sense of security? - macOS:
Safari > Preferences > Privacy > Website tracking > Ask websites not to track me[screenshot] - macOS:
Firefox > Preferences > Privacy > Tracking > Tell websites I do not want to be tracked - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Send a "Do Not Track" request with your browsing traffic - iOS:
Settings > Safari > Privacy & Security > Ask websites Not To Track Me[screenshot] - Win:
Edge > Settings > View Advanced settings > Privacy and services > Send Do Not Track Requests: on - Avoid "Single Sign On" login feature on 3rd-party sites using your Google, Facebook, Twitter credentials
- In addition to controlling cookies (next), see section Ad Blocking to further reduce tracking
[2] Reduce Browser 'Fingerprinting'
- Your unique combination of system settings and browser properties can enable web sites to identify you,
even if you're minimizing/clearing cookies, using private browsing, etc. - Currently, some systems/browsers are better at minimzing fingerprinting,
e.g., Safari, Firefox; -- and iOS generally; see Refs: Fingerprinting - Check your web browser's tracking settings, fingerprint uniqueness: EFF: Cover Your Tracks
- Unfortunately, Cover Your Tracks doesn't advise on how to fix this...
- Maybe use more defaiult browser settings -- to become less unique?
- Hopefully other tools/approaches will be forthcoming.
[2] Reduce / Clear Browsing History
- list of sites visited; usually erased by Private Browsing and utilities, e.g., Ghostery, Blur {TCYOP-4: 97, 101}
- history may be accessible by other users, e.g., nosy friend, cybercafe, law enforcement
- you can also use Bookmarks or Password Manager to save / return to important sites, rather than rely on history list
- Before
- macOS:
Firefox > Preferences > Privacy > History > Remember my browsing and download history - After
- macOS:
Safari > Clear History and Website Data (cookies, history, other data) - macOS:
Safari > History > Clear History and Website Data - macOS:
Safari > General > Remove History Items (time)[screenshot] - macOS:
Firefox > History > Clear History - macOS:
Firefox > Preferences > Privacy > History > Clear history when Firefox closes (Settings: browsing, downloads) - macOS:
Chrome > Clear Browsing Data - iOS:
Settings > Safari > Clear History and Website Data (cookies, history, other data) - iOS:
Settings > Safari > Frequently Visited Sites
[2] Reduce Search History / Suggestions
- Usually erased by Private Browsing
- Before
- macOS:
Safari > Preferences > Search - macOS:
Firefox > Preferences > Search - macOS:
Firefox > Preferences > Privacy > History > Remember search and form history - macOS:
Chrome > Preferences > Advanced > Privacy > Use a prediction service to help complete searches and URLs typed in the address bar or the app launcher search box; searches still saved and not clearable? - iOS:
Settings > Safari > Search Engine Suggestions - After -- same as browsing history?
[2] Clear Download History
- usually erased by Private Browsing -- though files may still be Downloads
- Before
- macOS:
Safari > General > Remove Download List Items (time)[screenshot] - macOS:
Chrome > Preferences > Advanced > Privacy > Content Settings > Automatic Downloads - After -- same as browsing history?
- macOS:
Safari > Show Downloads (far right icon)l > Clear - macOS:
Firefox > Tools > Downloads > Clear Downloads - macOS:
Chrome > Clear Browsing Data
[2] Clear Caches: Pages & Images
- usually erased by Private Browsing and utilities
- Before
- macOS:
Firefox > Preferences > Advanced > Network > Cached / Offline Content - After -- same as browsing history?
- macOS:
Safari: shift+click on the Refresh page button-- clears cache for only that page - macOS:
Safari > Preferences > Advanced > Show Develop menu in menu bar-- add Develop menu - macOS:
Safari > Develop > Empty Caches
[3] Reduce Browser Statistics
- Diagnostic data may be useful to vendors for bug fixes and improvements -- optional: it's up to you
- macOS:
System Preferences > Security & Privacy > Diagnostics & Usage - macOS:
Firefox > Preferences > Advanced > Data Choices - macOS:
Chrome > Preferences > Advanced Settings > Privacy > Automatically send usage statistics and crash reports to Google
References
- {TCYOP-4: 87-98; TCYOP-3: 71-78; Live Data, Historical Data, Avoid or Remove Local Data, Private Browsing Modes, Browser Privacy Settings, Do Not Track}
- sections: Refs: Bookmarks / Favorites; Cookies; FingerPrinting; Google; History; iOS; macOS; Microsoft; Private (Incognito) Browsing; Tracking
- topics: autofill, super/zombie cookie
- Wikipedia: browser privacy mode; browsing history; web cache
- Wikipedia: web storage HTML5 local storage
- How to Reload Your Tabs When Your Browser Unexpectedly Quits LH; 2/9/2023
- Thousands of Popular Websites See What You Type—Before You Hit Submit Wired; 5/11/2022
- How to Use Browser Profiles to Separate Work and Play Wired; 5/2/2021
- Please Refresh Your Browser So Websites Actually Work Giz; 12/4/2020
- How to Customize Your Web Browser's Homepage (and Why You Should) Giz; 9/2/2020
- Apple updates Safari’s anti-tracking tech with full third-party cookie blocking Verge; 3/24/2020
- How to stop those annoying website notification prompts Verge; 7/18/2019
- How to Clear Your YouTube History via YouTube app or web browser; 6/8/2019
- How to Leave No Trace on a Borrowed Computer private browsing; history, downloads, searches; apps: Recent Files; Giz; 3/29/2019
- Why Are Bots Unable to Check "I Am Not a Robot" Checkboxes? CAPTCHA, browser history; MF; 2/25/2019
Bookmarks / Favorites
- How to Sync Safari Bookmarks with Google Chrome OSXD; 12/5/2021
Cookies
- Wikipedia: Cookie small piece of data sent from a website and stored in a user's web browser; Flash cookies
cartoon credit: humoresquecartoons.com - Wikipedia: ever cookie; zombie cookie
- HowStuffWorks: How Cookies Work; What is an Internet cookie?; How to Delete Computer Cookies; Quiz
- How to Block Those Annoying Cookie Banners That Follow You From Website to Website
Super Agent browser extension; MF; 5/27/2022 - You Can Block Those Annoying Cookie Banners on Every Website LH; 5/17/2022
- How to Avoid Those Infuriating Cookie Pop-Ups
Reject All Cookie Consent Notices; Turn Off Cookies;
Use a Privacy-First Web Browser; Wired; 5/22/2021 - Yes, This Site Uses Cookies, Because Nearly All Sites Use Cookies, And We're Notifying You Because We're Told We Have To TD; 5/21/2020
- No need to mourn the death of the third-party cookie marketers, publishers and audiences are all better off; TNW; 5/14/2020
- How to clear cookies from your browser PC; 6/6/2019
Fingerprinting
- Wikipedia: Device Fingerprint
- dnsleaktest.com, ipleak.net check if IP address private
- The Quiet Way Advertisers Are Tracking Your Browsing Wired; 2/26/2022
- [2] How browser fingerprints identify you even when you have cookies turned off TNW; 4/24/2020
- Firefox 69 now blocks cryptominers and tracking cookies by default fingerprinting; TNW; 9/3/2019
- 'Fingerprinting' to Track Us Online Is on the Rise collected device characteristics; Safari(iOS/macOS): minimizes what's shared; Firefox: enable fingerprint blocking; extensions; mobile? NYT; 7/3/2019
- Apple Is Removing 'Do Not Track' From Safari to prevent potential use as a 'fingerprinting variable' (i.e., ironically for tracking); no websites actually honor the request not to be tracked because the government never forced them to comply with it; Giz; 2/6/2019
- Chrome bug meant browser didn't respect user requests to delete Google site data Verge; 10/21/2020
- How to automatically delete the web activity and location history data in your Google account PC; 7/9/2019
- Google will now auto-delete location and search history by default for new users compromise between privacy and ad-targeting data -- after 3-18 months; Verge; 6/24/2020
- A significant majority of consumers do not expect Google to track their activities across their lives, their locations, on other sites, and on other platforms 4/3/2019
History
- Wyden Pulls Support for Privacy Amendment After Rep. Adam Schiff Downplays Impact to NYTimes Giz; 5/26/2020
- Mozilla, Twitter, and a coalition that includes Facebook, Apple, and Google, call on Congress to protect search and browser data from warrantless access CNet; 5/22/2020
- Senate passes spying bill without search and browsing history protections Ars; 5/14/2020
- Firefox Will Give You a Fake Browsing History to Fool Advertisers Using the 'Track THIS' tool opens up 100 tabs at a time that will make you seem like a hypebeast, a filthy rich person, a doomsday prepper, or an influencer; MB; 6/26/2019
iOS
- How to Clear Cookies Only from Safari on iPhone & iPad
while keeping history, etc.; OSXD; 10/8/2021 - How to Check Privacy Report in Safari on iPhone & iPad iOS/iPadOS 14+; OSXD; 1/21/2021
- How to Change Safari Download Location on iPhone & iPad OSXD; 9/30/2020
- How to Clear Cache in Safari on iPhone & iPad Settings > Safari > Clear History and Data (caches, browsing data, cookies, browsing history); OSXD; 3/17/2020
macOS
- How to clear Safari's cache and cookies on Mac MW; 3/3/2023
- How to Check Privacy Report for Websites in Safari on Mac Safari 14+; OSXD; 1/25/2021
- How to Remove Web History in Safari While Keeping Cookies & Other Web Data on Mac OSXD; 1/20/2021
- How to modify the Start Page in Safari 14 for macOS instructions on how to adjust the categories that appear and add a background image; MW; 10/2/2020
- [3] Enabling the Debug menu in Safari 14 on Big Sur and Catalina in order to disable tab previews; 9/22/2020
- [2] How to troubleshoot and fix strange website errors with macOS Safari if a site loads fine in private browsing or another browser, stored data may be problem:
Safari > Preferences > Privacy > Manage Website Data > Remove; MW; 2/21/2019
Microsoft
- You Can Make It Way Harder for Cookies to Track You in Edge LH; 5/17/2022
- How to Keep Your Work and Personal Browsing Separate on Edge Chromium LH; 5/20/2020
Private Browsing
- Incognito Mode Isn't As Incognito As You Might Think NYT; 7/21/2022
- Does Safari always request fresh logins to your sites? If it does, there’s a reason MW; 8/5/2020
- Incognito Mode May Not Work the Way You Think It Does limited privacy; Wired; 8/2/2020
- What 'Incognito Mode' Can and Can't Do to Protect Your Data LH; 6/3/2020
- Suit Claims Google’s Tracking Violates Federal Wiretap Law Google tracked and collected users’ browsing history even in so-called private browsing (Incognito) mode; NYT; 6/3/2020
- Don’t trust Google Chrome’s incognito mode what it doesn't save: Browsing history, Cookies and Site Data, Information entered into forms; it does save: Bookmarks and downloads; who can still track: Websites you visit (via IP, device id), Your employer or school, Your ISP; TNW; 12/3/2019
- The New York Times is still detecting Chrome 76 Incognito Mode after Google's fix 8/9/2019
- Chrome 76 prevents NYT and other news sites from detecting Incognito Mode Ars; 7/19/2019
- Incognito mode won't keep your browsing private browser compartmentalization (different browsers for different activities); FC; 4/12/2019
- Chrome to patch loophole that allows sites to block Incognito mode users Verge; 2/18/2019
Tracking
- Wikipedia: website visitor tracking; Do Not Track (DNT)
- Google Chrome
- Firefox
- Microsoft Edge
- Microsoft IE
- Safari (iOS)
- Safari (OS X)
- Google Analytics Opt-out Browser Add-on
- Facebook Change Ensures Tracking by Preventing URL Stripping TB; 7/19/2022
- Brave takes on the creepy websites that override your privacy settings
'bounce tracking' can still set cookies; Ars; 3/9/2022 - DuckDuckGo wants to stop apps tracking you on Android Ars; 11/20/2021
- Browser 'Favicons' Can Be Used as Undeletable 'Supercookies' to Track You Online MB; 2/9/2021
- How to disable favicons in Safari on Mac Safari > Preferences > Tabs > Show website icons in tabs; 11/29/2020
- Now you can enforce your privacy rights with a single browser tick Global Privacy Control; Ars; 10/8/2020
- The high privacy cost of a 'free' website trackers; TNW; 9/27/2020
- Firefox 79 clears redirect tracking cookies every 24 hours 8/4/2020
- How to get bill-pay and financial sites to work in Safari may need to disable cross-site tracking setting -- later, re-enable; MW; 4/22/2020
- I Visited 47 Sites. Hundreds of Trackers Followed Me. NYT; 8/23/2019
- Microsoft brings tracking prevention to its Edge browser EG; 6/27/2019
- Chrome, Safari and Opera criticised for removing privacy setting 4/9/2019
- How the tragic death of Do Not Track ruined the web for everyone FC; 3/17/2019
- DuckDuckGo Warns that Google Does Not Respect 'Do Not Track' Browser Setting plus Facebook, Twitter; 2/5/2019
Safer Internet: Browsing: Block Ads
Safer Internet: Browsing: Block Ads
Quotes | Summary | Block Pop-ups | Avoid Pop-ups |
Install Ad Blocker | Unblock Sites | Remove Adware |
References: General | Android | Chrome |
Firefox | iOS | macOS | Windows | Wipr
Quotes
Summary
- [1] Block Pop-ups to avoid annoying and possibly dangerous ads
- [1] Avoid Pop-ups/Pop-unders -- some are 'malvertising' or 'click-bait'
- [1] Install an Ad-blocking Extension (aka 'Content Blocker'):
less data usage, faster page load times, longer battery life, decreased clutter, reduced tracking - [1] Use your browser's "reader mode" to reduce ads, clutter
- [2] Selectively Allow Ads?
- [3] Prevent / Remove Adware
- References
[1] Block Pop-ups
- Some browsers have a site-by-site preference, others global -- for no/all sites
- macOS:
Safari > Preferences > Web Sites > Popup Windows: Block, Block&Notify, Allow - macOS:
Firefox > Preferences > Content > Block pop-up windows[screenshot] - iOS:
Settings > Safari > Privacy & Security > Block pop-ups[screenshot] - If necessary for some sites to function, re-enable temporarily, then re-disable.
[1] Avoid Pop-ups
- Some pop-up windows may occur despite block settings, esp. 'pop-unders' which appear to 'hijack' your browser
- Some may warn of detected malware, and offer software, services, scams, or scans
- Although you should already be protected (see Software Updates, Malware sections),
you might still be vulnerable to "drive-by" malware -- so, do not click on links or close the popup, or respond to the threats/offers (would reputable organizations/companies act this way?) - Instead, close the browser entirely ('forcibly' if necessary), then run your own malware scan.
- I haven't encountered this problem in iOS, but if you need to force-close a window or force-quit Safari:
- iOS:
(diagonal pinch gesture; window thumbnails) > tap "x" in upper left of window - iOS:
(4-finger swipe up gesture; all open apps; flick left/right if Safari not visible) > swipe up on Safari - macOS:
Safari (in Dock) > ctrl-click > Quit (or Force Quit) Safari icon > click w/ Shift key-- to reopen w/o previous windows- Win:
(task bar) > right-click (on window) > Close - [2] Win:
ctrl-alt-del > Task Manager > Applications > (browser) > Close
[1] Install an Ad-blocking Extension (aka "Content Blocker")
- Several different approaches / business models:
- 'avoidance': avoid ads in first place: find alternatives to ad-heavy sites, apps, services, e.g., Facebook, Google
- 'consensual': block all except those you allow via your 'allow list' or opt-in; e.g., Privacy Badger; too drastic? support small publishers? some publishers may detect ad blockers and block content access; some, e.g., Spotify, consider ad blocking grounds to terminate your account!
- 'acceptable ads'; block all ads except vendor allows, e.g., Adblock Plus; who decides which sites are allowed or blocked? publisher payoffs?
- 'anonymised tracking': block ads but provides summary data; e.g., Ghostery
- 'some blocking free': pay for additional blocking; e.g., Disconnect and 1Blocker
- Some (free) apps may display advertising (and track you); consider a paid version that removes ads, check tracking/ad preferences (if any), or do you really need the app?
- Before: If using HTTPS: or VPN, some ads not inserted by your ISP; a VPN may also make it more difficult for ad sites to identify you
- Before: If using WPA2 (WiFi), avoid local 'man-in-the-middle' ads/malware
- Before: if you use Safari's "Reader View" (if available), most ads, navigation and sidebars are removed
- Before: use an ad blocker to remove adds and reduce tracking
- other advantages: speeds up page loading; downloads less data, esp. important for limited data plans.
- many good extensions are free; some paid tools are waste of money, and possibly malware
- may block ads/tracking only in web browsers, not apps
- Note: OS handling of browser extensions, especially content blockers, continues to evolve
- Content blocker Steve is currently using with Safari (iOS12+, macOS 14+): Wipr: $2;
it's simple to set up, and blocks ads fast and effectively - These previously recommended general tools (& example settings) may or may not work with your system and browser:
AdBlock Plus; IronVest (Blur); Ghostery; Privacy Badger; [3] uBlock Origin - Ghostery: {Figure 12: TCYOP-4: 97; TCYOP-3: 79}
- macOS:
Safari > Preferences > Extensions > Get Extension : AdBlock Plus - macOS:
AdBlock Plus > [deselect] Allow some non-intrusive advertising - iOS:
Settings > Privacy > Advertising > Limit Ad Tracking
Enabling this will cut down on unnecessary network traffic, but doesn't totally block - iOS:
Settings > Safari > Content Blockers - If a site doesn't work properly (esp. for 'mobile-friendly' sites):
- macOS & iOS:
Safari > [press refresh icon] > Reload Without Content Blockers - iOS:
Safari > [press refresh icon] > Request Desktop Site
[2] Selectively Allow Ads: Add Sites to 'Allow List'?
- "We respect your use of an ad blocker...
- macOS:
AdBlock Plus > Disabled on this site - macOS:
AdBlock Plus > Options > Allow some non-intrusive advertising : on / off
[3] Prevent / Remove Adware
- Before: obtain software only from official app stores, and pay attention to installation options
- After: tools to remove adware, e.g., Windows: AdwCleaner
References
- {TCYOP-4: 71, 96-97, 101; TCYOP-3: 58, 78-80}
- sections: Refs: Android; Chrome; Firefox; iOS; macOS; Windows; Wipr
- Support DuckDuckGo by disabling ad blockers on our page
- Wikipedia: pop-up ad; clickbait; ad blocker/filter; Superfish
- Wikipedia: Adblock Plus, Ghostery
- Wikipedia: PrivacyBadger EFF; Firefox, Chrome "browser add-on that stops advertisers and other third-party trackers from secretly tracking where you go and what pages you look at on the web"
- HowStuffWorks: How Pop-up Blockers Work; How do advertisers show me custom ads?; How do you remove adware from your computer?
- The App Tracking Transparency (ATT) recession
Apple's effect on digital advertising and tracking; 1/11/2023 - Even the FBI says you should use an ad blocker TC; 12/22/2022
- The 10 Worst New Places You're Going to See Ads in 2023 Giz; 12/18/2022
- You're Still Being Tracked on the Internet, Just in a Different Way
Apple and Google are pushing privacy changes, but a shift in digital tracking is giving some platforms a bigger advertising advantage; NYT; 4/6/2022 - The plain-text internet is coming 3/27/2022
- Our Favorite Ad Blockers and Browser Extensions to Protect Privacy NYT; 9/30/2021
- The NSA and CIA Use Ad Blockers Because Online Advertising Is So Dangerous MB; 9/23/2021
- How Your Ad Blocker Can Track You Across the Web Giz; 8/10/2021
- Millions of web surfers are being targeted by a single malvertising group Tag Barnakle infecting ad servers; Ars; 4/19/2021
- I tried to use the ad tech industry's tool to opt out of personalized ads. Did it work? Digital Advertising Alliance (DAA) AdChoices; TNW; 3/28/2021
- 4 major browsers are getting hit in widespread malware attacks Chrome, Firefox, Edge, and Yandex are all affected in widespread ad-injection campaign; Ars; 12/10/2020
- Bizarre internet 'dot' glitch lets you watch ad-free YouTube vids and bypass paywalls PW; 6/12/2020
- Popular VPN And Ad-Blocking Apps Are Secretly Harvesting User Data Android: Free and Unlimited VPN, Luna VPN, Mobile Data, Adblock Focus; iOS: Adblock Focus, Luna VPN; BF; 3/9/2020
- Adblock Plus's Till Faida on the shifting shape of ad blocking TC; 1/21/2020
- Senator Wyden Wants Paid Ad Blocking 'Allow Lists' Investigated TD; 1/14/2020
- Browsers [Chrome, Firefox] Are Fixing the Internet's Most Annoying Problem invasive pop-ups asking for notification permission; Wired; 1/14/2020
- Your Digital Detox May Be Toxic for Advertising NYT; 1/5/2020
- Adware Is the Malware You Should Actually Worry About Wired; 7/21/2019
- How to Fight Back Against Data Broker Advertising on Facebook LH; 7/12/2019
- I Used Google Ads for Social Engineering. It Worked. ad campaigns that manipulate searchers' behavior are frighteningly easy for anyone to run; NYT; 7/7/2019
- The Best Browsers for Ad Blocking (That Aren't Chrome) Brave, Firefox, Opera, Chromium, Edge; LH; 5/30/2019
- The future of AT&T is an ad-tracking nightmare hellworld everything you watch, everywhere you go; Verge; 5/22/2019
- Apple unveils Privacy Preserving Ad Click Attribution, a new web technology aimed at preserving user privacy without reducing effectiveness of ad campaigns TC; 5/22/2019
- These Ads Think They Know You in an experiment, the NYT bought and displayed ads targeting 16 profile attributes to reveal what advertisers think they know about users seeing targeted ads; NYT; 4/30/2019
- 83% of Consumers Believe Personalized Ads Are Morally Wrong, Survey Says Forbes; 2/9/2019
- Spotify's new Terms of Service, which go into effect on March 1, will give Spotify the authority to immediately terminate accounts that use ad blockers Verge; 2/7/2019
- How to Allow Pop-Up Windows in Safari for Mac Safari > Preferences > Web Sites > Popup Windows: Block, Block&Notify, Allow; OSXD; 2/5/2019
Android
Chrome
- Here comes the Google Chrome change that worries ad blocker creators CNet; 12/9/2020
- Malicious adblockers should be removed now Chromium versions of Nano Adblocker or Nano Defender; Ars; 10/20/2020
- The Best Chrome Extensions to Prevent Creepy Web Tracking Wired; 9/25/2020
- Google debuts a Chrome extension to show how many ads are loaded on a web page, what advertisers are involved, and what user data was used for personalized ads ZD; 8/2/2020
- Chrome will soon block resource-draining ads. Here’s how to turn it on now Ars; 5/14/2020
- Google backtracks on Chrome modifications that would have crippled ad blockers ZD; 2/16/2019
- Remove All The Ads and Sponsored Products From Amazon With This Extension Amazon Lite for Chrome; LH; 1/19/2019
- Google Chrome's ad-blocking feature will roll out worldwide in July 2019 TNW; 1/10/2019
Firefox
- Firefox's address bar has ads now, but you can disable them Verge; 10/7/2021
- Mozilla set to offer ad-free browsing in Firefox for $5 7/5/2019
iOS
- 96% of US users opt out of app tracking in iOS 14.5, analytics find Ars; 5/7/2021
- To Be Tracked or Not? Apple Is Now Giving Us the Choice iOS 14.5; NYT; 4/26/2021
- How to block ad tracking on your iPhone keep your apps from uploading your data -- mostly; Verge; 3/8/2021
- The 5 Best Ad Blockers For iOS, Ranked 6/29/2020
- Webkit zero-day exploit besieges Mac and iOS users with malvertising redirects Flaw rendered ad-sandboxing protections "entirely useless," researchers say; already fixed in both Mac and iOS Safari; Ars; 9/30/2019
macOS
- The Best Safari Ad Blockers Adguard, Wipr, and 1Blocker; LH; 12/16/2022
- Ghostery Slowing Down Safari Performance? Here’s a Fix OSXD; 6/4/2022
- How to enable Reader View automatically for websites in mobile and desktop Safari MW; 1/6/2020
- Report: since Apple debuted Intelligent Tracking Prevention, the cost for advertisers to reach Safari users has dropped 60%+, as such ads are less desirable it looks to have almost totally eliminated the ability for advertisers to market to specific demographics; 12/9/2019
- 1Blocker 3 review: Safari extension revamps its content-blocking for macOS Catalina MW; 11/18/2019
Windows
- Microsoft: Microsoft Safety Scanner remove adware
- WikiHow: How to Close an Internet Pop Up; How to Get Rid of a Window That Won't Close in Windows XP
Wipr
Safer Internet: Browsing: Protect Passwords
Safer Internet: Browsing: Protect Passwords
Summary |
References : General | 1Password | Multi-Factor Authentication | Android | Apps | Biometrics; Passkeys |
Bitwarden | Breaches / HaveIBeenPwned | Browser (as PM) | Chrome | Credential Stuffing | DashLane | Edge |
Facebook | Firefox | Freq. of Changing | iCloud/KeyChain | iOS | LastPass | macOS | Password Managers |
Safari | Security Questions | SMS, SIM hijacking | SSO (Single Sign-On | Password Strength | Windows
| Non-expert Online Practices 1. Use Antivirus Software 2. Use Strong Passwords 3. Change Passwords Frequently 4. Only Visit Websites They Know 5. Don't Share Personal Info |
Expert Online Practices 1. Install Software Updates 2. Use Unique Passwords 3. Use Multifactor-Factor Authentication 4. Use Strong Passwords 5. Use a Password Manager |
Summary
- Passwords are now covered in a separate 3-session OLLI course: P@s$w0rdz
- Passwords:Intro (from earlier in this course) now summarizes highlights from P@s$w0rdz.
- This section originally provided more details about other password issues, e.g., secret answers, biometrics, 2FA, etc.
- This section now provides only Reference articles (below) [for P@s$w0rdz] -- it will continue to be updated.
References
- {TCYOP-4: 99-100; TCYOP-3: 81-83}
- e-Books: Take Control of...: Your Passwords, 1Password; Passwords cheat sheet
- haveibeenpwned.com check if you have an account that has been compromised in a data breach
- SYSTEM: Please enter your new password.
- USER: cabbage
- SYSTEM:...
- USER:...
- SYSTEM:...
- USER:...
- SYSTEM:...
- USER:...
- SYSTEM:...
- USER:...
- SYSTEM:...
- USER:...
- SYSTEM:...
- USER:...
- SYSTEM:...
- Wikipedia: Password; Authentication; Backdoor method of bypassing normal authentication
- HowStuffWorks: Authentication
- Wikipedia: Password manager; Password strength
- Wikipedia: Password entropy derived from # character choices (# of bits) * length of password
- Wikipedia: FIPS-181 Fed. Info Processing Std.: Automated Password Generator
- Wikipedia: Random password generator; Diceware
- Wikipedia: Password cracking depends on info entropy; number, speed of CPU/GPUs, # of permitted attempts;
e.g., 2008: A user-selected eight-character password with numbers, mixed case, and symbols,
reaches an estimated 30-bit strength, according to NIST. 30 is only one billion permutations
and would take an average of 16 minutes to crack - Wikipedia: salt random data that is used as an additional input to a one-way function that hashes a password or passphrase
- zxcvbn (password strength tester): testing page; intro; source code
- Beware of Attacks Using Password Reset Request Notifications TB; 3/26/2024
- Back Up and Secure Your Digital Life
product reviews: ...
Password manager: free, paid;
Two-factor authentication; ...
NYT; 3/7/2024 - Suspects can refuse to provide phone passcodes to police, court rules
phone-unlocking case law is 'total mess,' may be ripe
for Supreme Court review; Ars; 12/14/2023 - Largest Study of its Kind Shows Outdated Password Practices are Widespread GAtech; 11/17/2023
- Cloaked manages your logins with proxy emails, phone numbers and a built-in password manager $10/mo.; TC;10/3/2023
- Top Ten Password Security Standards 6/21/2023
- Everything you've been told about passwords is a lie
Aim for longer password phrases; Use a password manager if you can;
Consider two-step authentication on your important accounts;
WaPo; 1/10/2023 - A Breach at LastPass Has Password Lessons for Us All
reassess whether to trust companies to store our sensitive data in the cloud; NYT; 1/5/2023 - How to Set Up Google Password Manager's On-Device Encryption for iOS, Chrome, and Android Giz; 6/22/2022
- Steps to Simple Online Security: 1: Always use strong passwords;
2: Set Up Two-Factor Authentication NYT; 4/1/2022 - Lapsus$ found a spreadsheet of passwords as they breached Okta, documents show TC; 3/28/2022
- Why You Should Sign Into All of Your Accounts Every Now and Then
inactive accounts -- inaccessible due to invalid email address;
account deletion -- policies vary: 6 mo. - 2 years;
LH; 11/30/2021 - Why the Password Isn't Dead Quite Yet
some drawbacks to new authentication methods;
often newer devices are required; Wired; 7/6/2021 - PSA for US Congresspeople: Please do not enter your phone’s passcode on TV Verge; 5/25/2021
- How to See Who's Using Your Streaming Passwords
Netflix; Hulu; Disney+; Amazon Prime Video; Spotify; Giz; 5/3/2021 - The 5 Best Ways to Store Passwords Safely
Use your browser; 1Password; LastPass; Dashlane; NordPass; Giz; 2/9/2021 - Microsoft takes on Keychain with Autofill features on iOS, macOS
via Microsoft Authenticator app and a Google Chrome extension; ApIn; 2/6/2021 - Lost Passwords Lock Millionaires Out of Their Bitcoin Fortunes
But what happens when you can’t access that wealth because you forgot the password to your digital wallet? NYT; 1/12/2021 - Here's how many Americans still secretly use their ex's passwords
password sharing even after breakup; ZD; 10/12/2020 - How Do I Get Into My Email If I've Lost My Recovery Codes? LH; 8/7/2020
- Why Am I Locked Out of My Netflix Account? (password oversharing?) LH; 7/31/2020
- How to Change Your Email Address LH; 6/17/2020
- Neo-Nazis Are Spreading a List of Emails and Passwords for Gates Foundation and WHO Employees MB; 4/21/2020
- Silicon Valley Legends Launch Beyond Identity in Quest to Eliminate Passwords Beyond Identify; 4/14/2020
- Three old password rules that are dumb today
Don't be afraid to write down your passwords; Do share your accounts;
Don't constantly change your passwords; CNet; 3/11/2020 - How to Share Your Online Accounts Without Sharing Your Password
via password manager; Amazon Prime 'Household Package'; Spotify, Apple Music, YouTube Music: family plan;
Netflix, Hulu, Disney Plus: share pw, but setup profiles; Wired; 2/23/2020 - More than 38,000 people will stand in line this week to get a new password
on paper, at German university; ZD; 12/18/2019 - How Can I Close Accounts for Old Services I Don't Use Anymore?
Check through your email for notices, confirmations, etc.; Search for old passwords in your browser
and password managers; Google your username; Clear out permissions for other apps; LH; 12/5/2019 - Who’s Hacking Your Spotify? NYT; 12/5/2019
- Why Sharing Your Disney+ or Netflix Password Is a Bad Idea
use unique password,2FA; Giz; 11/29/2019 - Suspect can’t be compelled to reveal “64-character” password, court rules Ars; 11/23/2019
- Nikki Haley lost her password, so she sent sensitive info over unclassified system
OpenNet; Ars; 11/20/2019 - How to use Sign In With Apple and manage your log in information ApIn; 11/7/2019
- Please get your digital affairs in order password manager, backup codes; TC; 9/15/2019
- How to create a backup plan to restore passwords if your system fails
iCloud, password manager; MW; 9/3/2019 - Fernando Corbató, a Father of Your Computer (and Your Password), Dies at 93 timesharing; NYT; 7/12/2019
- Hacker Lexicon: What Is Credential Dumping? extracting usernames and passwords from a victim computer,
so that they can be used to reenter that computer at will and reach other computers on the network; Wired; 7/7/2019 - [2] A quarter of major CMSs use outdated MD5 as the default password hashing scheme
Offenders include WordPress, osCommerce, SuiteCRM, Simple Machines Forum, miniBB, MyBB,
SugarCRM, and others; ZD; 6/17/2019 - 5 alarming facts in honor of World Password Day
1. Data breaches are happening more often;
2. Data breaches are getting worse;
3. Data breaches may not be detected and reported promptly;
4. The more online accounts you have, the more vulnerable you are;
5. We can't seem to shake our bad password habits; PC; 5/2/2019 - Introducing the 1Password Internet Password Book
;-) bad handwriting is the best form of encryption; 4/1/2019 - WebAuthn: What you need to know about the future of the passwordless Web
while OS and browser makers now support the WebAuthn API,
it's unclear when and how Web sites will begin implementing it; PC; 3/7/2019 - The web just took a big step toward a password-free future
WebAuthn is here to kill the password; uses USB key or other biometrics;
already supported by most browsers (Chrome, Firefox, Edge, and Safari); Verge; 3/4/2019 - Once Again, Sharing Streaming Passwords Is Not 'Piracy' Or 'Freeloading'
most actual streaming companies view as marketing and source of new accounts; TD; 3/1/2019 - [2] Cryptocurrency wallet caught sending user passwords to Google's spellchecker
Coinomi wallet bug sends users' secret passphrases to Google's Spellcheck API via HTTP, in plaintext; ZD; 2/27/2019 - Millions of utility customers’ passwords stored in plain text and sent in plain text via email; Ars; 2/25/2019
- When Your Shared Netflix Account Outlasts The Relationship NPR; 2/14/2019
- You happily share passwords for Netflix, HBO and more, despite risks CNet; 2/12/2019
- Digital exchange loses $137 million as founder takes passwords to the grave cryptocurrency; Ars; 2/2/2019
- How to Stop Worrying About Every 'Mega' Password Breach That Comes Along
1. Enable 2FA;
2. Get a password manager;
3. Buy a physical security token, e.g., Yubikey, Google Titan;
4. Enjoy; Giz; 1/17/2019
1Password
- wikipedia, 1password.com, Take Control Books
- 1Password 8.10.26 TB; 2/23/2024
- 1Password expands its endpoint security offerings with Kolide acquisition TC; 2/20/2024
- Our Favorite Password Manager Remembers All of Your Logins So You Don’t Have To NYT; 11/24/2023
- Issues with Legacy 1Password 6 and 7 from Mac App Store
"1Password app is damaged"; TB; 11/21/2023 - 1Password detects 'suspicious activity' in its internal Okta account 1Password CTO says investigation found no compromise of user data or sensitive systems; Ars; 10/23/2023
- Two-Factor Authentication, Two-Step Verification, and 1Password not true 2FA, but 2SV; TB; 7/10/2023
- 1Password launches a passkey public beta for Chrome, Edge, Safari, Firefox, and Brave but not its mobile apps 1PW announced passkey support in Nov. 2022; Verge; 6/6/2023
- 1Password is finally rolling out passkey management
save passkeys and synchronize them across devices and platforms after 6/6; Verge; 5/16/2023 - How 1Password is designed to keep your data safe, even in the event of a breach 1PW; 1/10/2023
- Now 1Password remembers sites that use third-party accounts like Google or Facebook to log in Verge; 12/1/2022
- 1Password 8 arrives on Android and iOS with a big redesign and personalized home Verge; 8/9/2022
- 1Password now lets you securely share files and documents with just a link Verge; 6/29/2022
- Twitter pays $150M fine for using two-factor login details (phone #, email) to target ads Ars; 5/26/2022
- 1Password 8.0 TB; 5/9/2022
- 1Password 8 for Mac brings autofilling passwords to native apps Verge; 5/3/2022
- 1Password 7.9.4 TB; 4/8/2022
- Moving from 1Password to KeePass TB; 4/11/2022
- 1Password now lets you easily store crypto wallet details Verge; 2/23/2022
- 1Password 8 for Windows is here 1PW; 11/16/2021
- Psst! Now you can securely share 1Password items with anyone 1PW; 10/12/2021
- Protect your privacy with 1Password and Fastmail 1PW; 9/28/2021
- Sync options compared 9/28/2021; Is it safe to sync my data over the cloud? 11/3/2021
- [2] syncing: other folder, cloud e.g., Box, Dropbox, Google Drive, Microsoft OneDrive, SpiderOak, SugarSync; 11/12/2021
- [2] from local file e.g., USB drive; some browsers restrict access
- Guide: Setup Touch ID 9/22/2021
How safe is it to use Touch ID to secure my vault?
settings for how often to re-enter master password; 9/22/2021 - 1Password has plans to get companies to actually use one password
supplement rather than compete with SSOs like Okta; Verge; 1/21/2022 - 1Password 7.9.2 TB; 12/10/2021
- 1Password 7.9 Adds Secure Password Sharing
blog.1password.com;
one-use or expiring link, optional email verification; TB; 10/19/2021 - 1Password 7.8.8 TB; 10/11/2021
- 1Password gets its own 'hide my email' feature
Create Masked Email -- unique email aliases for logins, much like
Apple's iCloud Plus Hide My Email function but integrated and not only for Apple users;
video; Verge; 9/28/2021 - 1Password Releases Safari Extension for iOS 15 and iPadOS 15 MR; 9/20/2021
- Accel doubles down on 1Password, which just raised $100M more at a $2B valuation TC; 7/27/2021
- 1Password 7.8.5 TB; 6/3/2021
- 1Password acquires SecretHub and launches new enterprise secrets management tool TC; 4/13/2021
- How to Pay Using Virtual Credit Cards in 1Password each tied to a separate merchant
-- linked to debit card or checking account (not credit card); one-off & recurring payments;
can also use privacy.com directly w/o 1PW; LH; 9/24/2020 - Toronto-based password manager 1Password raises $200M Series A
led by Accel, its first external round of funding in its 14-year history; 11/14/2019
Multi / 2 Factor Authentication (2FA) / 2 Step Verification
- Wikipedia: Two factor authentication; multi-factor authentication
- Wikipedia: Two step verification; One-time Password (OTP); TOTP = Time-based OTP
- List of websites and whether or not they support 2FA
- Apple: Apple ID (iCloud, iTunes, App Store) Frequently asked questions about two-step verification
- Apple: Two-factor authentication for Apple ID upgrade from 2-step verification; 5/11/2017
- Google: 2-Step Verification Authenticator (app); App Passwords; Backup codes
- Authy Desktop to Reach End-of-Life on 19 March 2024 TB; 2/14/2024
- The Best Security Key for Multi-Factor Authentication NYT; 1/5/2024
- How to Automatically Delete Passcode Texts on Android and iOS Wired; 8/6/2023
- Google Authenticator finally, mercifully adds account syncing for two-factor codes
but it's not E2EE (end-to-end encrypted) yet; Verge; 4/24/2023 - How to set up two-factor authentication on your online accounts Verge; 4/14/2023
- Still using authenticators for MFA? Software for sale can hack you anyway
AitM (adversary in the middle) works by placing a phishing site between the user and the desired site; Ars; 3/14/2023 - The Best Two-Factor Authentication App Authy; NYT; 7/27/2022
- How to set up two-factor authentication for your Apple ID and iCloud account MW; 5/5/2022
- Getting started with 2FA: Add an extra layer of protection to your passwords MW; 5/5/2022
- How to add your verification codes to Apple Passwords
iOS/iPadOS 15, Safari 15 for macOS; MW; 4/5/2022 - Lapsus$ and SolarWinds hackers both use the same old trick to bypass MFA Ars; 3/28/2022
- More than 1,200 phishing toolkits capable of intercepting 2FA detected in the wild stealing authentication cookies; 12/27/2021
- How to Manually Get Apple 2FA Codes on Mac OSXD; 12/17/2021
- Google wants every account to use 2FA, starts auto-enrolling users Ars; 11/3/2021
- The Booming Underground Market for Bots That Steal Your 2FA Codes
user cooperation necessary; Vice; 11/2/2021 - The White House's Plan to Stop Government Employees From Getting Phished
focus on hardware security keys; Vice; 10/15/2021 - How Coinbase Phishers Steal One-Time Passwords 10/13/2021
- Google is about to turn on two-factor authentication by default for millions of users
set up the Inactive Account Manager while you still can; Verge; 10/5/2021 - How to move Google Authenticator to your new iPhone ApIn; 9/24/2021
- You Should Use Your iPhone's New Built-in Two-Factor Authentication
instead of 3rd-party app; LH; 9/23/2021 - Microsoft adds a passwordless option for Microsoft accounts
In place of a password, Microsoft will use its Microsoft Authenticator app for your phone,
Windows Hello, and codes sent to your email or phone; PC; 9/15/2021 - Wireless Carrier Injects Ads Into Two-Factor Authentication Texts TD; 7/1/2021
- This Agency's Computers Hold Secrets. Hackers Got In With One Password.
New York City's Law Department had old unpatched software, did not implement 2FA; NYT; 6/18/2021 - Google will make two-factor authentication mandatory soon PC; 5/6/2021
- How to set up two-factor authentication for your Apple ID and iCloud account MW; 5/4/2021
- Why You Should Use a Physical Key to Sign Into Your Accounts Giz; 4/30/2021
- Two-Factor Authentication: Who Has It and How to Set It Up PCMag; 4/27/2021
- How to Move Google Authenticator Account to a New iPhone OSXD; 1/27/2021
- No emails have leaked from the 2020 election campaigns yet
-- tiny USB sticks may be one reason why CNBC; 12/23/2020 - Trump Twitter 'hack': Police accept attacker's claim BBC; 12/16/2020
- SolarWinds hackers have a clever way to bypass multi-factor authentication Ars; 12/14/2020
- With Google Authenticator's Latest iOS Update, You Really Have No Excuse Now
like Android version, supports account transfer to a different device; Giz; 12/3/2020 - Use 2FA to Stop This New WhatsApp Account Attack LH; 11/28/2020
- Microsoft urges users to stop using phone-based multi-factor authentication
use app-based authenticators and security keys instead; ZD; 11/12/2020 - A Dutch security researcher says he logged into Trump's Twitter account,
which didn't have 2FA, using the password 'maga2020!'
the account has now been secured w/ 2FA; 10/22/2020 - Gatekeeper Two-Factor Authentication review: Needs a consumer-grade overhaul
GateKeeper Wireless Security Key; PC; 10/15/2020 - Zoom’s mobile and desktop apps now support two-factor authentication previously only available via the web; Verge; 9/11/2020
- How to transfer your Google Authenticator 2FA to a new phone Verge; 9/2/2020
- Musk says Tesla two-factor authentication 'embarrassingly late' but coming soon Verge; 8/15/2020
- Apple has finally embraced key-based 2FA. So should you Advanced Protection Program (APP); Ars; 7/17/2020
- How Two-Factor Authentication Keeps Your Accounts Safe Wired; 7/12/2020
- [2] Choosing 2FA authenticator apps can be hard. Ars did it so you don’t have to
technical; doesn't discuss 1Password at all (except in reader comments); Ars; 5/27/2020 - No-password logon surges for Microsoft services to 150 million people
three no-password logon options for its online services on Windows machines:
a hardware security key combined with Windows Hello face recognition technology or fingerprint ID;
a hardware key combined with a PIN code;
or a phone running the Microsoft Authenticator app; CNet; 5/7/2020 - Google will switch on mandatory two-factor authentication for Nest accounts this month TH; 5/5/2020
- You Should Set Up Two-Step Verification on Your Nintendo Account Right Now LH; 4/20/2020
- How to bypass Apple’s multi-device two-factor system with Messages auto-fill except uses SMS; MW; 3/24/2020
- How Do I Switch From One 2FA Authentication App to Another? LH; 3/13/2020
- Microsoft: 99.9% of compromised accounts did not use multi-factor authentication
Only 11% of all enterprise accounts use a MFA solution overall; ZD; 3/6/2020 - What you need to know about security keys on iOS and macOS e.g., YubiKey; ApIn; 3/2/2020
- Researchers find an Android malware strain Cerberus that can extract and steal
one-time passwords generated by Google's Authenticator mobile app ZD; 2/27/2020 - Google now treats iPhones as physical security keys Verge; 1/15/2020
- Alternative Ways to Protect Yourself from Being Spearfished
Prioritize Your Accounts;
Use Strong, Unique Passwords & 2FA;
Provide Fake Answers to Security Questions;
Think You're Important;
Your Cell Phone Number Is the Weak Link;
The Problem With Authenticator Apps (most poorly designed);
Google Voice as an Alternative to Authenticator Apps and Cell Phone Numbers; TB; 1/31/2020 - The Best Authenticator Apps for Protecting Your Accounts
Google Authenticator; Microsoft Authenticator; Authy; LastPass; Duo Mobile;
(it didn't mention 1Password); Giz; 1/1/2020 - Does Apple ID two-factor work if you leave the country?
Make sure you know what devices and phone numbers you trust
(e.g., set up a free or inexpensive phone number that can receive text messages,
e.g., Google Voice or Skype); MW; 12/10/2019 - How to add trusted phones to your Apple ID two-factor authentication MW; 12/3/2019
- Twitter will finally let you turn on two-factor authentication without giving it a phone number
You could switch to another option later (like Google Authenticator, or a physical Yubikey)
-- but to turn it on in the first place, you were locked into giving Twitter a phone number
and using SMS; TC; 11/21/2019 - [2] Why One Secure Platform Passed on Two-Factor Authentication Keybase; Wired; 10/25/2019
- What Happens If I Use Two-Factor Authentication and Lose My Phone?
write down your backup codes; use a 3rd-party authentication app, such as Authy;
get a replacement phone for backup SMS authentication codes; what to do if you
get locked out (and haven't prepared); LH; 10/18/2019 - No One Knows About Two-Factor Authentication, and It's Putting Their Security at Risk
28% can identify (Pew survey); LH; 10/9/2019 - Beware a New Scam That Asks for Your Bank PIN on the Phone LH; 10/9/2019
- Twitter Took Phone Numbers for Security and Used Them for Advertising MB; 10/8/2019
- How to use 2FA on older Apple devices that won't let you enter a verification code MW; 8/14/2019
- How to Set Up Two-Step Authentication on Your Amazon Account LH; 7/6/2019
- I'll be passing on Google’s new 2fa for logins on iPhones and iPads Ars; 6/12/2019
- What is two-factor authentication, and which 2FA solutions are best? PC; 6/5/2019
- Here Are the Best Account Security Methods, According to Google LH; 5/22/2019
- Here's the Best Way to Protect Your Accounts From Hacker Takeovers
security key or device-based (rather than knowledge-based) challenges; LH; 5/17/2019 - When 2FA isn't 2FA: How Apple's iCloud authentication system fails to protect your account MW; 4/12/2019
- Two-factor authentication explained: How to choose the right level of security for every account PC; 4/10/2019
- How to set up two-factor authentication on all your online accounts
Apple, Instagram, Facebook, Twitter, Amazon, Google, Snapchat, Slack, Microsoft,
Dropbox, WhatsApp, PayPal, Nest, Signal; Verge; 3/27/2019 - Protecting Your Internet Accounts Keeps Getting Easier. Here's How to Do It.
four methods for setting up two-factor authentication; 1. text-messaged codes, e.g., Instagram;
2. authenticator app, e.g., Facebook; 3. Google Prompt, e.g., gmail; 4. physical key, e.g., Twitter; NYT; 3/27/2019 - [3] How to Set Up Two-Factor Authentication for Multiple Apple IDs on One Device MR; 2/20/2019
- [2] How to use two-factor authentication on popular PC gaming platforms
Steam; GOG Galaxy; EA’s Origin; Battlenet; Uplay; Epic Games; TNW; 2/19/2019 - [3] Apple to require two-factor authentication for developer accounts ApIn; 2/13/2019
- Push notifications are the future of multi-factor authentication
verifies the identity of users by sending a push notification to a mobile device associated
with their account during the login process; TNW; 2/9/2019 - Apple being sued because two-factor authentication on an iPhone or Mac takes too much time
and abusive since it can't be rolled back to a less safe login method after 14 days; ApIn; 2/9/2019 - Two-Factor Authentication Might Not Keep You Safe still vulnerable to phishing attacks; NYT; 1/27/2019
Android
- Your mobile password manager might be exposing your credentials "AutoSpill": Android autofill; TC; 12/6/2023
- How to Use Your Android Phone's Built-In Password Manager LH; 5/12/2022
- Google Authenticator’s first Android update in years lets you move your account between devices Verge; 5/6/2020
- Now you can use Android phones, rather than passwords, to log in to Google*
* = For now, fingerprint or lock screen authentication applies only to one Google service; Ars; 8/12/2019 - Google says any Android device running 7.0 or later can now be used as a security key
for two-factor authentication Verge; 4/10/2019 - With latest version of Google Play Services, Android 7.0 and up now supports the FIDO2 standard
which lets users login to services using fingerprints or PIN Verge; 2/25/2019
Apps
- Use an application to encrypt a file (.txt, .doc, spreadsheet, .pdf)
-- assuming AES-128 or AES-256 (better) level encryption, with latest version of software. - Microsoft Office (2016-; 365-); Acrobat (X -)
- compression utils.: WinZip (9.0-); 7-Zip; Keka
- discussion: P@s$w0rdz: Storing: Secure (Encrypt) Your Passwords
Biometrics, Fingerprints, Facial Recognition; Passkeys
- Biometrics; Fast IDentity Online (FIDO)
- HowStuffWorks: How will biometrics affect our privacy?
- I Stopped Using Passwords. It's Great -- and a Total Mess
Passkeys are here to replace passwords. When they work, it's a seamless vision of the future.
But don't ditch your old logins just yet; Wired; 2/8/2024 - Google begins prompting users to create passwordless passkeys by default Verge; 10/10/2023
- Passkeys: all the news and updates around passwordless sign-on Verge; 9/29/2023
- Windows 11 gains support for managing passkeys TC; 9/21/2023
- 1Password rolls out public passkey support to its mobile apps and web extensions Verge; 9/20/2023
- Passkey: Which popular apps and services offer the new feature? ApIn; 9/6/2023
- How to use Passkeys on your iPhone, iPad, and Mac MW; 6/22/2023
- 1Password is finally rolling out passkey management
save passkeys and synchronize them across devices and platforms after 6/6; Verge; 5/16/2023 - Passkeys may not be for you, but they are safe and easy -- here's why
answering common questions about how passkeys work; Ars; 5/12/2023 - How to Use Passkeys on Your iPhone or Mac LH; 5/11/2023
- Embrace the Passwordless Future of Passkeys LH; 5/9/2023
- Google's passkey offering is refined and comprehensive enough to recommend but the ecosystem is incomplete, despite PayPal, Kayak, and others using passkeys; Ars; 5/8/2023
- Google now lets you access your account with passkeys rather than passwords TC; 5/3/2023
- 1Password is trying for zero passwords
create and unlock 1Password accounts using biometric-based passkey tech; Verge; 2/9/2023 - Everything to Know About Passkeys for a Password-Free Future passkeys; NYT; 1/11/2023
- The Password Isn't Dead Yet. You Need a Hardware Key Wired; 12/30/2022
- The passwordless experience you deserve passkeys; 1PW; 11/17/2022
- Dashlane is ready to replace all your passwords with passkeys Verge; 8/31/2022
- Why Passkeys Will Be Simpler and More Secure Than Passwords TB; 6/27/2022
- Apple ‘passkeys’ could finally kill off the password for good TC; 6/6/2022
- Another Step Toward a Password-Free Future TB; 5/5/2022
- Apple, Google, and Microsoft will soon implement passwordless sign-in on all major platforms
unlocking phone to enable access; Verge; 5/5/2022 - Some of tech's biggest names want a future without passwords -- here's what that would look like CNBC; 4/24/2022
- A Big Bet to Kill the Password for Good
after a decade of work, the FIDO Alliance says it's found the missing piece in the bridge to a password-free future; Wired; 3/17/2022 - What You Need to Know About Facial Recognition at Airports NYT; 2/26/2022
- IRS will end use of facial recognition after widespread privacy concerns
ID.me facial recognition/sign-in issues; Verge; 2/7/2022 - The smart toilet era is here! Are you ready to share your analprint with big tech? Guard; 9/23/2021
- Researchers Create 'Master Faces' to Bypass Facial Recognition MB; 8/10/2021
- Apple demos passkeys, to let users set up accounts with just Face ID or Touch ID,
joining Microsoft and Google in advocating for passwordless authentication CNet; 6/10/2021 - John Gruber Analyzes Apple's Secure Intent TB; 6/4/2021
- How to Log In to Your Devices Without Passwords Wired; 4/11/2021
- Inside FIDO Alliance's vision of a future free of passwords
FIDO2 combines W3C's Web Authentication (WebAuthn) specification and FIDO Alliance’s
corresponding Client-to-Authenticator Protocol (CTAP). This allows you to use your phone
or laptop to identify yourself safely to a web service. To reduce the risk of phishing or
any other attacks, the FIDO2 method doesn't involve storing your credentials on a server.
Instead, it uses features such as biometric authentication to validate your identity so the
password never leaves your device; TNW; 10/9/2020 - Face ID and Touch ID Logins Coming to Websites With Safari Web Authentication API 6/24/2020
- The case for biometric authentication -- and why we should ditch passwords TNW; 6/6/2020
- Apple is making iPhones easier to unlock without Face ID while many wear masks CNet; 4/29/2020
- How to turn off Face ID and use a PIN to unlock your iPhone instead e.g., if wearing mask; TNW; 4/17/2020
- Attackers can bypass fingerprint authentication with an ~80% success rate:
using fake fingerprints for ~20 attempts fine for most people, but it's hardly foolproof; Ars; 4/8/2020 - This Smart Toilet Will Know You by the Shape of Your A*****e MB; 4/7/2020
- How YubiKey Bio could make remote security concerns a thing of the past PC; 3/31/2020
- Google Pixel 4 face unlock works even when you're unconscious
Your eyes don't need to be open to access the phone; CNet; 10/18/2019 - Samsung says it will issue a patch for a fingerprint recognition bug on its
Galaxy S10 phone that allowed any fingerprint to unlock the phone Reut; 10/17/2019 - [2] Biometrics using ear canals Giz; 9/19/2019
- How to Thwart Facial Recognition
1) disappear: go offline and off the grid; 2) flood the system with weird, incongruous data.
Wear someone else's likeness or lend out your own; NYT; 7/30/2019 - The Pentagon has a laser that can identify people from a distance—by their heartbeat
unique cardiac signature from 200 meters away, even through clothes; MIT; 6/27/2019
Bitwarden
- wikipedia, bitwarden.com
- Bitwarden begins adding passkey support to its password manager Verge; 11/2/2023
- Best Free Password Manager need a LastPass Alternative? Bitwarden; CNet; 9/22/2023
- Bitwarden review: This free password manager has few restrictions, and little polish PC; 8/25/2022
Breaches / HaveIBeenPwned
- How to verify a data breach TC; 3/15/2024
- Have I Been Pwned adds almost 71M email addresses tied to stolen accounts from the Naz.API dataset
it allegedly contains 1B+ lines of stolen credentials; BC; 1/18/2024 - Troy Hunt (pwned) scours the dark web for your stolen data 9/22/2023
- What to Do if Your Password Is Exposed in a Data Breach Giz; 7/27/2022
- The NCA shares 585 million passwords with Have I Been Pwned
UK National Crime Agency; US FBI had shared earlier; 12/20/2021 - Have I been Pwned (HIBP) goes open source
HIBP will now also receive compromised passwords discovered in the course of FBI investigations; ZD; 5/27/2021 - How to tell if your password has been stolen
HaveIBeenPwned; Hass-Platner-Institut;
Google Password Checkup; Firefox Lockwise; Microsoft Edge Password Monitor;
password managers: LastPass, Dashlane, 1Password; PC; 2/10/2021 - Have I Been Pwned is going open source tells you if passwords were breached; Verge; 8/7/2020
- How Have I Been Pwned became the keeper of the internet’s biggest data breaches
10 billion+ breached accounts; TC; 7/3/2020 - After a breach, users rarely change their passwords, and when they do, they're often weaker
to make things worse, users' new passwords were overall more similar to passwords they use on other accounts; 5/27/2020 - 10 Billion Wrecked Accounts Show Why You Need 'Have I Been Pwned' LH; 4/9/2020
Browser (as PM)
- Hackers can force iOS and macOS browsers to divulge passwords and much more speculative execution, WebKit; Ars; 10/25/2023
- How to Access Saved Passwords in Chrome OSXD; 5/8/2023
- How to Check for Reused & Compromised Passwords in Safari for Mac OSXD; 7/22/2021
- Why your browser's password manager isn't good enough
browser-specific; mobile support? less robust than standalone PM; PC; 1/25/2021 - Chrome and Edge want to help with that password problem of yours Ars; 1/22/2021
- Safari Autofill on Mac: How to Add Logins & Passwords, How to Update & Edit Saved Passwords OSXD; 9/8/2020
- How to Use Chrome, Firefox, or Safari to Change All of Your Bad Passwords
check for bad, vulnerable pw; a PM still preferable; LH; 7/14/2020 - [2] Easily Reveal Hidden Passwords In Any Browser LH; 12/5/19
Chrome
- Chrome's password safety tool will now automatically run in the background Verge; 12/21/2023
- How to Delete Your Autofill Passwords in Chrome (and Move to Something More Secure) LH; 5/9/2022
- How to Manage Your Passwords in Google Chrome LH; 5/28/2021
- Chrome now uses Duplex to fix your stolen passwords TC; 5/18/2021
- How to View Saved Passwords in Chrome on Mac OSXD; 6/18/2020
- Chrome Will Automatically Scan Your Passwords Against Data Breaches Wired; 12/15/2019
- Google's Chrome 79 will warn you if your password has been stolen—or will be PC; 12/10/2019
- Google's new Password Checkup tells you if your accounts can be compromised
Chrome; reused, compromised and weak passwords; PC; 10/2/2019 - Google's Password Checkup plugin for Chrome can warn you if your password was stolen PC; 2/5/2019
Credential Stuffing
- FBI says credential stuffing attacks are behind some recent bank hacks ZD; 9/14/2020
- One out of every 142 passwords is '123456'
'123456' was spotted 7 million times across a data trove of one billion leaked credentials,
in one of the biggest password re-use studies of its kind; average password length is
usually of 9.48 characters; most security experts recommend using passwords as long
as possible, and usually in the realm of 16 to 24 characters, or more; only letters (29%);
only numbers (13%); include special character (12%); ZD; 7/2/2020 - Hundreds of Thousands of People Are Using Passwords That Have Already Been Hacked, Google Says
New ‘Password Checkup' Chrome extension found 1.5 percent of all website logins use
compromised credentials, a figure that's higher for porn websites; MB; 8/15/2019 - Hacker Lexicon: What Is Credential Stuffing?
attackers take a massive trove of usernames and passwords (often from a corporate megabreach)
and try to "stuff" those credentials into the login page of other digital services. Because people
often reuse the same username and password across multiple sites, attackers can often use
one piece of credential info to unlock multiple accounts; Wired; 2/17/2019
DashLane
- wikipedia, dashlane.com
- Dashlane Authenticator app discontinued 5/13/2024 3/28/2024
- Dashlane is getting rid of its insecure master password Verge; 5/3/2023
- Dashlane publishes its source code to GitHub in transparency push TC; 2/2/2023
- Dashlane's new $3.99 password manager plan is cheaper but might not beat free
unlimited passwords but only on 2 devices; Verge; 4/29/2021 - Profile of the popular password management app Dashlane, which has raised $110M last spring
and is airing its first ever Super Bowl ad Superbowl ad: Password Paradise; Wired; 2/2/2020
Edge
- Microsoft Edge can finally generate new passwords for you PC; 1/21/2021
- Microsoft Edge can now auto-generate passwords, but only via your phone PC; 12/16/2020
- One million Facebook users had passwords stolen by fake apps ApIn; 10/7/2022
- Facebook Did Not Securely Store Passwords. Here's What You Need to Know. NYT; 3/21/2019
- Facebook has urged users to enable phone number-based 2FA,
but the numbers are used in a user lookup feature with no opt out and to target ads
Settings > Mobile: remove all numbers; setup 2FA with an authenticator app/PM; TC; 3/3/2019
Firefox
- Mozilla will end support for Firefox Lockwise app
still available via Firefox's desktop and mobile browsers;
CNet; 11/23/2021 - The Firefox password manager now tells you when you use leaked passwords
Firefox Lockwise; Firefox Monitor: checks whether a website has suffered a security breach; ZD; 5/5/2020 - How to Recover Your Missing Firefox Passwords LH; 6/18/2019
- Firefox to Warn When Saved Logins are Found in Data Breaches via partner haveibeenpwned.com; BC; 7/17/2019
- Firefox to get a random password generator, like Chrome ZD; 6/27/2019
Frequency of Changing
- Microsoft says mandatory password changing is "ancient and obsolete" Ars; 6/3/2019
- Microsoft drops password expiration requirement
with the Windows 10 May 2019 Update, suggests organizations implement other
password security practices; Ars; 4/25/2019
iCloud
- Using Apple's iCloud Passwords Outside Safari TB; 4/1/2024
- Why iCloud Keychain asks for an old device's password -- and why you don't need to worry MW; 7/4/2023
- How a Passcode Thief Can Lock You Out of Your iCloud Account, Possibly Permanently TB; 4/20/2023
- How to Use Apple's New All-In-One Password Manager Wired; 4/11/2023
- What kinds of passwords, tokens, and keys can Apple manage for you? MW; 3/24/2023
- How to update your passwords with Apple's Security Recommendations MW; 3/16/2023
- If both your iPhone and passcode get stolen, you're in deep trouble ApIn; 2/24/2023
- How to use iCloud Keychain on Windows and how it differs from macOS and iOS ApIn; 8/1/2022
- The macOS Monterey user's guide to Keychain Access password management ApIn; 7/29/2022
- How to use Apple's Keychain password manager in Google Chrome TNW; 2/1/2021
- How to use iCloud Keychain, Apple's built-in and free password manager ApIn; 2/14/2022
- How to use iCloud Keychain, Apple's built-in and free password manager ApIn; 12/29/2021
- If you lock a file in Apple's Notes, don't lose your password MW; 12/27/2021
- How to Install iCloud Passwords Extension on Microsoft Edge OSXD; 12/4/2021
- [2] How to use Keychain Access to view and manage passwords on your Mac MW; 11/18/2021
- How to Import and Export Passwords From iCloud Keychain to Other Password Managers
requires macOS Monterey; LH; 10/29/2021 - Add Two-Factor Codes to Password Entries in iOS 15, iPadOS 15, and Safari 15 TB; 10/7/2021
- You Should Use Your iPhone's New Built-in Two-Factor Authentication
instead of 3rd-party app; LH; 9/23/2021 - Designate Account Recovery and Legacy Contacts
only iCloud+ ($); MW; 6/8/2021 - iCloud 12.5 for Windows finally lets you manage passwords in Keychain MW; 8/16/2021
- How to master your passwords using iCloud Keychain MW; 5/6/2021
- How to set up two-factor authentication for your Apple ID and iCloud account MW; 5/4/2021
- How to take control of your passwords using iCloud Keychain on your iPhone, iPad, and Mac MW; 2/15/2021
- Apple releases Chrome extension for iCloud passwords Verge; 1/31/2021
- Why iCloud Keychain may prompt you for a device password used with other Apple hardware you own
Apple doesn't store your password; MW; 1/25/2021 - How to share a password via AirDrop from iOS 14, iPadOS 14, or macOS
from KeyChain, even if iCloud syncing off; MW; 10/23/2020 - How to Reset Keychain on Mac OSXD; 7/29/2020
- How to Create a New Keychain on Mac OSXD; 7/25/2020
- iPhone & iPad (KeyChain): How to Manually Add Passwords; How to Edit Saved Passwords,
How to Find Duplicate Passwords OSXD; 6/21/2020 - Apple's iOS 14 may turn iCloud Keychain into a true 1Password and LastPass competitor 2FA support; Verge; 4/1/2020
- How to Use iCloud Keychain on iPhone & iPad OSXD; 3/30/2020
- macOS Keychain Security Flaw Discovered by Researcher
but Details Not Shared With Apple Over Bug Bounty Protest; MR; 2/6/2019
iOS
- Wikipedia: Touch ID 4-digit PIN: 10,000 possibilities; fingerprint 50,000 but only 5 tries; stored locally not in cloud
- Apple: If you forgot the passcode for your Apple Watch 11/3/2022
- Apple: Use Touch ID instead of your passcode 3/17/2022
- Apple: About Touch ID security on iPhone and iPad 9/11/2017
- 1Password & Touch ID
- Apple to Introduce Stolen Device Protection in the Upcoming iOS 17.3 TB; 12/14/2023
- How iOS 15.4 could finally eliminate password hell MW; 2/7/2022
- How to Get Verification Codes For Apple ID on iPhone & iPad OSXD; 9/8/2021
- How to Check for Compromised or Leaked Passwords on iPhone & iPad with Security Recommendations OSXD; 2/5/2021
- How to check if your passwords saved in Keychain were compromised on iOS 14 TNW; 10/16/2020
- How to Generate Strong Passwords on iPhone and iPad using iCloud KeyChain; how strong? editable? 9/24/2020
- How to Use Third Party Password Managers on iPhone & iPad Instead of Keychain OSXD; 6/10/2020
- How to Turn Off Screen Time Password on iPhone or iPad OSXD; 3/15/2019
LastPass
- wikipedia, lastpass.com
- Multifactor Authentication
- LastPass now requires 12-character master passwords for better security BC; 1/3/2024
- Experts Fear Crooks are Cracking Keys Stolen in LastPass Breach Krebs; 9/5/2023
- Lastpass Publishes More Details about Its Data Breaches TB; 3/3/2023
- LastPass says employee's home computer was hacked and corporate vault taken Ars; 2/27/2023
- Additional GoTo Data Stolen in the LastPass Breach TB; 1/26/2022
- LastPass Data Breach: It's Time to Ditch This Password Manager Wired; 12/28/2022
- LastPass users: Your info and password vault data are now in hackers' hands
“Encrypted fields [username, passwords, notes] remain secured with 256-bit AES encryption
and can only be decrypted with a unique encryption key derived from each user's master password"; Ars; 12/22/2022 - LastPass warns users of 'security incident' that may have exposed personal data MW; 12/1/2022
- LastPass developer systems hacked to steal source code
user passwords/vaults should be safe; BC; 8/25/2022 - LastPass no longer requires a password to access your vault Eng; 6/6/2022
- Some LastPass users say their master passwords were compromised and used in blocked login attempts from unknown IPs; LastPass blames “credential stuffing” BC; 12/28/2021
- Big Changes Are Coming to LastPass, but Unfortunately Not Its Prices Giz; 12/14/2021
- LastPass is going to become an independent company Verge; 12/14/2021
- How to Export LastPass Passwords OSXD; 6/20/2021
- Security researcher finds seven embedded trackers in the Android app for LastPass password manager
LastPass says users can opt out if they want; Reg; 2/25/2021 - How to leave LastPass and move to another password manager Verge; 2/24/2021
- LastPass's free password manager is about to become a lot less useful
free tier will limit you to one type of device starting 3/16; PC; 2/16/2021 - LastPass will warn you if your passwords show up on the dark web paid subscription only; En; 8/5/2020
- LogMeIn lays off more than 300 workers Boston Biz Journal; 2/21/2020
- Watch Out for Lastpass' New Log-off Bug LH; 2/7/2020
- LastPass to Drop Support for Native Mac App and Replace it With Universal Web App MR; 1/30/2020
- LastPass is in the midst of a major outage
issue appears to impact users with accounts dating back to 2014 and earlier; ZD; 1/20/2020 - LogMeIn sells to private equity firms for $4.3 billion
parent of LastPass supposedly "becoming a private company will help fuel its next phase of growth and product investment"
(S: often private equity acquisitions don't have such rosy outcomes); ZD; 12/17/2019 - LastPass Parent Company (LogMeIn) Sold to Private Equity Firms PC; 12/18/2019
- Password-exposing bug purged from LastPass extensions
bug could let malicious websites extract your last used password; Ars; 9/16/2019 - What Happened When the DEA Demanded Passwords from LastPass Forb; 4/10/2019
macOS
- Apple: Frequently asked questions about two-step verification for Apple ID
- How to Recover Recently Deleted Passwords on Mac OSXD; 10/18/2023
- macOS Monterey Features Dedicated Password Section in System Preferences,
Built-In Authenticator and More MR; 6/11/2021 - How to Find Forgotten / Lost Web Site Passwords on Mac OSXD; 7/27/2020
- [2] How to find and insert special characters in macOS MW; 2/11/2019
SSO (Single Sign-On); OAuth
- Wikipedia: Single Sign On (SSO); OpenID users authenticated by certain co-operating sites
(known as Relying Parties or RP) using a third party service; security issues - Wikipedia: OAuth open standard for authorization; security issues
- OpenID / OAuth allow you to use your Google, Twitter, Facebook credentials to log into other sites
- You Can Disable Google Sign-in Pop-ups on All Websites LH; 12/20/2022
- She clicked sign-in with Google. Strangers got access to all her files. WaPo; 10/24/2022
- Behold, a password phishing site that can trick even savvy users Ars; 3/21/2022
- How to Use 'Sign In With Apple' on iPhone & iPad to Hide Email from Apps & Signups OSXD; 8/5/2020
- Remove Apps Linked to Your Facebook Account That You're Not Using LH; 7/3/2020
- How Google's New 'One Tap' Android Sign-Ins Work
how secure if someone can access your device or Google account? LH; 6/16/2020 - Sign in with Apple FAQ: What you need to know about Apple's single sign-on feature
compared with Facebook, Google, or Twitter sign-in options:no tracking;
fake email with free anonymous email forwarding; requires 2FA;
(also usable on non-Apple devices; still avail on fewer SSO sites?); MW; 4/7/2020 - Your smart watch will soon log you into your accounts without a password TNW; 10/23/2019
- ‘Sign In With Apple' Is Way Better Than Passwords -- If You Can Find It
anonymized email address; no personal info sharing (like Google, Facebook); WSJ; 9/18/2019 - Google bans logins from embedded browser frameworks to prevent MitM phishing
Google previously banned logins initiated from browsers where JavaScript had been disabled; 4/18/2019 - Behold, the Facebook phishing scam that could dupe even vigilant users
HTML block almost perfectly reproduces Facebook single sign-on Window; single sign-on, or SSO,
is a feature that allows people to use their accounts on other sites -- typically Facebook, Google,
LinkedIn, or Twitter—to log in to third-party websites; security and cryptographic mechanisms
under the hood usually allow the the login to happen without the third party site ever seeing
the username password; Ars; 2/16/2019
Password Managers
- Wikipedia: password manager; 1Password; Bitwarden; Dashlane; KeePass
- HowStuffWorks: How Password Management Software Works
- Our Favorite Password Manager Remembers All of Your Logins So You Don’t Have To NYT; 11/24/2023
- Best Password managers to protect your data on iOS and macOS
Keychain, 1Password, Bitwarden, Dashlane, Keeper, NordPass; ApIn; 11/4/2023 - Are password managers safe? 1PW
- The Best Password Managers to Secure Your Digital Life discussion of browsers and passkeys;
Bitwarden, 1Password, Dashlane, Nordpass, Enpass, KeePassXC; Wired; 12/5/2023 - Best password manager to use CNet; 8/19/2023
- Best password managers: Reviews of the top products PC; 8/8/2023
- Proton launches its password manager Proton Pass TC; 6/28/2023
- Best free password managers: Better online security doesn't have to cost a thing
Best free password manager for most people: Bitwarden
Best free password manager for DIYers: KeePass
Best free password manager for simplicity: Google, Apple, or Firefox
Free vs. paid password managers; PC; 4/13/2023 - Proton releases end-to-end encrypted password manager for desktop and mobile TC; 4/20/2023
- The Best Password Managers NYT; 3/1/2023
- KeePass disputes vulnerability allowing stealthy password theft BC; 1/30/2023
- NortonLifeLock warns that hackers breached Password Manager accounts BC; 1/13/2023
- Seven free alternatives to the LastPass password manager
Bitwarden; Zoho Vault; Dashland; KeePass;
LogMeOnce; NordPass; RoboForm;
Verge; 1/6/2023 - Bitwarden vs. LastPass CNet; 8/29/2022
- Mindpass Password Manager makes 3D password control super simple
4 sequence of objects, similar to 4 word phrase; gimmick? MW; 6/5/2022 - Why 1Password Is Now the Best Password Manager for Mac LH; 5/20/2022
- Best password managers for Mac MW; 5/5/2022
- McAfee Total Protection review: A new look, but more work is needed
to improve the experience with its password manager; PC; 3/1/2022 - LastPass vs. 1Password: Which password manager should you use? CNet; 1/13/2022
- 7 of the Best Password Managers to Choose From Before (Firefox) Lockwise Shuts Down
Firefox Browser; Bitwarden; LastPass;
iCloud Keychain; 1Password; KeePass;
Dashlane; LH; 12/6/2021 - Best Password Manager Tools for Linux
LastPass; Keeper; KeePass; SpiderOak Encryptr; EnPass; RoboForm; Buttercup; Bitwarden; Passmgr; 8/25/2021 - LogMeOnce review: The passwordless password manager
master password still needed to create vault, but biometric, numeric PIN, and/or photo can access; PC; 8/17/2021 - NordPass review: Streamlined password management PC; 7/29/2021
- Vulnerability in the Kaspersky Password Manager
generated guessable "random" passwords; 7/6/2021 - Backdoored password manager stole data from as many as 29K enterprises Passwordstate; Ars; 4/23/2021
- Isn't local storage better for password database security?
in the end, the use of any well-regarded password manager is more secure than most people’s habits,
regardless of where the password data is stored; PC; 4/14/2021 - Mastering your password manager: 5 must-know tips PC; 3/18/2021
- Should I Keep Using My Password Manager? if it's not in Top 10? e.g., Roboform; LH; 11/27/2020
- 5 Password Manager Perks You Might Not Be Using
Check for Compromised Accounts;
Find Sites That Support Two-Factor Authentication;
Store IDs and Credit Cards;
Share Passwords With Other People;
Safely Store Your Important Documents; Wired; 8/21/2020 - Password manager showdown: LastPass vs. 1Password 8/14/2020
- Dropbox launches password manager, computer backup, and secure ‘vaults’ out of beta 8/12/2020
- Apple announces open-source project for password manager developers ApIn; 6/5/2020
- Trend Micro Password Manager review: Basic and a little buggy PC; 5/28/2020
- Now's The Perfect Time to Start Using a Password Manager Wired; 5/24/2020
- The best password managers in 2020 Dashlane, LastPass, Keeper, Enpass, 1Password, Zoho Vault, RoboForm; Toms; 5/8/2020
- How Do I Access My Work Passwords From My Home Devices? Chrome sync; password managers; LH; 3/27/2020
- Roboform Everywhere review: Solid password security PC; 11/20/2019
- Password Boss review: Managing your passwords with authority PC; 11/7/2019
- Keeper review: Security is the greatest strength of this password manager PC; 10/30/2019
- It Is Time to Outsource Your Passwords to an App Your brain has better things to do than store secure passwords.
Get a dedicated password manager to keep your login data synced and secure across all devices;
The Best Password Managers to Secure Your Digital Life (abridged version); Wired; 10/22/2019 - Why You Need a Password Manager. Yes, You.
aside from using two-factor authentication and keeping your operating system and Web browser
up-to-date, it’s the most important thing you can do to protect yourself online; NYT; 9/2/2019 - Don't be an idiot -- here's how to store and remember all your passwords LastPass, 1Password; TNW; 8/25/2019
- Best Password Managers 2019 Tom; 8/23/2019
- The Best Password Managers BitWarden, KeePass, LastPass, 1Password; from readers; LH; 7/5/2019
- [2] Before You Use a Password Manager excessive(?) critique; 6/5/2019
- 4 Best Password Managers of 2019 (Paid, Family, and Free)
1Password, Dashlane, LastPass, KeePassXC; Wired; 5/26/2019 - [2] Severe vulnerabilities uncovered in popular password managers
passwords stored in RAM could lead to theft, only if attacker has already compromised
your Windows system; ZD; 2/20/2019 - Forgot password? Five reasons why you need a password manager
Browser Integration; Password Generation; Phishing Protection; Cross Platform Access; Surveillance Safeguard
plus debunking these questions:
"I already have a perfectly good system for managing passwords."
"If someone steals my password file, they have all my passwords."
I don't trust someone else to store my passwords on their server."
"I'm not a target."; ZD; 2/7/2019 - Data of 2.4 million Blur password manager users left exposed online
company says data breach didn't expose any actual passwords stored inside users' Blur accounts; ZD; 1/2/2019
Questions
- These Phishing Tactics Disguised as 'Fun' on Social Media. Here's What to Look For CNet; 3/27/2022
- Choosing and Using Security Questions Cheat Sheet 2021
- Online Security Questions Are Not Very Effective. I Still Love Them. NYT; 7/15/2021
- Why Social Media Name Games Are a Security Risk seemingly innocuous personal information
(your full name + the street your grew up on + your first car, etc.); LH; 12/15/2020 - Why You Shouldn't Play That 'Fun Quarantine Game' on Facebook
the answers to all those fun games are also the same things you might enter when you’re trying
to verify your identity on a website in order to reset your password; LH; 4/16/2020 - Why you should steer clear of "Florida Man Challenge"
some posts/sites ask for personal info: maiden name, pet, street, etc.; Ars; 3/24/2019
Safari
- When Safari flashes a 'Compromised Password' warning, pay attention MW; 11/30/2021
- How to Import Passwords & Logins from Chrome to Safari on Mac OSXD; 1/23/2021
- How to get a Safari password to save it in a password manager iOS, macOS; MW; 8/16/2019
- macOS browser now autosubmits logins. Here's how to disable it MW; 4/15/2019
- How to use Safari's saved passwords in other Mac apps ApIn; 1/4/2019
SMS, SIM swapping/hijacking
- Google backs Apple's SMS OTP standard proposal
for humans: 747723 is your WEBSITE authentication code.
for browser/apps: @website.com #747723
benefits? autofill, reduce phishing (but not SMS hijacking); ZD; 4/7/2020 - How to Tell if You're the Victim of a SIM-Swapping Attack LH; 1/14/2020
- Hackers Are Breaking Directly Into Telecom Companies to Take Over Customer Phone Numbers MB; 1/10/2020
- 'SIM-Swap' Scams Expose Risks Of Using Phones For Secondary I.D. NPT; 10/25/2019
- T-Mobile Has a Secret Setting to Protect Your Account From Hackers That It Refuses to Talk About
NOPORT setting can protect your phone number from SIM swapping; MB; 9/13/2019
Password Strength; Diceware
- Wikipedia: List of the most common passwords
- SplashData: List of current 100 worst
- Articles about each year's 'worst 25' list: 2019; 2018; 2017; 2016; 2015; 2014; 2013; 2012; 2011 mostly Gizmodo
- password lists
- Wikipedia: Diceware
- XKCD cartoon: correct horse battery staple
- How to Calculate Password Entropy?
- EFF: How to Make Super-secure Passwords using Dice
- Passwordle guess a 12-char password
- TV Tropes: Embarrassing Password; The Password Is Always "Swordfish"
It seems that most characters in fiction missed the memo on making a good Secret Word or pass phrase.
They are almost invariably single words, names, or dates of significance to a character which can be
easily deduced using a little detective work: the clue is often right there on the desk, in the form of
a picture or memento. Or simply spelled out in bold lettering on your commemorative plaque or a wall poster. - Dumb Password Rules list of sites
- A "ridiculously weak" password causes disaster for Spain's No. 2 mobile carrier Ars; 1/4/2023
- Iran-linked cyberattacks threaten equipment used in U.S. water systems and factories hackers used "1111" default password; NPR; 12/2/2023
- We cracked more than 18,000 passwords. Here are our tips. multifactor authentication; passphrases; WaPo; 8/2/2023
- The Password Game Is Fun, Frustrating, and Educational TB; 6/30/2023
- The Password Game will make you want to break your keyboard in the best way game; Ars; 6/28/2023
- People Sure Are Bad at Creating Passwords LH; 6/14/2023
- A fifth of passwords used by federal agency cracked in security audit
89% of the department's high-value assets didn't use multi-factor authentication; Ars; 12/10/2023 - Make Your Passwords Stronger With These 5 Tips CNet; 5/5/2022
- Never Change Your Password
1) If it's sufficiently strong;
2) If you created a unique one for each account
3) Unless there's a security breach where it's stored;
TB; 3/5/2022 - The 20 Most Commonly Leaked Passwords on the Dark Web MF; 3/3/2022
- Olympics Broadcaster Announces His Computer Password on Live TV
video; MB; 7/26/2021 - Russian Military Hackers Have Been On a Worldwide Password Guessing Spree
according to U.S. and U.K. government officials, the Russian cyber spies of Unit 26165
have been using brute force attacks to target hundreds of organizations; Giz; 7/1/2021 - Did weak wi-fi password lead the police to our door?
BBC; 5/23/2021 - How to create strong, secure passwords by learning how to crack them
it gets harder to crack a password if it's 10 characters or longer
-- but complexity matters too, of course. PC; 5/5/2021 - COMB: The Big Password Leak intl; pw reuse; 4/26/2021
- How to pick the perfect password PC; 4/6/2021
- Breached water plant employees used the same TeamViewer password and no firewall Ars; 2/10/2021
- Rules for strong passwords don't work, researchers find. Here's what does CNet; 11/12/2020
- The Police Can Probably Break Into Your Phone
phone-hacking tools typically exploit security flaws to remove a phone's limit on passcode attempts
and then enter passcodes until the phone unlocks. Because of all the possible combinations,
a six-digit iPhone passcode takes on average about 11 hours to guess, while a 10-digit code takes 12.5 years; NYT; 10/21/2020 - A computer can guess more than 100 billion passwords per second -- still think yours is secure? TNW; 9/22/2020
- 'DiceKeys' Creates a Master Password for Life With One Roll Wired; 8/21/2020
- 'Weird' Nintendo Switch Issue Makes it Easier to Guess Passwords
highlights ok when first 8 characters entered correctly; MB; 5/22/2020 - Suspected DNC & German Parliament Hacker Used His Name As His Email Password TD; 5/6/2020
- FBI recommends passphrases over password complexity
Longer passwords, even consisting of simpler words or constructs, are better than
short passwords with special characters; ZD; 2/21/2020 - It's Time to Nervously Mock the 50 Worst Passwords of the Year Giz; 12/18/2019
- 'Iloveyou' and the 24 Other Worst Passwords of 2019 LH; 12/18/2019
- Disney+ 'hack' panic stresses why you need to use unique passwords
bad password behavior is more to blame than a breach on Disney’s part; PC; 11/18/2019 - This Bank Had the Worst Password Policy We've Ever Seen
A European bank (FinecoBank) makes customers pay to change their passwords,
and suggests they Google their password to check if it is secure; MB; 11/15/2019 - Equifax used 'admin' as username and password for sensitive data 10/18/2019
- [2] Forum cracks the vintage passwords of Ken Thompson and other Unix pioneers Ars; 10/10/2019
- 600,000 GPS trackers left exposed online with a default password of '123456' ZD; 9/5/2019
- When a Company Asks You to Reset Your Password, Should You Be Worried?
may be proactive, not actual attack, but change anyway; LH; 8/23/2019 - Instead of Changing Your Passwords, Upgrade Them LH; 7/8/2019
- Most hacked passwords revealed as UK cyber survey exposes gaps in online security 4/21/2019
- Why 'ji32k7au4a83' Is a Remarkably Common Password
'ji32k7au4a83' (Taiwanese keyboard transliteration) translates to English as 'my password'; Giz; 3/4/2019 - Use an 8-char Windows NTLM password? Don't. Every single one can be cracked in under 2.5hrs
NTLM is an old Microsoft authentication protocol that has since been replaced with Kerberos,
but it's still used for storing Windows passwords locally or in Active Directory; Reg; 2/14/2019
Windows
- Microsoft Has a New Trick for Keeping Your Password Safe
Warn me about password reuse; Warn me about unsafe password storage; LH; 9/26/2022 - How to type special characters on a Windows 11 PC Verge; 4/26/2022
- How to type special characters on a Windows PC Verge; 3/26/2021
Safer Internet: Browsing: Search Privately
Safer Internet: Browsing: Search Privately
Quotes | Summary | Search Providers | Search Suggestions | Local Search |
References: General | AI | Apple | Bing | DuckDuckGo | Google | iOS | macOS
Quotes
- "The Web site you seek...
- Google won't search for Chuck Norris because...
- SEARCH ENGINES ARE SILLY...
- "We have compiled a list of nine proofs which definitively prove Google is...
- "Q: What did the turkey say to the computer?...
- "Knowledge is of two kinds...
Summary
- "Free" search services are big business,
e.g., Apple may have been paid $9.5B by Google in 2018 to stay default Safari search option - [1] Change Search Provider, e.g., DuckDuckGo or StartPage
to eliminate/minimize search profile stored by provider - [2] Turn Off Search Suggestions to further improve privacy
- [2] Check Local Search Settings
- [2] Unclutter search results with a browser extension?
- References
[1] Change Search Provider
- Most 'free' search providers (aka 'engines'), e.g., Google, Bing, store identifiable search history remotely on server
- Change search provider to one that does not collect your search data, e.g., DuckDuckGo
- macOS:
Safari > Preferences > Search - macOS:
Firefox > Preferences > Search - macOS:
Firefox > Preferences > Privacy > History > Location Bar - macOS:
Chrome: duckduckgo.com; click button: 'Add DuckDuckGo to Chrome'; help - macOS:
Chrome > Preferences > Search > Manage Search Engines > Make Default - note: if using an ad blocker, you might consider allowing DuckDuckGo
to show a few ads; section: Browsing : Block Ads - iOS:
Settings > Safari > Search Engine - If you relied on Home page or new window to access search site, e.g., google.com, be sure to change there also
- macOS:
Safari > Prefs > General > New Window Opens With & Homepage[screenshot] - If you find that you don't like the new search results (format, number, etc.),
you can easily switch to a different search engine -- just be sure to read the privacy policy - If you'd still prefer Google searches for some results, use startpage.com, which is more private
- Other private search sites/engines: search.brave.com; ecosia.org; peekier.com; qwant.com
- Deleting Search History or using Private Browsing -- see earlier section Browsing : Managing Data
- FrogFind (powered by DuckDuckGo) is optimized for vintage computers and browsers,
including the Newton, by converting the search result pages to extremely basic HTML. - [2] Some search engines support "right to be forgotten" (content about you) -- submit a form on Bing or Google site
[2] Turn Off Search Suggestions
- If you're not using Private Browsing, do you want to share your searches or see others' phrases?
- Maybe speed things up, reduce crashes
- macOS:
Safari > Preferences > Search > Include Safari Suggestions - iOS:
Settings > Safari > Search Engine Suggestions - If you're using a smart home device, e.g., Amazon Alexa, Google Home, check search engine settings;
also settings for search history & suggestions
[2] Check Local Search Settings
- Allow internet searches in 'local' search results; settings only in older versions < macOS 10.12, < iOS 10?
- macOS:
System Preferences > Spotlight > [list] Spotlight Suggestions [off] - macOS:
System Preferences > Spotlight >
[checkbox] Allow Spotlight Suggestions in Look up [off] - iOS:
Settings > Siri & Search > Suggestions in Search [?],specify by app
Suggestions in Lookup [?] - iOS: access Spotlight search:
1) while on the Home screen, pull down from anywhere between the status bar and Dock;
2) from the Lock screen or first page of the Home screen, swipe right to enter the Widgets screen,
which features a Spotlight search box - It's unclear if Spotlight still uses Bing rather than your preferred search engine
- Allow Siri request logging?
- iOS:
Settings > General > Siri > About Siri and Privacy (read)
References
- {TCYOP-4: 101-102; TCYOP-3: 83-85}
- sections: Refs: AI; Apple; Bing; DuckDuckGo; Google; iOS; macOS
- also Browsing:Correct Site:Web Archives, Newspapers
- Wikipedia: internet search engines: Yahoo
- Wayback Machine 475 billion web pages saved over time
- HowStuffWorks: How Internet Search Engines Work
- Ethical.net: Search engines
- Private and Secure Web Search Engines: DuckDuckGo, Brave, Kagi, Startpage Wired; 11/26/2023
- Neeva, the would-be Google competitor, is shutting down its search engine
privacy first, ad-free, $5/mo.; Verge; 5/20/2023 - The Ask Jeeves-ification of online search Verge; 5/12/2023
- Five Things Scammers Are Hoping You Google [Company] customer service number;
Free credit report; High paying remote job; Free people finder; Best crypto wallet; LH; 5/4/2023 - There's Already a Better Search Engine Than Google. It's YouTube. NYT; 2/3/2023
- 8 Google Alternatives: How to Search Crypto, the Dark Web, and More
how to surf in more private and more environmentally friendly ways; Giz; 2/1/2023 - A New Chat Bot Is a 'Code Red' for Google's Search Business NYT; 12/21/2022
- How to Use ChatGPT and Still Be a Good Person NYT; 12/21/2022
- The New Chat Bots Could Change the World. Can You Trust Them? NYT; 12/10/2022
- The best search engines to use, if you're tired of Google
Bing, DuckDuckGo, Brave Search, Ecosia, Startpage, Ask.com, Yahoo; ApIn; 11/10/2022 - How a Burner Browser Hides My Most Embarrassing Internet Searches
Firefox Focus, DuckDuckGo, Tor Browser; NYT; 5/17/2022 - This Digital Library Contains Answers to All the Mysteries of the Universe, If You Can Find Them LH; 10/18/2021
- How to Set Ecosia as the Default Search Engine on iPhone & iPad OSXD; 10/9/2021
- How to Make Your Web Searches More Secure and Private
Brave; DuckDuckGo; Limiting Google; Wired; 7/11/2021 - How to Opt Out of the Most Popular People Search Sites LH; 3/4/2021
- Brave Is Launching a Privacy-First Search Engine to Take On Google Giz; 3/3/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing;
DuckDuckGo for Search; OsmAnd for Maps; ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020 - 9 Browser Extensions to Help You Search the Web Better Wired; 12/6/2020
- US Library of Congress launches AI tool that lets you search 16 million old newspaper pages for historical images
dataset includes more than 1.5 million newspaper photos: Newspaper Navigator; TNW; 9/16/2020 - How Link-Begging Became the Most Annoying Search Engine Tactic MB; 8/3/2020
- US federal and state authorities are asking detailed questions about how to limit Google's search business,
as part of antitrust investigations according to DuckDuckGo CEO; Bloom; 6/4/2020 - How to change your default search engine on Google Chrome TNW; 3/13/2020
- Is Yahoo's [Verizon's] New 'OneSearch' Engine Good for Privacy? LH; 1/16/2020
- Verizon offers no-tracking search engine, promises to protect your privacy
with "OneSearch," Verizon promises no cookie tracking or personal profiling; Ars; 1/14/2020 - How to Opt Out of the Most Popular People Search Sites
Family Tree Now, Whitepages, Spokeo, Instant Checkmate, Pipl; LH; 12/12/2019 - Five Custom Searches You Should Enable In Your Browser Right Now
Search for pages within the past year on Google;
Search Wikipedia for TV episodes or music albums;
Get driving directions to an address via Google Maps;
Search whatever site you're currently viewing;
Search any site you can think of: Look up words in a Dictionary or Thesaurus;
Translate words on Google; Find out if a website is down for the count; LH; 11/7/2019 - How to Change Firefox's Default Search Engine for Private Browsing
in Firefox 71, different engines can specified for regular vs. private browsing; LH; 10/8/2019 - 6 Google Tricks That Will Turn You Into an Internet Detective (many other search engines support also);
Use quotation marks to find a specific phrase; Exclude words with the minus sign; Narrow your search to a specific time period;
Search your favorite sites with the "site:" operator; Add search shortcuts to your browser's address bar;
Find the source of a photo with reverse image search; NYT; 8/21/2019 - Endless AI-generated spam risks clogging up Google's search results Verge; 7/2/2019
AI
- OpenAI's ChatGPT LLM (Large Language Model); GPT (Generative Pretrained Transformer)
- Google's Bard LaMDA (Language Model for Dialogue Applications)
- Ten Ways AI Will Change Democracy 11/13/2023
- The Humane AI Pin is a bizarre cross between Google Glass and a pager Ars; 11/10/2023
- Chatbots May 'Hallucinate' More Often Than Many Realize
when summarizing facts, ChatGPT technology makes things up about 3%
of the time, according to research from a new start-up.
A Google system’s rate was 27 percent; NYT; 11/6/2023 - An Industry Insider Drives an Open Alternative to Big Tech’s A.I. Allen Institute for AI; NYT; 10/19/2023
- IBM Tries to Ease Customers’ Qualms About Using Generative A.I.
NYT; 9/28/2023 - Doomsayers, Reformers and Warriors: The Bitter Battle for the Future of A.I.
a contest about control and power, about how resources should be distributed
and who should be held accountable; NYT; 9/28/2023 - The Internet Is About to Get Much Worse
AI vs. human content creators; NYT; 9/23/2023 - What OpenAI Really Wants Wired; 9/5/2023
- A New Worry for a New College Year: A.I.-Generated Admissions Essays
A.I. chatbots could facilitate plagiarism on college applications or
democratize student access to writing help. Or maybe both; NYT; 9/1/2023 - The A.I. Revolution Is Coming. But Not as Fast as Some People Think. NYT; 8/29/2023
- AI Glossary: Basic Terms All ChatGPT Users Should Know CNet; 8/28/2023
- What’s the future of generative AI? An early view in 15 charts McKinsey; 8/25/2023
- How Schools Can Survive (and Maybe Even Thrive) With A.I. This Fall NYT; 8/24/2023
- A jargon-free explanation of how AI large language models work Ars; 7/31/2023
- 'A certain danger lurks there': how the inventor of the first chatbot turned against AI Joseph Weizenbaum & Eliza; Guardian; 7/25/2023
- Google Tests A.I. Tool That Is Able to Write News Articles NYT; 7/20/2023
- We're Using A.I. Chatbots Wrong. Here's How to Direct Them.
to mitigate the production and spread of misinformation from chatbots,
we can steer them toward high-quality data; NYT; 7/20/2023 - 'Human Beings Are Soon Going to Be Eclipsed' NYT; 7/13/2023
- AI Fatalism Won't Help Us Deal With Its Actual Risks
What is AI? Challenges posed by today’s AI systems;
Is AI really an existential risk for humanity? Giz; 7/2/2023 - Uncensored Chatbots Provoke a Fracas Over Free Speech NYT; 7/2/2023
- The True Threat of Artificial Intelligence digital neoliberalism; NYT; 6/30/2023
- The Huge Power and Potential Danger of AI-Generated Code
programming can be faster when algorithms help out, but there is evidence
AI coding assistants also make bugs more common; Wired; 6/29/2023 - How Christopher Nolan Learned to Stop Worrying and Love AI Wired; 6/20/2023
- America Is Dangerously Lonely Ezra Klein on Her; NYT; 6/20/2023
- AI shakes up way we work in three key industries
professional services, filmmaking and coding are among the
first to use the technology in everyday operations; FT; 6/17/2023 - Humans Aren't Mentally Ready for an AI-Saturated 'Post-Truth World'
the AI era promises a flood of disinformation, deepfakes, and hallucinated "facts."
Psychologists are only beginning to grapple with the implications. Wired; 6/18/2023 - The Optimist's Guide to Artificial Intelligence and Work
A.I. can complement human labor rather than replace it; Workers can focus on different tasks;
New technology can lead to new jobs; NYT; 5/20/2023 - Silicon Valley Confronts the Idea That the ‘Singularity’ Is Here NYT; 6/11/2023
- A Univ. of Vienna philosopher used ChatGPT to create a 40-minute church service
including the sermon, prayers, and music, led by four AI-generated avatars; AP; 6/10/2023 - How Could A.I. Destroy Humanity? NYT; 6/10/2023
- The A.I. Revolution Will Change Work. Nobody Agrees How. NYT; 6/10/2023
- Big Tech Is Bad. Big A.I. Will Be Worse. political and economic oppression by tech giants; NYT; 6/9/2023
- Marc Andreessen Is (Mostly) Wrong This Time Why AI Will Save the World; Wired; 6/8/2023
- New A.I. Chatbot Tutors Could Upend Student Learning
children as test subjects for A.I. experiments? NYT; 6/8/2023 - Not Just Math Quizzes: Khan Academy’s Tutoring Bot Offers Playful Features
Khanmigo allows students to chat with simulated historical figures or co-write stories with the software; NYT; 6/8/2023 - 'The machines we have now are not conscious'
Sci-fi writer Ted Chiang:'intelligence' vs. applied statistics; FT; 6/2/2023 - ChatGPT took their jobs. Now they walk dogs and fix air conditioners WaPo; 6/2/2023
- AI researchers say ChatGPT and rival chatbots are significantly less capable in languages
other than English, exacerbating the bias against non-English speakers Wired; 5/31/2023 - Big Tech Isn't Prepared for A.I.'s Next Chapter open source is changing everything; Slate; 5/30/2023
- A.I. Poses ‘Risk of Extinction,’ Industry Leaders Warn NYT; 5/30/2023
- The Race to Make A.I. Smaller (and Smarter)
BabyLM: teaching fewer words to large language models; NYT; 5/30/2023 - Is Generative AI Bad for the Environment? carbon footprint; Giz; 5/28/2023
- We Blew It With the Internet. Let's Not Blow It With A.I.
distraction and division; reliability, trustworthiness; filtering the noise; deeper insights and connections;
Beyond the 'Matrix' Theory of the Human Mind; Ezra Klein; NYT; 5/28/2023 - Get the Best From ChatGPT With These Golden Prompts
privacy, accuracy caveats; "Act as if." "Tell me what else you need to do this."
"Use the framework of (a book)"; NYT; 5/25/2023 - AI Is Steeped in Big Tech’s 'Digital Colonialism' Wired; 5/25/2023
- A.I.'s Threat to Jobs Prompts Question of Who Protects Workers NYT; 5/24/2023
- The incredible creativity of deepfakes -- and the worrying future of AI TED 2023
- ChatGPT Is Already Changing How I Do My Job journalism; NYT; 4/21/2023
- A.I.-Generated Content Discovered on News Sites, Content Farms and Product Reviews
Findings in two new reports raise fresh concerns over how AI may transform
the misinformation landscape online; NYT; 5/19/2023 - A.I. Is Having a 'Netscape Moment'
allow people to recognize the possibilities around an existing technology, leading to new innovation; NYT; 5/19/2023 - To See One of A.I.'s Greatest Dangers, Look to the Military NYT; 5/19/2023
- In Battle Over A.I., Meta Decides to Give Away Its Crown Jewels
is it dangerous to publicly release its latest A.I. technology so people can build their own chatbots? NYT; 5/18/2023 - Another Side of the A.I. Boom: Detecting What A.I. Makes
identify whether photos, text and videos are made by humans or machines; NYT; 5/18/2023 - 10 Signs That the AI 'Revolution' Is Spinning Out of Control Giz; 5/17/2023
- OpenAI CEO Sam Altman plans to tell Congress that AI regulation is "essential"
stress the need for government flexibility, and recommend safety measures; FinTimes; 5/16/2023 - Microsoft Says New A.I. Shows Signs of Human Reasoning NYT; 5/16/2023
- Help! My Political Beliefs Were Altered by a Chatbot!
AI assistants may be able to influence users without them being aware; WSJ; 5/13/2023 - You’re Probably Underestimating AI Chatbots
Just as the first iPhone reviews mostly missed the device’s huge potential,
it's folly to draw conclusions from today’s unrefined technology; Wired; 5/12/2023 - Law firms and companies' legal teams are experimenting with AI tools
that can handle work done by entry-level lawyers potentially reducing billable hours; WSJ; 5/11/2023 - Google's answer to ChatGPT is now open to everyone in US
Bard; many features, more languages, image inputs; Ars; 5/10/2023 - The disappearing computer -- and a world where you can take AI everywhere
Imran Chaudhri; TED 2023; video, transcript - AI gains "values" with Anthropic's new Constitutional AI chatbot approach
list of guiding AI values draws on UN Declaration of Rights -- and Apple's terms of service; Ars; 5/10/2023 - What if AI could rebuild the middle class? NPR; 5/9/2023
- AI machines aren’t 'hallucinating'. But their makers are
Hallucination #1: AI will solve the climate crisis;
Hallucination #2: AI will deliver wise governance;
Hallucination #3: tech giants can be trusted not to break the world;
Hallucination #4: AI will liberate us from drudgery;
wealthiest companies in history unilaterally seizing the sum total of human knowledge that exists in digital,
scrapable form and walling it off inside proprietary products, many of which will take direct aim at the humans
whose lifetime of labor trained the machines without giving permission or consent; Naomi Klein; Guardian; 5/8/2023 - What Does Sentience Really Mean?
the fact that AI isn't alive doesn't mean it can't be sentient,
the sociologist Jacy Reese Anthis argues; Atlantic (paywall); 5/8/2023 - ChatGPT is powered by these contractors making $15 an hour NBC; 5/6/2023
- AI text generators are quietly authoring more of the internet
possiblty fewer clients buying human-written content; WaPo; 5/6/2023 - Will A.I. Become the New McKinsey?
as it's currently imagined, the technology promises to concentrate wealth and disempower workers.
Is an alternative possible? Ted Chiang; New Yorker; 5/4/2023 - Can We Build Trustworthy AI? motives, incentives, capabilities; who trained it and benefits? Giz 5/4/2023
- A.I. Could Actually Be a Boon to Education Khan; NYT; 5/3/2023;
The Amazing AI Super Tutor for Students and Teachers Sal Khan; Khan Academy; TED; 5/1/2023 - Meta warns malware actors are increasingly spreading their infrastructure across platforms
it has blocked 1,000+ ChatGPT-themed malicious URLs since 3/2023; Wired; 5/3/2023 - My Weekend With an Emotional Support A.I. Companion
"Pi" assists people with their wellness and emotions; NYT; 5/3/2023 - UO experts to weigh in on the use of AI in higher education 5/3/2023
- We Must Regulate A.I. Here's How. Lisa Khan, FTC; NYT; 5/3/2023
- We Are Opening the Lids on Two Giant Pandora's Boxes Friedman; NYT; 5/2/2023
- This company adopted AI. Here's what happened to its human workers NPR; 5/2/2023
- How Do We Ensure an A.I. Future That Allows for Human Thriving? Gary Marcus; NYT; 5/2/2023
- AI is being used to generate whole spam sites fake news stories and blog posts; Verge; 5/2/2023
- When A.I. Chatbots Hallucinate NYT; 5/1/2023
- 'The Godfather of A.I.' Leaves Google and Warns of Danger Ahead Geoff Hinton; NYT; 5/1/2023
- Quiz: Can You Tell the Difference Between ChatGPT and a Doctor?
a new study found the AI answers online medical questions better and more empathetically than real doctors; Giz; 4/30/2023 - Watch an A.I. Learn to Write by Reading Nothing but ...
Jane Austen and Shakespeare; Federalist Papers; transcripts of the TV show “Star Trek: The Next Generation”;
“Moby Dick”; Harry Potter novels; NYT; 4/27/2023 - 6 Tips for Using ChatGPT to Brainstorm Better Wired; 4/27/2023
- 10 of the First Things You Should Try With ChatGPT
quickly convert time zones; book recommendations;
plan your next holiday; solve programming problems;
write (or punch up) your resume; summarize long YouTube videos;
quickly create calendar events; solve math problems;
discover new music; summarize long articles, e.g., summarize .pdfs; LH; 4/25/2023 - How Artificial Intelligence Can Aid Democracy Slate; 4/21/2023
- Want More Out of Generative AI? Here Are 9 Useful Resources Wired; 4/18/2023
- How 35 Real People Use A.I.
"It's like collaborating with an alien."
"Everything is becoming much easier."
"It feels like I've hired an intern."
"What used to take me around a half-hour to write now takes one minute."
"It’s enormous fun."
Plan gardens, workouts, meals;
Make a gift (book); Design parts for spaceships; Organize a messy computer desktop;
Write a wedding speech, write an email Get a first read; Get feedback on fiction; Play devil’s advocate;
Build a clock that gives you a new poem every minute; Organize research for a thesis;
Skim dozens of academic articles; Cope with ADHD and dyslexia; Sort through an archive of pictures;
Transcribe a doctor’s visit into clinical notes; Appeal an insurance denial; Write Excel formulas;
Get homework help; Learn Chinese; Get help when English is your second language;
Create an app when you’ve never coded before; Fix bugs in your code; Play Pong or 3D games;
Build entirely new games; Teach people to curl like a pro; Create new proteins in minutes;
Identify diseases in banana plants; Draw like Sol LeWitt; Describe entire Dungeons & Dragons worlds;
Make a Spotify playlist; Play with language; NYT; 4/14/2023 - Can Intelligence Be Separated From the Body? NYT; 4/11/2023
- Why A.I. Might Not Take Your Job or Supercharge the Economy Ezra Klein; NYT; 4/7/2023
- Why ChatGPT and Bing Chat are so good at making things up Ars; 4/6/2023
- ChatGPT vs Google Bard: Which is better? we put them to the test in 7 categories; Ars; 4/5/2023
- NYT tech series:
How to become an expert on A.I. part 1; 3/27/2023;
How Does ChatGPT Really Work? part 2: large language model (LLM), Generative Pretrained Transformer (GPT); 3/28/2023;
What Makes A.I. Chatbots Go Wrong? part 3: hallucinating software; 3/29/2023;
How Should I Use A.I. Chatbots Like ChatGPT? part 4: LLMs are already good at a wide variety of tasks; 3/30/2023;
What's the future for A.I.? part 5; 3/31/2023 - Tinkering With ChatGPT, Workers Wonder: Will This Take My Job? NYT; 3/28/2023
- Can a Machine Know That We Know What It Knows? theory of mind; NYT; 3/27/2023
- A.I. Is Being Built by People Who Think It Might Destroy Us NYT; 3/27/2023
- If We Don’t Master A.I., It Will Master Us Yuval Harari; NYT; 3/24/2023
- The Best ChatGPT Alternatives Worth Checking Out Giz; 3/23/2023
- The A.I. Chatbots Have Arrived. Time to Talk to Your Kids.
experiment together; talk about how chatbots make you feel;
get to know the technology and its limitations; stay on top of new developments; NYT; 3/22/2023 - The Age of AI has begun Bill Gates; 3/21/2023
- Our New Promethean Moment Tom Friedman; NYT; 3/21/2023
- A.I. Is About to Get Much Weirder. Here’s What to Watch For. Ezra Klein; NYT; 3/21/2023
- Testing Google Bard NYT; 3/21/2023
- 10 Ways GPT-4 Is Impressive but Still Flawed NYT; 3/14/2023
- This Changes Everything Ezra Klein; NYT; 3/12/2023
- The False Promise of ChatGPT Noam Chomsky; NYT; 3/8/2023
- The Chatbots Are Here, and the Internet Industry Is in a Tizzy NYT; 3/8/2023
- Why Chatbots Sometimes Act Weird and Spout Nonsense NYT; 2/19/2023
- ChatGPT Is a Blurry JPEG of the Web
lossy vs. lossless compression; blurriness vs. fabrication;
'hallucinations' as compression artifacts; NewYorker; 2/9/2023 - The Chatbot Search Wars Have Begun Wired; 2/9/2023
- OpenAI Used Kenyan Workers on Less Than $2 Per Hour to Make ChatGPT Less Toxic Time; 1/18/2023
- Artificial Intelligence and The Matter with Things
Dr. Iain McGilchrist, keynote video; AI World Summit 2022;
neuroscientist McGilchrist's latest book: The Matter with Things: Our Brains, Our Delusions and the Unmaking of the World - Knowledge Navigator video about intelligent assistant; Apple; 1987
Apple (generally)
- see also: Refs:iOS; Refs:macOS
- Wikipedia: Spotlight system-wide search feature of Apple's OS X and iOS operating systems
- Lawsuit Says Google Pays Apple to Keep Away From Internet Search Market 1/4/2022
- Apple develops alternative to Google search Ars; 10/28/2020
- Apple may launch its own web-based search engine ApIn; 8/27/2020
- Spotlight: Don't take your Mac's powerful search engine for granted MW; 4/10/2019
Bing
- Wikipedia: Bing
- Bing (Yes, Bing) Just Made Search Interesting Again NYT; 2/8/2023
DuckDuckGo
- Wikipedia: DuckDuckGo
- DuckDuckGo Releases Its Own ChatGPT-Powered Search Engine, DuckAssist
mostly answers from Wikipedia; Giz; 3/8/2023 - DDG has a tracker blocking carve-out linked to Microsoft contract
DuckDuckGo's mobile browsers do not block advertising requests made by Microsoft scripts on non-Microsoft web properties; TC; 5/24/2022 - Fed Up With Google, Conspiracy Theorists Turn to DuckDuckGo
DuckDuckGo uses Bing search engine; NYT; 2/23/2022 - DuckDuckGo's Quest to Prove Online Privacy Is Possible Wired; 6/16/2021
- Privacy-focused search engine DuckDuckGo is growing fast BC; 9/16/2020
- A Feisty Google Adversary Tests How Much People Care About Privacy
DuckDuckGo displays ads at the top of each search page.
But unlike others, it does not track the online behavior of its users to personalize the ads; NYT; 7/15/2019 - Google quietly adds DuckDuckGo and other privacy-focused search engines as an option
for Chrome users in more than 60 markets based on new usage statistics; TC; 3/13/2019 - Privacy-focused search engine DuckDuckGo announces it will use Apple Maps
to power map and address-related searches using Apple's MapKit JS framework; Verge; 1/15/2019 - DuckDuckGo denies using fingerprinting to track its users 'false positive'; 1/7/2019
- Why should I use DuckDuckGo instead of Google? 10 Reasons:
1. Google tracks you. We don't.
2. Block Google trackers lurking everywhere.
3. Get unbiased results, outside the Filter Bubble.
4. We listen (and respond).
5. We don’t try to trap you in our 'ecosystem.'
6. We have !bangs to search other sites directly, e.g., !w (wikipedia), !a (amazon)
7. We strive for a world where you have control over your personal information.
8. Our search results aren't loaded up with ads.
9. Search without fear.
10. Google is simply too big, and too powerful; 1/2019
- Wikipedia: Google
- myactivity.google.com: view/remove search history
- view cached page result for a site -- usually via menu on search results page,
or webcache.googleusercontent.com e.g., https://webcache.googleusercontent.com/search?q=cache:http://example.com/;
similar to web.archive.org - Google Says Switching Away From Its Search Engine Is Easy. It's Not. NYT; 9/20/2023
- Why You Need to Stop Clicking Sponsored Google Links LH; 2/27/2023
- Your Google Searches Are Quietly Evolving. Here’s What's Next Wired; 11/21/2022
- Here's How to Use Google's New Privacy Tool to Scrub Your Personal Info From Search Results MF; 10/5/2022
- The Best Google Search Alternatives if Privacy Is Your Thing
DuckDuckGo; StartPage; Brave Search; SwissCows; MetaGer;
etc. Giz; 3/4/2022 - How to Google without words: The coolest searches you may not know
Live images, sounds and pictures can give you some of the best Google search results; CNet; 2/3/2022 - How to Get Google Search Results That Are Actually Useful Wired; 10/3/2021
- The Most Helpful Google Search Modifiers Everyone Should Be Using LH; 9/9/2021
- Google spending $15B to remain default iOS search engine to block Microsoft ApIn; 8/27/2021
- How to Password Protect Your Google Search History and Hide Your Secrets LH; 5/25/2021
- DuckDuckGo Calls Out Google Search for 'Spying' on Users After Privacy Labels Go Live MR; 3/15/2021
- My Attempt to Prepare for a Future Without Google NYT; 1/28/2021
- The Blurred Lines and Closed Loops of Google Search what's an ad? seemingly small design tweaks
to the search results interface may change how and where people find information online; Wired; 8/31/2020 - 15 simple tips to get better search results on Google TNW; 4/30/2020
- Google Will Require Proof of Identity From All Advertisers
a slew of scams and misleading ads pushed the search giant to expand its verification policy; NYT; 4/23/2020 - Google now alerts you when search results suck TNW; 4/23/2020
- Why Google Backtracked on Its New Search Results Look NYT; 1/31/2020
- Google is testing how to make ads sneakier in search results TNW; 1/24/2020
- My Decade in Google Searches Decade of Distrust; Images pulled from Google search; NYT; 12/27/2019
- Get Google's Search Results With More Privacy By Using Startpage
startpage.com: actual Google search results w/o tracking; LH; 12/1/2019 - I Ditched Google for DuckDuckGo. Here's Why You Should Too Wired; 12/1/2019
- How to Set Your Google Data to Self-Destruct myactivity.google.com; search and location data; NYT; 10/3/2019
- Apple may have been paid $9.5B by Google in 2018 to stay default Safari search option ApIn; 2/12/2019
iOS
macOS
Safer Internet: Browsing: Anonymity
Safer Internet: Browsing: Anonymity
Quotes | Summary |
References: General | Censorship, Journalism, Wikileaks |
Dark Web / Deep Net | NSA, CIA | Tails | Tor
Quotes
Summary
- [3] Use Tor "The Onion Router" and Tails OS "The Amnesic Incognito Live System"
- Advantages: more anonymity for targeted users, e.g., political dissidents, investigative journalists, whistleblowers, criminals, trolls, hate groups
- minimizes associating your actual IP with routing/server activities
- more encryption (like VPN); random routing via multiple nodes
 Disadvantages: difficult to guarantee 100% anonymity, and likely to attract unwanted attention
Disadvantages: difficult to guarantee 100% anonymity, and likely to attract unwanted attention- difficult to setup; slow; government monitoring / filtering / blocking / censoring
- network {Figure 14: TCYOP-4: 104; TCYOP-3: 87}
- configuration {Figure 15: TCYOP-4: 105; TCYOP-3: 88;}
References
- {TCYOP-4: 103-105; TCYOP-3: 86-88}
- sections: Refs: Censorship, Journalism, Wikileaks; Dark Web / Deep Net; NSA, CIA; Tails; Tor
- topics: China, Iran, ISIS, Silk Road, Snowden, Turkey
- Wikipedia: anonymous browsing; Privacy software
- HowStuffWorks: How Internet Security Works; How to Surf the Web Anonymously; Can the government see what Web sites I visit?
- EFF: Surveillance Self-Defense Tips, Tools and How-tos for Safer Online Communications: Overviews, Tutorials, Briefings, Playlists
- How to Read a Blocked Website
hide your real IP address with a proxy connection, e.g., VPN;
try using TOR (The Onion Browser); LH; 9/2/2022
Censorship, Journalism, Wikileaks
- "Censorship reflects a...
- "As to the evil which results from a censorship,...
- "Wikileaks' silencing was sought by antidemocratic governments worldwide --
including China, whose censors work mightily to block all access to the site.
Wikileaks' plug was pulled, ironically,... - Wikipedia: Internet censorship; internet filter
- Wikipedia: WikiLeaks publishes secret information, news leaks, and classified media from anonymous sources
- HowStuffWorks: How Internet Censorship Works
- Russia May Have Found a New Way to Censor the Internet throttling rather than blocking; Wired; 4/8/2021
- Tuber browser, which let Chinese users register and access banned services like YouTube, has been blocked and removed from China's third-party Android stores BB; 10/10/2020
- I wrote this law [Section 230] to protect free speech. Now Trump wants to revoke it Wyden; CNN; 6/9/2020
- The Internet's most important—and misunderstood—law, explained Section 230 is the legal foundation of social media, and it's under attack; Ars; 6/10/2020
- China's Global Reach: Surveillance and Censorship Beyond the Great Firewall EFF; 10/10/2019
- Ron Wyden wrote the law that built the internet je still stands by it — and everything it's brought with it; 5/16/2019
Dark Web / Deep Net
- see also: Shopping: Cryptocurrency
- Wikipedia: Deep Web (aka Deepnet, Invisible Web, or Hidden Web) is not indexed by standard search engines
- Wikipedia: DARPA's Memex search engine for the dark web vs. Memex: 1945 paper that inspired hypertext and the World Wide Web
- Wikipedia. online black markets: Agora; Evolution; Silk Road
- HowStuffWorks: How the Deep Web Works
- Google brings dark web monitoring to all U.S. Gmail users BC; 5/10/2023
- Darknet markets generate millions in revenue selling stolen personal data Ars; 12/3/2022
- The Hunt for the Dark Web's Biggest Kingpin -- The Rise and Fall of AlphaBay:
Part 1: The Shadow Wired; 10/25/2022;
Part 2: Pimp_alex_91 11/1/2022;
Part 3: Alpha Male 11/8/2022;
Part 4: Face to Face 11/15/2022;
Part 5: Takedown 11/22/2022;
Part 6: Endgame 11/29/2022 - The Difference Between the Dark Web and the Deep Web
surface web: collection of sites indexed by search engines;
dark web: collection of private networks accessed only by special browsers and/or protocols;
deep (aka hidden) web: unindexed pages requiring login; LH; 3/15/2022 - Should You Use a 'Dark Web Scan' to Protect Your Identity? LH; 10/23/2020
- Can You Really Hire a Hit Man on the Dark Web? generally scams; NYT; 3/4/2020
- What's Actually on the Dark Web MB; 1/30/2020
- A look at the rise of murder-for-hire marketplaces on the dark web, the vast majority of which are schemes to pilfer money from gullible users Harpers; 12/15/2019
- Feds Bust One of the Dark Web's Biggest Child Porn Sites Thanks to Tremendously Bad Opsec MB; 10/16/2019
- The CIA Will Use its New Dark Web Site to Collect Anonymous Tips MB; 5/7/2019
- What is a “Dark Web Scan” and Should You Use One? 3/26/2019
- The Evolution of Darknets 1/23/2019
National Security Agency (NSA); CIA
- Wikipedia: National Security Agency; Freedom of the Press Foundation
- Wikipedia: Crypto wars; Backdoors
- HowStuffWorks: How the NSA Works
Tails
- Wikipedia: Tails OS The Amnesic Incognito Live System; "a live operating system, that you can start on almost any computer from a DVD, USB stick, or SD card. It aims at preserving your privacy and anonymity, and helps you to: use the Internet anonymously and circumvent censorship; all connections to the Internet are forced to go through the Tor network; leave no trace on the computer you are using unless you ask it explicitly; use state-of-the-art cryptographic tools to encrypt your files, emails and instant messaging."
- Privacy-Focused OS Wants to Know How Facebook and the FBI Hacked it Verge; 6//23/2020
- Facebook Helped Develop a Tails Exploit 6/12/2020
- Tails, the security-focused OS, adds support for UEFI Secure Boot ZD; 4/8/2020
 Tor
Tor
- Wikipedia: Tor ("The Onion Router"); .onion pseudo-top-level domain host suffix for Tor
- Tor Browser for Apple Silicon Macs is Now Available OSXD; 12/17/2022
- Tor is under threat from Russian censorship and Sybil attacks Ars; 12/8/2021
- Someone Is Running Hundreds of Malicious Servers on the Tor Network and Might Be De-Anonymizing Users Giz; 12/3/2021
- What Is Tor and Why Should I Use It? LH; 12/7/2020
- Does Tor provide more benefit or harm? New paper says it depends more harmful in 'free countries'? licit vs. illicit services; Ars; 11/30/2020
- BBC Launches Tor Mirror Site To Thwart Media Censorship NPT; 10/24/2019
Safer Internet: Browsing: Shopping
Safer Internet: Browsing: Shopping
Summary | Correct, Secure Site | Credit Cards | Other: Paypal, Bitcoin,... |
References: General | Amazon | Apple |
Crytocurrency, Bitcoin | Google | Payment, Credit | Paypal
Summary
- "Remote shopping, while entirely feasible,...
- [1] Use Correct, Secure Site / App
- [1] Protect Credit Card Info: store in password manager -- not browser, not vendor site
- Provide a temporary (instead of your actual) credit card number,
e.g., Apple Pay; Virtual Account Number (Citi), digital wallet,
privacy.com linked to debit card or checking account, with 1Password integration,
when possible, esp. for one-off purchases on smaller / lesser-known sites - [2] Consider other Forms of Payment, e.g., Paypal; [3] Cryptocurrency?
- References
[1] Use Correct, Secure Site / App
- Many of these already covered in other sections:
- Be sure to navigate to correct web site, esp. not via ads / impostor links
- Use HTTPS: for login & entering contact / payment details -- see section
- Clear purchase history on sites?
- If using an app, make sure it's authentic & up-to-date: app store, exact name, ratings, etc.
[1] Protect Credit Card Info
- Save credit card info in a password manager rather than browser -- more secure, sync across browsers/platforms
- macOS:
Safari > Preferences > AutoFill > Credit Cards: off - iOS:
Settings > Safari > AutoFill > Credit Cards: off - Avoid storing credit info on merchant site, if possible -- though some may require a card on file
- This should be less of an issue for major vendors, e.g., Amazon, Apple -- who can invest more on security
- If you misplace your card, you can lock your card with some credit card companies (and unlock it later when you find it).
- Check your credit card statements monthly, or more frequently, to detect fraudulent charges
- Enable account notifications (email/text) if supported, e.g.,
- for an international charge
- for an online, phone or mail charge
- for an amount over $x
- Check Apple Pay (or similar) settings, if applicable
- iPhone:
Settings > Wallet & Apple Pay - iPhone:
Settings > Safari > Check for Apple Pay - Rank credit cards by importance and impact; what happens if one is compromised?
- Use different credit cards for different purposes/sites, e.g., online only, regular automatic payments, one-time purchases with new vendors, etc.
- A single-use, virtual credit card number linked to a credit card (or bank account) provides additional security
- Virtual Account Numbers creates a temporary credit card # & security code; you set expiration date and credit limit; e.g., Citi not avail for Costco Visa apparently
- Bank of America formerly offered virtual card numbers via "ShopSafe", which has now been discontinued in favor of Digital Wallets?
- Check with your bank or credit card company
[2] Consider other Forms of Payment
- PayPal can be linked to checking account or credit card; vendor doesn't see credit card info
- Downsides: yet another account; does not provide same protection for contesting charges; may block some quasi-legal purchases, which use VPN or violate their definitions of copyright, decency, etc.
- Other services can be used to transfer cash, e.g., Square, Messenger, Venmo -- understand possible fees and consumer protections
- [3] Avoid cryptocurrency, e.g., Bitcoin
- Although a cryptocurrency might provide more anonymity and can be used to hide transactions, it's also unreliable, variable and hackable; also, definitely not an 'investment'
References
- {TCYOP-4: 106-109; TCYOP-3: 89-90}
- section: Refs: Amazon; Apple; Crytocurrency, e.g., Bitcoin; Google; Payment, e.g., credit card, money transfer; Paypal
- topics: Cyber Monday, E-commerce, GoFundMe, Google Play/Wallet, Square, Venmo
- Wikipedia: Online shopping; micropayment
- HowStuffWorks: How Electronic Payment Works; 5 Ways to Send Money Online
- Tips for Canceling Online Subscriptions
it's easy to sign up but not always so easy to stop a service.
F.T.C. is proposing rules to change that; NYT; 7/7/2023 - Canceling Online Subscriptions Is Confusing, Difficult and Absurd... by Design
many companies use tactics called "dark patterns" to make it difficult to cut ties; CNet; 4/4/2022 - Why the Internet Is Turning Into QVC
greed, fear and China; NYT; 11/14/2021 - How to Protect Yourself From Online Card Fraud
be wary of websites that offer brand-name goods at steep discounts;
credit cards have federally mandated protections; NYT; 10/22/2021 - How to cancel your account at Netflix, Amazon Prime, and others Verge; 1/15/2021
- It's Time to Audit Your Autopay Subscriptions average American spends $237 a month; LH; 10/9/2020
- How to Protect Yourself From the Newest Mobile Banking Malware LH; 6/11/2020
- They See You When You’re Shopping How Sephora, Gucci, Kiehl’s and more track about 20 million online shoppers every day; NYT; 11/26/2019
- How to Not Get Phished When Shopping Online Make sure the URL is safe and accurate; Use a browser with DNS over HTTPS; Don’t click on suspicious email links or attachments; Bookmark the real website and/or login pages; Use a password manager; Use the official mobile apps for online stores/services; LH; 11/18/2019
- E-Commerce Promised the World. Are We Happy With Our Purchase? It's been 25 years since the first online transaction, but we are still struggling with the balance between convenience and security; NYT; 8/10/2019
- 7 Ways Artificial Intelligence Can Help Protect Us Against Online Fraud
1. AI Can React Immediately To Suspicious Activity.
2. AI Can Help Spot Fraudulent Online Ads.
3. AI Is Helping Humans Do More Work.
4. AI Learns From A Variety Of Businesses.
5. AI Could Make Transactions Faster, Not Slower.
6. AI Can Assess Where The Most Likely Threats Are Coming From.
7. AI Can Help Us Identify Social Engineering Hacks; MF; 7/2/2019 - How Dark Patterns Change Our Behavior LH; 7/1/2019
- How to avoid Internet fraud, scams, phishing and other cybercrime PC; 6/25/2019
- How E-Commerce Sites Manipulate You Into Buying Things You May Not Want dark patterns; fake notifications; default options; NYT; 6/24/2019
- How to Find and Report Fake Businesses on Google Maps LH; 6/21/2019
- Apple Pay vs. Google Pay vs. Samsung Pay: Mobile payments compared CNet; 6/17/2019
- In Stores, Secret Surveillance Tracks Your Every Move Bluetooth 'beacons' work well at short-range, indoors; remove retailer & spy apps, shut off location services and Bluetooth where they are not needed; NYT; 6/15/2019
- Stanford Team Aims at Alexa and Siri With a Privacy-Minded Alternative Almond virtual assistant software is decentralized and connected by programming standards that will make it possible for consumers to choose where their information is stored and how it is shared; NYT; 6/14/2019
- Loyalty programs cost you your personal data -- are the rewards worth it? TNW; 6/12/2019
- Don't Use a Debit Card at the Gas Pump card skimmers; use digital wallet (e.g., Apple/Samsung/Android Pay) or credit card (fraud protection); LH; 2/22/2019
Amazon
- How to Download Everything Amazon Knows About You (It's a Lot) LH; 1/25/2022
- 10 Privacy Settings Every Amazon User Should Enable Right Now LH; 11/4/2021
- Life Without Amazon (Well, Almost) NYT; 12/29/2020
- Amazon Knows What You Buy. And It's Building a Big Ad Business From It. NYT; 1/20/2019
Apple
- How to Delete Your Apple Pay Information Remotely If Your Device Is Stolen LH; 4/6/2021
- Apple Card Now Available to All US iPhone Users TB; 8/20/2019
- How to Get the Most from Your Apple Card Benefits TB; 8/14/2019
[3] Cryptocurrency, e.g., Bitcoin
- Wikipedia: Bitcoin; Cryptocurrency; Ethereum; Initial coin offering (ICO)
- HowStuffWorks: How Bitcoin Works
- What Is Blockchain? The Complete WIRED Guide Wired; 2/2/2023
- The Crypto Story: an in-depth look at crypto and blockchains
bitcoin and the underlying tech, the uses and meaning, the crypto financial system, and trust, money, and community; Bloom; 10/25/2022 - Here's what to know about "the Merge." NYT; 8/26/2022
- Ethereum's "Merge" is about to put every ether miner out of work
ambitious change from proof-of-work to proof-of-stake is expected to cut
energy consumption by a factor of 1,000; Ars; 8/19/2022 - Cryptocurrency tech is vulnerable to tampering, a DARPA analysis finds NPR; 6/21/2022
- How 'Trustless' Is Bitcoin, Really? blockchain leakage; NYT; 6/6/2022
- Understand Cryptocurrency, but Don't Invest in It TB; 4/20/2022
- NFTs Are a Privacy and Security Nightmare
the blockchain isn't as "anonymous" as you might think; Wired; 4/5/2022 - The Latecomer's Guide to Crypto
What are NFTs?: nonfungible tokens
What is web3?: internet services built using decentralized blockchains;
What are DAOs?: decentralized autonomous organizations;
What is DeFi?: decentralized finance;
NYT; 3/18/2022 - Maybe There's a Use for Crypto After All
Helium, a wireless network (for IoT) powered by cryptocurrency, hints at the practical promise of decentralized services; NYT; 2/6/2022 - Cracking a $2 Million Crypto Wallet Verge; 1/24/2022
- We All Need to Stop Only Seeing the Dark Side of Crypto
in some parts of the developing world, cryptocurrency is changing lives for the better; Wired; 12/19/2021 - Cryptocurrency faces a quantum computing problem
cracking public key cryptography; CNet; 11/12/2021 - Widely Used Bitcoin ATMs Have Major Security Flaws, Researchers Warn Giz; 9/30/2021
- Bitcoin Cosplay Is Getting Real NYT; 9/14/2021
- Crypto Banking and Decentralized Finance, Explained NYT; 9/5/2021
- The Brutal Truth About Bitcoin NYT; 6/14/2021
- Bitcoin and Encryption: A Race Between Criminals and the F.B.I. NYT; 6/12/2021
- New Rule: Crypto Mania! Real Time with Bill Maher (HBO); 4/30/2021
- Ars Technica's non-fungible guide to NFTs
is blockchain item authentication a speculative fad or a technological sea change? Ars; 3/29/2021 - Want to really understand how bitcoin works? Here’s a gentle primer Ars; 12/26/2020
- Cryptocurrency Hardware Wallets Can Get Hacked Too Wired; 5/18/2020
- Bitcoin Has Lost Steam. But Criminals Still Love It. NYT; 1/28/2020
- 3 pivotal Bitcoin figures thought to be Satoshi that you should know about Harold Finney, Nick Szabo, David Kleinman; TNW; 8/21/2019
- Terrorists Turn to Bitcoin for Funding, and They're Learning Fast NYT; 8/18/2019
- Was Bitcoin Created by This International Drug Dealer? Maybe! Paul Le Roux; Wired; 7/16/2019
- How Libra Would Work for You Facebook's cryptocurrency; NYT; 6/18/2019
- After the Bust, Are Bitcoins More Like Tulip Mania or the Internet? NYT; 4/23/2019
- Kurt Russell's New Bitcoin Crime Movie 'Crypto' Looks so Awful I Must See It an instant so-bad-it's-good classic ala 1995's 'The Net'? MB; 3/12/2019
- Cryptocurrency wallet caught sending user passwords to Google's spellchecker Coinomi wallet bug sends users' secret passphrases to Google's Spellcheck API via HTTP, in plaintext; ZD; 2/27/2019
- You Do Not Need Blockchain: Eight Popular Use Cases And Why They Do Not Work 2/22/2019
- A brief history of cryptocurrency and blockchain white papers TNW; 2/21/2019
- The differences between cryptocurrencies, virtual, and digital currencies TNW; 2/19/2019
- Why storing your Bitcoin private keys on Google Drive is a terrible idea or any cloud service -- if the chosen password isn't strong/unique; TNW; 2/13/2019
- Blockchain and Trust Schneier; 2/12/2019
- How Bitcoin Could Help Iran Undermine U.S. Sanctions NYT; 1/29/2019
- Why the Ethereum Classic hack is a bad omen for the blockchain the 51% attack is real, and it's easier than ever; Verge; 1/9/2019
- Google is tracking your purchases through Gmail every time a store sends a confirmation to your Gmail account, Google adds it to your list of purchases; see, manage here; CNet; 5/17/2019
- Update Your Google Pay Privacy Settings Now LH; 3/16/2019
Payment
- All the Ways Your Credit Card Info Can Be Stolen LH; 7/27/2023
- How to Look Up an Unauthorized Charge on Your Credit Card WhatsThatCharge.com; LH; 11/7/2022
- Why You Shouldn't Pay for Anything With Zelle LH; 10/7/2022
- Insomnia, addiction, depression: The dark side of life trading crypto WaPo; 4/29/2022
- The Easy Way I Protect My Credit Cards Online and Keep Free Trials Free privacy.com; NYT; 4/26/2022
- Fraud Is Flourishing on Zelle. The Banks Say It's Not Their Problem. NYT; 3/6/2022
- Venmo gets more private—but it's still not fully safe Ars; 7/25/2021
- Yes, You Should Be Using Apple Pay or Google Pay paying with a smartphone is actually more secure and more efficient than using a credit card; Wired; 11/7/2020
- How to Pay Using Virtual Credit Cards in 1Password each tied to a separate merchant -- linked to debit card or checking account (not credit card); one-off & recurring payments; can also use privacy.com directly w/o 1PW; LH; 9/24/2020
- How to Reduce Credit Card Fraud NYT; 6/8/2020
- Beware the Fees That Come With Some Money Transfers on Apps treated as cash advances, with interest accruing immediately? Paypal? Venmo? Square? NYT; 4/24/2020
- A Case for Paying With Your Phone NYT; 2/5/2020
- How to Use Up the Last Few Dollars on a Prepaid Gift Card buy an Amazon e-gift card for the exact amount on the Visa gift card; LH; 2/4/2020
- How Scammers Can Use Your Old Credit Card Numbers use only 1 credit card (or virtual cards) for online purchases; LH; 1/6/2020
- How I Survived a Week Without My Wallet with just smartphone; NYT; 9/27/2019
- What it Costs to Send Money Internationally With Wire Transfer Apps MoneyGram, TransferWise, Xoom, Western Union, WorldRemit; LH; 9/3/2019
- Deep dive into the byzantine tracking and analytics industry around credit card purchases and steps that consumers can take to improve their privacy WaPo; 8/26/2019
- MoviePass exposed thousands of unencrypted customer card numbers TC; 8/20/2019
- Here's Why Everyone Already Has Your New Credit Card Expiration Date auto-updater services; LH; 5/17/2019
- Unless you want your payment card data skimmed, avoid these commerce sites Ars; 5/8/2019
- Apple Card will be the most secure credit card ever, and here's why AI; 4/2/2019
- Apple Card FAQ: Interest rates, rewards, sign-up and everything else you need to know MW; 3/27/2019
- Apple Card has a rotating security code that is protected by Touch ID or Face ID, helping better prevent credit card fraud TC; 3/25/2019
- A new rash of highly covert card-skimming malware infects ecommerce sites Ars; 3/14/2019
- Check Your Credit Report Even If Your Credit Is Frozen a freeze does not prevent someone from using an existing account to make fraudulent charges, which is far more common; LH; 3/8/2019
Paypal
Safer Internet: Browsing: Crossword #1
Safer Internet: Browsing: Crossword #1
The Puzzle
 Interactive version [below]
Interactive version [below]
Check button: check puzzle for errors; Reveal button: reveal current word
Web version created by Crossword Compiler Print versions [.pdf]: puzzle; solution
Print versions [.pdf]: puzzle; solution Download for a crossword app [.puz]: puzzle w/ solution
Download for a crossword app [.puz]: puzzle w/ solution
open it in a crossword app, e.g., Mac, Windows: Across Lite (free); Android, iOS: Crosswords
Safer Internet: Improve Email Privacy
Safer Internet: Improve Email Privacy
Quotes | Summary | When Email Best? | Email Account |
Malware | Spam | Web Mail | Client App | Tracking |
References: General | Android | Gmail, Google | Government | iCloud |
iOS | macOS | ReplyAll | Spam | Tracking | Windows | Yahoo
Quotes
- "Email: nothing more than...
- 'Spam will soon be...
- "I just got an email about how to read maps backwards, but...
- A child was watching her mother sift through and delete a long list of junk E-mail.
"This reminds me of the Lord's Prayer," the child said.
"What do you mean?" the mother asked.
"You know... - "I've Never Sent an Email"...
Summary
- [1] Is Email the Best Communication Method?
- [1] Protect Email Account
- [1] Avoid Malware in Attachments and Links
- [1] Reduce Spam
- [2] Webmail in Browser: use HTTPS:
- [2] Email Client App: use TLS/SSL for login, transfer, sending
- [2] Reduce Email Tracking
- [3] see section: Encryption, Anonymity
- References
[1] Is Email the Best Communication Method?
- Type of information -- and its sensitivity? Audience? Timeliness?
- Even though email should be encrypted in transit to mail server, it may no longer be private when stored on mail server or on recipient's computer; what if it becomes public later?
- Verify intended addressees before sending, i.e., To:, cc:; autocomplete/autofill may be incorrect; Reply vs. Reply All
- Use bcc: for groups to protect privacy and reduce Reply All volume
- Email is not the best way to send large / many attachments -- see Share Files Privately
- Is the email service provided by your ISP adequate, reliable, secure, well-maintained?
- Email provider's privacy policy and business model?
some providers, e.g., ProtonMail; Posteo; Tutanota; FastMail; Thexyz; Kolab Now; Mailbox.org, may provide more privacy or "end-to-end encryption"; section Encryption, Anonymity - Ethical.net: Email services
- Maybe communicate fragments of secrets over different channels, e.g., phone, text message, video, etc., to replace / complement email -- see section Talk and Chat Privately
[1] Protect Email Account
- Use a 'permanent' account if possible, e.g., icloud.com, gmail.com, outlook.com
- If you rely primarily on your ISP (charter, comcast, ashlandhome), what happens to your address if you move or change ISPs?
- If your email account is hacked, change password immediately.
- If that same password was used for any other accounts, be sure to update those accounts also.
- Check Sent/Trash for any messages sent by hacker, e.g., password resets for other accounts.
- Strengthen security answers; turn on 2-factor authentication if available, etc.
[1] Avoid Malware in Attachments and Links
- Don't open/download unexpected attachments in messages; enable malware protection; check Sender:
- [1] macOS: click on the little downward pointing “v” at the right of the From address to see address of sender
- [2] macOS:
Mail > View > Message > All Headers - Most email applications display messages as mini-web pages -- with problems (like web) of ad tracking, fraudulent links, etc.
- Don't click on links in messages; even truer for unexpected messages about products/sites/services you don't use
- Exceptions: after changing an email address on an account, the site often sends an email with a link to verify the address; others??
- If an email asks you to click a link/button to address a problem or change your password, log in to the site directly using your password manager -- not the email links, unless you've just initiated a "I forgot my password" request
- If it's an offer to update software, use the official methods described earlier to check, download and install
- Quiz: Can You Identify Phishing Emails?
- To avoid displaying possible mal-content, don't open or display message in first place:
- macOS:
Mail > ctrl-click msg > Delete(individual msg) - macOS:
Mail > Mailbox > Erase Junk Mail(delete all w/o opening) - macOS:
Mail > (drag dot on separator bar -- between message list & preview area -- to bottom of window); select & delete message(s); restore bar - iOS:
Mail > (swipe left on title in message list) > Trash - When sending large attachments, enable "Mail Drop", which uses iCloud temporarily
- macOS:
Mail > Preferences > Accounts > (account) > Advanced > Send Large Attachments with Mail Drop - iOS: no need to set -- triggered automatically; select
Use Mail Dropfrom popup - When sending attachments to a Windows user:
- macOS:
Mail > File > Attach Files > Options > Send Windows-friendly Attachments
[1] Reduce Spam
- Don't forward chain letters or spam; check Snopes
- Unsubscribe from reputable sources only; otherwise, you just confirmed validity of your address to a spammer
- Limit auto-reply usage: omit dates when your house can be burgled, spam confirmations
- It's difficult to reduce/eliminate spam once your email address has been disseminated, e.g., by replying to spammers, by making address public on a web site or forum, by malware harvesting your friend's Contacts, etc.
- Use filters to minimize danger from phishing, and annoyance from spam;
check Junk/Spam folder periodically for good messages, move messages to "train" - If using multiple devices and IMAP, centralize settings with mail provider
- gmail.com: Spam: no setup required
- gmail.com:
Settings > Filters - If not centralized, spam and filter settings for individual device:
- macOS:
Mail > Preferences > Junk Mail - macOS:
Mail > Preferences > Rules - The most common scams will target you through fake emails, text messages, voice calls,
letters or even someone who unexpectedly shows up at your front door.
Review all five scenarios for important red flags that could signal a scam. - 1. You're pressured to act immediately
- Remember: In some cases, scammers can be friendly, sympathetic and seem willing to help.
In others, they use fear tactics to persuade a potential victim, for example: - You're instructed to not trust your bank, or to respond to questions in untruthful ways.
- You're pressured to send money.
- You're threatened with law enforcement action.
- You receive a request from a government agency or the IRS
asking you for a payment and/or to verify your personal information.
Scammers may threaten lawsuits or law enforcement action to trick you in to acting quickly. - 2. You're asked to provide authorization codes
- Remember: Authorization codes are important ways to verify who you are in order to access your account.
- Never share your authorization codes, regardless of the reason someone gives you,
unless you've contacted the company through a verified method.
Once a scammer has your codes, they can gain full access to your accounts. - Your company should never text, email or call you asking for an authorization code.
If someone reaches out to you and asks for it, it is a scam. - 3. You've received a suspicious text or email
- Your account should not use email or text to ask you for personal information
such as your account number, card PIN, Social Security number or tax ID number. - The best way to avoid email or text fraud is to remain vigilant.
Never click on a link in an email or text message unless you are absolutely certain
who sent the email and where the link is taking you. - Fraudulent emails or texts typically imply urgency, attempting to get you to act quickly
before you have time to carefully read and examine the message.
They often don't address you by name and contain obvious grammar and/or spelling errors. - 4. You're told to buy a gift card to pay a debt or a service.
- Never share gift card information (such as the card's unique identifier number) with someone you don't know.
- Criminals may pressure you to send funds via gift cards by asking for the code numbers
or PINs on the backs of the cards so they can be redeemed immediately. - A scammer may tell you a story that they urgently need funds to pay a debt,
for a medical emergency or they want to travel to see you. - 5. You're asked to deposit a check and return the money
- Never cash a check for someone you don’t know.
The bad check will be held against your account when it doesn't clear. - If you're asked to return money for overpayment of an item you’re selling, it’s most likely a scam
and the bad check will be held against your account when it doesn't clear. - You're approached by a stranger who claims to have left their wallet at home and asks you to cash a check for them.
Or you may be asked to deposit a check that overpays for something you’re selling, then send the difference elsewhere.
[2] Webmail in Browser: use HTTPS:
- Webmail on your ISP's website, e.g., icloud.com/#mail, gmail.com, mail.yahoo.com, webmail.aol.com
- Some ISPs, e.g., ashlandhome.net, may support HTTPS: only for desktop (not mobile) browser
- If ISP also doesn't support SSL/TLS in email client (next), obtain a separate, secure account for your main communication; also more portable if you move or change providers
- Some sites communicate only via secure email "portal", e.g., medical, financial
[2] Email Client App: use TLS/SSL for login, transfer, sending
- Use SSL (Secure Socket Layer, or newer TLS: Transport Layer Security) in an email client app, e.g., Mail on iOS / macOS; Thunderbird, Outlook, Outlook Express; network: {Figure 6. TCYOP-4: 67}
- i.e., for your account: login, transfer, sending
- When adding an account, certain providers may have automatic settings/templates
- iOS:
Settings > Accounts & Passwords > Add Account - macOS:
Mail > Accounts > + - Otherwise, check email app or email provider's site for configuration details, e.g., mail settings tool
- Login, transfer: enable SSL for IMAP or POP email; {Figure 16: TCYOP-4: 120; TCYOP-3: 96}
- Do not use unencrypted POP, e.g., earthlink
- IMAP: better for sharing messages & folders between devices; webmail; backup?
- if using IMAP, check if supported by email provider; enable if necessary
- iOS:
Settings > Mail, Contacts, Calendars > (account) > Account > Advanced > Use SSL - macOS: generally, adding a new account will automatically enable SSL for receiving & sending; to check this:
- macOS:
Mail > Inbox > (ctrl-click) > Account Info > Summary > Incoming SSL: on - macOS (older):
Mail > Preferences > Accounts > (account) > Advanced > Use SSL - Sending: enable SSL, i.e., SMTP server
- Can you access email easily while traveling, esp. sending?
- iOS:
Settings > Mail, Contacts, Calendars > (account) > Account > SMTP > (server) > Use SSL - macOS:
Mail > Inbox > (ctrl-click) > Account Info > Summary > Outgoing SSL: on - macOS (older):
Mail > Preferences > Accounts > (server) > Account Info > Outgoing Mail Server (SMTP) >
Edit SMTP Server List > (server) > Advanced > Use SSL
[2] Reduce Email Tracking
- Disable image display -- to minimize tracking; extra benefit: slightly faster display
- macOS:
Mail > Preferences > Viewing > Load content in remote messages - macOS:
Mail > (individual message) > Load Remote Content - iOS:
Settings > Mail,Contacts,Calendar > Load Remote Images - Some messages provide a link to view the message in browser, which, if configured properly, might provide better security.
- more selective solutions are being developed to block 1x1 tracking pixels (all, or selected marketers) --analogous to Browsing : Adware); e.g., PixelBlock, UglyMail; stay tuned
- Create different email addresses or aliases for different purposes -- via different providers: iCloud, Yahoo, Gmail, Live, etc.
- Apple allows 3 aliases that are redirected to main account, e.g., main: johsmith@icloud.com; aliases: jsmithabc@icloud.com, jsmithdef@icloud.com, jsmithghi@icloud.com
- macOS:
Mail > Preferences > Accounts > iCloud > Edit: Email Address > (icloud.com/) > Mail > Add an alias - Some providers allow "+" suffix, e.g., johnsmith+amazon@icloud.com, john.smith+facebook@gmail.com; those recipients appear in main Inbox
- This allows you to track who gave out your address, and to setup email filters; addresses completely separate from your main account are desirable for password resets, even though inconvenient; it also could provide some anonymity if your address is leaked later; unfortunately, some sites may not allow "+" in username or email contact fields.
- [Spam]: 'Gmail: Your address has more or fewer dots (.) or different capitalization'
References
- {TCYOP-4: 110-131; TCYOP-3: 91-106; Understand the Privacy Risks of Email: On your end, In transit, On email servers, On the recipient's end, In backups; Are Gmail Ads an Invasion of Privacy? Log In Securely; Transfer Email Securely; IMAP vs. POP Privacy Implications; Email Your Doctor, Accountant, or Lawyer Privately}
- sections: Android; Gmail, Google; Government; iCloud; iOS; macOS; ReplyAll; Spam; Tracking; Windows; Yahoo
- topics:
- Wikipedia: E-mail; Email address; phishing attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity in an electronic communication
- Wikipedia: phishing types e.g., Spear phishing, Clone phishing, Whaling, Rogue WiFi (MitM)
- Wikipedia: webmail web-based email, e.g., via browser
- Wikipedia: email client (application): Mozilla Thunderbird
- Wikipedia: AOL Mail; Gmail; Windows Live Mail; Yahoo! Mail
- Wikipedia: Post Office Protocol (POP); Internet Message Access Protocol (IMAP); Simple Mail Transfer Protocol (SMTP)
- Wikipedia: Multipurpose Internet Mail Extensions (MIME) encoding for non-text file attachments
- Wikipedia: Secure MIME (S/MIME)
- HowStuffWorks: How E-mail Works; Quiz
- Email - How does it work? video: 1:17
- HowStuffWorks: POP and IMAP servers; SMTP Server
- Wikipedia: email fraud; Internet memex; Internet hoaxes; urban legend
- hoaxes: snopes.com; Urban Legends; Dept. Homeland Security
- HowStuffWorks: How Phishing Works; Phishing Quiz; How E-mail Scams Work
- HowStuffWorks: How do viruses and worms spread in e-mail?; Can the government read your private e-mails?
- Ethical.net: Email services
- These Are the Best Free Email Accounts
Gmail, Outlook, Proton, Yahoo, Zoho; LH; 10/26/2023 - All the Different Email Addresses You Should Set Up (and What to Use Them For) apps, newsletters, ...; LH; 10/24/2023
- Why ISP email services are terrible, and what to use instead
Apple's iCloud, Google's Gmail, Microsoft's Outlook.com; paid services; ApIn; 5/12/2023 - Everyone Wants Your Email Address. Think Twice Before Sharing It. UID 2.0;
create a bunch of email addresses; use email-masking tools;
when possible, opt out; NYT; 1/25/2023 - Anyone can sign up for DuckDuckGo's privacy-protecting @duck.com email address Verge; 8/25/2022
- 4 Quick Tips for Managing Email Overload on the Go NYT; 6/1/2022
- Now Is a Good Time to Update Your Recovery Email Addresses
make sure those 'emergency' email addresses (you can use to get into your email
and other accounts in case you're locked out) are up to date; Wired; 1/23/2022 - How to Hide Your Email From Data Collectors
Apple's Hide My Email / Sign in With Apple;
Firefox Relay; [Anon]addy; Simplelogin;
DuckDuckGo Email Protection;
1Password and Fastmail's Masked Email;
Use a Temporary Burner Email;
Verge; 12/6/2021 - The Best Ways to Hide Your Email Address
Gmail: add . anywhere, or +label before @;
Yahoo: create up to 500 aliases w/ text appended;
Outlook: create up to 10 aliases;
Apple: Hide My Email;
Firefox: Relay; 5 free aliases; Premium plan for unlimited;
DuckDuckGo: Email Protection;
Fastmail + 1Password: Masked Email;
others: Protonmail, SimpleLogin, Addy;
Giz; 11/23/2021 - Firefox Relay offers unlimited email aliases as part of its new premium plan Eng; 11/16/2021
- How To Fix Email -- with Science!
behavioral changes; Wired; 11/8/2021 - Cut Down on Junk Mail with iCloud+'s Hide My Email TB; 10/21/2021
- 1Password gets its own 'hide my email' feature
Create Masked Email -- unique email aliases for logins, much like
Apple's iCloud Plus Hide My Email function but integrated and not only for Apple users;
video; Verge; 9/28/2021 - Cloudflare Is Taking a Shot at Email Security
Email Routing and Email Security DNS Wizard, built on top of Gmail, Outlook, Yahoo, and others to prevent phishing, spoofing, and more; Wired; 9/27/2021 - Could Gen Z Free the World From Email? NYT; 7/10/2021
- [2] 21Nails vulnerabilities impact 60% of the internet's email servers 5/4/2021
- How to Back Up Your Most Important Emails Forward Emails to a Backup Account; Use POP and IMAP; Download Everything To a Desktop Client; Other Options; Wired; 1/24/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing; DuckDuckGo for Search; OsmAnd for Maps; ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020
- Some email clients are vulnerable to attacks via 'mailto' links GNOME Evolution, KDE KMail, IBM/HCL Notes, and older versions of Thunderbird that support 'dangerous' parameters like 'attach', 'attachment'; ZD; 8/18/2020
- How Do I Get Into My Email If I've Lost My Recovery Codes? LH; 8/7/2020
- [2] Decades-Old Email Flaws Could Let Attackers Mask Their Identities 18 exploits that take advantage of inconsistencies in the email plumbing most people never think about; Wired; 8/4/2020
- How to Change Your Email Address LH; 6/17/2020
- New Firefox service will generate unique email aliases to enter in online forms Firefox Private Relay add-on; ZD; 5/1/2020
- How Apple ‘Intercepts' And Reads Emails When It Finds Child Abuse using hashes; Forbes; 2/11/2020
- How Big Companies Spy on Your Emails e.g., Edison, Cleanfox: scrape the contents of your email inbox, sell data; MB; 2/10/2020
- How Can I Save All My Emails for a Personal Backup? LH; 1/27/2020
- Switch From Your Internet Provider’s Email to Something Better Gmail, Outlook, iCloud, Fastmail, ProtonMail; NYT; 1/24/2020
- What Your Email Signature Says About You NYT; 12/9/2019
- How to Change Your Email Address Without Screwing Everything Up LH; 10/7/2019
- Automatically Unsubscribe From Unwanted Emails With 'Leave Me Alone' paid, but more private than Unroll.me; LH; 9/24/2019
- Don't Put Your Work Email on Your Personal Phone Mobile Device Management potentially gives your company the ability to spy on your location, your web browsing, and more; 7/23/2019
- Can You Switch ISPs Without Losing Your Email Address? LH; 7/5/2019
- 'The world's greatest email app' is a privacy nightmare Superhuman; tracking pixels; TNW; 7/3/2019
- Your Fake Email Isn't Keeping Your Health App Data Private LH; 5/17/2019
- How to Write the Ultimate Canned Email checklist; LH; 2/25/2019
- 'Catastrophic' hack on email provider destroys almost two decades of data VFEmail says data for virtually all US users is gone for good; Ars; 2/12/2019
Android
Gmail, Google
- Google Is Finally Cracking Down on Mass Emails new bulk email rules; LH; 2/17/2024
- Google will start deleting inactive accounts after two years Ars; 5/16/2023
- Google brings dark web monitoring to all U.S. Gmail users BC; 5/10/2023
- Your Gmail Account Has Unlimited Addresses "+", googlemail.com; LH; 11/21/2022
- How to (hopefully) restore your Gmail account if you lose access Verge; 8/4/2021
- Tired of Gmail? Try a Privacy-First Email Provider ProtonMail, Lavabit, Burner Mail; Wired; 8/16/2020
- 5 Simple Ways to Make Your Gmail Inbox Safer
1. Block Persistent Spammers;
2. Increase the Undo Send Time;
3. Use Confidential Mode;
4. Delete Cached Offline Data;
5. Hide External Images; Wired; 5/23/2020 - How to Free Up Space in Gmail if 15Gb isn't enough; Wired; 10/31/2019
- Gmail confidential mode is not secure or private 6/20/2019
- Gmail becomes first major email provider to support MTA-STS and TLS Reporting new security standards; ZD; 4/11/2019
- Gmail is now blocking 100 million extra spam messages every day with AI using TensorFlow; Verge; 2/6/2019
- Using Gmail "Dot Addresses" to Commit Fraud Schneir; 2/6/2019
Government
iCloud
- Apple will delete your inactive iCloud account faster than Google MW; 5/17/2023
- Three ways to add an iCloud.com address, even if you already have one
AppleID w/o icloud.com address; aliases; new AppleID; MW; 3/20/2023 - How to add an alias email address to your iCloud account MW; 1/23/2023
- How to use iCloud to create rules that automatically sort, delete, & forward Mail ApIn; 9/29/2021
- How to Set Up Custom Email Domains with iCloud Mail TB; 8/27/2021
- Apple announces iCloud+ with privacy-focused features
Private Relay: combines DNS-over-HTTPS with proxy servers);
Hide my email: generate random email addresses;
TC; 6/7/2021 - iCloud email won't send? Here's what to check to fix it
Invalid iCloud sender address;
Too many (> 500) recipients in one message;
Too many recipients across all messages (daily limits);
Attachment size exceeded (w/o MailDrop); MW; 3/4/2021 - How to Set Up and Use iCloud Email Aliases OSXD; 8/15/2020
- How to use iCloud aliases to send and receive email MW; 1/15/2020
iOS
- How to Change Your Default Email and Web Clients in iOS 14 and iPadOS 14 TB; 9/25/2020
- Why the iOS Mail app shows a phantom unread message badge and what to do about it sorting glitch; MW; 7/16/2020
- How to Keep Yourself Safe From the Zero-Day iOS Mail Attacks update imminent, or change from Mail client? LH; 4/23/2020
- How to Add AOL Account to Mail on iPad & iPhone OSXD; 2/16/2020
- How to Fix "No Sender" & "No Subject" Mail Bug in iOS 13 & iPadOS 13 OSXD; 9/28/2019
- Five of the Best Email Apps on iOS Spike, Polymail, Airmail, Spark, Edison Mail; MR; 1/31/2019
macOS
- Wikipedia: Apple Mail
- Take Control: Apple Mail
- How to stop macOS Mail from using a bad email address MW; 7/8/2021
- Can't Scroll a Message in Mail? Here's One Reason Why embedded IFRAME; TB; 3/4/2021
- How to consolidate mail from multiple Macs using Apple Mail MW; 10/30/2020
- Twelve years later, Apple is still trying to erase mac.com email addresses and me.com; ApIn; 8/31/2020
- How to Add an Outlook.com Email Address to Mac Mail OSXD; 2/8/2020
- Apple is fixing encrypted email on macOS because it's not quite as encrypted as we thought Verge; 11/8/2019
- How does Apple's "click to unsubscribe" feature in Mail work? 10/19/2019
- How to Format Emails on Mail for Mac the Easy Way OSXD; 3/21/2019
- If you can't get macOS Mail to work after upgrading to two-factor authentication, here's a way to fix it MW; 1/23/2019
Outlook, Hotmail
- Wikipedia: Microsoft Outlook
- Microsoft Outlook for Mac Now Free, with Strings Attached
no Office license or Microsoft 365 subscription required;
ad-supported and requires the “New Outlook” user interface; TB; 3/8/2023 - Your Microsoft Exchange Server Is a Security Liability
Endless vulnerabilities. Widespread hacking campaigns. Slow and technically tough patching.
It's time to say goodbye to on-premise Exchange; Wired; 10/21/2022 - Microsoft Office 365 vulnerability lets hackers sidestep email encryption 10/14/2022
- Microsoft adds support for custom '+' email addresses in Office 365 feature already present in Hotmail; Ars; 7/13/2020
- Hackers could read non-corporate Outlook.com, Hotmail for six months Ars; 4/15/2019
Reply All
- SNAFU: The Air Force Just Survived a Reply-All Apocalypse
'email storm' or a 'Replyallcalypse'; Giz; 9/3/2022 - How to Handle the Dreaded 'Reply All Moment' 'humailiation'; 1/17/2019
Spam
- Wikipedia: spam email
- HowStuffWorks: How Spam Works
- Gmail: Your address is similar but has more or fewer dots (.) or different capitalization
- Email Unsubscribe Services Don’t Really Work
privacy, pricey, ineffective.
Follow This (Free) Advice Instead.
1. Hit the Unsubscribe button or link; 2. Mark it as spam;
3. Set email rules and filters; 4. Create an email alias; NYT; 1/19/2024 - You’ve Got (Scam) Mail
is everyone being swindled all the time and just not talking about it? NYT; 9/22/2023 - Personalized AI-Written Spam May Soon Be Flooding Your Inbox Giz; 4/23/2023
- An Annotated Field Guide to Identifying Phish TB; 1/16/2023
- 10 of the Biggest Scams of 2022 LH; 12/287/2022
- No, You Haven't Won a Yeti Cooler From Dick's Sporting Goods
it circumvents some of Google's robust anti-spam tools for Gmail; Wired; 12/23/2022 - The Top 10 Scams of 2022 LH; 12/17/2022
- Ongoing phishing campaign can hack you even when you’re protected with MFA Ars; 7/12/2022
- How to Help a Friend Whose Email Has Been Hacked to Send Scams TB; 5/5/2022
- How to Spot the Seasonal Scams
IRS, charities, Ukraine; NYT; 3/30/2022 - Why Are Online Scams Called 'Phishing'? MF; 1/20/2022
- 4 Steps to Change Your Email Address AARP; 1/12/2022
- I maxed out the number of spammy addresses Gmail can block Ars; 11/20/2021
- Cut Down on Junk Mail with iCloud+'s Hide My Email TB; 10/21/2021
- Beware this new phishing attack that's after your passwords!
that (redirect) email link might not send you where you expect; PC; 9/1/2021 - How to protect yourself from phishing emails
Disable loading images; Don’t click on site links in email;
Hover over links before clicking; Look for warnings in email;
Check the padlock; Watch for blatant/moderate security warnings;
Use a password manager; MW; 6/25/2021 - The Young Fall for Scams More Than Seniors Do. Time for a Warning. NYT; 6/25/2021
- How to Tell the Difference Between a Spam Email and a Scam LH; 6/1/2021
- How to spot an online scam: 3 dead giveaways PC; 4/29/2021
- How to Avoid Phishing Emails and Scams
Always Think Twice Before Clicking;
Consider the Source;
Lock Your Accounts Down (PM, 2FA); Wired; 2/16/2021 - Who's Making All Those Scam Calls? NYT; 1/27/2021
- GoDaddy: Sorry We Promised Holiday Bonuses, That Was Just a Phishing Test Giz; 12/25/2020
- Avoid This Fake Zoom Meeting Invite Phishing Scam LH; 12/2/2020
- How to Spot the Latest Netflix Phishing Scam LH; 7/29/2020
- Environmentalists Targeted Exxon Mobil. Then Hackers Targeted Them. NYT; 6/9/2020
- Iran- and China-backed phishers try to hook the Trump and Biden campaigns Ars; 6/4/2020
- The problem with Apple Mail's junk filtering if your email provider changes how it marks messages as spam, they have to provide controls, too; MW; 5/25/2020
- GitLab runs phishing test against employees – and 20% handed over credentials 5/21/2020
- How to Avoid Spam—Using Disposable Contact Information the next time you sign up for a coupon code or retail promotion, use these apps to avoid spam text and email messages; Disposable Email Addresses: Sign in with Apple, 10 Minute Mail; Guerrilla Mail; Burner Mail; Firefox Private Relay; Disposable Cell Numbers: Burner; Wired; 5/16/2020
- List of all known Coronavirus (COVID-19) Scams 5/2020
- Don't Share a Screenshot of Your Stimulus Payment Online LH; 4/23/2020
- Deep dive on a “sextortion” spam email scheme that raked in 50.98 BTC, or ~$473K, over five months and, on some days, accounted for 20%+ of all observed spam; 4/22/2020
- So you received the Bitcoin 'sextortion vid' email -- here's what to do TNW; 4/20/2020
- How to Avoid the New 'NetSupport Manager' Phishing Scam LH; 3/3/2020
- How Can I Tell if This 'Sextortion' Email Is Legit? LH; 2/21/2020
- Don't Click on Links in Texts From 'Your Bank' enter link yourself, or use mobile app; LH; 2/17/2020
- How to Protect Yourself From Real Estate Scams NYT; 1/3/2020
- Researcher Releases Data on 100,000 Phishing Attempts This massive dataset can help teach and understand phishing better; MB; 12/16/2019
- Cybercrime Booms As Scammers Hack Human Nature To Steal Billions NPR; 11/18/2019
- The Language Of Cybercrime scripts, digitized voice; NPR; 11/18/2019
- Scammers favor malicious URLs over attachments in email phishing TNW; 11/8/2019
- PSA: Tell your parents to never wire you money before calling you first TNW; 10/30/2019
- How to stop iCloud calendar spam and junk mail steps in Apple Mail on Mac and iOS; AI; 8/26/2019
- 7 Ways to Protect Yourself from the Newest Phishing Scams on the Net
1. Be Wary of Emails Asking You To Click a Link to Confirm or Update Sensitive Details.
2. Don't Fall For Pop-Ups Asking You to Verify Account Information.
3. Even If An Email Looks Like It Was Sent By Someone You Know, Double Check the Sender's Address For Typos.
4. Be Careful When Logging Into Your Email.
5. Watch Out For "Cloned" Emails.
6. Don't Trust "Copyright Notices" on Social Media.
7. Enable Two-Factor Authentication; MF; 7/2/2019 - How to Keep Spam Out of Your Google Calendar LH; 6/24/2019
- Tricky Scam Plants Phishing Links in Your Google Calendar Wired; 6/17/2019
- Security researcher finds massive spam operation in an unsecured server now inactive, which sent 5M+ emails over 10 days that 160K+ people clicked through; discovered because spammer had forgotten to set a password; TC; 4/2/2019
- How Phishing Scams Are Evolving -- And How Not to Get Caught threatening language, misspellings, inaccuracies in the text, pressure to act quickly, attempts to cause panic, and requests to transfer money (even if you're expecting them); Giz; 3/20/2019
- Google Made a Quiz to See if You Can Identify Phishing Emails quiz; MB; 1/22/2019
Tracking
- Wikipedia: web bug object embedded in a web page or email, which unobtrusively (usually invisibly) allows checking that a user has accessed the content. Common uses are email tracking and page tagging for web analytics. Alternative names are web beacon, tracking bug, tag, or page tag. Common names for web bugs implemented through an embedded image include tracking pixel, pixel tag, 1x1 gif, and clear gif.
- How to delete an email without opening it on iPhone or Mac MW; 7/14/2022
- Apple Mail Now Blocks Email Tracking. Here's What It Means for You Wired; 5/7/2022
- DuckDuckGo launches a new Email Protection service that scans emails for trackers then forwards them from a free '@duck.com' address to a user's regular inbox \
cross-platform; Verge; 7/20/2021 - How to block tracking pixels in Apple Mail Mac blanket approach: don't load any Remote Content/Images; extensions? MW; 3/2/2021
- Spy pixels in emails have become endemic BBC; 2/17/2021
- How to Stop Emails From Tracking You LH; 7/8/2019
- How to See if Someone is Tracking Emails They Send You LH; 3/24/2019
Windows
- How to Set Up Mail on Your Windows 10 Computer LH; 5/15/2020
Yahoo
Safer Internet: Email: Anonymity, Encryption
Safer Internet: Email: Anonymity, Encryption
Summary |
References: General | iOS | macOS | PGP | ProtonMail
Summary
- If content and/or sender/receiver are extremely sensitive, additional measures may be desired beyond encryption during transit of message and attachments via HTTPS:.
- [2] Send files encrypted separately via email but transmit key via non-email-- see Encryption section, e.g., 7-zip
- Transfer via cloud or other sharing method -- see Share Files Privately
- [3] Encrypt email messages using PGP or S/MIME (requires certificate) -- or other services, e.g., Lavabit
- iOS:
Settings > Accounts & Passwords > Account > Advanced > S/MIME - [3] Send email anonymously, e.g., specialized providers
- [3] Use self-destructing email -- never stored on recipient's system
References
- {TCYOP-4: 125-131; TCYOP-3: 101-108; S/MIME; PGP/OpenPGP/GnuPG: SecureMyEmail; Proprietary encrypted email: Peerio, ProtonMail, Tutanota; Encrypted attachments; Transferring Passwords Out of Band: in person, by phone, by chat or private message, via shared knowledge; Send and Receive Email Anonymously; Use Email Alternatives; 'self-destructing' messages}
- sections: Refs: iOS; macOS; see Browsing: Tor, NSA
- Wikipedia: Email encryption; S/MIME (Secure/Multipurpose Internet Mail Extensions) requires key/certificate
- Wikipedia: GnuPG (Gnu Privacy Guard) aka GPG; open source; GPGTools/GPG Suite: encrypt, decrypt, sign and verify files or messages
- Wikipedia: Snapchat user set time limit for viewing photos/videos
- How to send anonymous emails PC; 3/4/2019
iOS
macOS
PGP
- Wikipedia: PGP (Pretty Good Privacy) commercial; Symantec
ProtonMail
- Proton Is Trying to Become Google -- Without Your Data Wired; 5/25/2022
- ProtonMail Amends Its Policy After Giving Up an Activist's Data Wired; 9/8/2021
- Russia blocks encrypted email provider ProtonMail TC; 3/11/2019
Safer Internet: Talk and Chat Privately
Safer Internet: Talk and Chat Privately
Summary |
References: General | Clubhouse | Facetime |
Google: Meet, etc. | iOS, Messages | Messenger | macOS | Phone | Robocalls | Signal |
Skype, Teams | Slack | Telegram | Webex | WhatsApp | Yik Yak | Zoom
Summary
- "I sold my users' privacy...
- [1] Check preferences -- do not assume default settings are the most secure
- [1] Read the privacy policies of (and articles about) services you use:
what they log, share or encrypt, especially 'free' services
(and especially Google and Facebook) - Text messaging, audio, video apps can be more secure than email.
- Messages and Facetime (for Apple users) are generally very private and quite secure.

 Zoom (like other meeting services) can be very private and secure, even the free version --
Zoom (like other meeting services) can be very private and secure, even the free version --- if problems are quickly fixed -- and users install updates
- if privacy & security preferences are provided and explained -- and checked! e.g.,
- user: strong unique account password; enable 2FA if avail; minimize user profile info;
click only on expected meeting links; etc. - host: keep meeting ID private; set meeting room password; use waiting rooms to admit participants; route calls outside China; etc.
- Zoom (or any communication) app may be more secure/private on iOS compared to Mac or Windows.
- Zoom's free version doesn't have ads or market your info (like some other products)
-- it's offered as 'trialware', with the hope that you'll upgrade to bypass limits (e.g., session length) and access other features. - In its early years, Zoom was slow to acknowledge & address problems; it has made substantial progress in recent months.
- Refs:Zoom (articles -- below); Strong Passwords: Zoom 'credential stuffing' explanation
- [1] Create a 2nd entry in Contacts with minimal info about you: name, phone, email;
share that with others who shouldn't have all your info! - [1] Enable sending unknown phone callers (not in your contacts) directly to voicemail, e.g.,
- iOS:
Settings > Phone > Silence Unknown Callers - [2] Install software to block robocalls
- [2] Use less common apps to improve privacy (and to avoid government monitoring?)
- [2] Consider using video (ideally) or audio instead of any text -- more difficult to capture and analyze
- [3] Secure phones
References
- {TCYOP-4: 132-136; TCYOP-3: 109-114; Understand the Privacy Risks of Real-time Communication: iMessage, Bleep by BitTorrent, Cryptocat, Peerio, Signal, WhatsApp, Wire; Security in iMessage and Other Apple Services; [3] Using Keybase for Identity Verification and Chat; Improve Your Real-time Communication Privacy: Read the privacy policies, Use end-to-end encryption when available, Use weaker encryption if necessary, use obscure products, Favor higher-bandwidth communication (over text)}
- sections: Refs: Clubhouse; Facetime; Google: Meet, etc.; iOS, Messages; Messenger; macOS; Robocalls; Signal; Skype, Teams; Slack; Telegram; Webex; WhatsApp; Yik Yak; Zoom
- topics:
- Wikipedia: Voice Over IP (VOIP); Vonage
- HowStuffWorks: How VoIP Works; Skype vs. Vonage
- Wikipedia: Secure telephone; Secure phone
- HowStuffWorks: Will the landline phone become obsolete?
- Wikipedia: Instant Messaging
- Wikipedia: Mattermost an open-source, self-hostable online chat service with file sharing, search, and integrations. It is designed as an internal chat for organisations and companies, and mostly markets itself as an open-source alternative to Slack and Microsoft Teams
- HowStuffWorks: How Instant Messaging Works; How Instant Messaging Security Works
- Ethical.net: Messaging
- One of the Last Bastions of Digital Privacy Is Under Threat encrypted messaging; NYT; 6/13/2023
- How Mobile Phones Became a Privacy Battleground -- and How to Protect Yourself NYT; 9/29/2022
- Firefox's new service gives you a burner phone number to cut down on spam Relay subscription; Verge; 10/13/2022
- Never Open a PDF from a Strange Text LH; 7/7/2022
- Best encrypted messaging apps for use across Mac, iOS, Android, and Windows MR; 6/29/2022
- Did You Receive a Text Message From Yourself? You're Not Alone. NYT; 4/6/2022
- Americans Can't Quit SMS
the world loves WhatsApp and other texting apps.
Americans are chatting in their own bubble; NYT; 2/2/2022 - How to Stop Scam Texts 'smishing'; NYT; 12/1/2021
- FBI document shows what data can be obtained from encrypted messaging apps 11/30/2021
- Remember, Communication Services Cannot Guarantee Privacy
WhatsApp, ProtonMail; TB; 9/10/2021 - FBI sold phones to organized crime and read 27 million 'encrypted' messages Ars; 6/8/2021
- Best Zoom alternatives CNet; 5/21/2022
- The best free apps for video calling
Zoom; Skype; Webex; Verge; Google Meet;
Microsoft Teams; Google Duo; Starleaf;
Jitsi Meet; Whereby; Glip Pro; 5/4/2021 - How to Stop Spam Calls
FTC's National Do Not Call Registry;
spam blocking carrier apps (not 3rd parties);
block calls not in Contacts;
landline: Anonymous Call Rejection;
more tips; NYT; 4/15/2021 - Getting started with Signal and other encrypted messaging apps PC; 3/11/2021
- Donald Trump is one of 15,000 Gab users whose account just got hacked GabLeaks includes 70,000 messages in more than 19,000 chats by over 15,000 users; Ars; 3/1/2021
- QAnon Now Getting Banned On Platforms We've Never Even Heard Of e.g., Clapper, Gab; Giz; 2/11/2021
- Are Private Messaging Apps the Next Misinformation Hot Spot? NYT; 2/3/2021
- How to Keep Internet Trolls Out of Remote Workplaces employee bad behavior; NYT; 1/24/2021
- I looked at all the ways Microsoft Teams tracks users and my head is spinning ZD; 1/17/2021
- Millions Flock to Telegram and Signal as Fears Grow Over Big Tech and privacy concerns; NYT; 1/13/2021
- What's a Simple Way to Video Chat with My Elderly Parents? LH; 1/8/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing; DuckDuckGo for Search; OsmAnd for Maps; ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020
- Wormable code-execution flaw in Jabber has a severity rating of 9.9 out of 10 Ars; 12/11/2020
- The Best Alternatives to Zoom for Remote Meetings
free: Google Meet, Discord, Facebook Messenger Rooms, FaceTime, Skype;
paid: Zoho Meetings, Zencastr; LH; 10/23/2020 - Digital Hygiene in the Zoom Era
How can I make sure private things don’t become public?
I had a minor disaster. How do I handle the situation gracefully?
What if it is not you who is being embarrassing, but your colleague?
When should I mute myself?
Can I just skip being on camera?
How do employers monitor what we do on our computers and how much do they know?
How do I know if I’m being monitored?
What if I’m on my lunch break?
I opened an inappropriate website on my work computer. What do I do?
While we’re here, someone please explain “incognito mode.”
What should I definitely not do on my work devices?
NYT; 10/23/2020 - Encrypted messaging can be intercepted an alleged plot to kidnap the governor of Michigan puts the spotlight on secure messaging apps; CNet; 10/8/2020
- Trump's WeChat and TikTok App Store Bans Are a Cybersecurity Nightmare no more security updates; Giz; 9/18/2020
- Iranian Hackers Can Now Beat Encrypted Apps, Researchers Say the hackers use a variety of infiltration techniques, including phishing, but the most widespread method is sending what appear to be tempting documents and applications to carefully selected targets; NYT; 9/18/2020
- How to Have a Productive Disagreement During a Zoom Meeting LH; 9/7/2020
- How Secure Are Your Texts, Really? podcast; Wired; 8/21/2020
- What remote learning will look like this fall in Meet, Teams, and Zoom PC; 8/11/2020
- How Remote Work Will Create Economic Winners and Losers NYT; 7/26/2020
- What comes after Zoom fatigue: the history and future of video chat Vox; 7/17/2020
- What comes after Zoom? 6/22/2020
- Become a Videoconferencing Pro with These Tips TB; 6/3/2020
- Since Zoom Won't Ensure Your Privacy, Try These Alternatives LH; 6/3/2020
- Why Does Zoom Exhaust You? Science Has an Answer on video calls, looming heads, staring eyes, a silent audience, and that millisecond delay disrupt normal human communication; WSJ; 5/27/2020
- How to use Zoom or FaceTime with an Apple TV (or any TV) MW; 5/26/2020
- This Video Chat Prediction From 1918 Was So Much Cooler Than Zoom Television and Telephot; Gernsback; Electrical Experimenter; Giz; 5/19/2020
- Mattermost reviewed TR; 5/8/2020
- How to Mirror Your Apple TV to Your Mac for Screenshots or Presentations TB; 5/7/2020
- 5 Ways to Stay in Touch With Less Tech-Savvy Family and Friends
smart devices: Amazon's Echo Show, Facebook Portal, Google Nest Hub Max;
browser: Jitsi Meet;
Write a letter; NYT; 5/6/2020 - An analysis of privacy policies of Google Meet, Microsoft Teams, and Cisco Webex finds that the services may be collecting more data than many consumers realize CR; 4/30/2020
- Companies are turning to intrusive monitoring of work-from-home employees with always-on webcam rules, virtual 'water coolers', daily check-ins, and not-so-optional company happy hours; WaPo; 4/30/2020
- Here's the NSA's guide for choosing a safe text chat and video conferencing service
assessed tools include Slack, Zoom, Signal, Skype, more: .pdf;
Does the service implement end-to-end (E2E) encryption?
Does the E2E encryption use strong, well-known, testable encryption standards?
Is multi-factor authentication (MFA) available?
Can users see and control who connects to collaboration sessions?
Does the tool's vendor share data with third parties or affiliates?
Do users have the ability to securely delete data from the service and its repositories as needed (both on client and server side)?
Is the tool's source code public (e.g. open source)?
Is the service FedRAMP approved for official US government use? ZD; 4/30/2020 - Is Your Video Chat App Secure? discusses Mozilla's reviews:
product ratings -- minimum security standards:
Encryption: Does the app/service offer it?
Security updates: How regularly is the app/service updated?
Strong passwords: How strong are the app’s password guidelines?
Manages vulnerabilities: Is there a way for people to report bugs and other security issues with the app?
Privacy policy: Does it exist?; LH; 4/29/2020 - Notes From a Videochat Memorial Atl; 4/23/2020
- The Simplest Video Chat Apps for People Who Struggle With Tech LH; 4/9/2020
- 10 Zoom alternatives for more secure, cross-platform video calls 9to5; 4/1/2020
- What Is the Most Secure Video Conferencing Software? MB; 3/31/2020
- How to Set Digital Boundaries With Friends and Family LH; 1/27/2020
- Major TikTok Security Flaws Found (and Fixed) could have let attackers manipulate content and extract personal data; NYT; 1/8/2020
- It Seemed Like a Popular Chat App. It’s Secretly a Spy Tool. ToTok, a messaging app from the United Arab Emirates that has been downloaded to millions of phones, is the latest escalation of a digital arms race; NYT; 12/22/2019
- Is It Bad That I Gchat My Friends While I’m at Work? NYT; 12/12/2019
- SMS Replacement is Exposing Users to Text, Call Interception Thanks to Sloppy Telecos RCS standard; MB; 11/28/2019
- What Is End-to-End Encryption? Another Bull’s-Eye on Big Tech; NYT; 11/19/2019
- The FCC created an online index for known phone scams FCC index; PopSci; 8/20/2019
- EFF Posts New White Paper On Stingray Device Capabilities cell-site simulators (CSS); "Gotta Catch 'Em All: Understanding How IMSI Catchers Exploit Cell Networks (Probably)"; TD; 7/15/2019
- The Best iOS Walkie Talkie Apps to Use Instead of Apple's Voxer, Two Way, Walkie-Talkie -Communications, Zello, FireChat; LH; 7/11/2019
- How To Prevent and Respond to a SIM Swap Scam LH; 6/19/2019
- Every secure messaging app needs a self-destruct button TC; 6/12/2019
- How to Make Your Phone Limit Your Screen Time for You iOS, Android; NYT; 4/1/2019
- Why Do We Need So Many Different Messaging Apps? no interoperability or standards between proprietary, 'walled gardens'; SMS, RCS? MB; 3/19/2019
- Comcast set mobile pins to '0000', helping attackers steal phone numbers Xfinity Mobile deploys fix after weak PIN system fueled number-porting attacks; Ars; 3/1/2019
- The Route of a Text Message, a Love Story the surprisingly complex journey a text message takes every time we hit 'send'; MB; 2/22/2019
- Private Messages Are the New (Old) Social Network Wired; 1/27/2019
- El Chapo Trial: How a Colombian I.T. Guy Helped U.S. Authorities Take Down the Kingpin "In a daring move that placed his life in danger, the I.T. consultant eventually gave the F.B.I. his system's secret encryption keys in 2011 after he had moved the network's servers from Canada to the Netherlands during what he told the cartel's leaders was a routine upgrade"; NYT; 1/8/2019
Android; Allo
Clubhouse
- Clubhouse and its clones have an accessibility problem Verge; 6/8/2021
- Clubhouse's security and privacy lag behind its explosive growth Ars; 2/28/2021
- Join Clubhouse! Umm, What Is Clubhouse? NYT; 2/22/2021
Facebook Messenger
- Messenger Rooms, Facebook’s 50-caller Zoom competitor, is now available TNW; 5/14/2020
- How to Make Video Calls with Facebook Messenger OSXD; 5/7/2020
- Facebook Messenger Rooms challenges Zoom with free, unlimited group video calls PC; 4/24/2020
- Zuckerberg Plans to Integrate WhatsApp, Instagram and Facebook Messenger NYT; 1/25/2019
Facetime
- How to Use FaceTime Screen Sharing and SharePlay
iOS/iPadOS 15.1; TB; 11/8/2021 - Apple Was Slow to Act on FaceTime Bug That Allows Spying on iPhones NYT; 1/29/2019
- Apple Disables Group FaceTime After Security Flaw Let Callers Secretly Eavesdrop NPR; 1/29/2019
Google: Meet, etc.
- How Google Meet Weathered the Work-From-Home Explosion Wired; 8/11/2020
- Google Meet is now free for everyone, as the pursuit of Zoom continues Google Meet was restricted to paying G Suite users, but not anymore; still requires Google account, such as a Gmail email address; PC; 6/17/2020
- Android; Google Meet passes 50 million downloads, boosted by coronavirus 5/17/2020
- Google's Zoom rival, called Meet, is now free to consumers increase to 60 minutes (until 9/30); requires Google account; previously paid G Suite customers could host; CNet; 4/29/2020
iOS; Messages; Facetime
- How to get back deleted text messages on your iPhone MW; 3/25/2024
- New iMessage PQ3 Encryption Protocol Protects Against Post-Quantum Attacks TB; 2/23/2024
- iOS 17.2: Turn On Contact Key Verification With These Easy Steps CNet; 12/22/2023
- Apple announces RCS support for iMessage instead of SMS/MMS; Ars; 11/16/2023
- The Easiest Ways to Sync iMessages Across All Your Devices LH; 1/19/2023
- You Can Export Your Entire iMessage History LH; 1/19/2023
- How to Use Apple Notes to Have Secret Chats With Others
not as safe as an encrypted messaging app, but it can work in a pinch; LH; 6/27/2022 - How to Use Email Instead of Phone Number for iMessage on iPhone & iPad OSXD; 7/25/2021
- How to share your Mac's screen the quick and easy way in Messages MW; 1/20/2021
- How to Get SMS Text Messages Across All Your Apple Devices LH; 9/24/2020
- How to Secretly Open iMessages Without Triggering Read Receipts LH; 7/30/2020
- Troubleshooting FaceTime on iPhone and iPad OSXD; 7/20/2020
- How to Share iPhone & iPad Screen with AnyDesk OSXD; 6/8/2020
- Do you use Wi-Fi Calling? Here's how to check if it's active on your iPhone Wi-Fi Calling is a helpful feature in improving call quality, but seems to turn itself off; MW; 5/11/2020
- PSA: New Character Bug in Messages Causing iOS Devices to Crash also Mail; update imminent; MR; 4/23/2020
- How to Block Unwanted Emails, Phone Calls, and Messages in iOS 13 LH; 9/25/2019
- What Actually Happens When You Block Someone on Your iPhone LH; 9/17/2019
- Google Hackers Found 10 Ways to Hack an iPhone Without Touching It MB; 8/12/2019
- How to Make & Receive Phone Calls with iPad via your iPhone; OSXD; 2/28/2019
macOS
- How to set up your Mac and iPhone for texts and calls same AppleID; Verge; 6/24/2020
Phone
- 10 Free Reverse Phone Number Lookup Sites MW; 11/30/2023
- What Is Wifi Calling and How to Enable It on Your Phone LH; 11/25/2023
- The Best Cell Phone Plans NYT; 7/25/2023
- The Best Cheap Phone Plans Wired; 2/5/2023
- Always Do This Before Letting Someone Borrow Your Phone
Android: Guest Mode; Screen Pinning;
iOS: Accessibility: Guided Access; LH; 6/1/2022 - Best Cheap Phone Plans: Affordable Alternatives to Verizon, T-Mobile and AT&T CNet; 5/31/2022
- Steps to Simple Online Security: 7: Secure Your Smartphone;
Send messages and files safely NYT; 4/22/2022 - How to Stop Verizon, AT&T, and T-Mobile From Collecting Your Phone Data to Sell Ads LH; 12/8/2021
- Criminal hackers are now going after phone lines, too
VoIP; NPR; 12/6/2021 - How to Stop Butt Dialing Everyone with Your Smartphone Wired; 8/20/2020
- How to Buy a Burner Phone LH; 6/4/2020
- What Actually Happens When You Block Someone on Your iPhone LH; 5/6/2020
- How to Turn Your Smartphone Into a Webcam Using a phone (old or new) as a camera for your Zoom meetings is an easy and affordable way to be visibly present if you don't have a webcam; Wired; 5/4/2020
- How to Make Phone Calls From Your Computer LH; 4/3/2020
- How to Use 'Do Not Disturb' on Your Phone (While Still Letting Important Calls Through) iOS, Android; NYT; 1/24/2019
Robocalls
- How to Block Spam Calls
to forward spams to your carrier:
1. tap and hold down on the message;
2a. iPhone: tap 'More', then press the forward button (arrow on the bottom-right corner of the screen)
2b. Android: When a menu pops up, select "Forward Message"
3. Enter 7726 in the recipient field and hit send;
NYT; 5/26/2022 - How to Block Spam Calls and Text Messages Wired; 3/12/2022
- How Do You Stop Robocalls? NYT; 7/12/2021
- Caller ID Authentication May Tame the Scourge of Spam Calls TB; 3/18/2021
- Robocall blocking apps caught sending your private data without permission e.g., Hiya, TrapCall, TrueCaller; TC; 8/9/2019
- Stop Robocalls on Your iPhone, Once and for All LH; 5/6/2019
- Robocalls Are Getting Worse. How Do We Stop Them? Verge; 5/3/2019
- Phone Companies Are Testing Tech to Catch Spam Calls. Let's Hope It Works. a new standard, called Stir/Shaken, could come to your mobile provider by the end of the year. But there are already ways around it; NYT; 4/26/2019
- What you can do right now to stop robocalls Verizon, ATT, T-Mobile, Sprint, Google, Comcast; CNN; 3/29/2019
Signal
- Signal's rapid growth following WhatsApp privacy changes has raised concerns from Signal staff who worry the service's new features will be misused Verge; 1/25/2021
- Signal Provides Secure Cross-Platform Replacement for WhatsApp TB; 1/18/2021
- Signal has better privacy policies than WhatsApp or Telegram -- here's why TNW; 1/11/2021
- Hacker Lexicon: What Is the Signal Encryption Protocol? becoming de facto standard for end-to-end encryption; Wired; 11/29/2020
- How to Use Signal Encrypted Messaging Wired; 8/18/2020
- Signal's New PIN Feature Worries Cybersecurity Experts your contacts stored in the cloud; Verge; 7/10/2020
- Signal Downloads Are Way Up Since the Protests Began organizers and demonstrators say they feel safer communicating with end-to-end encryption; NYT; 6/11/2020
- How to Add PIN Security to Your Signal Account LH; 5/21/2020
- Signal to move away from using phone numbers as user IDs ZD; 5/20/2020
- Signal Is Finally Bringing Its Secure Messaging to the Masses Wired; 2/14/2020
Skype, Teams
- Wikipedia: Skype
- HowStuffWorks: How to Use Skype
- How to use Microsoft Teams with your friends and family Verge; 8/7/2020
- How to Group Video Chat with Skype on iPhone & iPad OSXD; 4/18/2020
- Skype Meet Now is Microsoft's effort to make Skype calls as easy as possible PC; 4/3/2020
- Skype tries competing with Zoom by reminding people that they don’t need the app or an account to make a call Verge; 4/3/2020
- Skype 8.41 merge an incoming call with the current call; resize your video preview; TB; 3/13/2019
- Microsoft introduces background blur feature to Skype, which uses AI to detect the user's hair, hands, and arms, and blur distracting objects in the background Giz; 2/7/2019
Slack
- All the Ways Slack Tracks You -- and How to Stop It e.g., changing privacy settings, putting limits on those infuriating notifications; Wired; 10/29/2020
- What if All Your Slack Chats Were Leaked? Slack stores everything you do on its platform by default -- your username and password, every message you've sent, every lunch you've planned and every confidential decision you've made. That data is not end-to-end encrypted -- accessible by Slack, law enforcement, hackers; NYT; 7/1/2019
Telegram
- 8 Telegram Privacy Settings You Should Enable Immediately LH; 5/17/2022
- Fleeing WhatsApp for Better Privacy? Don't Turn to Telegram it doesn't encrypt conversations by default—or at all for group chats; Wired; 1/27/2021
- Telegram, Pro-Democracy Tool, Struggles Over New Fans From Far Right NYT; 1/26/2021
- How Telegram evaded its Russian ban ban lifted earlier this month; Verge; 6/29/2020
- Telegram adds the option to delete chats on other people's devices Verge; 3/25/2019
Webex
- How to Use Webex Meetings for Videoconferencing on iPhone & iPad Virtual Backgrounds; OSXD; 5/5/2020
- WhatsApp "end-to-end encrypted" messages aren't that private after all
millions of WhatsApp messages are reviewed by both AI and human moderators; Ars; 9/8/2021 - The 5 best WhatsApp alternatives
Signal, Wire, Telegram, Viber, Keybase; PC; 5/19/2021 - The Truth About Your WhatsApp Data NYT; 1/13/2021
- WhatsApp Has Shared Your Data With Facebook for Years, Actually since 2016; Wired; 1/8/2021
- Use 2FA to Stop This New WhatsApp Account Attack LH; 11/28/2020
- For Better Privacy, Use These Apps Instead of WhatsApp’s New Disappearing Messages Signal, Telegram, Viber; LH; 11/2/2020
- How to Boost WhatsApp's Privacy and Better Protect Your Data Wired; 9/7/2020
- WhatsApp: Israeli firm 'deeply involved' in hacking our users e.g., humans rights activitsts; Guard; 4/29/2020
- How to Get Up to 8 People on a WhatsApp Video Call LH; 4/22/2020
- WhatsApp says flaw let attackers install NSO Group surveillance software on iPhones and Android phones since May via the app's call function; flaw now patched 5/13/2019
- The Best WhatsApp Alternatives Signal, Viber, Telegram, GroupMe; LH; 1/25/2019
Yik Yak
Zoom
- OLLI: Basic Zoom Instructions
- Download Zoom (app): Mac, Windows; iOS: Apple App Store; Android: Google Play Store;
note: it's possible to run a browser version of Zoom (without an installed plugin);
however, see browser & feature limitations - Zoom: Getting Started: Mac, Windows; iOS; Android;
note: for viewing presentation materials/demos, a tablet or desktop screen is preferable to a phone - Zoom: Privacy and Security
- Zoom: Best Practices for Securing Your Zoom Meetings .pdf
- Zoom 5.17.10 TB; 3/5/2024
- Zoom Videoconferencing App Now Available for the Apple TV TB; 12/6/2023
- Zoom is adding new options for sharing your pronouns Verge; 6/22/2021
- Researchers identify causes for Zoom fatigue intense close-up eye contact, constantly seeing own reflection, reduced mobility, and increased cognitive load; It’s not just Zoom. Popular video chat platforms have design flaws that exhaust the human mind and body. But there are easy ways to mitigate their effects; Stan; 2/23/2021
- How to Give Presentations and Demo Apps in Zoom TB; 2/5/2021
- Why Insider 'Zoom Bombs' Are So Hard to Stop most calls to disrupt videoconferences originate with the participants, especially in high schools and colleges; Wired; 2/3/2021
- New Zoom features are prepping for a hybrid world when you go back to the office Zoom Rooms is adding the ability to count the number of people in conference rooms to maintain social distancing, and measure air quality; CNet; 2/3/2021
- A brief look at the evolution of video chat during 2020
as Zoom, Microsoft, and others added features to make the medium more interactive and easier to use; WSJ; 12/31/2020 - How Zoom made video meetings easy for workers, students and all of us in 2020
Zoom's chief product officer explained the company'' massive growth during the pandemic and where it's going next; CNet; 12/30/2020 - Avoid This Fake Zoom Meeting Invite Phishing Scam LH; 12/2/2020
- How to Stop a Zoombombing Suspend Participant Activities; warning if meeting invite appears in any public social media posts or other websites; LH; 11/18/2020
- Zoom unveils At-Risk Meeting Notifier, a feature that scans the net for posted Zoom meeting links and alerts meeting organizers to potential Zoombombing attacks ZD; 11/16/2020
- Zoom's end-to-end encryption (E2EE) has arrived Mac, PC, iOS, Android; when it's enabled several features like cloud recording, telephone dial-in, and 1:1 private chat will not work; how to enable; first of 4 E2EE phases; Verge; 10/27/2020
- Zoom to start first phase of E2E encryption rollout next week TC; 10/14/2020
- Zoom’s mobile and desktop apps now support two-factor authentication previously only available via the web; Verge; 9/11/2020
- Zoom Reports Partial Outage as Many Schools Return to Remote Learning Zoom said it had 'identified the issue' and was working to resolve the problem for users unable to start or join meetings; NYT; 8/24/2020
- How to change your name and add a photo to Zoom Verge; 8/14/2020
- 11 Handy Zoom Hacks to Make Your Digital Life Easier LH; 7/20/2020
- Amid pressure, Zoom will end-to-end encrypt all calls, free or paid non-paying users will have to verify themselves with a phone number in a one-time process (to stop bad actors from creating multiple abusive accounts); if encryption's turned on, participants with traditional PSTN phone lines can’t join in; TNW; 6/17/2020
- Zoom defenders cite legit reasons to not end-to-end encrypt free calls Ars; 6/4/2020
- How to Look Better on Zoom with 'Touch Up My Appearance' OSXD; 5/28/2020
- How to Use Zoom Virtual Backgrounds on iPhone & iPad OSXD; 5/6/2020
- No, the Best Doesn't Win 'It just works' are some of the most powerful words in technology; NYT; 4/27/2020
- Zoom: It's Here! 5 Things to Know About Zoom 5.0
1. AES 256-bit GCM encryption; 2. 'Report a User' (misuse) feature; 3. New encryption icon;
4. Enhanced data center information; 5. Enhancements to ending/leaving meetings; Additional security enhancements; 4/27/2020 - Zoom's Biggest Rivals Are Coming for It Facebook: video group chats for as many as 50 people on Facebook Messenger, WhatsApp video calls for up to eight people and video calls in Facebook Dating; Google: Meet video chat app accessible through Gmail; Cisco: Webex teleconferencing service; Verizon: acquiring BlueJeans Network, a videoconferencing service; Epic Games: Houseparty, a video chat app; NYT; 4/24/2020
- Zoom Daily Users Surge to 300 Million Despite Privacy Woes BB; 4/22/2020
- Zoom rolls out its 5.0 update focused exclusively on security and privacy features including easier call management and upgrading encryption; 4/22/2020
- Zoom fatigue is now setting in s it moves from being a social lifeline to a chore, used for all interactions while aggravating anxieties in an exhausting time; 4/22/2020
- Zoom's Security Woes Were No Secret to Business Partners Dropbox privately paid top hackers to find bugs in software by the videoconferencing company Zoom, then pressed it to fix them; NYT; 4/20/2020
- How to Share Screen with Zoom on iPhone & iPad OSXD; 4/16/2020
- Zoom Repairs Flaws and Improves Privacy TB; 4/15/2020
- Hackers Are Selling a Critical Zoom Zero-Day Exploit for $500,000 1 Mac; 1 Windows: exploit requires the hacker to be in a call with the target; MB; 4/15/2020
- Getting Dumped During A Pandemic "Zumping": the internet connection wasn't great, so we kept freezing. "We're breaking up," I said — and we were! 4/13/2020
- Zoom will let paying customers pick which data center their calls are routed from Free users can’t change their region, but data won’t be routed through China; Verge; 4/13/2020
- Zoom: Every security issue uncovered in the video chat app CNet; 4/13/2020
- Zoom removes meeting IDs from client title bar to boost security BC; 4/8/2020
- The Lesson We Are Learning From Zoom use with meeting passwords, avoid for sensitive issues? NYT; 4/8/2020
- How to Prevent 'Zoombombing' in a Few Easy Steps NYT; 4/9/2020
- Zoom Rushes to Improve Privacy for Consumers Flooding Its Service NYT; 4/8/2020
- 'Zoombombing' Becomes a Dangerous Organized Effort target for harassment and abuse coordinated in private off-platform chats; NYT; 4/3/2020
- Every Zoom Security and Privacy Flaw So Far, and What You Can Do to Protect Yourself TB; 4/3/2020
- Zoom Has Security Flaws. It's Still Fine to Use MB; 4/3/2020
- Security tips every teacher and professor needs to know about Zoom, right now
Make sure meetings are password protected;
When possible, don't announce meetings on social media or other public outlets;
Carefully inspect the list of participants periodically;
Carefully control screen sharing;
Disable the Join Before Host setting;
Use the Waiting Room option to admit participants;
Lock a meeting;
Be aware of everything that's within view of your camera; Ars; 4/2/2020 - New York Attorney General Looks Into Zoom’s Privacy Practices NYT; 3/30/2020
- Now that everyone's using Zoom, here are some privacy risks you need to watch out for Tattle-tale (attention-tracking) feature; Cloud snitching; Data gossip; CNet; 3/28/2020
- A look at the rise of 'Zoombombing', where trolls disrupt public Zoom conferencing calls by using the service's screen-sharing feature to share graphic content NYT; 3/20/2020
Safer Internet: Keep Social Media Sort of Private-ish
Safer Internet: Keep Social Media Sort of Private-ish
Quotes | Summary |
References: General | Dating | Facebook | Genealogy, DNA Testing |
Instagram | LinkedIn | Mastodon | Metaverse | NextDoor | Parler | Tiktok | Twitter / X
Quotes
- "If it's free,...
- "Here is an essential truth about Facebook:...
- "How do we consume as much of...
- Q: Why is Facebook like a refrigerator?...
- Q: Why is Facebook like Jail?...
- "Can we go back to using Facebook for what it was originally for...
- "I used to wonder what it'd be like to read other people's minds...
- "Benefits of unplugging from Facebook:...
Summary
- "Social" media is by its nature un-private.
- "Free" services rely on collecting and selling your information.
- [1] Consider limiting the info & photos that you post or share -- it's difficult to delete
- [1] Don't assume 'private' messages really are; Don't assume 'secret' services really are
- [1] Limit friend lists and apps
- [1] Review vendors' Terms & Conditions: these are incomprehensible and changing,
and grant them broad rights to use your freely given info -- pretty much however they want - [1] Review the privacy policies & settings for each site or service you use;
{Figure 17: TCYOP-4: 143; TCYOP-3: 117} - Policies: e.g., Facebook; Google; Linkedin; Twitter
- Settings: e.g., Facebook; Google+; Linkedin; Twitter
- [1] Realize that sensitive info, e.g., health, financial, entered in other apps may be shared with Facebook, without your permission -- hopefully this will decrease as more of these apps/practices are exposed
- [1] Don't use SSO (Single Sign On) to log into 3rd party sites using your Facebook credentials
- [1] Minimize Facebook tracking of your browsing activities across the web:
- on computer: use Firefox web browser, with Facebook Container add-on that isolates your browsing activities from Facebook.
- on your phone: delete the Facebook mobile app and use Facebook.com only via the mobile browser.
Install a tracker blocker, like Disconnect.me, and activate the blocking.
Alternatively, you can install a private web-browsing app like Firefox Focus,
which blocks trackers by default, and only use this browser when loading Facebook.com. - [1] Beware of impostors, e.g., a sockpuppet is an online identity used for purposes of deception; catfishing is a type of deceptive activity where a person creates a sock puppet social networking presence, or fake identity on a social network account, usually targeting a specific victim for deception.
- [1] Avoid providing personal details to 'fun' polls / quizzes
-- now available to marketers, and to hackers ('secret answers' for accounts) - [1] When you finally realize that the settings & privacy policies & empty promises of the major players don't actually protect you or your information, drastically minimize your usage or just deactivate / remove your account
- [1] Enable 2-Factor Authentication (2FA) -- see Passwords: 2FA
- [2] If you must share information with a group, switch to services that do support privacy, e.g., Slack.
The inertia of moving your family / friends / workgroup also makes this option particularly difficult - [2] Request the data they've collected about you, e.g., Facebook;
see section Who Wants Your Private Data : Companies
References
- {TCYOP-4: 137-146; TCYOP-3: 115-120; Understand the Privacy Risks of Social Media: Check Your Privacy Settings; Use Other Social Media Precautions: HTTPS:, passwords, Limit your friend lists, Don't assume "private" messages really are, Don't assume "secret" services really are, Limit apps, Think carefully about pseudonyms; When Privacy Hurts}
- sections: Refs: Dating; Facebook; Genealogy, DNA Testing; Instagram; LinkedIn; NextDoor; Parler; Tiktok; Twitter
- topics: GDPR,
- Wikipedia: social networking service: Facebook; LinkedIn
- Wikipedia: Cyberbullying; troll; revenge porn
- HowStuffWorks: What is a social networking site?
- HowStuffWorks: Top 10 Things You Should Not Share on Social Networks
- HowStuffWorks: What are the pros and cons of social networking sites?
- HowStuffWorks: Why do people share embarrassing information online?
- AARP: Social Media TEK (Technology Education and Knowledge) Center
- Ethical.Net: Social media; Conferences & Meetups; Team collaboration
- What is Bluesky? Everything to know about the app trying to replace Twitter TC; 11/14/2023
- Is Social Media Addictive? Here’s What the Science Says. NYT; 10/25/2023
- Try Topical Alternatives to Social Media TB; 10/18/2023
- 11 Social Media Platforms You Probably Forgot Existed (And Why They Failed)
Orkut, Google Buzz, Google+, Friendster, Ping, FriendFeed,
Vine, Periscope, Path, Yik Yak, Yahoo! 360; MF; 9/20/2023 - How the Social Media Wars Will Change the Internet NYT; 7/15/2023
- The Five Best Twitter Alternatives LH; 7/5/2023
- Threads, Instagram's 'Twitter Killer,' Has Arrived NYT; 7/5/2023
- An overview of Twitter alternatives, including Mastodon, Bluesky, and Nostr, and how they might evolve and improve
6 months after Elon Musk's takeover; TD; 4/28/2023 - The Future of Social Media Is a Lot Less Social mostly brands and influencers; to restore a sense of community, some users are trying smaller social networks; NYT; 4/19/2023
- The best Twitter alternatives worth checking out TC; 1/27/2023
- Is Your Future Distributed? Welcome to the Fediverse! e.g., Mastodon; TB; 1/27/2023
- Stop Using Social Media Apps. The Web Version Is Often Better Wired; 12/31/2022
- The Great Delusion Behind Twitter: The Town Square NYT; 12/11/2022
- A profile of iNaturalist, a not-for-profit social network that uses an ML algorithm
to help users identify plants and animals, driving cooperation and consensus NYT; 12/9/2022 - A Journey Into the Misinformation Fever Swamps
disinformation and misinformation on social media; NYT; 8/26/2022 - This site exposes the creepy things in-app browsers from TikTok and Instagram might track InAppBrowser.com; Verge; 8/19/2022
- Instagram and Facebook Could Track Everything You Do in Their In-App Browsers TB; 8/15/2022
- The Least-Awful Social Media Sites for Anyone Who Wants to Be Less Unhappy
MeWe, WT.Social, 500px, Discourse, etc.; LH; 7/6/2022 - Truth Social Review: Trump's Uncensored Social App Is Incomplete
app is inundated with phony accounts and features that don’t work. It also hides some posts, including those with curse words; NYT; 4/287/2022 - Steps to Simple Online Security: Lock down social media accounts;
Digital security for online dating and sexting NYT; 4/22/2022 - How to Stop Doomscrolling -- With Psychology Wired; 3/30/2022
- How to Set Healthy Boundaries Around What You Share Online Wired; 3/26/2022
- AARP-backed social network looks to lure older users from Facebook
Senior Planet Community focuses on shared interests, discourages off-topic political rants; Ars; 3/23/2022 - Trump's Truth Social has been almost entirely inaccessible in its first few days due to technical glitches, a 13-hour outage, and a 300,000-person waitlist WaPo; 2/23/2022
- Trump's Truth Social Is Poised to Join a Crowded Field
hard-right alternative to Twitter; NYT; 2/18/2022 - How to Beat Social Media Algorithms (and Why You Should Try)
Don't confirm the algorithm’s assumptions;
Eliminate suggested feeds when possible;
Use platforms without your account when possible;
Use a burner account; LH; 1/17/2022 - Can We Have a Meaningful Life in a Virtual World? David Chalmers; NYT; 12/10/2021
- He Conceived of the Metaverse in the '90s. He’s Unimpressed With Mark Zuckerberg's. Neal Stephenson; NYT; 12/13/2021
- Apple's Privacy Policy Cost Snap, Facebook, Twitter, and YouTube an Estimated $9.85 Billion in Revenue
Apple's App Tracking Transparency policy; Giz; 10/31/2021 - The First Amendment in the Information Age
podcast; transcript; Yale; 10/4/2021 - A look at content moderation on Clubhouse, where discussions have included homophobia, anti-Semitism, harassment, and the like, as media increases its scrutiny Bloom; 1/26/2021
- MeWe: Fast-Growing Alternative To Facebook And Twitter Finds Post-Trump Surge 'Messy' NPR; 1/22/2021
- 6 Privacy-Focused Alternatives to the Apps You Use Every Day Signal for Messaging; Firefox for Web Browsing; DuckDuckGo for Search; OsmAnd for Maps; ProtonMail for Email; Jumbo for Social Media; Wired; 12/13/2020
- How Trump's presidency has changed the internet from fueling conspiracy theories to forcing social media platforms to reexamine their content policies; Atl; 10/30/2020
- How Facebook and Other Sites Manipulate Your Privacy Choices dark patterns; 'Privacy Zuckering': when “you are tricked into publicly sharing more information about yourself than you really intended to; Wired; 8/12/2020
- What Is Randonautica Really About? NYT; 7/31/2020
- Vet Your Social Media before hitting like or retweet on a post about the protests, it’s important to know that the accounts you are following are trustworthy; NYT; 6/17/2020
- Let's Go Through Trump's Terrible Internet Censorship Order, Line By Line Spoiler: you can't nationalize Twitter; Verge; 5/29/2020
- Finally, There's a Social Network Without Any People Botnet; MB; 2/13/2020
- Why Is Social Media So Addictive? Giz; 2/10/2020
- You’re probably more susceptible to misinformation than you think 1/10/2020
- Should You Send That DM? direct messaging; NYT; 12/10/2019
- Wikipedia’s co-founder takes on Facebook with ad-free social network WT:Social; TNW; 11/15/2019
- We Need a PBS for Social Media Instead of breaking up Facebook, America should create a public alternative; NYT; 9/24/2019
- Build an Online Presence Without Giving Up Privacy careers; NYT; 9/3/2019
- The Horrible Place Between the Apps addiction; many of us have half-quit apps like Twitter and Instagram; NYT; 7/4/2019
- Watch out for Social Media Scams and Protect Your Data AARP; 6/2019
- 7 Pieces of Personal Information You Should Think Twice About Sharing On Social Media
1. Your Phone Number;
2. Your Home Address;
3. Pictures of Your Passport Or Driver's License;
4. Your Hometown and Full Date Of Birth;
5. Your Financial Information;
6. Answers To Your Password Security Questions;
7. Clubs Or Other Affiliations; MF; 5/30/2019 - Pl@ntNet, a social collaborative app for identifying plants shows how good social media can be without the engagement imperative; 5/25/2019
- The New Social Network That Isn't New at All email newsletter; NYT; 3/19/2019
- How TikTok Is Rewriting the World an app for making and sharing short videos; NYT; 3/10/2019
- How to Find Websites That Won't Give Out Your Private Information some websites are encrypted, some are ad-free; LH; 2/6/2019
- Research shows self-reported heavy Facebook users make impaired decisions, like drug addicts on a classic test of maximizing rewards; TC; 1/10/2019
Dating
- Best dating apps/sites CNet; 8/31/2023
- When Romance Is a Scam NYT; 3/27/2020
- 30% of US adults say they have used a dating app or website up from 11% in 2013, with 12% saying they found a long-term relationship via online dating; Pew; TC; 2/6/2020
- Grindr and OkCupid Spread Personal Details, Study Says NYT; 1/13/2020
- How to Maintain (Relative) Privacy on Dating Apps Edit details pulled from your social media accounts; Don’t give out your number so quickly; Turn off location settings; Consolidate your dating identities; Delete the app; LH; 2/15/2019
- FTC: Americans lost ~$143M to online dating scams in 2018, which was number one in terms of dollar loss when compared to other types of fraud NYT; 2/13/2019
- Wikipedia: Facebook
- HowStuffWorks: How Facebook Works; Myths; Quiz
- HowStuffWorks: How to Update Your Facebook Privacy Settings; Is Facebook sharing your personal information?
- for Messenger, see section Talk and Chat Privately
- Facebook Change Ensures Tracking by Preventing URL Stripping TB; 7/19/2022
- What to Know About Facebook's New 'Privacy Center' LH; 1/20/2022
- How to Recover When Your Facebook Account Is Hacked
there's only so much you can do;
Scenario 1. You let a family member or friend 'borrow' your Facebook account on your computer or phone;
Scenario 2. Someone uses your photo and name and sets up a new account;
Scenario 3. Someone guesses your account password and proceeds to lock you out of your account;
Verge; 12/7/2021 - How to Permanently Delete Your Facebook Account Wired; 10/11/2021
- Leaked documents reveal the special rules Facebook uses for 5.8M VIPs
"These people can violate our standards without any consequences."; Ars; 9/13/2021 - It's Time to Switch to a Dummy Email Address on Facebook leaked when they're set to private; LH; 4/21/2021
- Facebook Doesn't Need Your Real Phone Number LH; 1/26/2021
- How Facebook Can Slow QAnon for Real NYT; 9/21/2020
- Facebook Has Been a Disaster for the World major ways that authoritarian regimes exploit Facebook and other social media services:
organize countermovements to emerging civil society or protest movements;
frame the public debate along their terms;
let citizens voice complaints without direct appeal or protest;
coordinate among elites to rally support;
aid in the surveillance and harassment of opposition activists and journalists;
NYT; 9/18/2020 - Use These Tools to Delete All of Your Old Facebook Posts LH; 6/4/2020
- NSO Group Impersonated Facebook to Help Clients Hack Targets MB; 5/20/2020
- How a Digital Ad Strategy That Helped Trump Is Being Used Against Him NYT; 4/28/2020
- How to Stop Bots From Sending You Facebook Friend Requests LH; 1/25/2020
- Change These Facebook Settings to Protect Your Photos From Facial Recognition Software LH; 1/21/2020
- Facebook says it will no longer use phone numbers provided for 2FA for friend suggestions stopped their use for ad targeting in June; Reut; 12/19/2019
- Facebook bug shows camera activated in background during app use scrolling thru feed on iOS; CNet; 11/12/2019
- Facebook suspends tens of thousands of apps in ongoing privacy investigation Apps improperly obtained user data, installed malware, and committed other offenses; Ars; 9/20/2019
- How to Protect Your Privacy on Facebook's New Dating Service LH; 9/6/2019
- Don't Trust Facebook With Your Love Life NYT; 9/5/2019
- Facebook leak contained phone numbers for 419 million users in some cases the data included the user’s real name, gender, and country; TNW; 9/4/2019
- Many Are Abandoning Facebook. These People Have the Opposite Problem. disabled accounts; NYT; 8/22/2019
- Facebook's New Tool Lets You See Which Apps and Websites Tracked You Off-Facebook Activity; NYT; 8/20/2019
- Change These Facebook Settings to Make Your Voice Recordings More Private LH; 8/13/2019
- 5 Things to Know About Military Romance Scams on Facebook NYT; 7/28/2019
- Facebook Connected Her to a Tattooed Soldier in Iraq. Or So She Thought. Renee Holland sent her Facebook friend thousands of dollars. She became entwined in a global fraud that the social network and the United States military appear helpless to stop; Facebook seems unable or unwilling to address accounts that use others' photos as their own profile pictures; NYT; 7/28/2019
- How to Fight Back Against Data Broker Advertising on Facebook LH; 7/12/2019
- No, You Still Shouldn't Let Facebook Pay You to Track Your Phone Habits 'Study from Facebook' Android app; LH; 6/12/2019
- Facebook's Notifications Are Out of Control. Here's How to Tame Them. NYT; 5/30/2019
- How to Disable Facebook's Automatic Face Recognition Setting (If You Can) LH; 5/21/2019
- Thanks to Facebook, Your Cellphone Company Is Watching You More Closely Than Ever Int; 5/20/2019
- 5 Takeaways From (co-founder) Chris Hughes's Call to Break Up Facebook NYT; 5/9/2019
- Facebook passwords for hundreds of millions of users were exposed to Facebook employees PC; 4/18/2019
- Facebook Is Stealing Your Family's Joy more fun to share in person; NYT; 4/12/2019
- App Developers Left 540 Million Facebook Users' Records on the Public Internet third-party Facebook app by Cultura Colectiva left 540M+ records of users' FB info exposed on Amazon WS; MB; 4/3/2019
- Facebook will no longer ask for people's email passwords used to verify some new accounts; CNet; 4/3/2019
- Facebook Did Not Securely Store Passwords. Here's What You Need to Know. NYT; 3/21/2019
- I Deleted Facebook Last Year. Here's What Changed (and What Didn't) NYT; 3/21/2019
- Hackers Used Facebook Quizzes to Steal Data from 60,000 Users users were prompted to install browser extensions; MF; 3/12/2019
- Facebook Promises Encrypted Messaging (and Privacy-Abusing Business as Usual) TB; 2/7/2019
- Some popular Android apps are still sending your data to Facebook Privacy International is demanding an investigation after discovering apps are still connected to Facebook; CNet; 3/6/2019
- Facebook is introducing a new 'Tributes' section for memorialized accounts TC; 3/4/2019
- How to Protect Your Facebook Without Giving It Your Phone Number if you need to use SMS for 2FA, some privacy settings may help; (or just remove phone#s and use authenticator app); Giz; 3/4/2019
- Facebook has urged users to enable phone number-based 2FA, but the numbers are used in a user lookup feature with no opt out and to target ads Settings > Mobile: remove all numbers; setup 2FA with an authenticator app/PM; TC; 3/3/2019
- Popular Apps Cease Sharing Data With Facebook WSJ; 2/24/2019
- You Give Apps Sensitive Personal Information. Then They Tell Facebook. WSJ; 2/23/2019
- How to report a problem on Facebook Verge; 2/25/2019
- Facebook VPN that snoops on users is pulled from Android store Onavo Protect VPN (removed for iOS 8/2018); Facebook also stops recruiting new users for controversial "Research" program; Ars; 2/22/2019
- You Give Apps Sensitive Personal Information. Then They Tell Facebook. like user's heart rate, intent to get pregnant, home listings viewed to Facebook via analytics SDK provided by the company; e.g., Instant Heart Rate: HR Monitor; Flo Period and Ovulation Tracker; Move Inc; WSJ; 2/22/2019
- How to stop Facebook from tracking your location And, iOS; TNW; 2/21/2019
- Behold, the Facebook phishing scam that could dupe even vigilant users HTML block almost perfectly reproduces Facebook single sign-on (SSO) Window; Ars; 2/16/2019
- What is a Facebook 'legacy contact' and why do you need one? allowed to have limited access to your account after your death; TNW; 2/15/2019
- Fed Up with Facebook? Move Your Family to Slack TB; 2/12/2019
- Germany orders Facebook to stop combining data from WhatsApp, Instagram, and third-party sites with data in a user's main Facebook account without their consent BBC; 2/7/2019
- What Was Your Facebook Breaking Point? LH; 2/6/2019
- Maybe Only Tim Cook Can Fix Facebook's Privacy Problem NYT; 1/30/2019
- Apple Shuts Down Facebook's Internal Apps Due to Flagrant Policy Violations TB; 1/30/2019
- Does Facebook Really Know How Many Fake Accounts It Has? maximum number of active fake accounts Facebook reported each quarter was significantly smaller than the number of fake accounts it said it took down; plus many duplicate accounts; NYT; 1/30/2019
- This Is Your Brain Off Facebook a major new study offers a glimpse of what unplugging might do for your life. (Spoiler: It's not so bad.); more in-person time with friends and family. Less political knowledge, but also less partisan fever. A small bump in one's daily moods and life satisfaction. And, for the average Facebook user, an extra hour a day of downtim; NYT; 1/30/2019
- Could The 10-Year Challenge Be Putting Your Data At Risk? data from the challenge could be used by companies like Facebook or Amazon to train facial recognition algorithms; NPR; 1/20/2019
- Most Facebook users don't know that it records a list of their interests, new study finds 74% of people weren't aware of Facebook's methods; Verge; 1/16/2019
- Facebook is the new crapware pre-installed Android app can't be deleted; TC; 1/9/2019
Genealogy, DNA Testing
- 'The GoFundMe Generation' Wants to Pay to Solve Murders NYT; 3/27/2022
- Your DNA Test Could Send a Relative to Jail
'genetic genealogy'; NYT; 12/27/2021 - Why a Data Breach at a Genealogy Site Has Privacy Experts Worried GEDmatch; NYT; 8/1/2020
- 23andMe vs. AncestryDNA: Which ancestry DNA kit is better? PC; 12/11/2019
- Genealogy Site GEDMatch Is Now Owned by a Forensics Company (Verogen) LH; 12/10/2019
- Privacy And DNA Tests NPT; 11/9/2019
- Which DNA Databases Are the Best and Worst for Privacy? 23andme and Ancestry are among the least risky; Genealogy databases that allow uploads are the ones with the major privacy concerns; LH; 4/10/2019
- Study: by the start of 2019, over 26M consumers have added their DNA to four leading commercial ancestry and health databases, primarily AncestryDNA MIT; 2/11/2019
- FamilyTreeDNA Admits to Sharing Genetic Data With F.B.I. NYT; 2/4/2019
- How to Keep the FBI From Accessing Your FamilyTreeDNA Results check privacy/match settings; LH; 2/1/2019
- DNA testing firm FamilyTreeDNA is working with the FBI and allowing agents to search its 1M+ DNA profiles user concerns about data privacy; BF; 1/31/2019
- Wikipedia: Instagram
- HowStuffWorks: How Instagram Works
- How to Avoid the Worst Instagram Scams Wired; 7/6/2022
- How to delete your Instagram account Verge; 7/2/2022
- Instagram Doesn't Own Your Photos, But They Can Still Use Them Forever LH; 8/21/2019
- How to Make Your Instagram Account as Private as Possible LH; 7/2/2019
- HowStuffWorks: How LinkedIn Works
- Delete LinkedIn -- you'll have zero *** regrets TNW; 2/18/2021
- Tap LinkedIn for Career Opportunities NYT; 10/31/2020
- People Are Looking At Your LinkedIn Profile. They Might Be Chinese Spies NPR; 9/19/2019
- Why Aren't We Talking About LinkedIn? Twitter helps the powerful discover their worst selves and leaves everyone else vulnerable. Facebook brings people together only to subject them to marketing and manipulation; LinkedIn is more like a workplace where people behave with employers in mind; NYT; 8/8/2019
Mastodon
- Mastodon: A New Hope for Social Networking TB; 1/27/2023
- Mastodon -- and the pros and cons of moving beyond Big Tech gatekeepers interoperability; Ars; 1/1/2023
- How secure a Twitter replacement is Mastodon? Let us count the ways Ars; 11/29/2022
- Looking to leave Twitter? Here are the social networks seeing new users now NPR; 11/24/2022
- What Is Mastodon and Why Are People Leaving Twitter for It? NYT; 11/7/2022
Metaverse
- The Timeline We're on Is Even Darker Than 'The Matrix' Envisioned NYT; 12/22/2021
- The Metaverse Is Coming, and the World Is Not Ready for It NYT; 12/2/2021
- How will Facebook keep its metaverse safe for users? FT; 11/12/2021
- So what is "the metaverse,"" exactly? Ars; 11/7/2021
- Zuckerberg's Meta promises a 'future' these video games delivered years ago
Roblox, Steam; WaPo; 10/29/2021 - The Metaverse Is Mark Zuckerberg's Escape Hatch NYT; 10/29/2021
NextDoor
- How to Stop Getting Nextdoor Emails OSXD; 4/29/2023
- How the social network Nextdoor is replacing local newspapers as a news and opinion hub letting governments bypass the media and present a one-sided picture; 1/26/2021
- Content Moderation Case Study: Nextdoor Faces Criticism From Volunteer Moderators Over Its Support Of Black Lives Matter (June 2020) TD; 8/21/2020
- Nextdoor eliminates its Forward to Police program allowed posts on the app to be sent directly to police departments; Verge; 6/20/2020
- Inside Nextdoor's 'Karen Problem' can Nextdoor really be a social network for communities if black people don’t feel safe on it? Verge; 6/8/2020
- Nextdoor Is Courting Cops And Public Officials Using All-Expenses-Paid Trips To Its Headquarters TD; 6/5/2020
Parler
- Parler's New Owner Shuts Down Site 'No Reasonable Person Believes Twitter For Conservatives Is A Viable Business Model' TD; 4/17/2023
- Apple will allow Parler to return to the App Store Verge; 4/19/2021
- Parler Says It's Back Wired; 2/17/2021
- Parler Tries to Survive With Help From Russian Company DDoS-Guard; NYT; 1/19/2021
- Amazon, Apple and Google Cut Off Parler, an App That Drew Trump Supporters NYT; 1/9/2021
- Right-Wing Social Media Finalizes Its Divorce From Reality true believers can get their misinformation elsewhere; Atl; 11/23/2020
- What is Parler, and why is everyone suddenly talking about it? no fact checking or censorship; 11/12/2020
- Fact-Checked on Facebook and Twitter, Conservatives Switch Their Apps Parler, Rumble, Newsmax; NYT; 11/11/2020
- Parler, the Trumpy Alternative to Twitter, Is Already Falling Apart DB; 7/13/2020
- As Predicted: Parler Is Banning Users It Doesn't Like TD; 6/29/2020
- Parler's Founder Explains Why He Built Trump's New Favorite Social Media App Forb; 6/27/2020
- Just Like Every Other Platform, Parler Will Take Down Content And Face Impossible Content Moderation Choices TD; 6/26/2020
Tiktok
- Don’t Ban TikTok. Fix Internet Privacy. NYT; 3/31/2023
- Why Countries Are Trying to Ban TikTok
sensitive user data in the hands of the Chinese government? NYT; 3/3/2023 - The Latecomer's Guide to TikTok NYT; 10/26/2022
- TikTok shares your data more than any other social media app — and it’s unclear where it goes, study says 2/8/2022
- The Lesson We’re Learning From TikTok? It’s All About Our Data we should minimize how much we share with all of our favorite and not-so-favorite apps; NYT; 9/14/2020
- Is Microsoft Sure It Wants to Buy TikTok? NYT; 8/4/2020
- What to Do About TikTok instead of banning the app, U.S. officials could force it to be more transparent; NYT; 7/27/2020
- Don’t Ban TikTok. Make an Example of It. NYT; 7/27/2020
- TikTok Is Wonderful. I Still Don’t Want It on My Phone. even though one of best social media platforms; NYT; 7/17/2020
- TikTok Enlists Army of Lobbyists as Suspicions Over China Ties Grow NYT; 7/16/2020
- TikTok says it will stop clipboard snooping after iOS 14 reveals when apps attempt to read the clipboard; TikTok claims it was used to identify spammy behavior Tel; 6/25/2020
Twitter / X
- Wikipedia: Twitter
- HowStuffWorks: How Twitter Works; Myths; Quiz; Tweetups
- Permanently Delete Your X Account in 5 Steps: Elon Musk Boosting Antisemitic Tweet Causes Growing Boycott CNet; 11/18/2023
- How to delete your Twitter history Verge; 8/29/2023
- How to Download Your Twitter Archive NYT; 11/18/2022
- How to Prepare for Life After Twitter
Plan an Exit Strategy; Spread Your Bets; Learn to Let Go; NYT; 11/16/2022 - Twitter rolls out security features for high-profile political accounts, including enabling password reset protection and security prompts, ahead of US election Verge; 9/17/2020
- Florida teen charged as 'mastermind' in Twitter hack Ars; 7/31/2020
- Twitter hackers used 'phone spear phishing' in mass account takeover targeted multiple employees; Ars; 7/31/2020
- A Brazen Online Attack Targets V.I.P. Twitter Users in a Bitcoin Scam employees who had access to internal systems had their accounts compromised in a 'coordinated social engineering attack'; NYT; 7/15/2020
- Watch six decade-long disinformation operations unfold in six minutes 1/26/2020
- Twitter halts plan to remove inactive accounts until it can memorialize dead users Verge; 11/27/2019
- Twitter will finally let you turn on two-factor authentication without giving it a phone number You could switch to another option later (like Google Authenticator, or a physical Yubikey) -- but to turn it on in the first place, you were locked into giving Twitter a phone number and using SMS; TC; 11/21/2019
- Twitter Took Phone Numbers for Security and Used Them for Advertising MB; 10/8/2019
- How Twitter CEO Jack Dorsey's Account Was Hacked it was a SIM swap; Wired; 8/30/2019
- Here's how to delete or deactivate your Twitter account TNW; 7/8/2019
- Why Won't Twitter Help Us Delete Our Tweets? NYT; 4/11/2019
- Even years later, Twitter doesn't delete your direct messages TC; 2/15/2019
Safer Internet: Share Files Privately
Safer Internet: Share Files Privately
Summary |
References: General | BitTorrent | Copyright, Piracy |
iOS | macOS, iTunes | Windows
Summary
- How to share / distribute files, photos, media, ...
- [1] Email attachment -- generally not recommended for many / large files; security?
- macOS: attach a large file (up to 5Gb) in Mail app
- MailDrop feature will store in iCloud; recipient can download file (for up to 30 days)
- [1] AirDrop (via Bluetooth and Wi-Fi): transfer files, videos, photos wirelessly between Apple devices; multiple files should be same type, e.g., .pdf, .jpg
- [1] AppStore: share apps within a household -- if AppleIDs use same credit card to purchase apps
- Even better, setup Family Sharing for separate AppleIDs, which share same credit card.
- macOS:
System Preferences > iCloud > Manage Family - iOS:
Settings > iCloud > Family - [1] Photos: share/stream via iCloud (free / $)
- settings...
- [1] Music
- macOS:
iTunes > Preferences > Sharing - [1] Cloud service: store files on iCloud, Box, Dropbox, Google Drive, Microsoft OneDrive, etc.
-- see section Backup - Email file link to recipient
- [2] If information is extra sensitive, don't depend on the encryption built into Dropbox or other cloud services (protected only by account password); encrypt sensitive files yourself first, e.g., 7-zip; note: 1Password already encrypted
- [1] "SneakerNet": on USB thumb drive or DVD
- [2] Local network: remote drive
- For specific purposes only, use temporarily -- don't forget to disable when no longer needed
- macOS:
System Preferences > Sharing : Files - Windows: (File Sharing) {Figure 7. TCYOP-4: 72}
- [3] Friend-to-friend networks, e.g., Retroshare
- [3] Peer-to-peer networks, e.g., BitTorrent; note: sharing of other's content can be illegal (piracy) or dangerous (malware)
- [3] Create your own private cloud, e.g., Transporter
References
- {TCYOP-4: 147-155; TCYOP-3: 121-129; Understand the Privacy Risks of File Sharing; Encrypt Transfers, Files, or Both; Keep File Syncing and Backups Private; Use Peer-to-Peer File Sharing: Hide your IP address, Avoid suspicious public indexes, Avoid seeding, Try a friend-to-friend network; Create a Personal Cloud: Lima, NAS devices, Resilio Sync, ownCloud and Nextcloud}
- see also: Backups
- sections: Refs: BitTorrent; Copyright, Piracy; iOS; macOS, iTunes; Windows; Backup:Cloud
- Ethical.net: File sharing
- Wikipedia: BitTorrent: peer-to-peer file sharing
- Wikipedia: The Pirate Bay 2003: founded in Sweden; facilitates peer-to-peer file sharing using the BitTorrent protocol
- Wikipedia: Darknet private network where connections are made only between trusted peers -- sometimes called "friends" -- using non-standard protocols and ports
- Wikipedia: SecureDrop Freedom of the Press Foundation; "open-source whistleblower submission system that media organizations use to securely accept documents from anonymous sources. It was originally coded by the late Aaron Swartz."
- GPG Suite; encrypt, decrypt, sign and verify files or messages
- Wikipedia: friend-to-friend type of peer-to-peer network in which users only make direct connections with people they know. Passwords or digital signatures can be used for authentication
- How to share large files over the web
iCloud Drive, Google Drive, Microsoft OneDrive, WeTransfer, Smash; Verge; 11/14/2023 - The Best Ways To Share Files Between Multiple Devices in 2022 Giz; 6/23/2022
- How to share folders and files from Mac to Windows and vice versa ApIn; 6/21/2022
- Steps to Simple Online Security: Send messages and files safely NYT; 4/22/2022
- How to Set Up a NAS to Securely Share Files Wired; 9/19/2021
- [2] Upgrade Your File Transfer Security with Encryption Keys SFTP; TB; 7/18/2021
- How to Keep Nearby Strangers from Sending You Files Wired; 3/28/2021
- How to turn on AirDrop iOS, Mac; ApIn; 1/19/2021
- Mozilla says it is permanently shutting down Firefox Send after some users sent malware and conducted spear phishing attacks using the file-sharing service CNet; 9/17/2020
- How Do I Share a Hard Drive on My Home Network? Windows, NAS (network attached storage); LH; 8/21/2020
- Three ways to pass web pages across your Mac, iPhone, and iPad Handoff, AirPlay, iCloud bookmarks, QR; MW; 8/14/2020
- How to Sync and Access Your Data Across Devices switch between your phone and laptop seamlessly; Wired; 6/2/2020
- How to Share Files Securely Online Firefox Send, Dropbox, WeTransfer, Google Drive, OneDrive, SendAnywhere, iCloud; Wired; 2/9/2020
- Hacker Lexicon: What Is a Dead Drop? Wired; 11/29/2019
- How to send large attachments with Mail Drop and other services upload or sync a file to cloud storage, and then create a shareable link from it, sometimes with an attached time limitMW; 11/29/2019
- Apple's AWDL protocol plagued by flaws that enable tracking and MitM attacks e.g., AirDrop; ZD; 7/30/2019
- How to share files using iCloud Drive AI; 4/29/2019
- Smash's file transfer service just let us transfer a 33GB file for free another option: WeTransfer; TNW; 2/18/2019
BitTorrent
- HowStuffWorks: File Sharing; How BitTorrent Works
- [2] A Beginner's Guide to BitTorrent LH; 7/11/2019
Copyright, Piracy
- "Your fair use of this book is restricted...
- "Only one thing is impossible for God:...
- Wikipedia: Copyright; Digital Millennium Copyright Act (DMCA)
- Wikipedia: Digital Rights Management; SOPA Stop Online Piracy Act; proposed legislation
- Wikipedia: PIPA PROTECT IP Act: Preventing Real Online Threats to Economic Creativity and Theft of Intellectual Property Act; proposed legislation;
successor to COICA: Combating Online Infringement and Counterfeits Act - HowStuffWorks: How Digital Rights Management Works; How SOPA Works
- Wikipedia: ACTA Anti-Counterfeiting Trade Agreement: multinational treaty
iOS
- Apple: Family Sharing up to six people in a family can share each other's iTunes, iBooks, and App Store purchases without sharing accounts
- The Easiest Way to Zip and Unzip Files on Your iPhone LH; 11/21/2022
- How to SSH to Mac from iPad OSXD; 5/24/2022
- AirDrop could be hacked to reveal personal information, researchers say CNet; 4/23/2021
- How to maintain video resolution when sharing videos via AirDrop MW; 4/7/2021
- How to Access Windows Shared Folders from iPhone & iPad OSXD; 2/24/2021
- AirDrop Proved Handy on NASA’s Demo-2 Mission TB; 8/6/2020
- [2] How to Connect to SMB Shares from iPhone & iPad with Files App OSXD; 11/4/2019
- How to see your Mac's documents across your network on your iPad with the Files app ApIn; 2/25/2019
- How to use and troubleshoot AirDrop for simple file transfers and handoffs MW; 2/25/2019
macOS, iTunes
- Apple: Family Sharing up to six people in a family can share each other's iTunes, iBooks, and App Store purchases without sharing accounts
- Today I learned about an easy way to share files between Mac apps
it's all in the title bar; Verge; 7/31/2022 - How to connect two Macs without a network
SMB file sharing; Bonjour; direct app support;
1. Thunderbolt; 2. 1Gbps-10Gbps ethernet; 3. Wi-Fi hotspot with your Mac;
4. computer-to-computer wireless network; MW; 5/16/2022 - How to use AirDrop on a Mac Verge; 4/6/2022
- If you’re using AFP to share a Mac drive, It's time to change AFP = Apple File Protocol from late 80s; MW; 12/18/2020
- AirDrop is great for the iPhone, iPad and Mac, but it can be even better. Here’s how UI improvements and wider range; MW; 8/12/2020
- How to use and troubleshoot AirDrop for simple file transfers and handoffs MW; 2/25/2019
Windows
Safer Internet: Manage Mobile Privacy
Safer Internet: Manage Mobile Privacy
Summary | Accounts | Backup | Encryption | Network | Location | Public Device |
References: General | Android | Border Crossings |
Cell Networks | iOS | macOS | Travel
Summary
- Mobile Devices are more vulnerable to loss, theft, hacking and inspection -- whether travelling internationally or just away from home for a few minutes.
- Many recommendations echo previous sections, but with an emphasis on mobility / travel:
- [1] Strong Passwords on all Devices; 2FA avail at destination?
- [1] Backups, especially Photos; portable drives?
- [1]
 Encryption, especially Passwords; border concerns?
Encryption, especially Passwords; border concerns? - [1] Networks: secure Wi-Fi? use VPN?
- [1] Location: enable Find My xxx; disable other services?
- [1] Using Non-Personal Devices to access online accounts -- don't, or exercise extreme caution
- References
Accounts
- Consider not only laptops, tablets, phones, but also other smart mobile devices, e.g., camera, watch, wearables.
- Strong passwords are especially recommended for your mobile device -- in case it gets lost or stolen -- and for any important remote accounts that you need to access while traveling.
- [2] If using 2-factor authentication (or 2-step verification), check that phone/token can be used at destination, or bring backup codes -- or disable 2FA until back home.
 Backup
Backup
- Backup data before leaving home
- During trip, backup new photos / info
- from camera / phone / tablet
- to cloud / other device
- Depending on network speed / cost / security, you may want to disable automatic cloud backup / sync.
- macOS:
System Preferences > iCloud - iOS:
Settings > iCloud > Photos etc. - Bring copies of travel info as .pdfs, e.g., scanned passports / driver's license, air/hotel confirmations, itinerary
- Tag portable items with address labels, add phone no. and/or email contact
- Bring any needed cables, chargers, adapters, plugs, spare batteries, battery pack
- Avoid "juice jacking" at public USB charging ports, which can also access data ! -- bring your own wall charger
Encryption
- Remove or encrypt sensitive info, esp. passwords; use a password manager
- Devices are increasingly subject to searches in luggage and at international borders
Network
- Access WiFi: securely -- WPA2 recommended
- Use a Virtual Private Network (VPN) if appropriate
- Check with carrier about voice / data plans if leaving US
- Avoid excessive charges by using "airplane mode" or disabling cell data on an app-by-app basis
- iOS:
Settings > Cellular Data > Use Cellular Data For: - [2] Opt out of your cell carrier's "supercookies"
- "Unlike regular cookies, supercookies can't be blocked or deleted, because the carrier inserts these unique identifiers between the time a request for a page leaves your device and the time it's sent to the server"
Location
- Enable/test tracking service, e.g., Find My Mac/iPad/iPhone, in case device lost/stolen
- Be aware that your approximation physical location can be determined from your cell network, from geotagging in photos, or by apps that ask to track you -- or even from device MAC address when using Wi-Fi (though iOS 8 randomizes MAC address regularly)
- iOS:
Settings > Privacy > Location Services - [2] iOS:
Settings > Bluetooth: off-- if you want to disable iBeacon
When Traveling Without Your Device
- Best not to use public computers, e.g., cybercafe, hotel -- even if 'well-maintained' and privately location -- malware, keyloggers, etc.?
- If you need to login, uncheck 'remember me' or 'stay signed in'
- 2FA (2-factor authentication) can provide some protection your account, but changing your password later (from a secure system) is recommended
- Use private browsing; cleanup cookies, history, downloads that you've created and left behind
- Logout / Turn off
References
- {TCYOP-4: 156-165; TCYOP-3: 130-139; Cellular Data Considerations: Your SIM Card; Supercookies; Proximity-based Logins; Granting Apps Access Permission; Location Awareness; Photos and Videos; Mobile Backups; Privacy and International Travel}
- sections: Refs: Android; Border Crossings; Cell Networks; iOS; macOS; Travel
- see also: Web Browsing: Manage Data; Services: Location; Backups
- topics:
- Ethical.net: Smartphones; Mobile Apps
- HowStuffWorks: Can the government take away my laptop?
- REI: Solar Chargers and Portable Power
- Ten Items That Belong in Every Carry-On Bag airline travel; LH; 5/24/2022
- How to secure your phone before attending a protest Verge; 5/5/2022
- Steps to Simple Online Security: Maintain privacy at international borders and protests NYT; 4/22/2022
- Privacy myths busted: Protecting your mobile privacy is even harder than you think
settings alone aren't enough to secure your privacy,
but they're a lot more powerful with the right apps;
Use a PIN code to lock your phone
-- not fingerprints or facial recognition;
Disable location tracking; Turn off your mobile ad ID;
Check your apps and accounts; Sign out of all other devices;
Lock down your social media; Enable 2FA;
Check for leaky apps; Fail-safe: Nuke your phone remotely;
The real key to privacy: Add these five apps
1. Signal Private Messenger App; 2. Surfshark VPN;
3&4. Brave Browser and DuckDuckGo;
5. BitWarden password manager; CNet; 1/9/2022 - How to Safely Stay Connected When You Travel
By Foot: power banks, interactive maps;
By Bicycle: geolocation, fitness tracking;
By Car: data plans, WiFi, VPNs, maps;
By RV: mobile hot spots, camping;
By Plane: airline apps, TSA;
By Public Transportation: WiFi on train, buses;
Wired; 6/22/2021
Android
Border Crossings
- EFF (Electronic Frontier Foundation): Border Search Pocket Guide;
Digital Privacy at the U.S. Border: Protecting the Data On Your Devices and In the Cloud;
Surveillance Self-Defense - ACLU: Know Your Rights: What To Do When Encountering Law Enforcement At Airports And Other Ports Of Entry Into The U.S.
- Irish police to be given powers over passwords
with search warrant; BBC; 6/14/2021 - CBP Now Has a Massive Searchable Database for Devices Seized at the Border the US border agency will be able to sift through data extracted from travelers' laptops and cellphones for up to 75 years; MB; 8/24/2020
- Court Rules Government Can’t Search Your Phone at the Airport for No Reason The ruling is a significant win for privacy rights of Americans and tourists traveling to the US; MB; 11/12/2019
- US border officials are increasingly denying entry to travelers over others’ social media CBP searched 30,000 devices last year without a warrant, up ~4x from three years prior; TC; 8/27/2019
- China Is Forcing Tourists to Install Text-Stealing Malware at its Border Xinjiang region; Android; downloads a tourist's text messages, calendar entries, and phone logs, as well as scans the device for over 70,000 different files; MB; 7/2/2019
- Senators (Wyden & Paul) propose bill requiring warrants to search devices at the border CNet; 5/22/2019
- Canada Border Services seizes lawyer's phone, laptop for not sharing passwords CBC; 5/5/2019
- ACLU says info uncovered through its lawsuit show CBP and ICE have "near-unfettered" authority to search and seize travelers' electronic devices at the border violations of 1st and 4th Amendments; ACLU; 4/30/2019
- Former Mozilla CTO was detained at US border and told he had no right to a lawyer US citizen; 4/4/2019
Cell Networks
- What is eSIM exactly? The feature, which is included on newer phones like the iPhone XR (and later) and some Android devices, eliminates the hassle of swapping out your physical SIM card for a foreign one. Instead, you keep your normal SIM card inside your phone and essentially activate a digital SIM card to access a foreign carrier’s service. Carriers offer eSIM in various forms: Some require installing an app to buy a data plan, while others require scanning a barcode to activate service; instructions: Apple, Google; foreign carriers offering eSIM support
- Is 5G Available for You? Here's How to Find Out Wired; 12/31/2021
- 3 Tips For Using Your Cellphone Internationally AARP; 8/20/2019
- The Key to Cheap Internet Service: a Local SIM Card NYT; 4/9/2019
iOS
macOS
Travel
- Traveling? Beware of Unsecured Hotel Wi-Fi Networks OSXD; 7/28/2022
- GasBuddy Is a Privacy Nightmare. Here Are Other Ways to Find the Cheapest Gas.
Google Maps (or Waze); Geico’s gas search;
GasBuddy’s browser-based search; NYT; 3/9/2022 - Cybersecurity Safety Tips for Travelers AARP; 8/2/2021
- Airbnb's new speed test feature lets you check the Wi-Fi before you book
if owner tests and posts results; CNet; 7/29/2021 - Why Posting Boarding Pass Photos Is a Bad Idea e,g, hints to traveler's passport and phone number; TB; 9/21/2020
- What to Do If You Lose Your Wallet
Know what's in your wallet;
Cancel your credit and debit cards;
Call a Non-Emergency Helpline;
Update your subscriptions and online accounts;
Get a new drivers license or ID;
Replace your miscellaneous cards;
Request a credit report and initiate a fraud alert; LH; 9/17/2020 - How to Become a U.S.-Based Digital Nomad LH; 9/16/2020
- How to Keep Your Wallet Safe When You Travel LH; 5/5/2020
- A Case for Paying With Your Phone NYT; 2/5/2020
- Only three of the Top 100 international airports pass basic security checks Tests involved scanning public websites, mobile apps, and exposures of sensitive airport data on public code repositories and the dark web; ZD; 2/3/2020
- How to Share Internet Between Your Devices When You're Away From Home LH; 12/26/2019
- Use a 'USB Condom' to Protect Your Devices at Public Chargers LH; 12/3/2019
- Stop! Don’t Charge Your Phone This Way think twice before plugging into USB at an airport or on the train; 'juice jacking'; NYT; 11/18/2019
- Wake Up! Your House Is Calling Smart technology can make it easier to keep tabs on your home when you’re on vacation, but it also makes it harder to really get away; NYT; 8/23/2019
- Americans would rather get food poisoning on vacation than not have internet access lost luggage: 54%; no internet access: 49%; food poisoning: 47%; consistent bad weather: 47%; lost credit card: 44%; 8/13/2019
- I Opted Out of Facial Recognition at the Airport -- It Wasn't Easy Wired; 7/2/2019
- How to Avoid Getting Scammed When Traveling LH; 6/28/2019
- A Comprehensive Guide to Taking Your Smartphone Abroad for Cheap For $15 to $40, you can easily take your phone to a foreign country and enjoy access to apps, maps and the web; easy/expensive: your US carrier; harder/cheaper: unlock phone, obtain foreign SIM card, prepare phone; NYT; 6/26/2019
- Everybody Hates the Key Card. Will Your Phone Replace It? NYT; 6/6/2019
- 5 Financial Security Measures to Take Before Traveling
1. Research the Scams That Are Common In the City You're Traveling To;
2. Be Wary of Property Rental Owners Asking For an Immediate Down Payment;
3. Make Sure Your Phone Is Password Or Fingerprint-Protected;
4. Take Care Of Your Online Finances Before Heading To the Airport;
5. Consider Buying a Wallet Or Money Belt with RFID-Blocking Technology; MF; 5/30/2019 - How Hackers Can Steal Your Data at Airports plugging into a public USB port; LH; 5/23/2019
- These Smart Devices Protect Your Home While You're on Vacation
the basics: Lighting timers and smart plugs;
budget-friendly upgrades: Security cameras and smart lights;
the works: Smart locks, thermostats, and security systems; NYT; 5/2/2019 - Review of 1,500 hotels across 54 countries: ~67% of hotel websites inadvertently leak guests' booking info to third-party sites like ad and analytics services allowing others to view your personal data or even cancel your reservation; 4/9/2019
- How to Leave No Trace on a Borrowed Computer private browsing; history, downloads, searches; apps: Recent Files; Giz; 3/29/2019
- How to conserve mobile data by turning off iTunes and other downloads in iOS
Settings > Music > Cellular Data; Settings > Cellular > Cellular Data; Settings > iTunes & App Store > Use Cellular Data; MW; 3/25/2019 - How to Switch Out (and Store) Your SIM Card When You Travel LH; 3/22/2019
- The Best Ways to Use Google Translate in a Foreign Country LH; 3/20/2019
- Do All These Things Before Traveling Internationally LH; 3/8/2019
- Airline e-ticketing systems put passenger data at risk emails with unencrypted check-in links; beta; 2/6/2019
- How to Safeguard Your Tech, and Your Money, While Traveling avoid unsecured Wi-Fi; forwarding phone no.; throwaway email address; encrypted device; own charger; virtual credit cards; credit monitoring; NYT; 2/4/2019
Safer Internet: Internet of Things
Safer Internet: Internet of Things
Summary |
References: General | Alexa (Amazon Echo), Ring | Apple |
Camera | Cars | Google Home | Health | Home; |Smart TVs | Wearables
Summary
- Q. How many engineers does it take to change a lightbulb?...
- "Amazon Alexa is for...
- There ever more types of internet-connected devices -- at home and on our person:
- Home: Amazon Alexa, Google Home, security cameras, home automation, lightbulbs, thermostats, smoke alarms, appliances, water valves
- Set-top Devices: camera, microphone, people identification (Kinect), playlist, game consoles
- Wearable technology: watches, fitness trackers, glasses
- [1] Be vigilant about cool new features: Helpful Assistant vs. 'Big Brother'
- [1] Check list: privacy & security settings, changeable password, ongoing support, security updates, encryption, ...
-- or, don't purchase gadget, or disable 'smart' functionality altogether?
References
- {TCYOP-4: 166-170; TCYOP-3: 140-144; Set-top Devices; Web-connected Cameras; appliances, light bulbs, home-automation equipment, home security systems, Google Home, Amazon's Alexa}
- sections: Alexa (Amazon Echo), Ring; Apple; Camera; Cars; Google Home; Health; Home; Smart TVs; Wearables
- Wikipedia: Internet of Things (IoT); ubiquitous computing
- Wikipedia: 6LoWPAN acronym of IPv6 over Low power Wireless Personal Area Networks
- Mozilla: Entertainment, Health & Exercise, Pets,
Smart Home, Wearables
product ratings -- minimum security standards:
Encryption: Does the app/service offer it?
Security updates: How regularly is the app/service updated?
Strong passwords: How strong are the app’s password guidelines?
Manages vulnerabilities: Is there a way for people to report bugs and other security issues with the app?
Privacy policy: Does it exist? - All of Your Smart Devices Are Spying on You LH; 8/16/2022
- Steps to Simple Online Security: Secure small gadgets and smart-home devices NYT; 4/22/2022
- The UK Just Banned Default Passwords and We Should Too
the new bill would require unique passwords for IoT devices and would
prevent those passwords from being reset to universal factory default; Giz; 11/24/2021 - Thinking about selling your Echo Dot—or any IoT device? Read this first
deleting data is hard; factory reset; encryption? Ars; 7/2/2021 - How Secure Is Your Digital Assistant? Google Assistant, Alexa, Siri; Giz; 12/11/2020
- Critical Flaws in Millions of IoT Devices May Never Get Fixed Wired; 12/8/2020
- Secure Your Smart Home Devices AAA Via, pp 26-27 Nov/Dec 2020
- Ink-Stained Wretches: The Battle for the Soul of Digital Freedom Taking Place Inside Your Printer HP; EFF; 11/5/2020
- Over 100 irrigation systems left exposed online without a password ZD; 10/26/2020
- The WIRED Guide to the Internet of Things What you need to know about the promise (and peril) of networked lightbulbs, ovens, cameras, speakers, ...; Wired; 9/11/2020
- Ripple20 vulnerabilities will haunt the IoT landscape for years to come TCP/IP library found at the base of many IoT products; ZD; 6/16/2020
- Carnegie Mellon Researchers Design 'Nutrition Label' For The Internet Of Broken Things TD; 6/9/2020
- 6 devices to keep tabs on your aging family members without invading their privacy CNet; 5/1/2020
- Critical bugs in dozens of Zyxel and Lilin IoT models under active exploit DDoS botnets abuse IoT flaws to conscript vulnerable devices; Ars; 3/21/2020
- How to protect your personal data in the age of IoT TNW; 3/10/2020
- IoT Trouble: The Sonos Example -- And More 1/26/2020
- How hackable is your smart device? The UL IoT Security Rating and UL Verified Mark will tell you TH; 1/8/2020
- FBI recommends that you keep your IoT devices on a separate network separate router? The FBI also recommends changing factory-set (default) passwords and not allowing an IoT device's accompanying mobile app to gain access to too many smartphone permissions; ZD; 12/6/2019
- Diagnose Your Devices' Privacy Problems With This List From Mozilla Mozilla: Privacy Not Included -- minimum security standards vs. creepy; LH; 11/25/2019
- The Debate Over How to Encrypt the Internet of Things lightweight encryption vs. AES? Wired; 11/23/2019
- Researchers hack Siri, Alexa, and Google Home by shining lasers at them MEMS mics respond to light as if it were sound; Ars; 11/4/2019
- The Internet of Things Is Still a Privacy Dumpster Fire biggest IoT study ever finds "smart" devices hoover up a universe of user behavior data and share it with a laundry list of global third parties, frequently with little transparency to the end user; MB; 9/19/2019
- How to keep Amazon, Apple, and Google from listening to your Alexa, Siri, and Assistant recordings TH; 8/3/2019
- 200 million devices—some mission-critical—vulnerable to remote takeover elevators, medical equipment, and other mission-critical systems running VxWorks OS; Ars; 7/29/2019
- [2] New Offensive USB Cable Allows Remote Attacks over WiFi BC; 2/11/2019
Alexa, Ring
- An Alexa bug could have exposed your voice history to hackers Amazon has patched the flaw, but remember to lock down your voice assistant interactions; Ars; 8/15/2020
- Ring cameras are more secure now, but your neighbors still snoop with them Ars; 2/18/2020
- How to Prevent Ring from Sharing Your Data with Marketing Companies LH; 2/18/2020
- 3 privacy issues to consider before bringing an Amazon Echo into your house Sharing with law enforcement; Tracking health issues; Transparency; TNW; 2/6/2020
- Hi, Alexa. How Do I Stop You From Listening In On Me? also, Apple Siri, Google Home; NYT; 8/21/2019
- Amazon confirms it keeps your Alexa recordings basically forever recordings and their transcripts never expire automatically; Ars; 7/3/2019
- Prevent Amazon From Eavesdropping On Your Alexa Conversations LH; 4/12/2019
- Amazon Workers Are Listening to What You Tell Alexa A global team reviews audio clips in an effort to help the voice-activated assistant respond to commands; 4/10/2019
- Think about privacy the next time you ask Alexa the weather TNW; 3/16/2019
Apple
- AirTag bug could let a hacker steal iCloud passwords MW; 9/29/2021
- When You’re Told an AirTag Is Moving with You TB; 6/4/2021
- The Two Faces of Find My
Find My device (Internet);
Find My network (crowdsourced);
TB; 5/23/2021 - 13 AirTag Tracking Scenarios
Something Lost:
Bill's Wayward Keys;
Manjula and the Missing Messenger Bag;
Nic's Missing Laptop Bag;
Martyn's Post-Bender Panic;
Ruth Bader Ginspurr Escaped the House;
Something Stolen:
Chai's Snagged Bag;
Sorry, Charlie;
Fenchurch's Double AirTag;
Bad News, Vicente;
Someone Stalked or Tracked:
Yuen's Ex-Boyfriend;
Annelise's Nosy Neighbor;
A Package for Betsy;
Florian's Mystery AirTag;
TB; 5/15/2021 - [2] How to Unlock That Hidden Debug Mode for AirTags in iOS 14.5 LH; 5/6/2021
- AirTag review: They work great—maybe a little too great Ars; 5/5/2021
- How to Delete Siri Audio History on iPhone & iPad OSXD; 11/11/2019
- Apple's promised Siri recording opt-in feature arrives in iOS 13.2 beta Verge; 10/10/2019
- Apple was a little behind on Siri privacy, now it’s way ahead Verge; 8/29/2019
- Siri records fights, doctor's appointments, and sex (and contractors hear it) drug deals, etc.; Ars; 7/26/2019
Camera, Drones
- Popular Chinese-Made Drone Is Found to Have Security Weakness NYT; 7/23/2020
- Security cameras can tell burglars when you're not home, study shows amount of data uploaded; CNN; 7/6/2020
- Who's Watching Your Porch? NYT; 1/20/2020
- IoT device vendor Wyze says a server leak exposed data, including email addresses, camera user IDs, and WiFi SSIDs, of ~2.4M customers from Dec. 4 to Dec. 26 ZD; 12/29/2019
- How Hackers Are Breaking Into Ring Cameras MB; 12/11/2019
- Human Employees Are Viewing Clips from Amazon's Home Surveillance Service Cloud Cam; Giz; 10/10/2019
- Hacker spoke to baby, hurled obscenities at couple using Nest camera, dad says CBS; 1/31/2019
- Protect Your Privacy From Your Own Cloud Security Cameras LH; 1/11/2019
Cars
Google Home
- A Google Nest Hub might join you for your next hotel stay Nest Hub (as opposed to the larger Nest Hub Max) doesn’t have an integrated camera, and guests will always be able to flip a switch to disable the display’s microphone. Also, you won't have to sign in to the Nest Hub with your Google account to use the display, and 'any activities' will be wiped from the device before the next guest checks in; TH; 8/25/2020
- Google contractors are secretly listening to your Assistant recordings TNW; 7/10/2019
- Bought a used Nest security cam? The previous owner can spy on you Nest Cam Indoor paired with a Wink hub; NYT; 6/20/2019
- How to Prevent Google from Saving Your Voice Recordings LH; 5/1/2019
Health
- Half of internet-connected devices in hospitals are vulnerable to hacks, report finds
IV pumps were the biggest risk; Verge; 1/19/2022 - Your Pricey Peloton Has Another Problem For You To Sweat Over
malware apps; monitor users via bike's camera and microphone; NPR; 6/16/2021 - The Dick Jail Is 'Safe' Again, but Use at Your Own Risk Qiui Cellmate Chastity Cage; Giz; 2/10/2021
- Internet-Connected Chastity Cages Hit By Bitcoin Ransom Hack TD; 1/12/2021
- GE puts default password in radiology devices, leaving healthcare networks exposed Ars; 12/8/2020
- IoT Chastity Penis Lock Can Be Hacked TD; 10/9/2020
- Why fixing security vulnerabilities in medical devices, IoT is so hard Ars; 2/19/2020
- 600,000 GPS trackers left exposed online with a default password of '123456' ZD; 9/5/2019
- Comcast Working on Health Monitoring Device For the Elderly But Don't Call it an Alexa Giz; 5/21/2019
Home
- Unwanted Connection: Who Has Control of Your Smart Home? NYT; 2/17/2023
- A New City, Built Upon Data, Takes Shape in South Korea
smart city, homes; NYT; 3/28/2022 - Nobi will watch over your grandparents, literally, from a ceiling mounted smart lamp this AI powered gadget is smart enough to know if you're sitting, standing or laying down and will reach out for help if you fall down; CNet; 1/12/2021
- When coffee makers are demanding a ransom, you know IoT is screwed watch along as hacked machine grinds, beeps, and spews water; Ars; 9/26/2020
- Amazon Unveils Drone That Films Inside Your Home. What Could Go Wrong? NYT; 9/25/2020
- How to Secure and Protect Your Smart Home
Secure your network;
Use unique passwords;
Stick with reputable brands;
Directly protect your devices (2FA);
Read the fine print;
Take responsibility; NYT; 9/18/2020 - Consumer Reports Study Shows Many 'Smart' Doorbells Are Dumb, Lack Basic Security TD; 8/24/2020
- Meet the Star Witness: Your Smart Speaker requests are rising from law enforcement for information on the devices, which can include internet queries, food orders, and overheard conversations; Wired; 8/23/2020
- Petnet 'Smart' Feeder Customers Are Stuck In IoT Purgatory TD; 7/16/2020
- Tips and best practices for optimizing your smart home TH; 5/6/2020
- Philips' Internet-Connected Lightbulbs Will No Longer Connect to the Internet Philips no longer feels like supporting 1st generation; MB; 3/6/2020
- Security experts warn of vulnerability in Philips Hue smart lights vulnerability could have let hackers infiltrate users' home or corporate networks; Fortune; 2/5/2020
- Smart homes will turn dumb overnight as Charter kills security service lack of interoperability in alarm systems; Ars; 1/17/2020
- Change Your Ring Account Password Right Now LH; 12/19/2019
- Alexa, Siri, and Google Assistant might soon all speak the same smart home language Project Connected Home over IP (CHoIP); also includes: IKEA, Samsung, Hue, NXP, Silicon Labs (Z-Wave chips); TH; 12/18/2019
- Amazon Ring doorbells exposed home Wi-Fi passwords to hackers TC; 11/7/2019
- Smart Lights Enhance Home Security and Shine a Light on Crime NYT; 9/19/2019
- HP printers try to send data back to HP about your devices and what you print 9/15/2019
- Smart ovens have been turning on overnight and preheating to 400 degrees Verge; 8/14/2019
- Security flaws in a popular smart home hub let hackers unlock front doors Zipato; TC; 7/2/2019
- America's Favorite Door-Locking App Has a Data Privacy Problem Great for landlords. Not so great for you; Med; 4/29/2019
- Spy on your smart home with this open source research tool IoT Inspector; TC; 4/13/2019
- The Easy Way to Create a Smart Home NYT; 4/2/2019
- What Sony's robot dog teaches us about biometric data privacy CNet; 4/1/2019
- How to Protect Your Smart Home from Hackers password protect network; isolate via guest network; unique passwords; reputable brands; secure devices (updates, 2FA); erasing; NYT; 3/27/2019
- Can Your Refrigerator Improve Your Dating Life? Samsung's Refrigerdating app lets users look at the inside of a potential mate's refrigerator; NYT; 3/12/2019
- Are You an Amazon or an Apple Family? home innovations like smart microwaves and toilets could lock us into a digital caste system; NYT; 3/9/2019
- Google says the built-in microphone it never told Nest users about was 'never supposed to be a secret' BI; 2/20/2019
- Flo by Moen smart water valve review: The high price of prevention system monitors and reports on your home's water usage. It can also shut off the water supply to prevent catastrophic damage; TH; 2/8/2019
- Best smart bulbs for your connected home TH; 2/8/2019
- Best smart smoke detector to keep your home safe Smart smoke and carbon monoxide detectors don't just sound the alarm, they also alert your smart phone and more; TH; 2/8/2019
- Samsung SmartThings still hasn't earned my trust in the smart home CNet; 2/3/2019
- This Hacker Showed How a Smart Lightbulb Could Leak Your Wi-Fi Password LIFX Mini white; MB; 1/31/2019
- For Owners of Amazon's Ring Security Cameras, Strangers May Have Been Watching Too teams in Ukraine and the US had unfiltered cloud access to unencrypted home security camera videos and live feeds; 1/10/2019
Smart TVs
- Vizio TV buyers are becoming the product Vizio sells, not just its customers
Vizio's ads, streaming, and data business grew 133 percent year-over-year; Ars; 5/12/2021 - Can I Save Money by Buying a 'Dumb' TV? not really, but you can disconnect it from internet; Wired; 11/26/2020
- Behind Roku's Ad-Supported Streaming Strategy WSJ; 3/29/2020
- How to Make Your New Smart TV as Secure as Possible Make sure your accounts are secure; Always install firmware and apps updates for your TV; Disable (or tape up) your TV’s camera and mic; Tune up your home network’s security; LH; 12/3/2019
- You watch TV. Your TV watches back. in our latest privacy experiment, we tracked how four of the most popular TV brands record everything we watch; WaPo; 9/18/2019
- No, your smart TV isn't catching viruses a misguided tweet from Samsung; TH; 6/20/2019
- As smart TVs become the only option, your privacy choices fizzle out Automatic Content Recognition shares data about everything you're watching on the TV with advertisers. Other TVs can collect audio through recordings, while apps can be used to track viewings by listening through the phone; CNet; 6/18/2019
- Android TV update puts home-screen ads on multi-thousand-dollar Sony Smart TVs users are reportedly not enjoying Google's 'pilot program'; Ars; 4/4/2019
- Smart TVs could get annoying ads just like your web browser does Vizio is developing an open standard with nine partners; Verge; 3/12/2019
- Vizio is telling you how to get paid for TV-spying lawsuit by taking over your TV VizioTVsettlement.com; Verge; 2/12/2019
Wearables
- Wikipedia: Wearable computer; Smart watch; Google Glass
- Could Someone Hack My Microchip Implant? Giz; 10/5/2020
- A Software Update Is Breaking Nike’s Expensive, Auto-Lacing Sneakers Giz; 2/20/2019
Safer Internet: Maintain Privacy for Your Kids
Safer Internet: Maintain Privacy for Your Kids
Summary |
References: General | iOS | IoT, Toys | macOS |
Phones | School | Shopping | Social Media, YouTube | Teens
Summary
- In addition to recommendations covered in earlier sections, certain users may be more vulnerable
- Infants, teenagers, grandkids, aging parent / partner may be unaware, less experienced, naive, impulsive, or be memory-/judgment-impaired
- [1] Provide safe environment, and teach/model awareness and safer online practices
- [1] Technology, e.g., parental controls, might help -- though more tech-savvy kids may be able to bypass?
- [1] Extra caution about social media: any text, photos, videos are posted -- by child or you -- will be online forever, with greater impacts on future careers, relationships, etc.
- [1] Location: Avoid posting anything that can give away your child's location or that might embarrass the child later in life
References
- {TCYOP-4: 171-173; TCYOP-3: 145-147}
- sections: Refs: iOS; IoT, Toys; macOS; Phones; School; Shopping; Social Media, YouTube; Teens
- Wikipedia: cyberbullying
- Common Sense Media apps, web sites
- Safer Internet Day each February
- NYT Learning Network Crosswords: Internet Safety .puz; 5/15/2003; Social Media 11/7/2011
- How to Protect Your Parents From Elder Fraud and Scams LH; 11/14/2023
- The A.I. Chatbots Have Arrived. Time to Talk to Your Kids.
experiment together; talk about how chatbots make you feel;
get to know the technology and its limitations; stay on top of new developments; NYT; 3/22/2023 - How to Set Up an Apple Watch for Your Kids Wired; 10/4/2022
- An Apple Watch for Your 5-Year-Old? More Parents Say Yes. NYT; 9/1/2022
- How to Limit What a Toddler Can Do When You Hand Over Your iPhone or iPad MR; 12/20/2021
- Why Apps Suddenly Want to Protect Kids
new British guidelines are influencing what U.S. internet companies do to protect American children; NYT; 12/9/2021 - Is It Too Soon to Give My Kid a Tablet? NYT; 12/1/2021
- What's One of the Most Dangerous Toys for Kids? The Internet. NYT; 11/24/2021
- Australia proposes teaching cyber-security to five-year-old kids Reg; 4/30/2021
- Microsoft Edge is getting a Kids Mode to add 'guardrails' to browsing the web custom browser themes, Bing SafeSearch; Verge; 2/16/2021
- How to Protect Your Family's Privacy During Remote Learning NYT; 8/21/2020
- Why Parents Should Pause Before Oversharing Online NYT; 8/4/2020
- Microsoft launches new Family Safety app for iOS and Android content filters, location sharing, and much more; Verge; 7/28/2020
- TikTok Broke Privacy Promises, Children's Groups Say NYT; 5/14/2020
- Millions of passwords for hit kid's game Webkinz leaked online TNW; 4/23/2020
- Teaching Your Kids to Be Safe Online: A Hasty Primer NYT; 4/2/2020
- These Students Are Learning About Fake News and How to Spot It NYT; 2/20/2020
- How Parents Can Get Involved on 'Safer Internet Day' LH; 2/11/2020
- How to change your kid's adult Apple ID account to a child account MW; 1/22/2020
- Why an internet that never forgets is especially bad for young people Obsessive documentation of one's life online has made it hard for young people to shed their past identities and might have bad effects for society at large; MIT; 12/27/2019
- Video Games and Online Chats Are ‘Hunting Grounds’ for Sexual Predators NYT; 12/7/2019
- How to Protect Your Children From Online Sexual Predators
Set rules for when and how your child can interact with others online;
Spend time with your child on new games and apps;
Talk to your child about online safety, and listen;
Encourage your child to raise any concerns with a trusted adult;
Be on the lookout for warning signs of abuse;
Educate your child about blocking users who make them uncomfortable;
Don’t blame your child if abuse arises;
Take charge as your child’s online protector. No one else will; NYT; 12/7/2019 - Why you need to teach your kids about data privacy TNW; 11/23/2019
- How Photos of Your Kids Are Powering Surveillance Technology Millions of Flickr images were sucked into a database called MegaFace; NYT; 10/11/2019
- The Simplest Way to Freeze Your Child's Credit 10/2/2019
- How to Safeguard Children Against Cyberbullying NYT; 9/5/2019
- Mom and Dad, It’s My (Digital) Life according to your children, 'sharenting' undermines their autonomy; NYT; 9/2/2019
- When Children Use Technology, Let Common Sense Prevail All things in moderation is a good way to think about it, says Jessica Grose, the editor of NYT Parenting; NYT; 8/28/2019
- How to Protect Your Parents From Online Dating Scams LH; 8/26/2019
- Keep These Apps Off Your Kid's Phone MeetMe; Grindr; Skout; WhatsApp; TikTok; Badoo; Bumble; Snapchat; Kik; LiveMe; Holla; Whisper; Ask.fm; Calculator% (and many other calculator apps that hide photos, videos and other files); Hot or Not; LH; 8/22/2019
- America's elderly seem more screen-obsessed than the young Seniors spend nearly ten hours a day in front of televisions, smartphones and computers; Econ; 8/14/2019
- How to Protect Our Kids' Data and Privacy Wired; 7/7/2019
- Teach Your Kid About Digital Safety Internet Awesome from Google;
Interland: 4 games -- some Q&A, some movement, quizzes:
Reality River: spot fake news, recognize the signs of a scam and understand phishing.
Mindful Mountain: consequences of being an "oversharer"
Kind Kingdom: what to do about cyberbullies
Tower of Treasure: create a strong password; LH; 6/28/2019 - Becoming a Digital Grandparent video chat; NYT; 6/5/2019
- Listen, parents, here are 3 reasons you shouldn't use child tracking apps
1. Companies are tracking for profit;
2. Risks of leaking private data;
3. It can break trust with child; TNW; 5/20/2019 - Old, Online, And Fed On Lies: How An Aging Population Will Reshape The Internet as more seniors go online, they are largely being left out of digital literacy efforts, making them targets for misinformation and hyperpartisan rhetoric; BF; 4/3/2019
- New privacy bill would give parents an 'Eraser Button' and ban ads targeting children Verge; 3/12/2019
- Do you see a yield sign in QuickTime Player for your Mac's FaceTime camera? you may have used parental controls to disable it; MW; 3/12/2019
- How Equifax Complicates a Simple Task: Freezing a Child's Credit NYT; 3/8/2019
- Suicide tips and other dark and dangerous content was found spliced in kids' cartoon videos on YouTube and YouTube Kids WaPo; 2/24/2019
- The worrying trend of children’s data being sold on the dark web tax fraud, synthetic identities; TNW; 2/23/2019
- When Kids Realize Their Whole Life Is Already Online Kids googling themselves for the first time face shock, frustration, and sometimes excitement at content parents had been posting about them since their birth; Atl; 2/20/2019
- Screen time inhibits toddler development, study finds TC; 1/28/2019
iOS
- How to Keep Kids From Bypassing iOS 13.3's Communication Limits LH; 12/13/2019
- Apple’s new parental controls on iOS can be bypassed Communication Limit feature in iOS 13.3 has some bugs; Verge; 12/12/2019
- How parents can turn on iOS 12 Screen Time for their child's iPhone or iPad ApIn; 2/24/2019
- How to Lock Your iPhone While Your Kid Uses an App
Setting > General > Accessibility > Guided Access; LH; 2/20/2019
Internet of Things, Toys
- Kids' Smartwatches Are a Security Nightmare Despite Years of Warnings five out of six brands tested by researchers would have allowed hackers to track kids -- and in some cases eavesdrop on them; Wired; 9/10/2020
- EU orders recall of children's smartwatch over severe privacy concerns ENOX Safe-KID-One smartwatches contain several security flaws that let third-parties track and call children's watches; ZD; 2/5/2019
macOS
- How to set up parental controls on a Mac MW; 5/12/2022
- How to Create a Child Account for Family Sharing on Mac OSXD; 1/26/2021
Phones
- How to Use Parental Controls on Your Child's New Phone NYT; 12/14/2022
School
- Kids Can Learn to Love Learning, Even Over Zoom NYT; 9/7/2020
- Schools already struggled with cybersecurity. Then came COVID-19 Ars; 7/3/2020
- Privacy Questions Raised By Distance Learning TD; 6/26/2020
- Can artificial intelligence prevent the next Parkland shooting? scan student emails, texts, documents, and social media activity for warning signs of cyber bullying, sexting, drug and alcohol use, depression, and to flag students who may pose a violent risk not only to themselves, but classmates; USA; 2/13/2019
Shopping
- Toys “R” Us Pivots From Teddy Bears to Surveillance MB; 12/11/2019
- Are Your Children Racking Up Charges From Mobile Games? Here’s How to Fight Back bait apps lure children into buying virtual junk online; NYT; 2/6/2019
Social Media, YouTube
- How to Wean a Teen Off Social Media NYT; 6/29/2023
- How to help young people limit screen time -- and feel better about how they look NPR; 2/26/2023
- Social Media Use Is Linked to Brain Changes in Teens, Research Finds NYT; 1/3/2023
- Does Social Media Make Teens Unhappy? It May Depend on Their Age. NYT; 3/28/2022
- US Teens Are Being Paid to Spread Disinformation on Social Media Pro-Trump youth group enlists teens in secretive campaign likened to a ‘troll farm,’ prompting rebuke by Facebook and Twitter; 9/15/2020
- What Parents Need to Know About Twitch LH; 8/31/2020
- A Third of TikTok's U.S. Users May Be 14 or Under, Raising Safety Questions NYT; 8/14/2020
- 4 Things to Know About YouTube’s New Children Privacy Practices Limited Collection of Digital Data; Changes to Ads and Recommendations; New Requirement for YouTube Producers; NYT; 1/5/2020
- How to Introduce Your Kid to the Wild World of Social Media LH; 11/20/2019
- Don't Post Your Toddler's Tantrum on Social Media LH; 8/26/2019
- Facebook design flaw let thousands of kids join chats with unauthorized users Verge; 7/22/2019
- Study of 3,800 young people over four years: high levels of social media usage showed an increase in depressive symptoms, while playing video games did not CBC; 7/16/2019
- Social Media Could Make It Impossible to Grow Up Wired; 7/8/2019
- YouTube under federal investigation over allegations it violates children's privacy WaPo; 6/19/2019
- Social Media May Sway Kids To Eat More Cookies -- And More Calories NPR; 3/4/2019
- Who Are Online, Recruited by Advertisers and 4 Years Old? Kidfluencers Brands are giving lucrative endorsement deals to young children on YouTube and Instagram, raising questions about whether their young followers should be seeing that kind of marketing; NYT; 3/1/2019
- How to Check If Your Kid Is Using Facebook's 'Banned' Research App LH; 1/30/2019
- Facebook has been paying teens $20 a month for total access to their phone activity the company's research division is installing root certificates on iPhones; Verge; 1/29/2019
- Senators ask Facebook why it tricked kids into spending parents' money Ars; 1/29/2019
Teens
- 'Luddite' Teens Don't Want Your Likes
When the only thing better than a flip phone is no phone at all; NYT; 12/15/2022 - How to convert a child account with two-factor authentication to an adult account MW; 9/15/2022
- What Adults Don't Get About Teens and Digital Life Wired; 8/21/2022
- Teens find circumventing Apple's parental controls is child's play WaPo; 10/15/2019
- Google Docs grows as a popular secret communication tool for teens as parents and teachers, unaware of its chat feature, assume students are just taking notes; Atl; 3/15/2019
Safer Internet: Course Updates
Safer Internet: Course Updates
Summary
- Students of earlier courses can refer back to this site as a refresher and to learn more about the latest privacy and security updates, significant changes, information and advice.
- Students who implemented only a few changes are welcome to re-enroll in the future to review, fine-tune and expand their protection.
- OS Update Status:
- Ongoing: newest articles appear at the top of Reference sections for each topic
- older (more than ~4 years ago) article references will usually be removed
- new subsections will be added as needed
Spring 2020
- P@s$w0rdz (separate course) is now 3 sessions.
- Be Safer on the Internet (version 2) is now shorter (3 sessions), with some other topics -- besides Passwords -- omitted.
- Comparison table of topics covered: original, version 2, P@s$w0rdz
Fall 2019
- For updated discussion of passwords and password managers, see my shorter (2-session) course: P@s$w0rdz
- Software Updates: iOS, iPadOS 13; macOS: 10.15
Winter 2019
- Wipr for ad blocking (iOS, Mac)
- Consider quitting social media altogether -- privacy settings won't really protect you from advertisers and data brokers; spend more time with your family & real friends
- added Summary sections with recommendations and links to subsections
- added topics: to References to supplement major subsections
Winter 2018
- Meltdown and/or Spectre processor 'speculative execution' flaws affect almost all computers/devices with Intel, AMD, ARM CPUs over past decade or so; Software Updates > References > Meltdown/Spectre
- It's not possible to completely fix (w/o replacing with newer CPU), but risk can be mitigated/minimized
- Update system software (Android, iOS, Linux, macOS, Windows); avoid malware; Software Updates > References